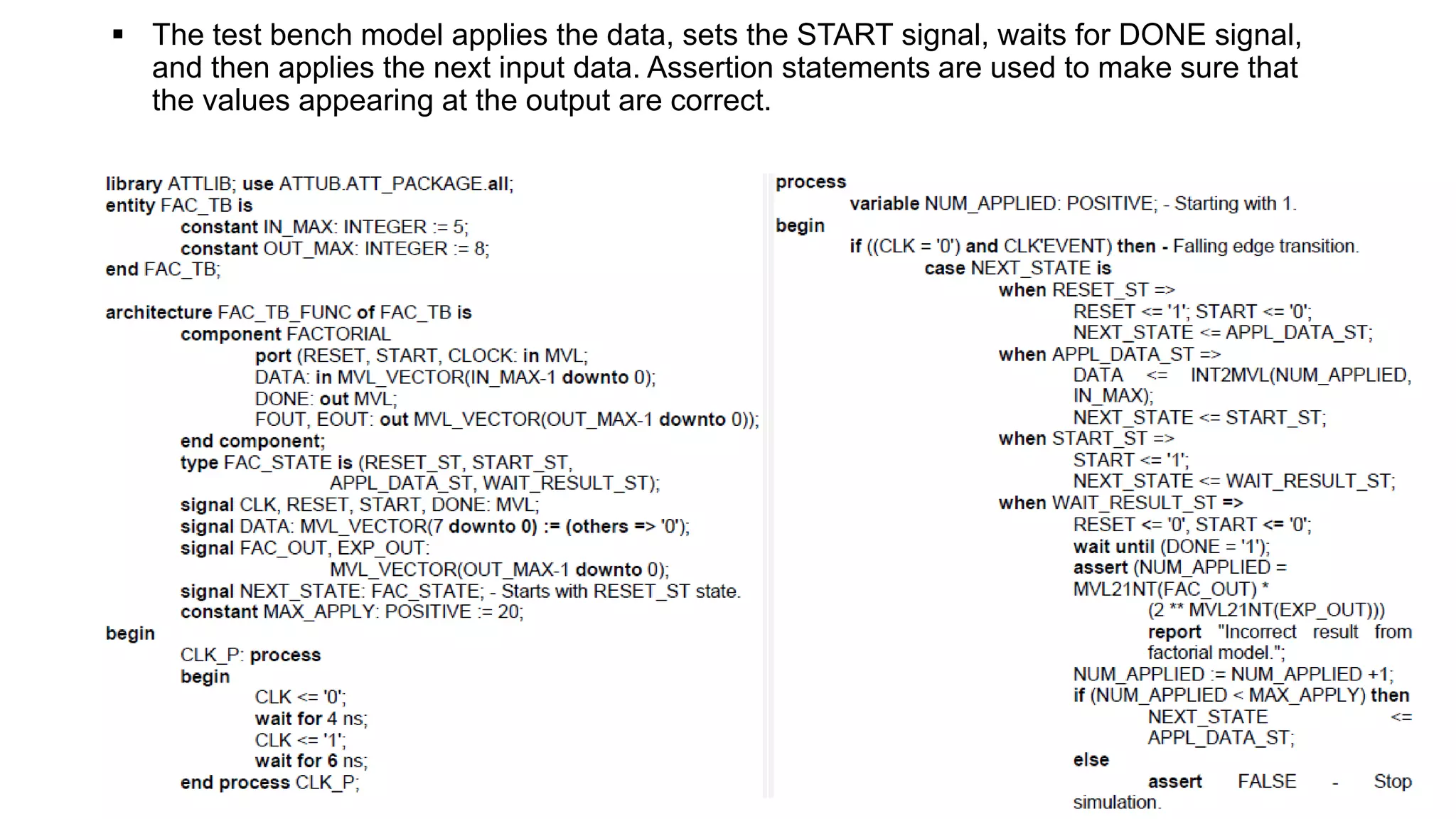
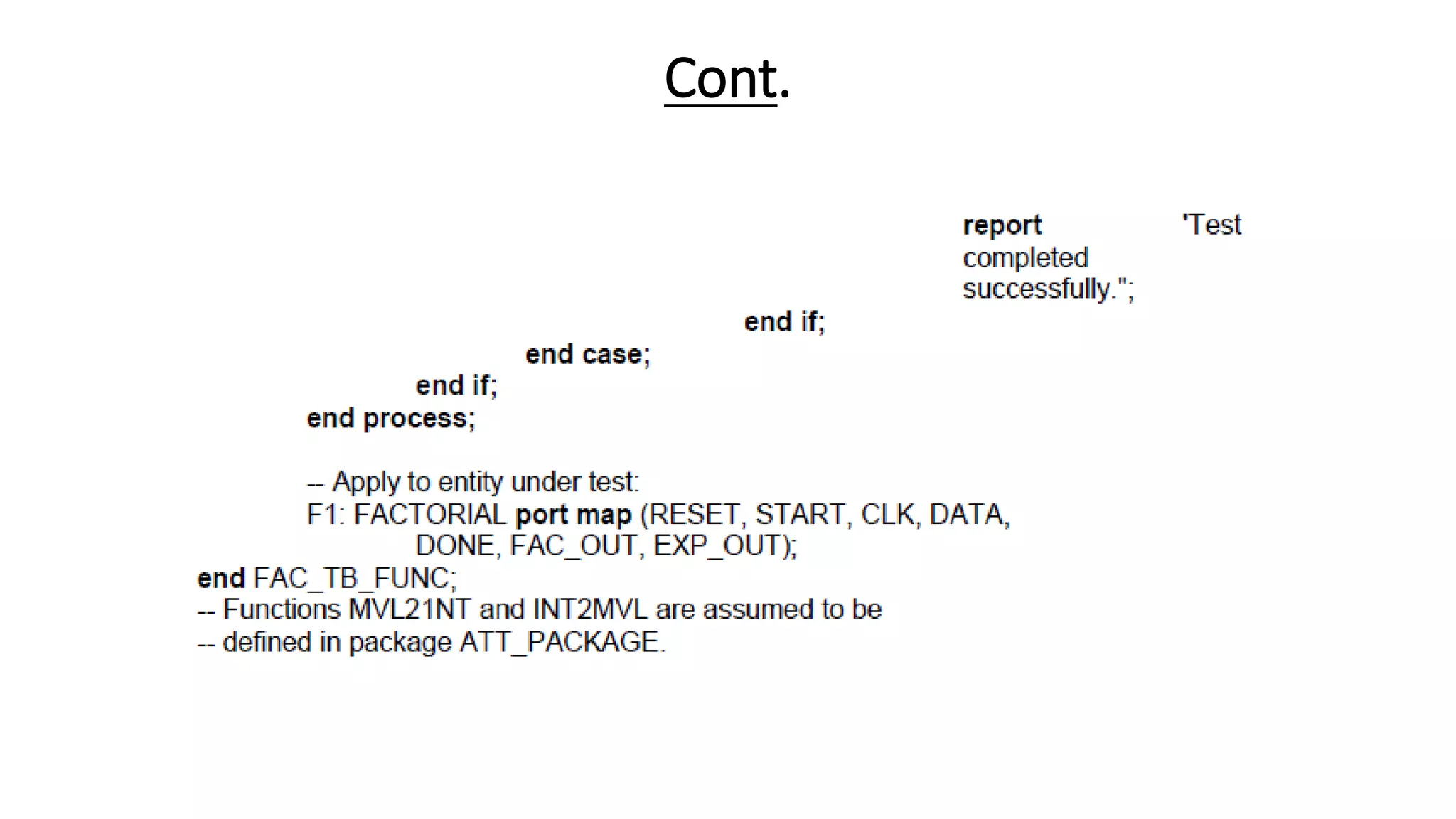
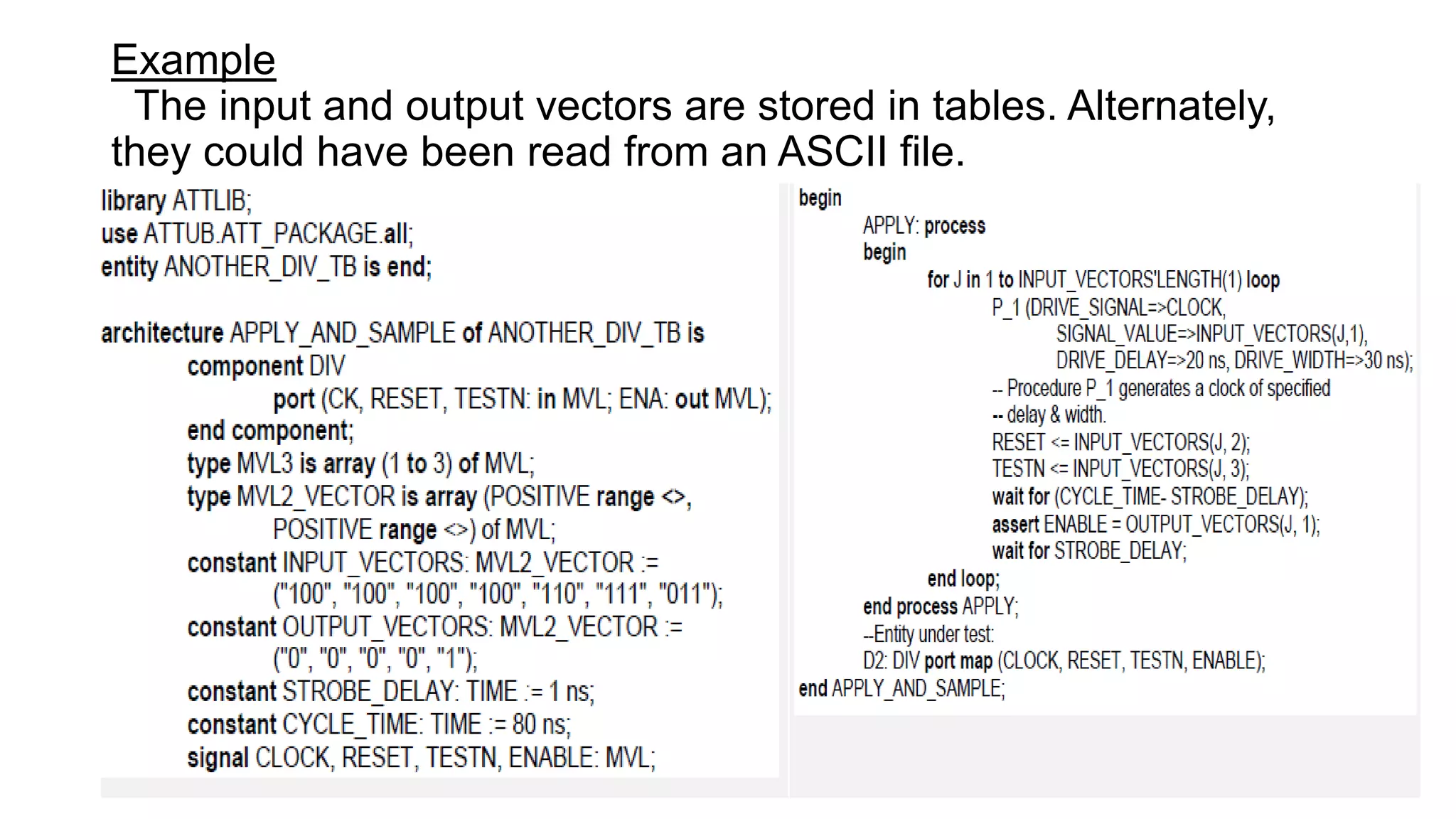
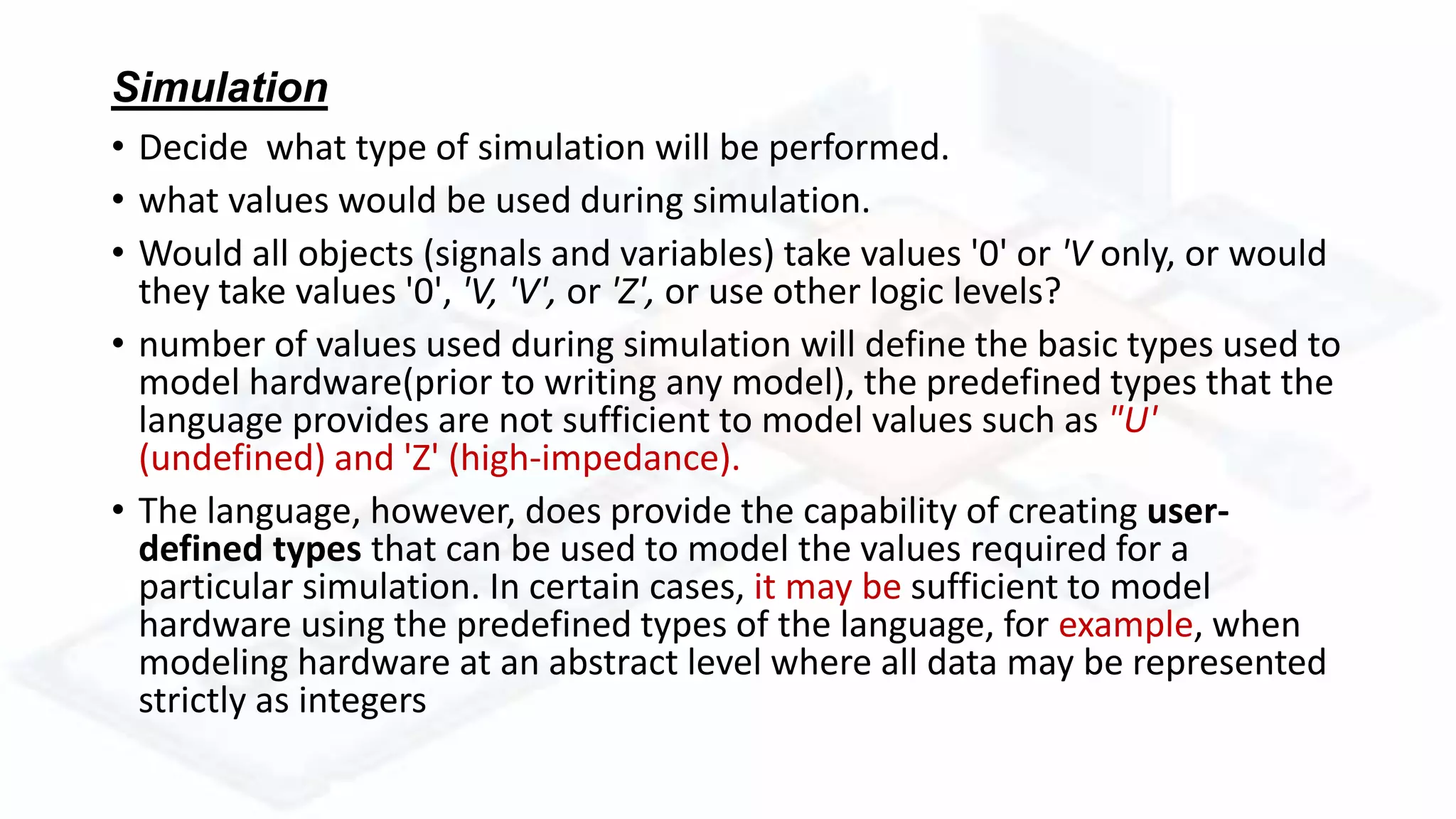
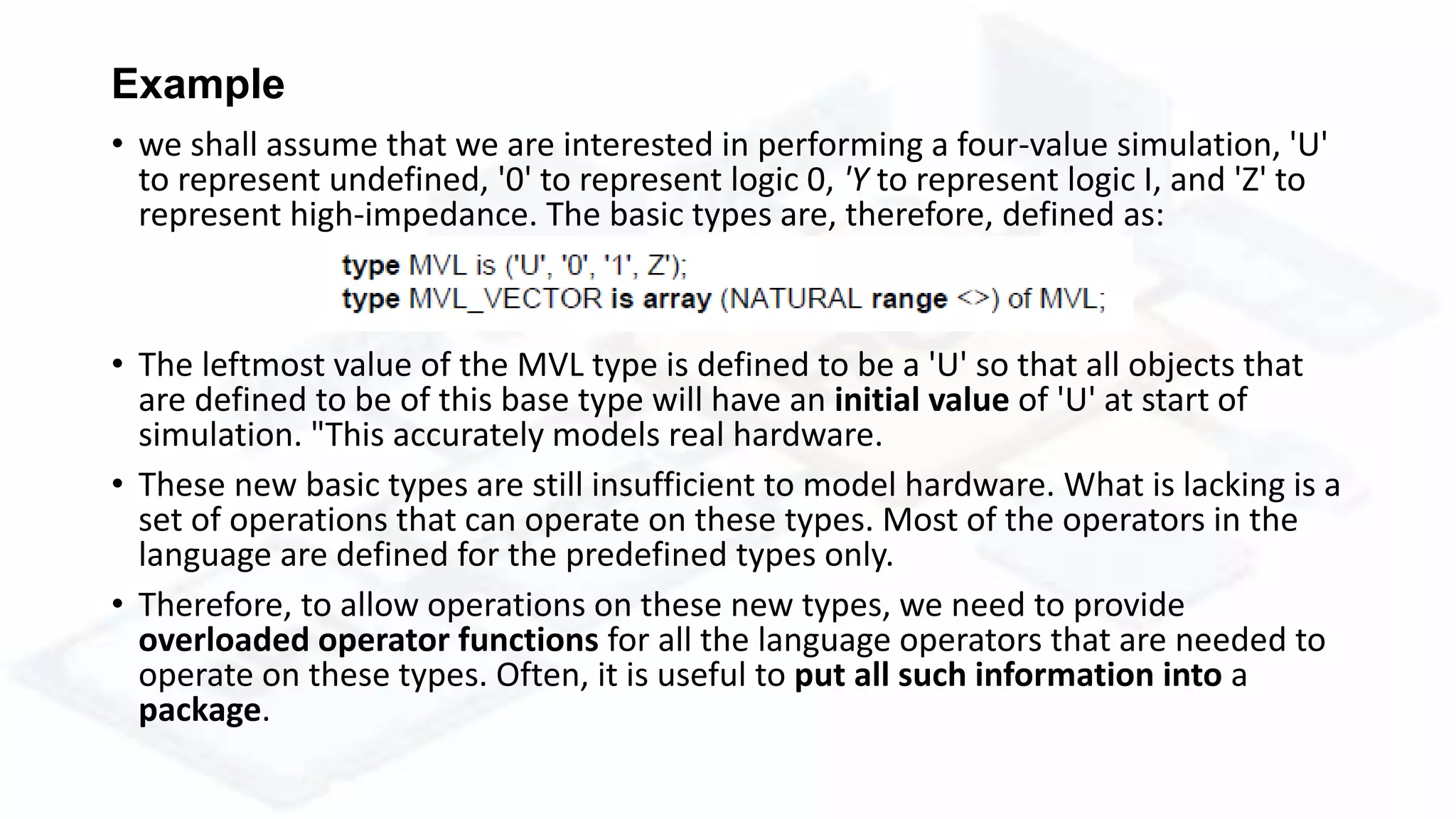
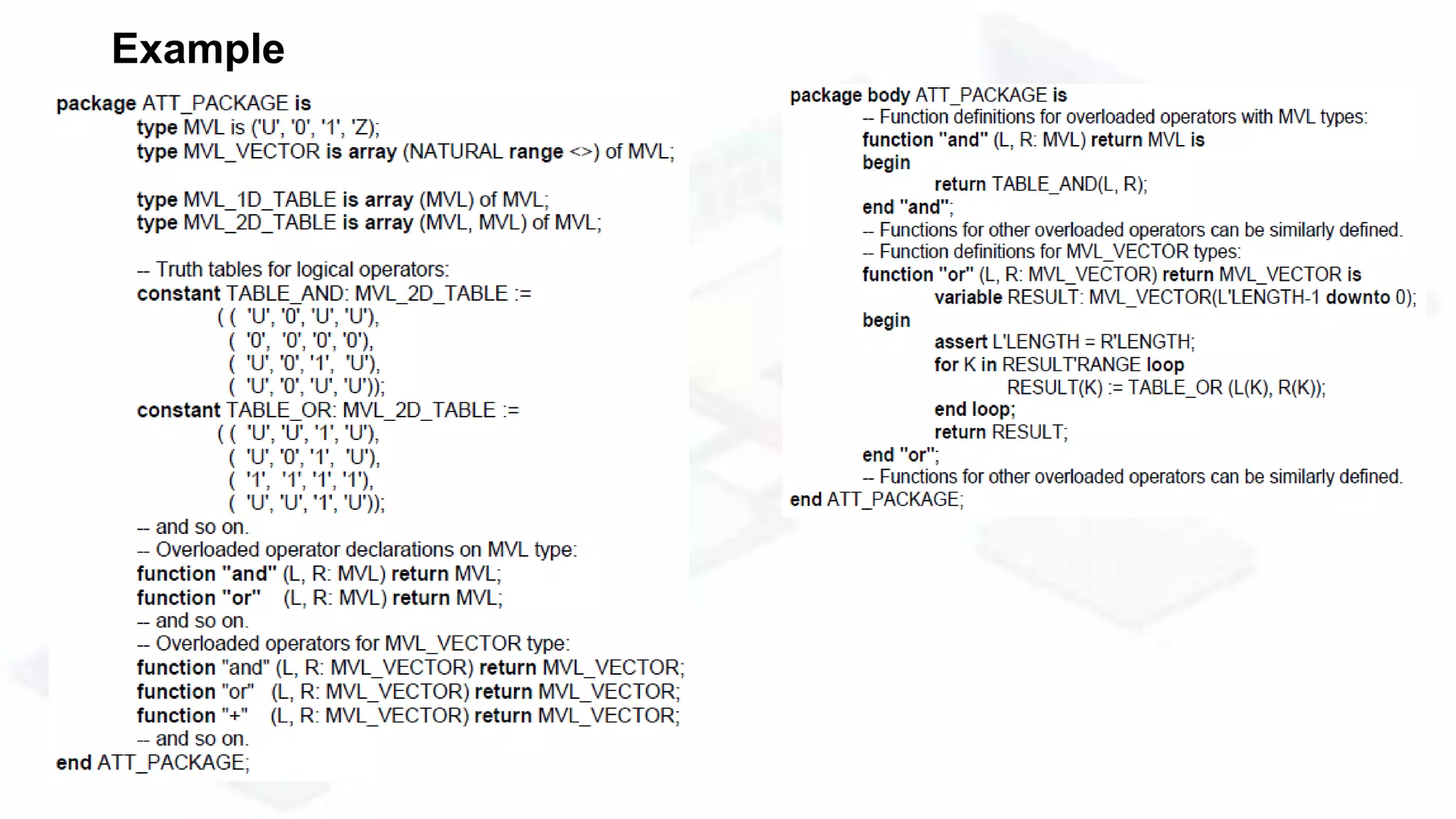
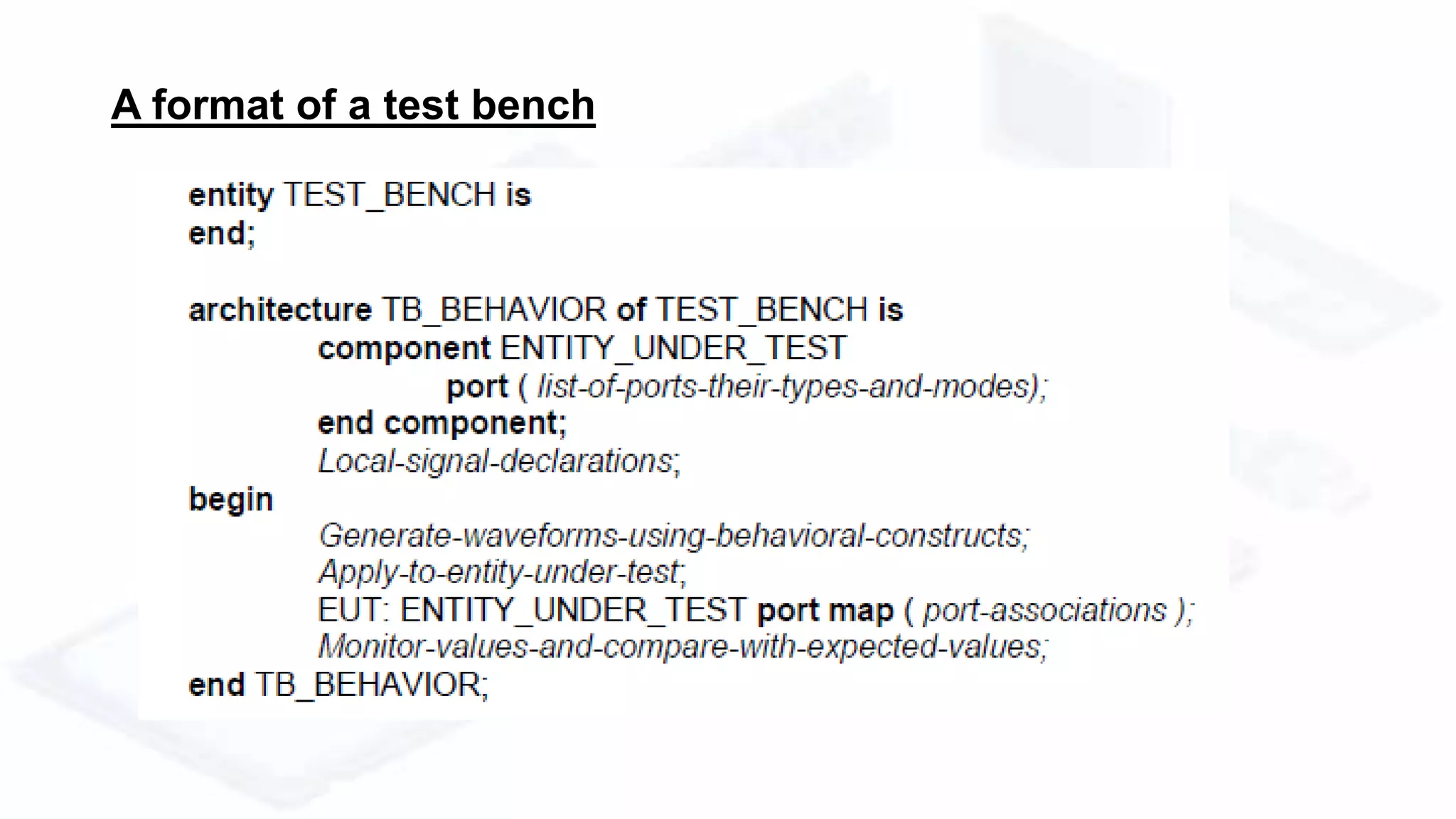
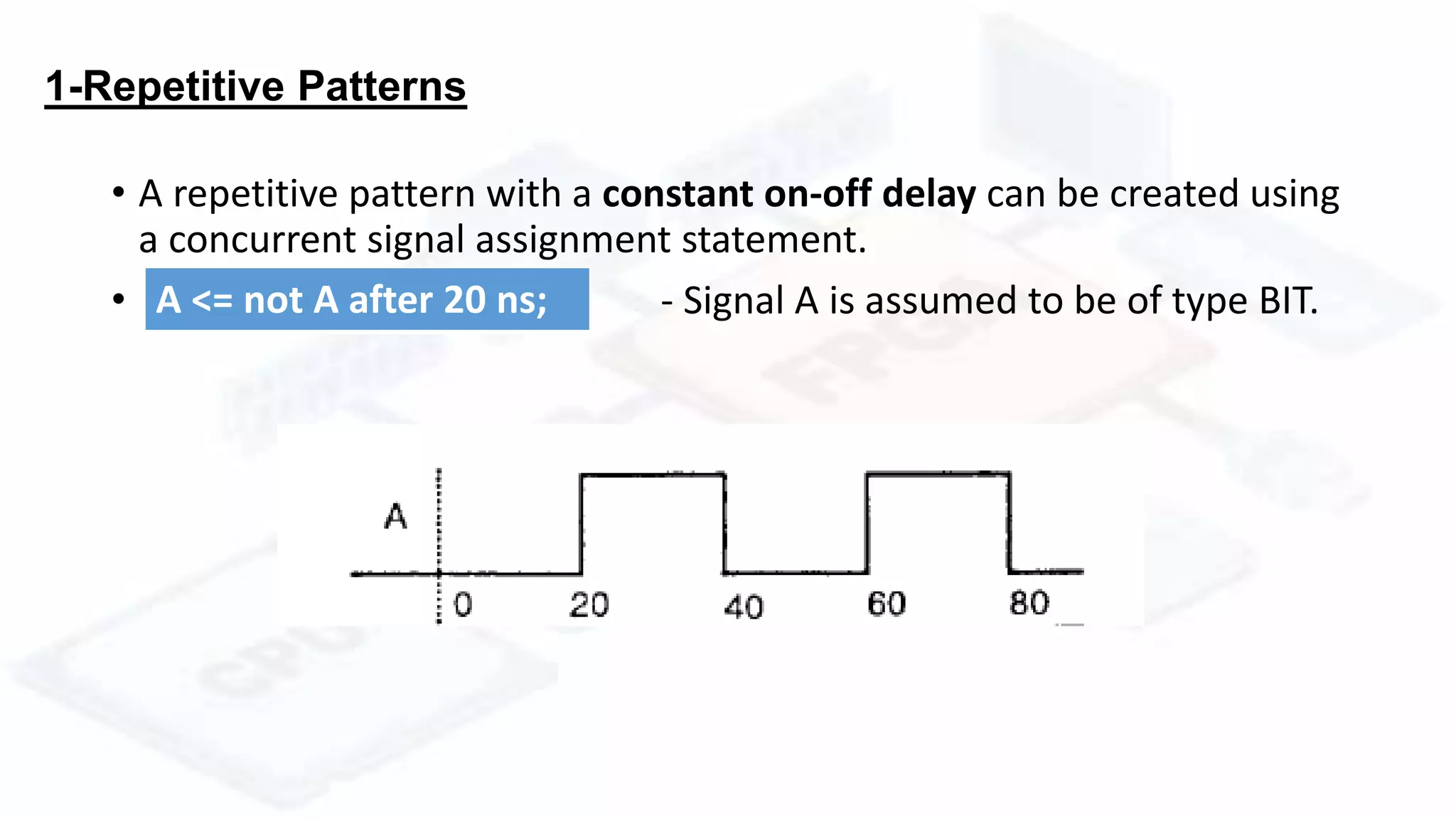
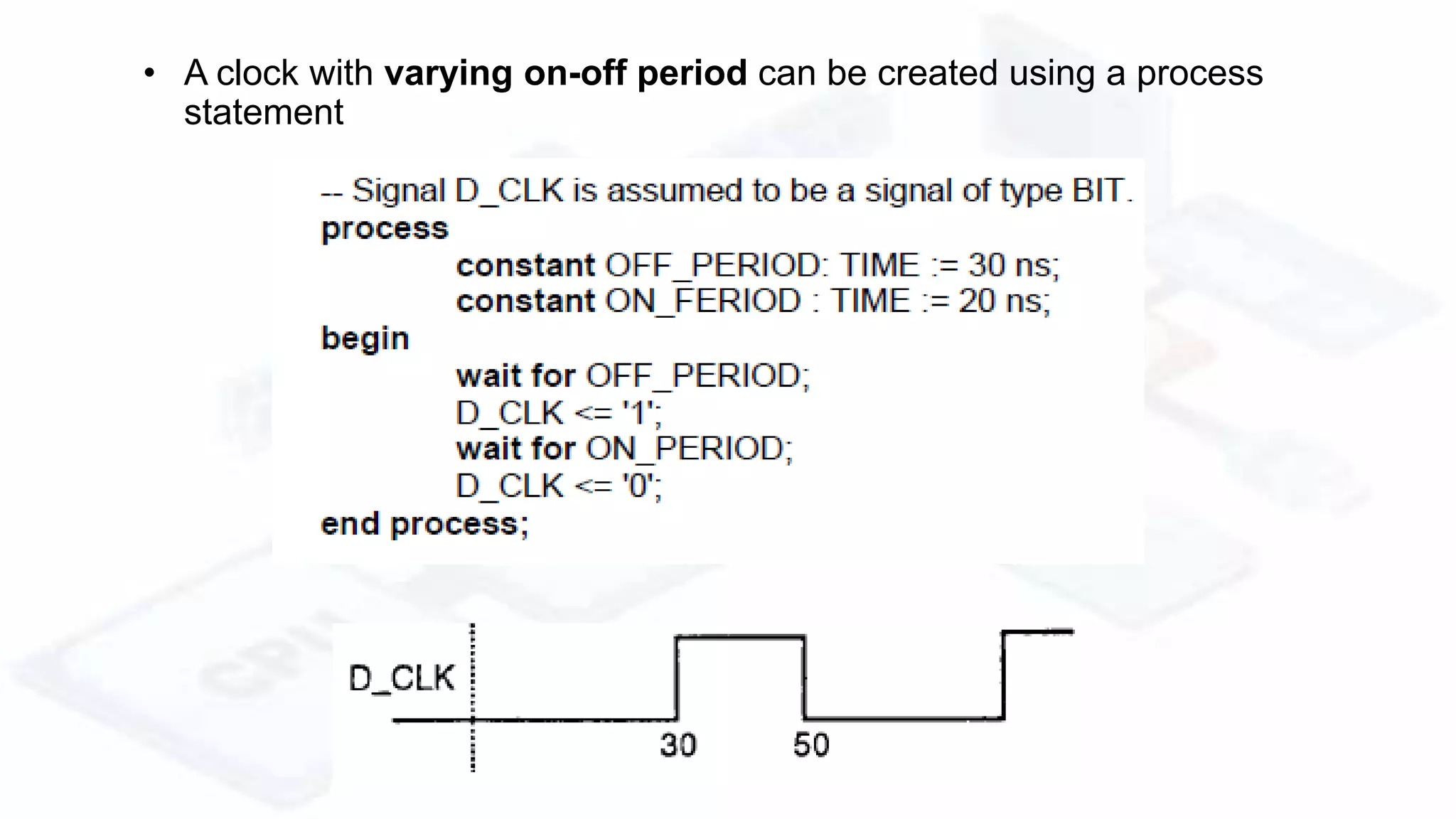
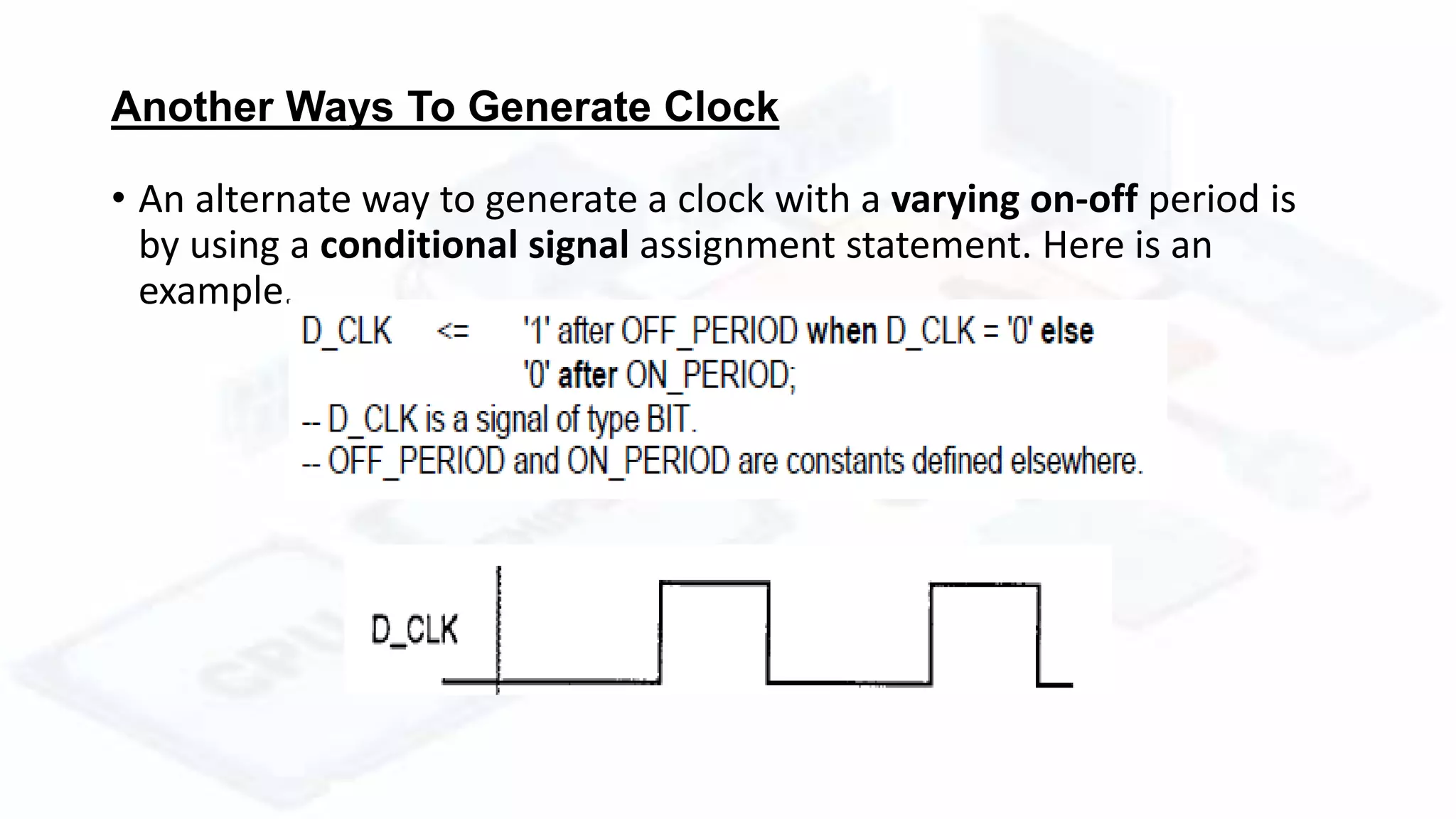
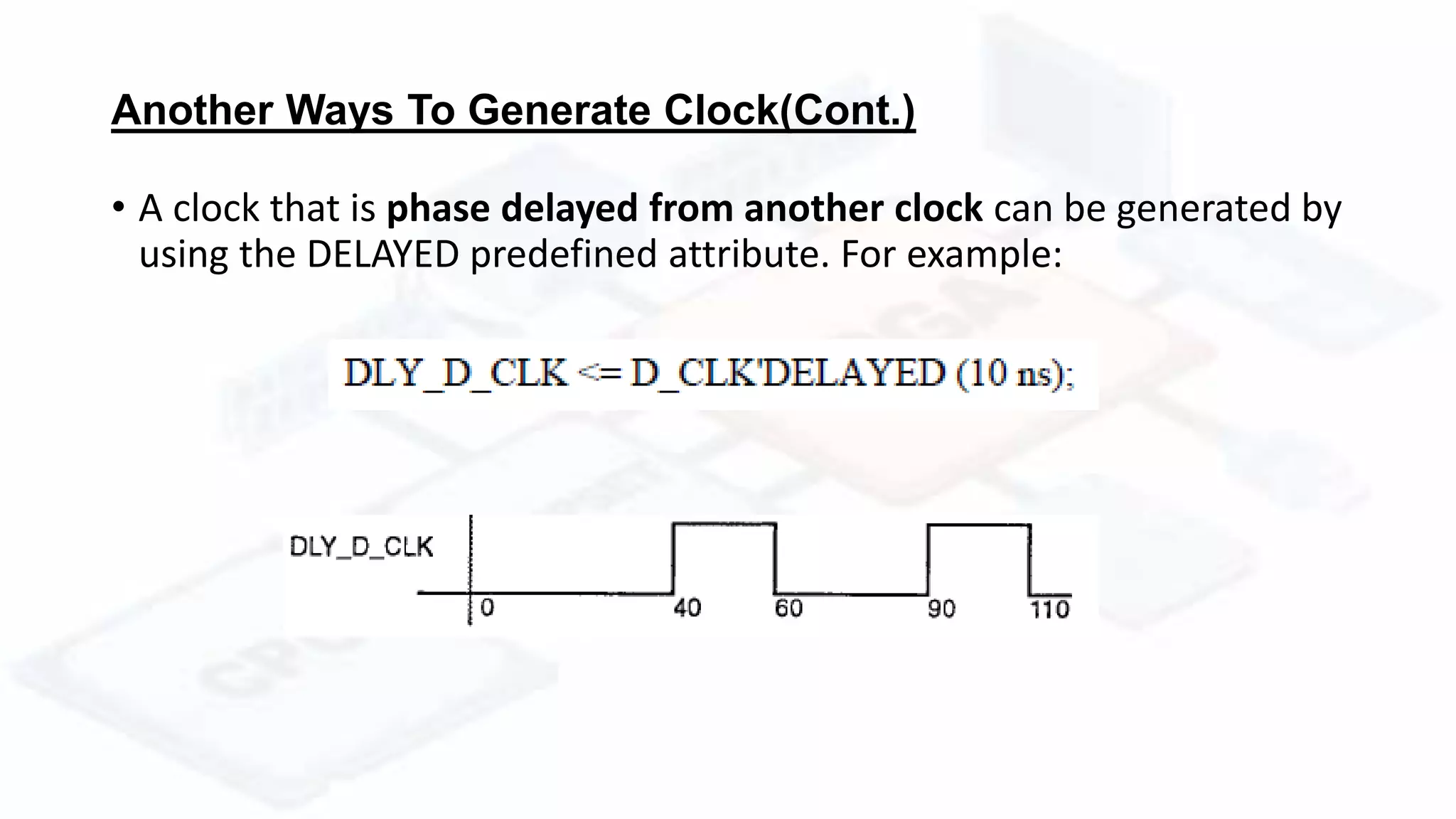
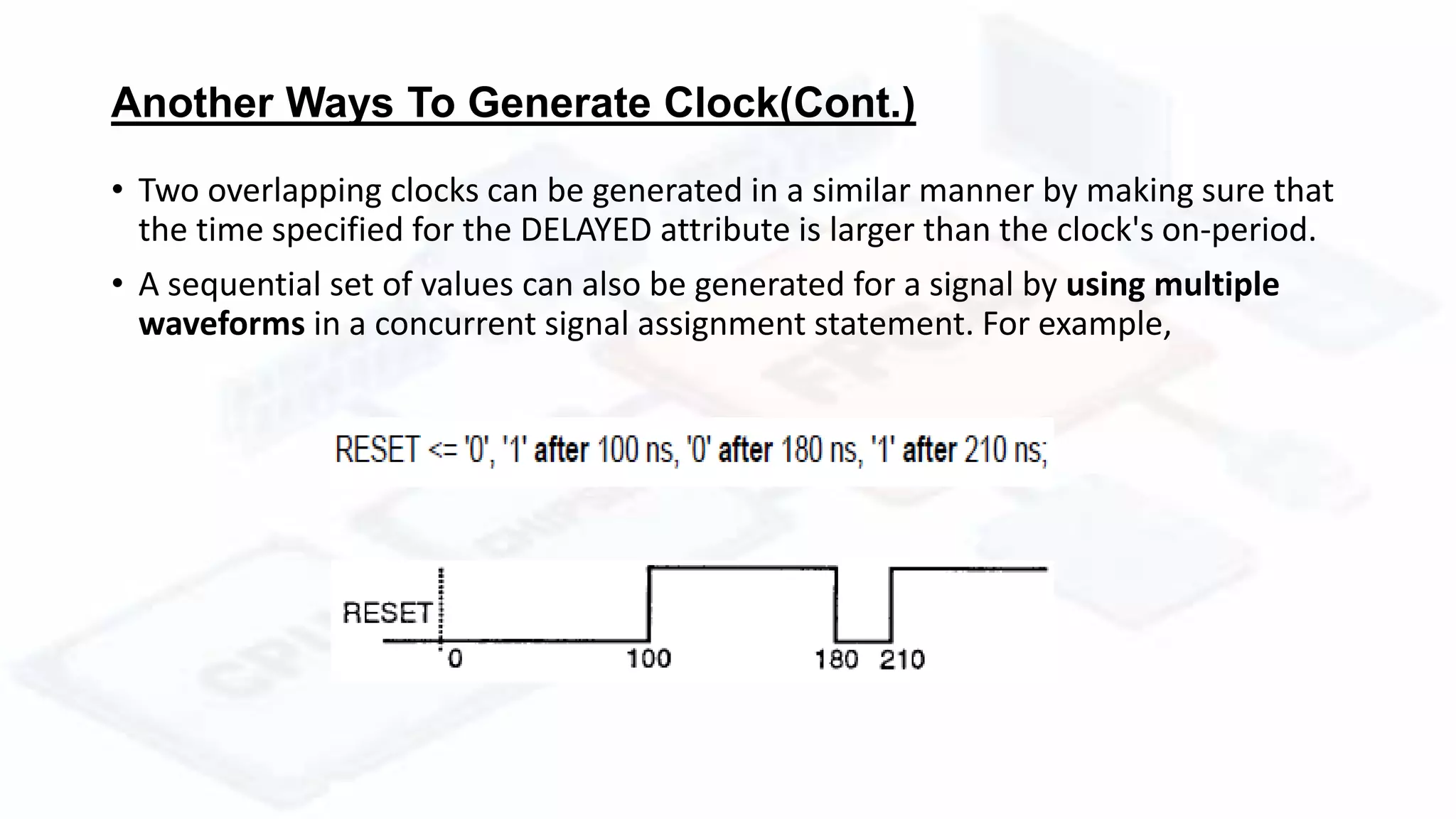
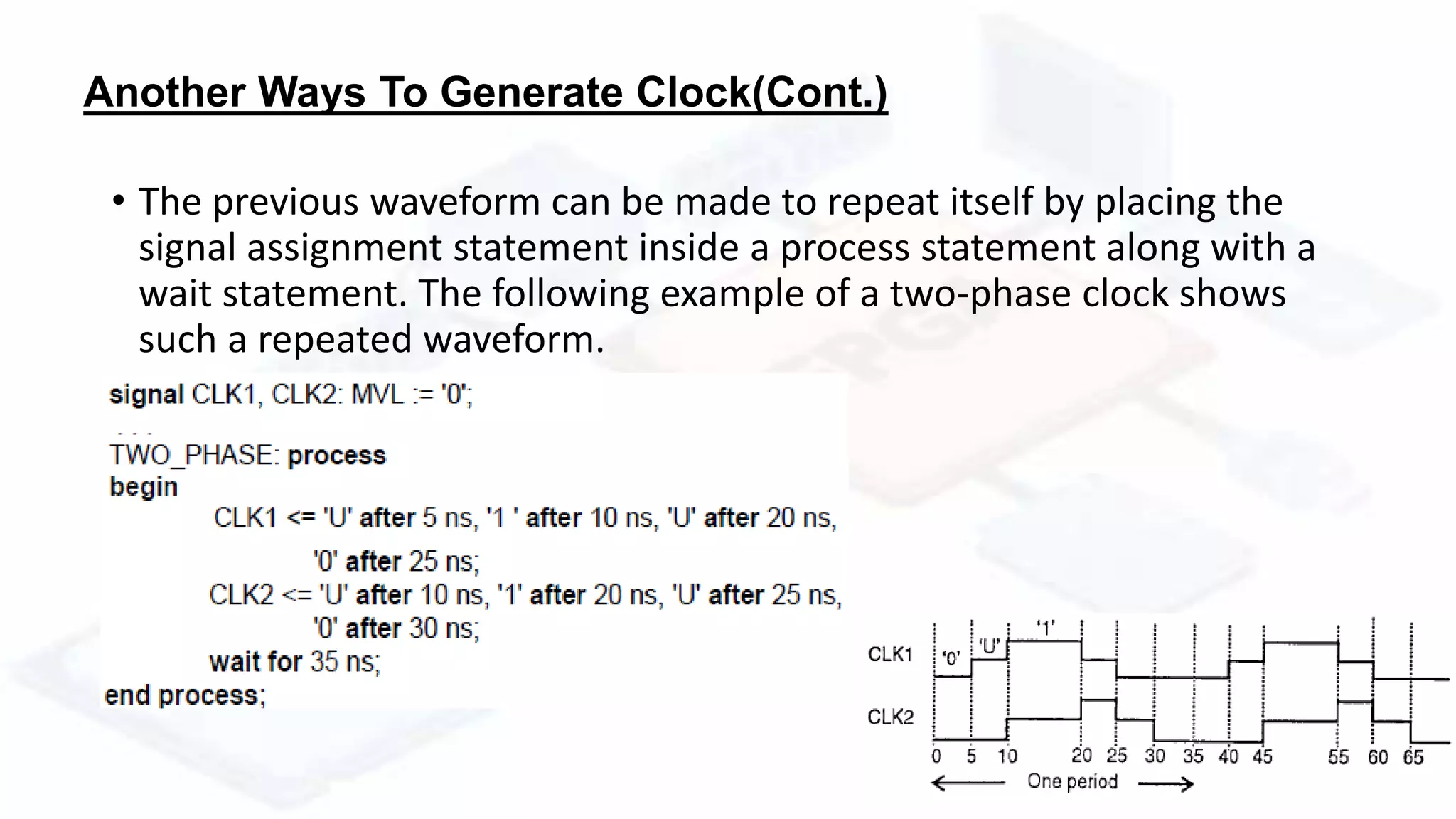
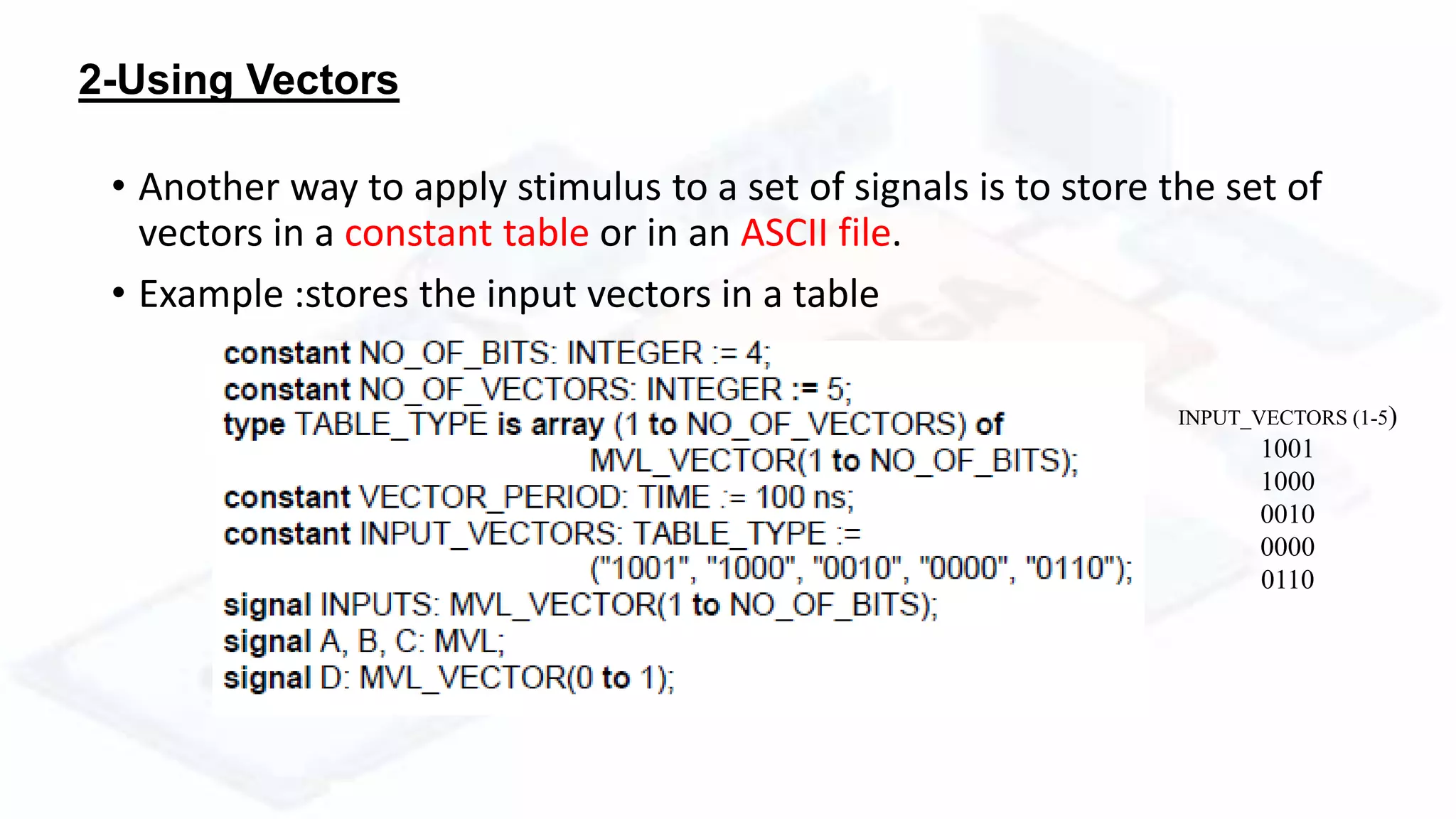
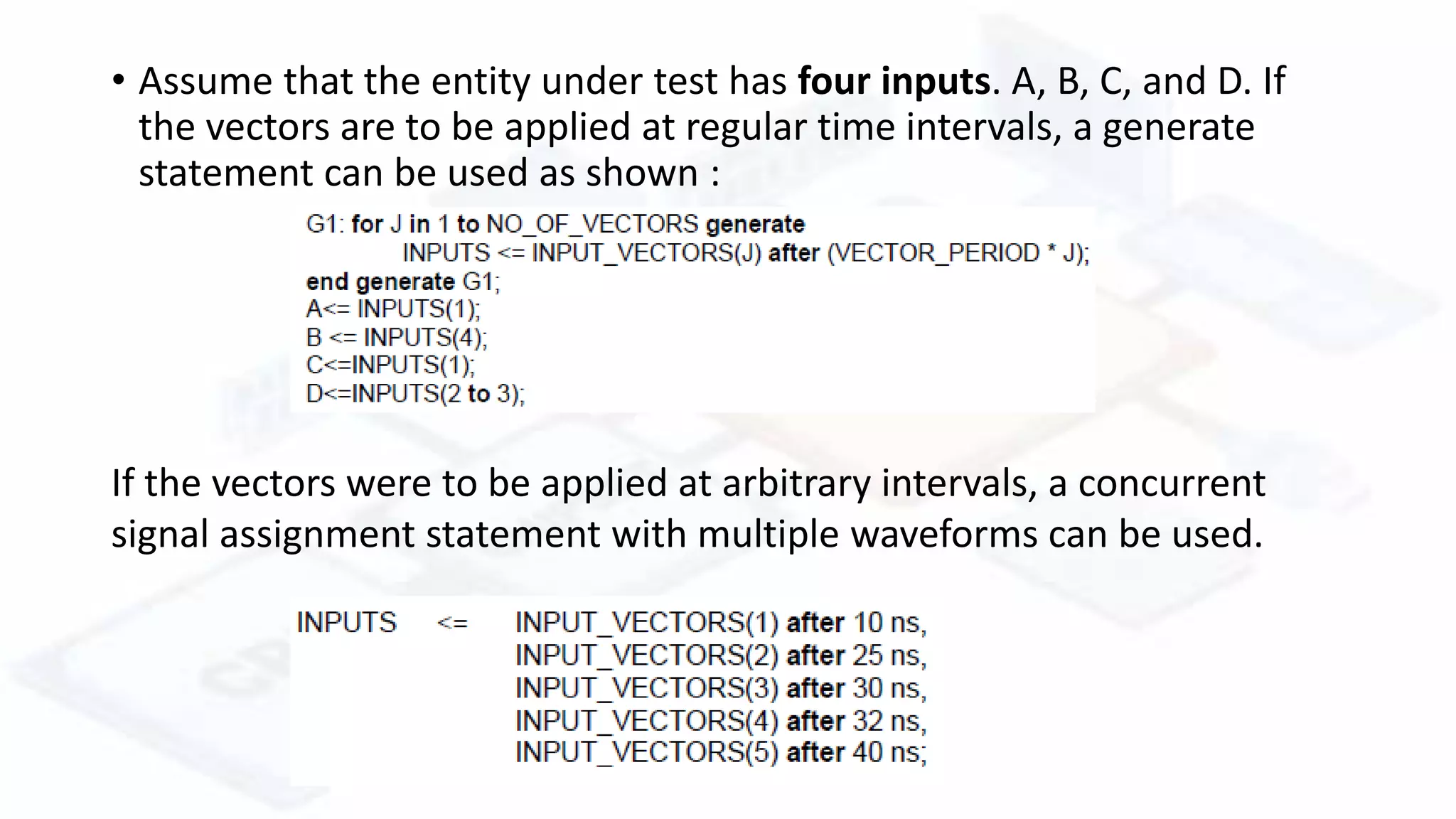
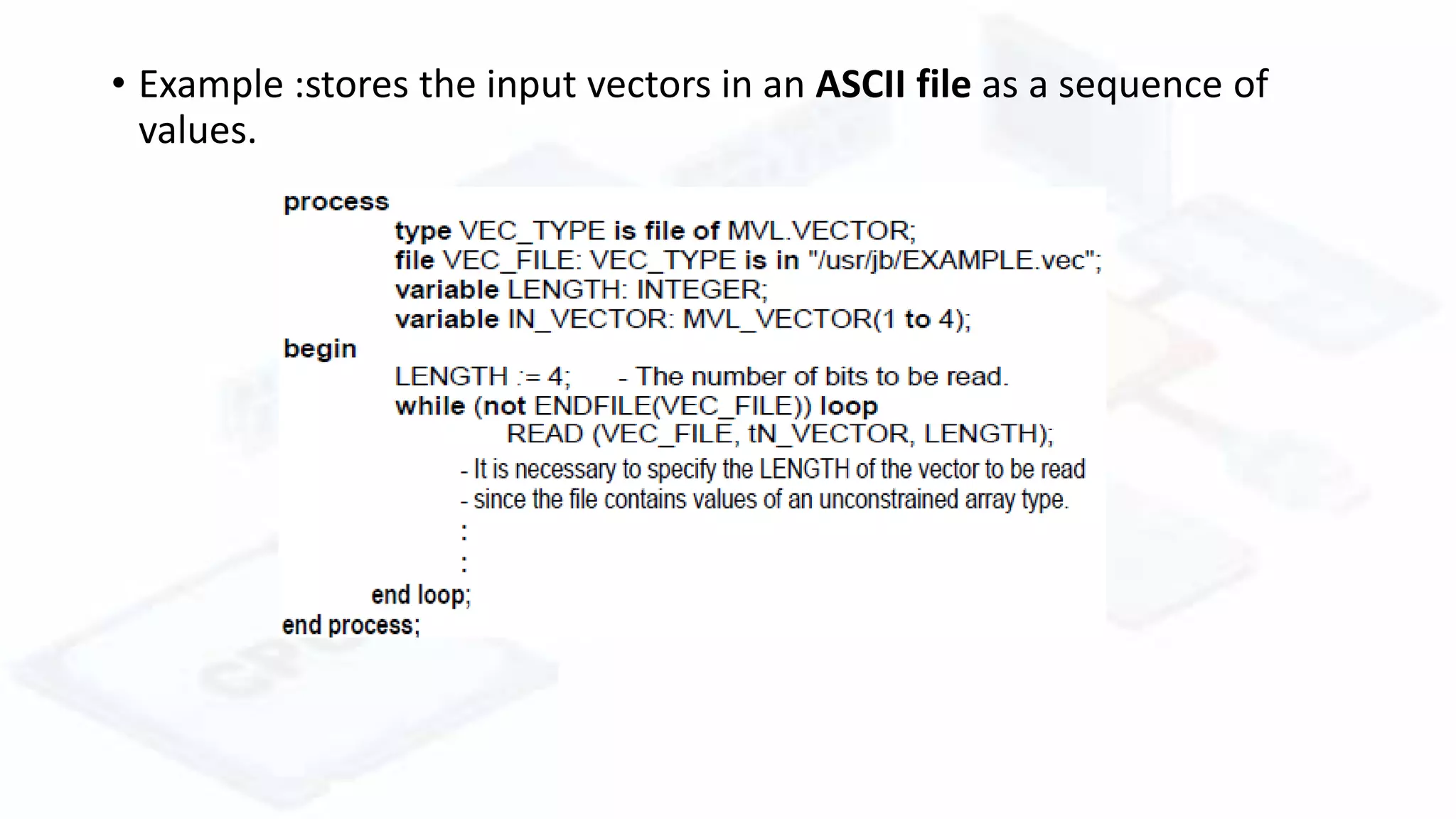
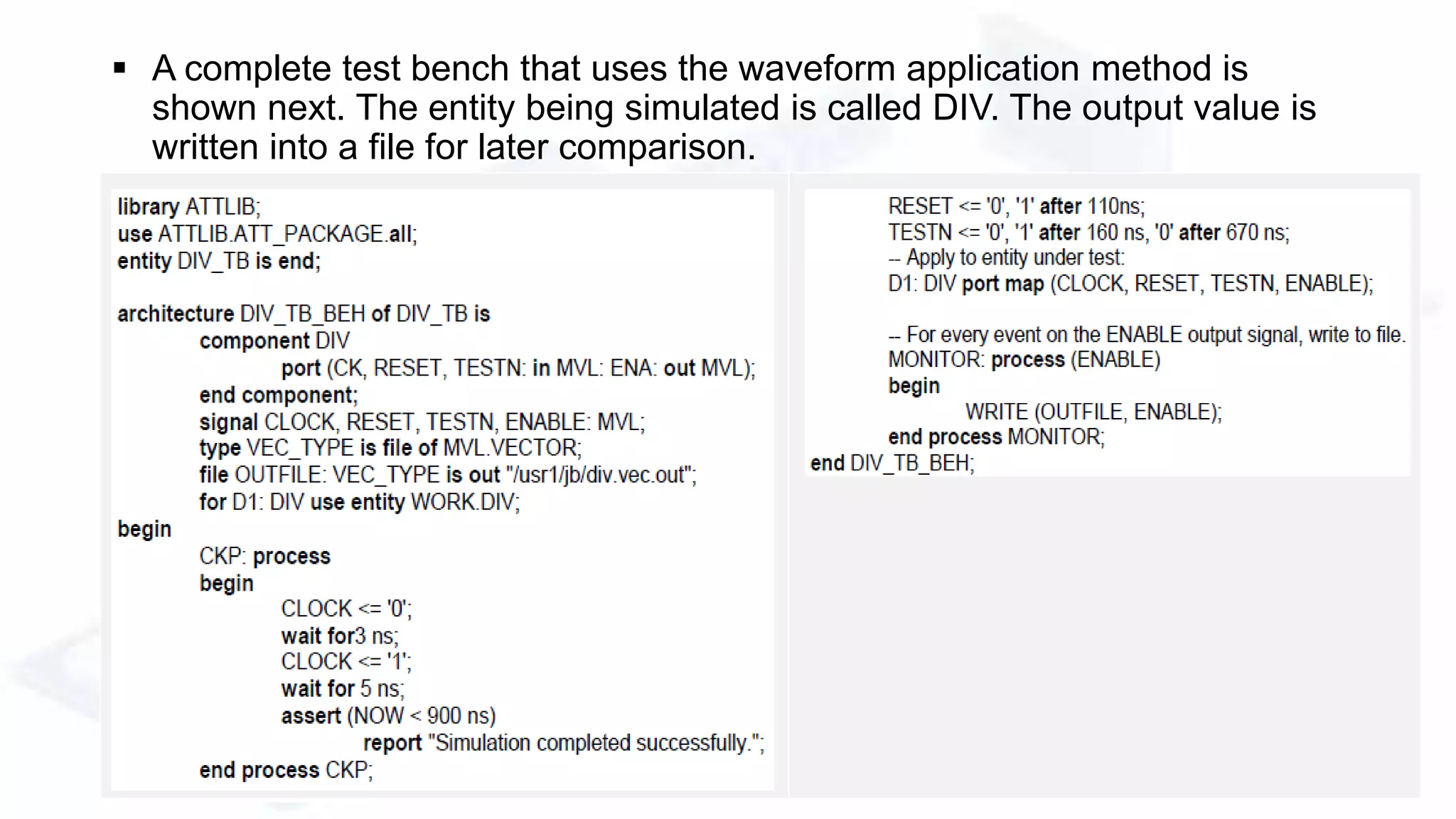
The document describes modeling and simulation of hardware designs in VHDL. It discusses writing test benches to simulate and verify models. Test benches generate stimulus, apply it to the model, and monitor the output responses. Stimulus can be created using repetitive patterns or vectors. Vectors can be stored in tables or files. Assertions are used to check output matches expectations. Monitoring behavior involves applying a vector, sampling output after a delay, and verifying it matches the expected value.
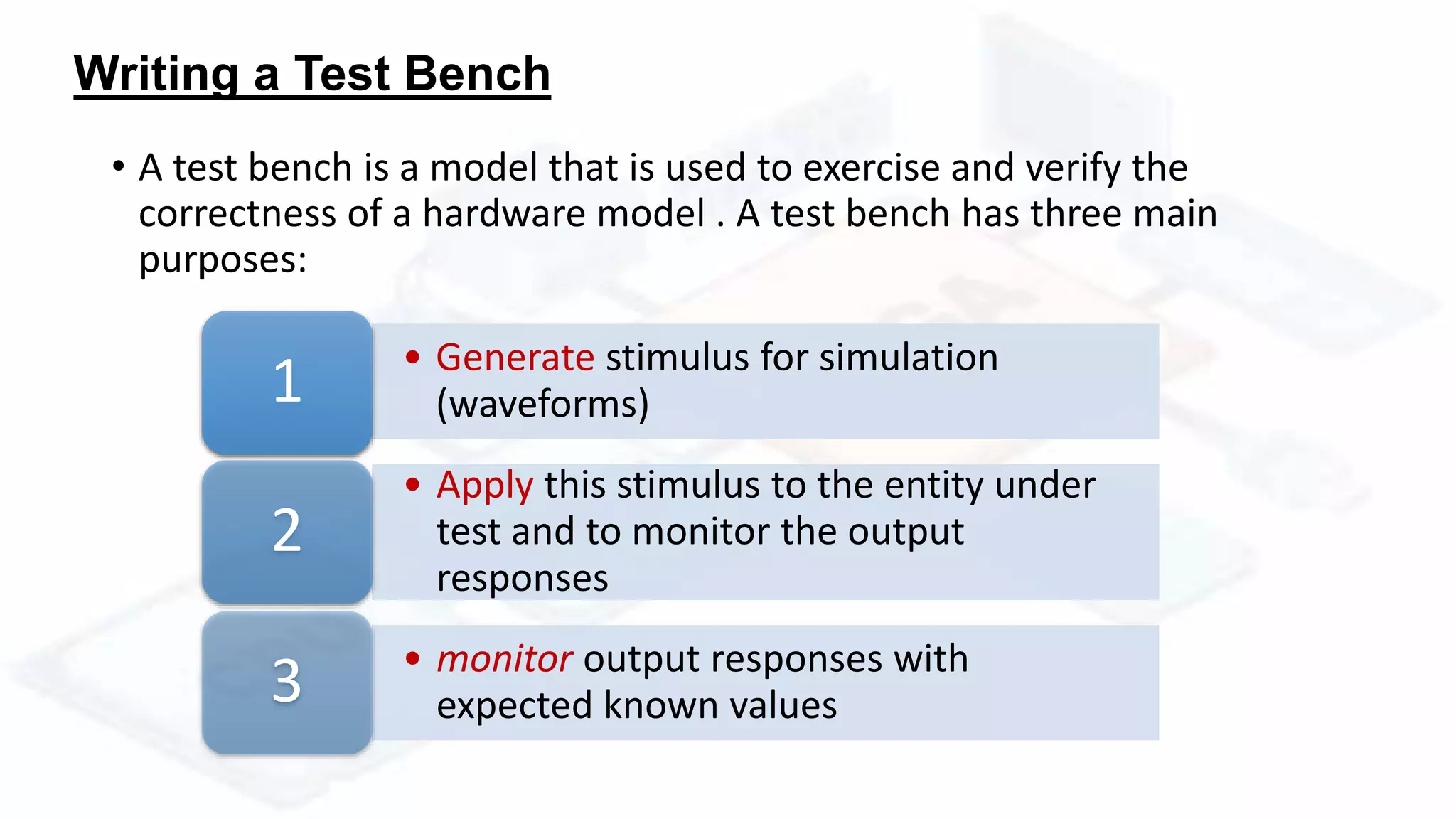
![• Consider an entity in which the objective is to compute the factorial of an
input number. The handshake mechanism between the entity under test
and the test bench model is shown bellow
• RESET input to the entity resets the
factorial model to an initial state.
• START signal is set after the DATA input is
applied.
• DONE signal is set when computation is
complete,
• FAC_OUT and EXP_OUT outputs signals
to indicate output
• . The resulting factorial value is [ FAC.OUT *
2^EXP_OUT ].
Hands on Example](https://image.slidesharecdn.com/modelsimulation-170503172436/75/Model-simulation-VHDL-24-2048.jpg)