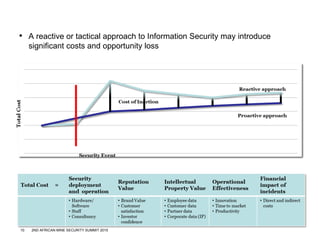
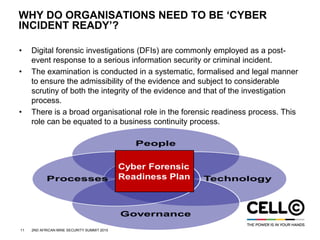
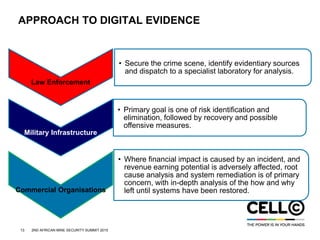
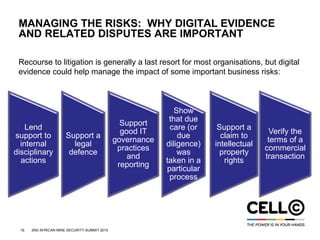
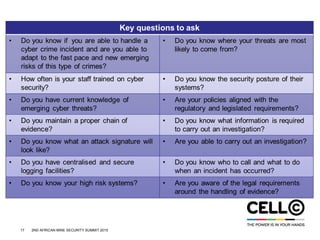
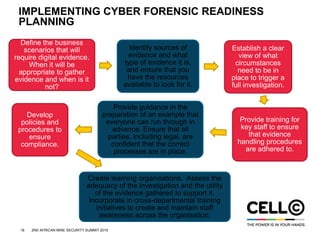
The document summarizes the presentation "Creating cyber forensic readiness within your organisation" given at the 2nd African Mine Security Summit. The presentation covered defining cyber crime, the current state of cyber crime in South Africa, why organizations are vulnerable, and what cyber forensic readiness planning entails. It discussed why organizations need to be prepared for cyber incidents, how to approach digital evidence, and provided steps to implement cyber forensic readiness plans, including defining scenarios requiring evidence, identifying evidence sources, and training staff on evidence handling procedures.