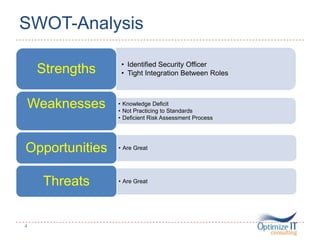
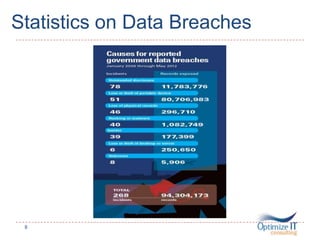
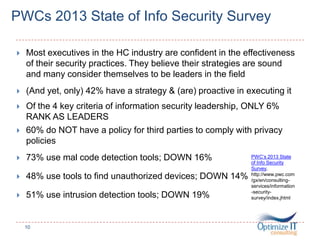
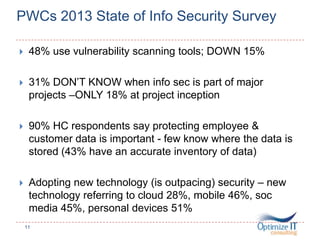
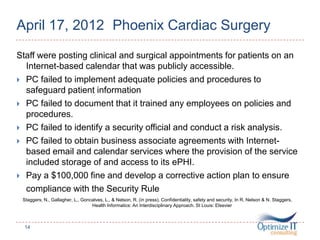
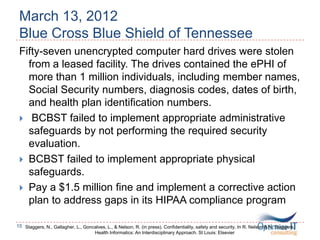
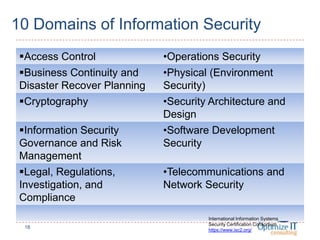
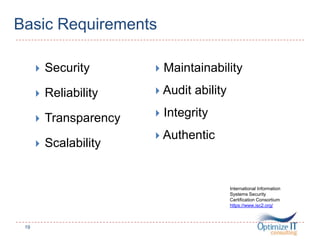
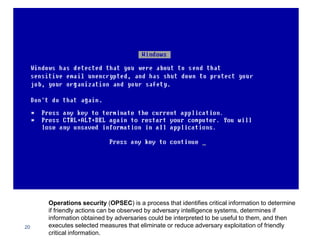
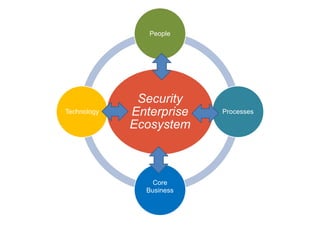
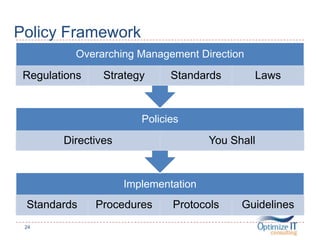
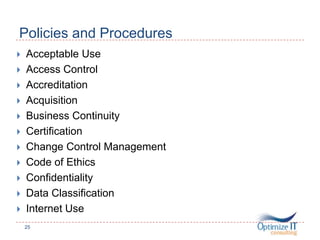
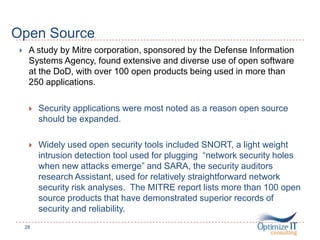
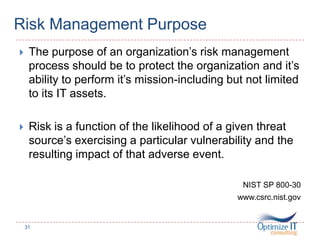
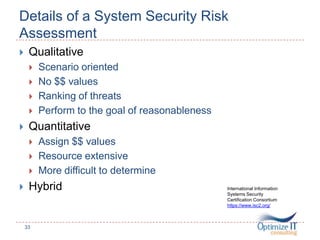
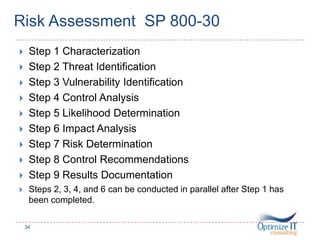
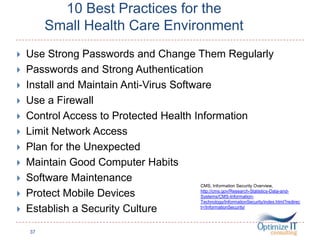
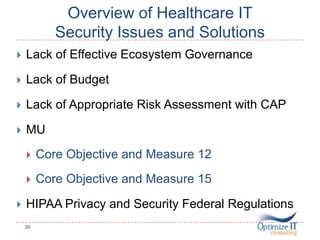
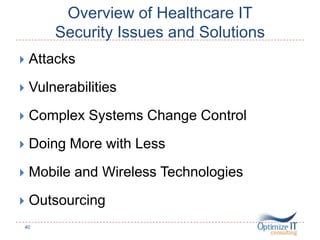
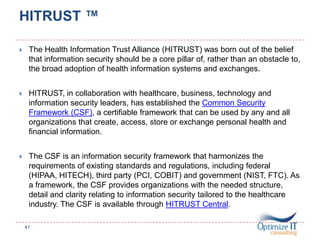
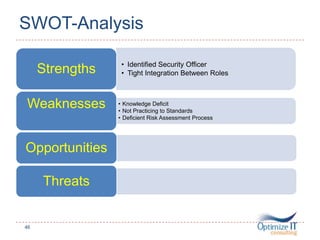
This document discusses information security for informatics professionals. It begins with an introduction of the speaker, Amy Walker, which details her experience in healthcare, informatics, and security. The presentation will cover IT security pillars, constructing policies and procedures, security standards and risk assessment strategies, system architecture and design, and an overview of security issues and solutions. Examples of data breaches and related fines are provided to illustrate security risks faced by healthcare organizations. Frameworks and best practices for security are also outlined to help attendees strengthen their organization's security posture.