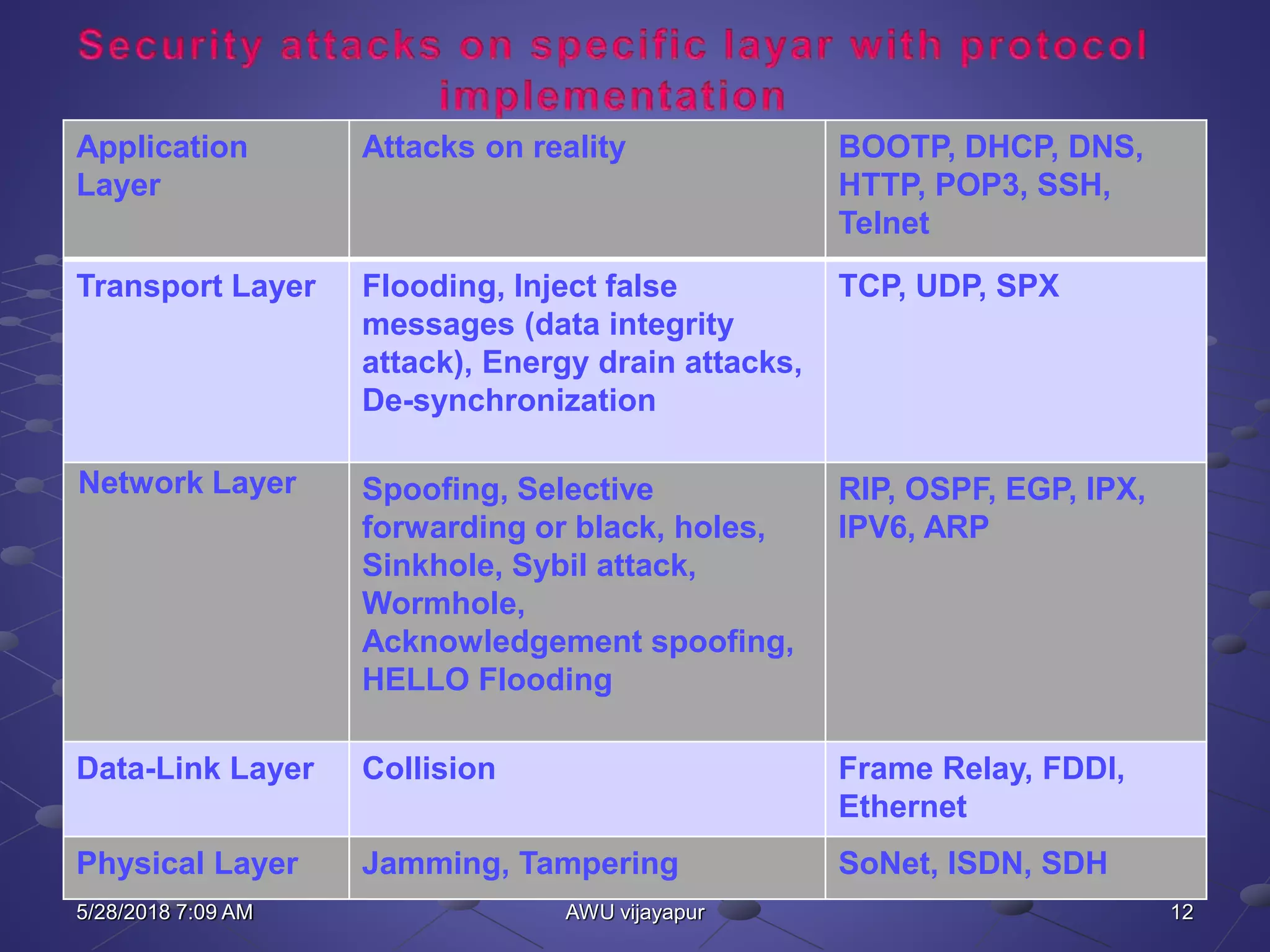
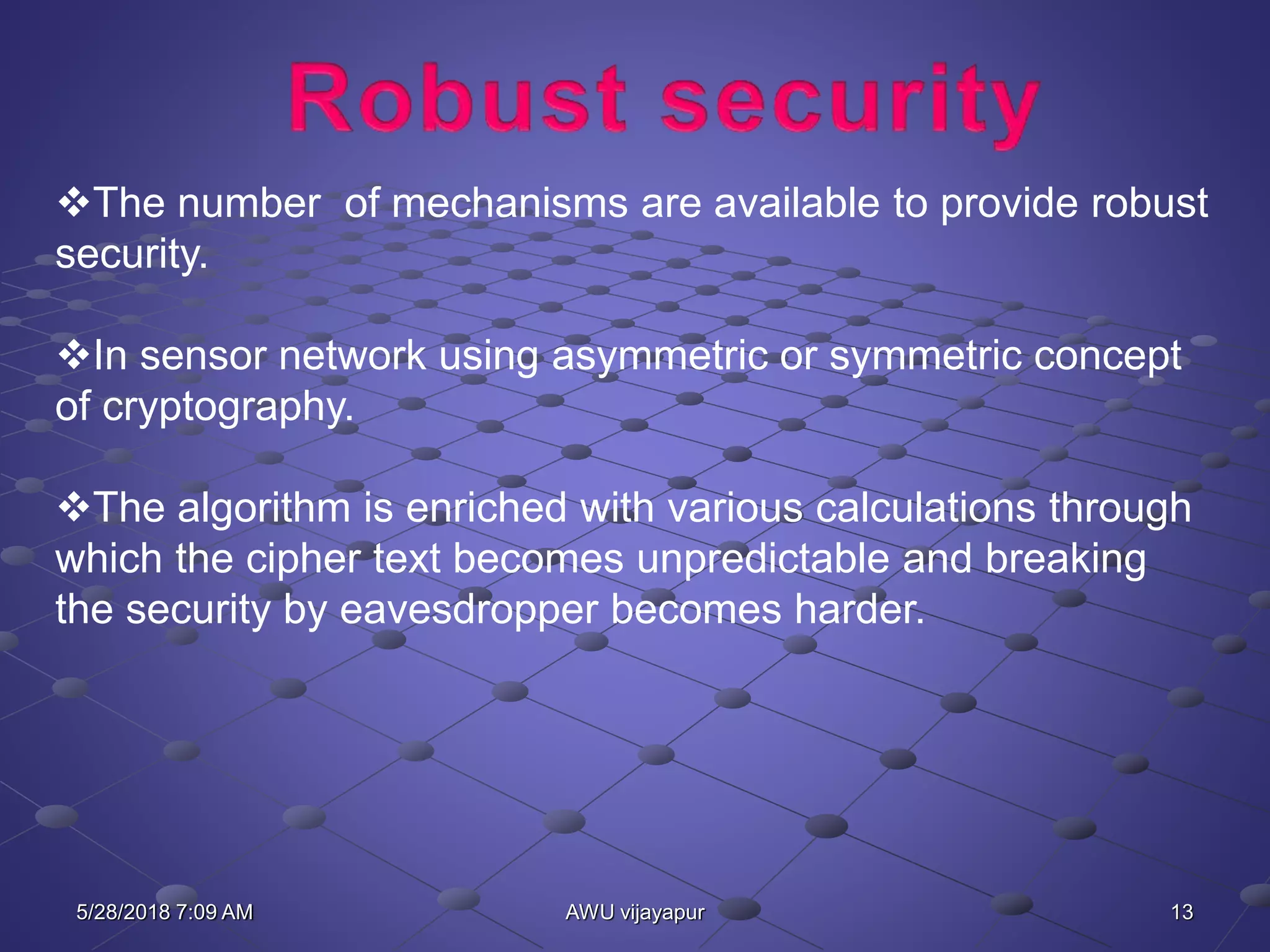
The document discusses security vulnerabilities and requirements in sensor networks. It outlines various security attacks that can occur at different network layers. Key management is identified as an important mechanism for security. Public key cryptography algorithms like Elliptic Curve Cryptography (ECC) are optimized solutions for sensor networks due to their lower computational overhead compared to algorithms like RSA. The document also reviews different key management protocols and concludes by recommending ECC for its ability to provide robust security while reducing storage and communication costs in resource-constrained sensor networks.



![22AWU vijayapur
References
[1] J. Xu, J. Wang, S. Xie, W. Chen and J. Kim, “Study on Intrusion
Detection Policy for Wireless Sensor Networks”, International Journal of
Security and Its Applications, vol. 7, no. 1, (2013) January, pp. 1-6.
[2] I. Akyildiz, W. Su, Y. Sankarasubramaniam, and E. Cayirci, “Wireless
Sensor Networks: a Survey”, Computer Networks, vol. 38, no. 4, (2002), pp.
393-422.
[3] K. Martinez, J. Hart, and R. Ong, “Environmental Sensor Networks”,
IEEE Computer, vol. 37, no. 8, (2004), pp. 50-56
[4] R. Abouhogail, “Security Assessment for Key Management in Mobile Ad
Hoc Networks”, International Journal of Security and Its Applications, vol. 8,
no. 1, (2014), pp. 169-182, http://dx.doi.org/10.14257/ijsia.2014.8.1.16
[5] J. Zhang, J. Tan, and J. Li, “Key Distribution using Double Keyed-hash
Chains for Wireless Sensor Networks”, International Journal of Security and
Its Applications, vol. 7,
5/28/2018 7:09 AM](https://image.slidesharecdn.com/networksecurityppt-1-180528070921/75/Network-security-ppt-22-2048.jpg)
![23AWU vijayapur
[6] E. Ngai, J. Liu, and M. Lyu, “On the Intruder Detection for Sinkhole Attack in
Wireless Sensor Networks”, IEEE International Conference on
Communications, (2006).
[7] D. Martins and H. Guyennet, “Wireless Sensor Network Attacks and Security
Mechanisms: A Short Survey”, 13th International Conference on Network-
Based Information Systems, (2010).
[8] M. Jain, “Wireless Sensor Networks: Security Issues and Challenges”,
International Journal of Computer and Information Technology, vol. 2, no. 1,
(2011), pp. 62-67.
[9] N. Sethi and D. Sharma, “A Novel Method of Image Encryption Using
Logistic Mapping”, International Journal of Computer Science Engineering, vol.
1, no. 2, (2012) November.
[10] S. Karmakar and S. Chandra, “An Approach for Ensuring Security and its
Verification”, International Journal of Computer Science Engineering”, vol. 2, no.
3, (2013) May.
5/28/2018 7:09 AM](https://image.slidesharecdn.com/networksecurityppt-1-180528070921/75/Network-security-ppt-23-2048.jpg)
