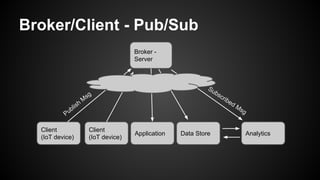
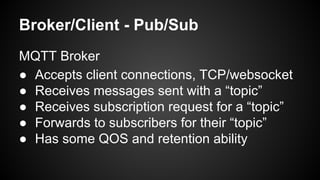
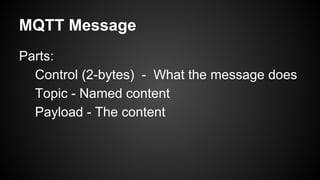
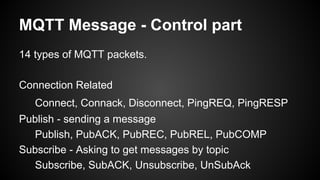
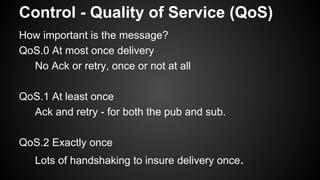
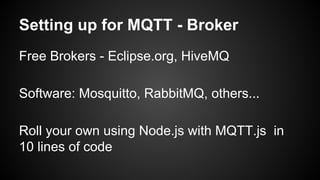
MQTT is a lightweight publish/subscribe messaging protocol ideal for constrained devices and low-bandwidth networks. It allows devices to publish messages to topics and subscribe to receive messages for topics, minimizing network usage. MQTT was created in 1999 and is in the process of being standardized. It uses TCP ports 1883 and 8883 and supports publish/subscribe messaging along with quality of service (QoS) guarantees and message retention. MQTT brokers allow clients like IoT devices to connect and publish/subscribe to topics to send and receive payload data.