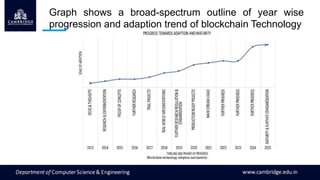
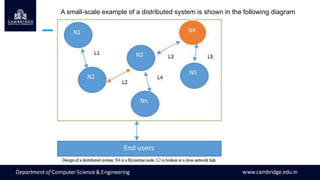
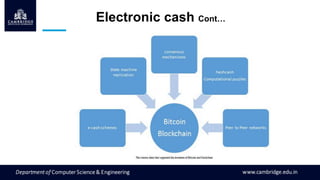
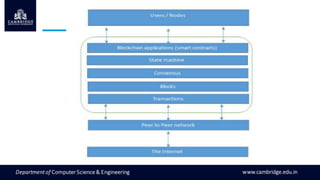
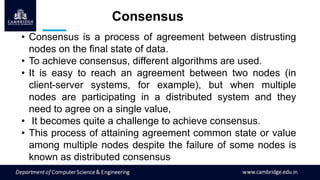
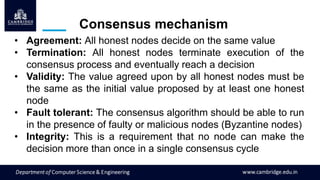
The document provides an introduction to blockchain technology. It discusses how blockchain first emerged with the invention of Bitcoin in 2008 and how its usage has expanded beyond cryptocurrencies to other areas. The document also describes key elements of blockchain like distributed ledgers, blocks, transactions, consensus mechanisms, and challenges like scalability and privacy. Distributed systems and concepts like the CAP theorem are also introduced.