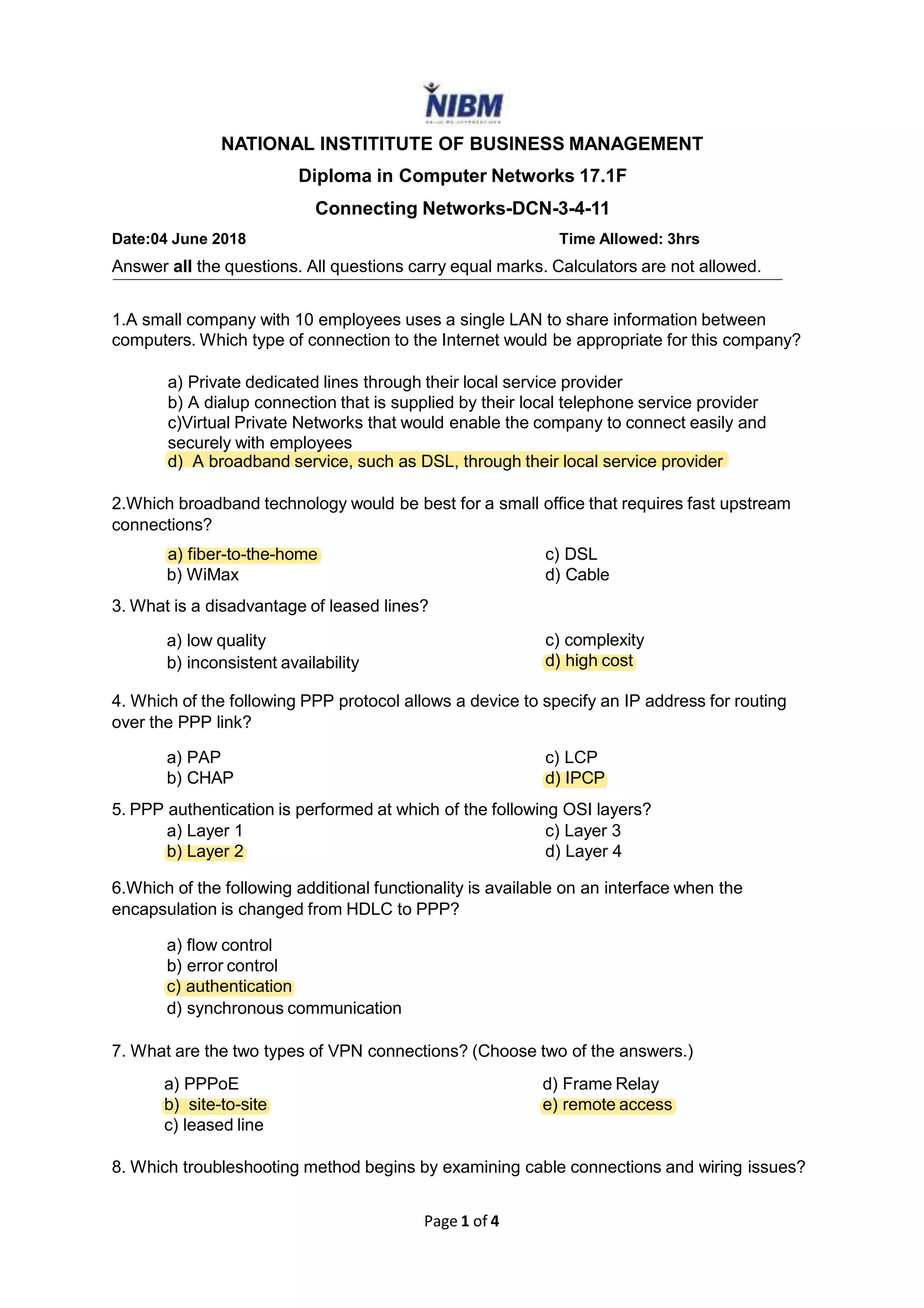
This document contains a 20 question practice exam on computer networks. It covers topics such as internet connection types for small businesses, broadband technologies, PPP protocols, VPN connections, troubleshooting methods, ACLs, SNMP, QoS, and network security concepts. The exam consists of multiple choice and short answer questions testing understanding of networking fundamentals and common network devices, protocols, and services.