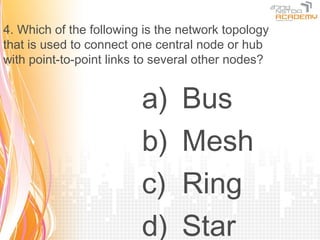
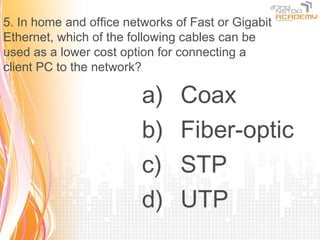
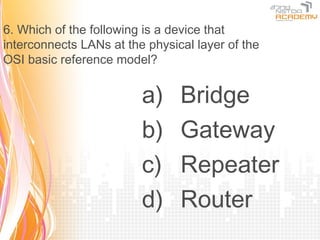
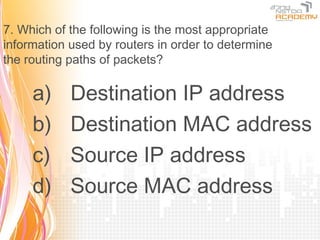
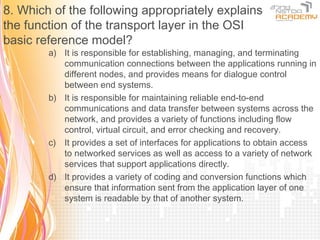
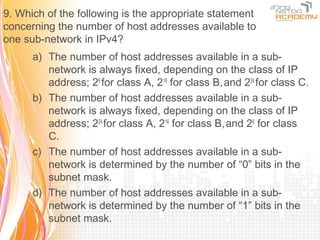
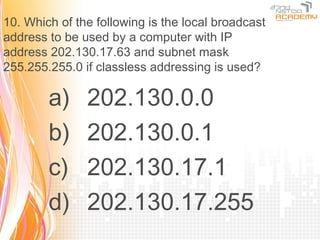
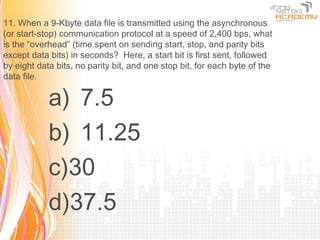
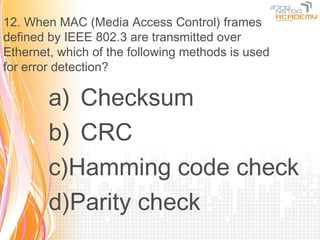
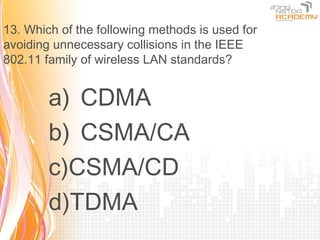
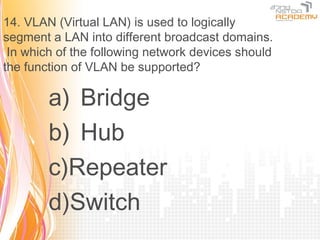
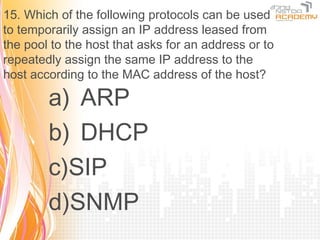
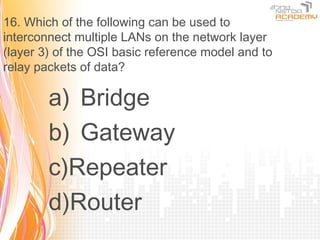
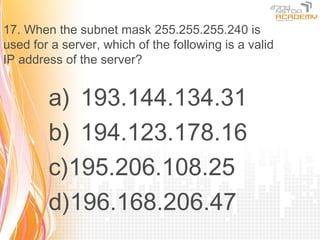
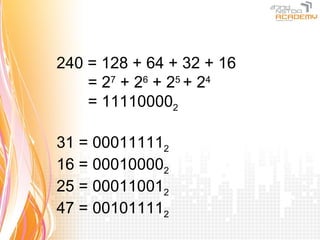
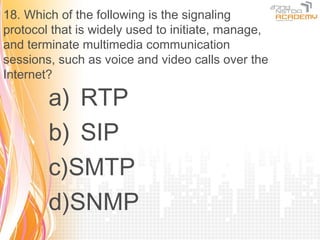
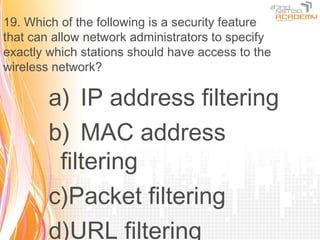
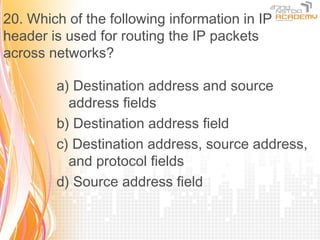
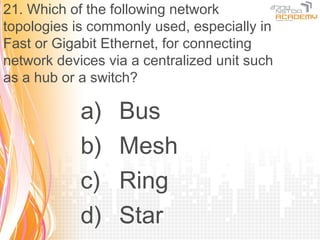
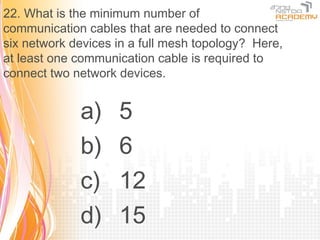
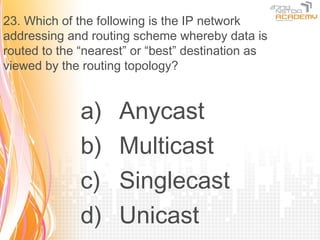
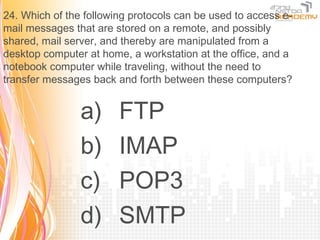
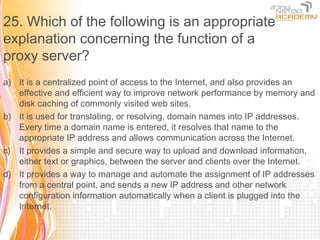
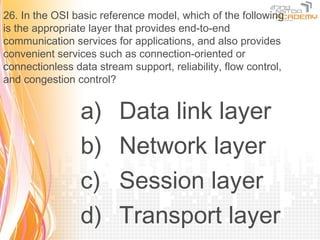
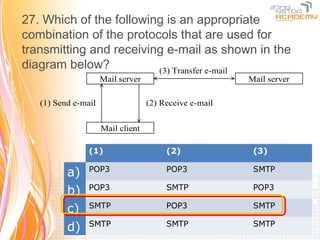
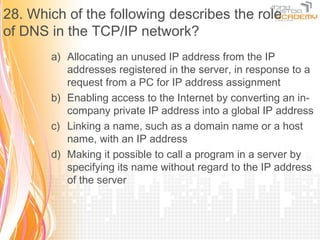
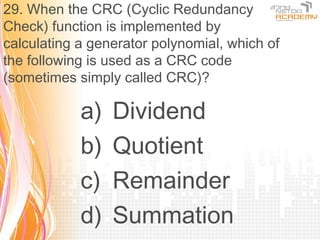
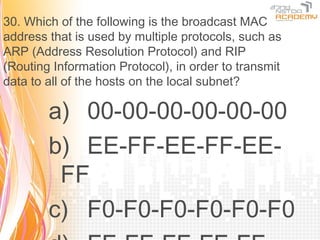
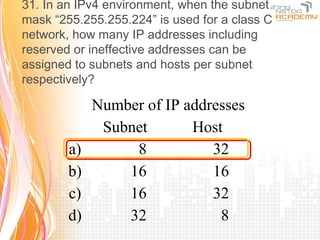
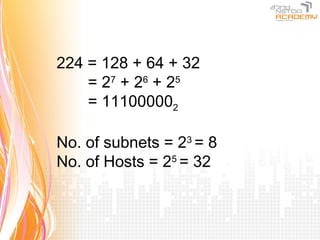
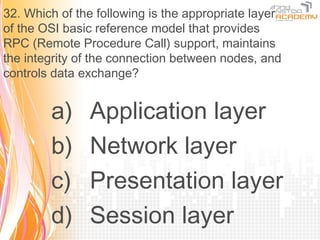
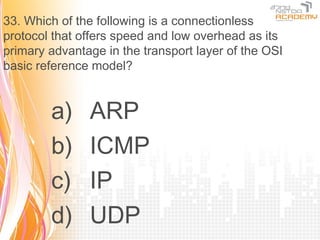
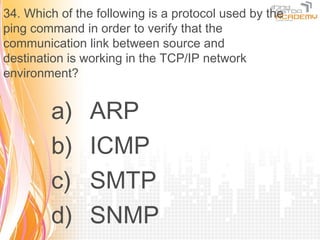
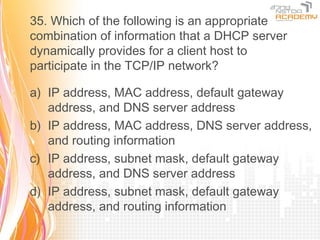
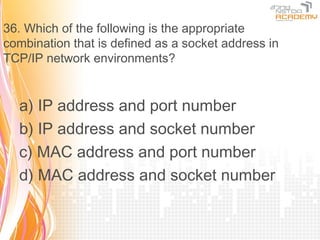
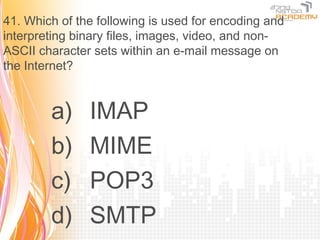
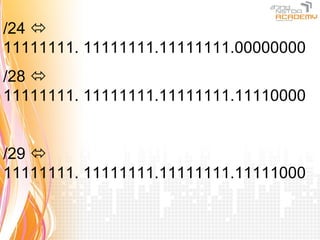
This document contains 27 multiple choice questions about networking concepts. The questions cover topics such as IP addressing, protocols, network devices, network topologies, and the OSI model. They assess understanding of fundamental networking principles including subnet masking, MAC addressing, routing, wireless standards, VLANs, and more.