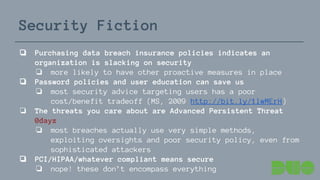
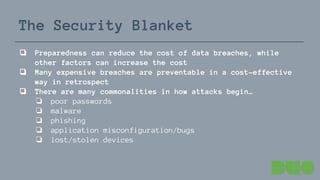
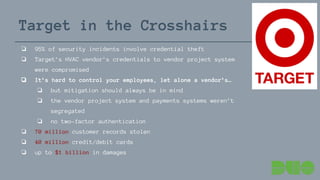
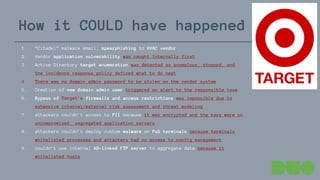
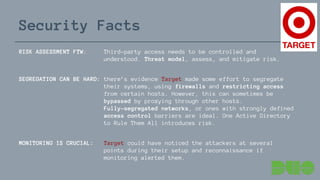
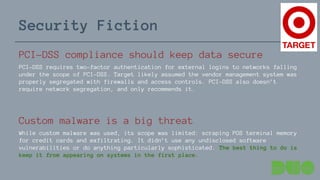
The document discusses the realities of data breaches, highlighting that many incidents are caused by simple mistakes rather than sophisticated attacks. It emphasizes the importance of strong security measures, effective incident response plans, and access controls to mitigate risks and reduce breach costs. Additionally, it contrasts common misconceptions about security compliance and advanced threats with the actual vulnerabilities organizations face.


![Security Facts
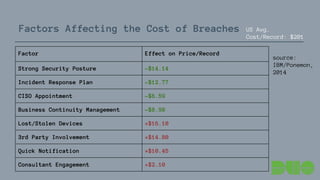
❏ The cost of a data breach is on the rise
❏ average cost increased 8.3% from $5.4 MM in 2013 to $5.85
MM in 2014
❏ average cost per record increased 6.9% from $188 in 2013
to $201 in 2014
❏ the most costly breaches are malicious & criminal attacks
❏ Will your organization be breached?
❏ “The results show that a probability of a material data
breach [over the next 2 years] involving a minimum of
10,000 records is more than 22 percent”*
* source: IBM/Ponemon “Cost of Data Breach Study”, 2014: http://ibm.co/1Df4urk
based on survey of 314 global organizations that experienced data breach](https://image.slidesharecdn.com/newmindpreso-150513141357-lva1-app6892/85/Security-Fact-Fiction-Three-Lessons-from-the-Headlines-6-320.jpg)