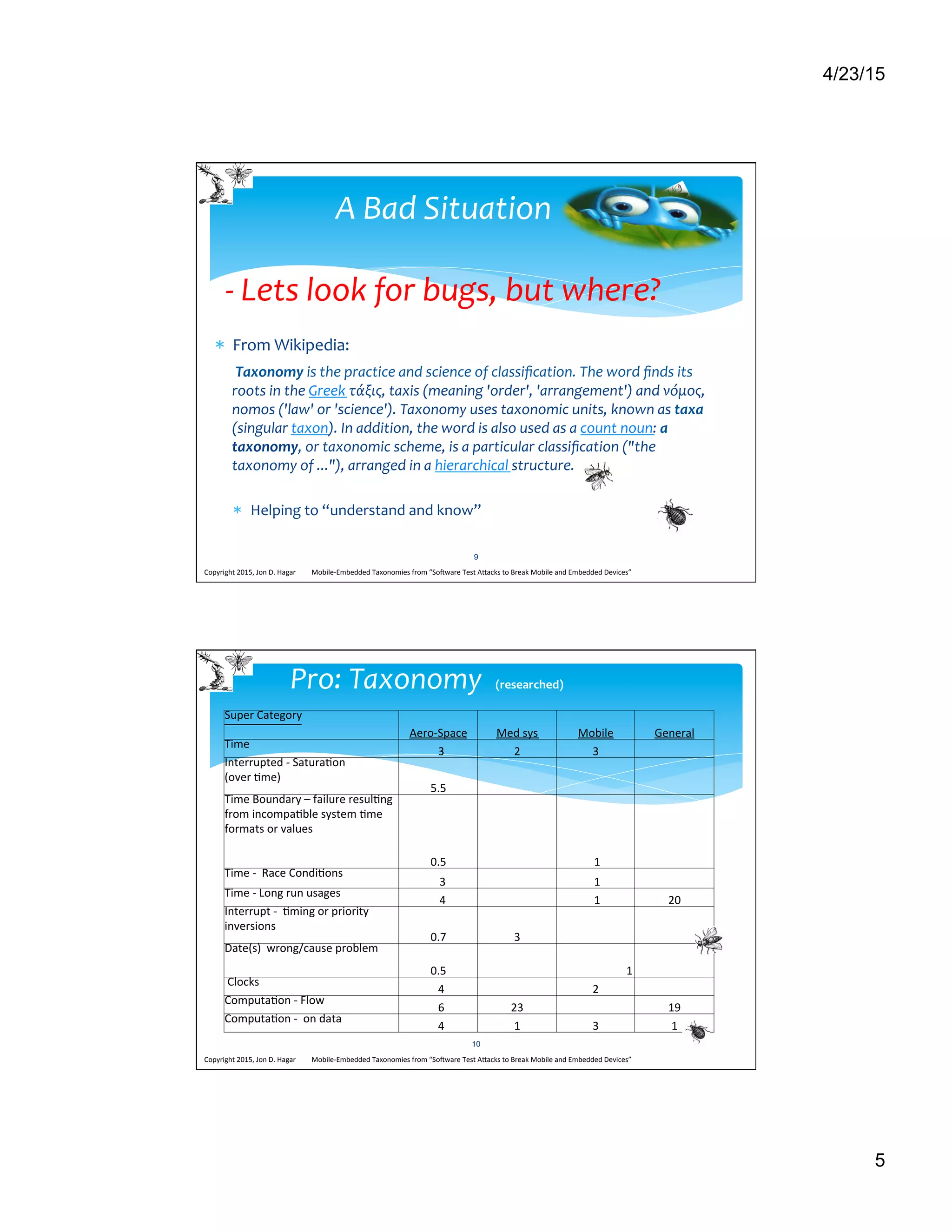
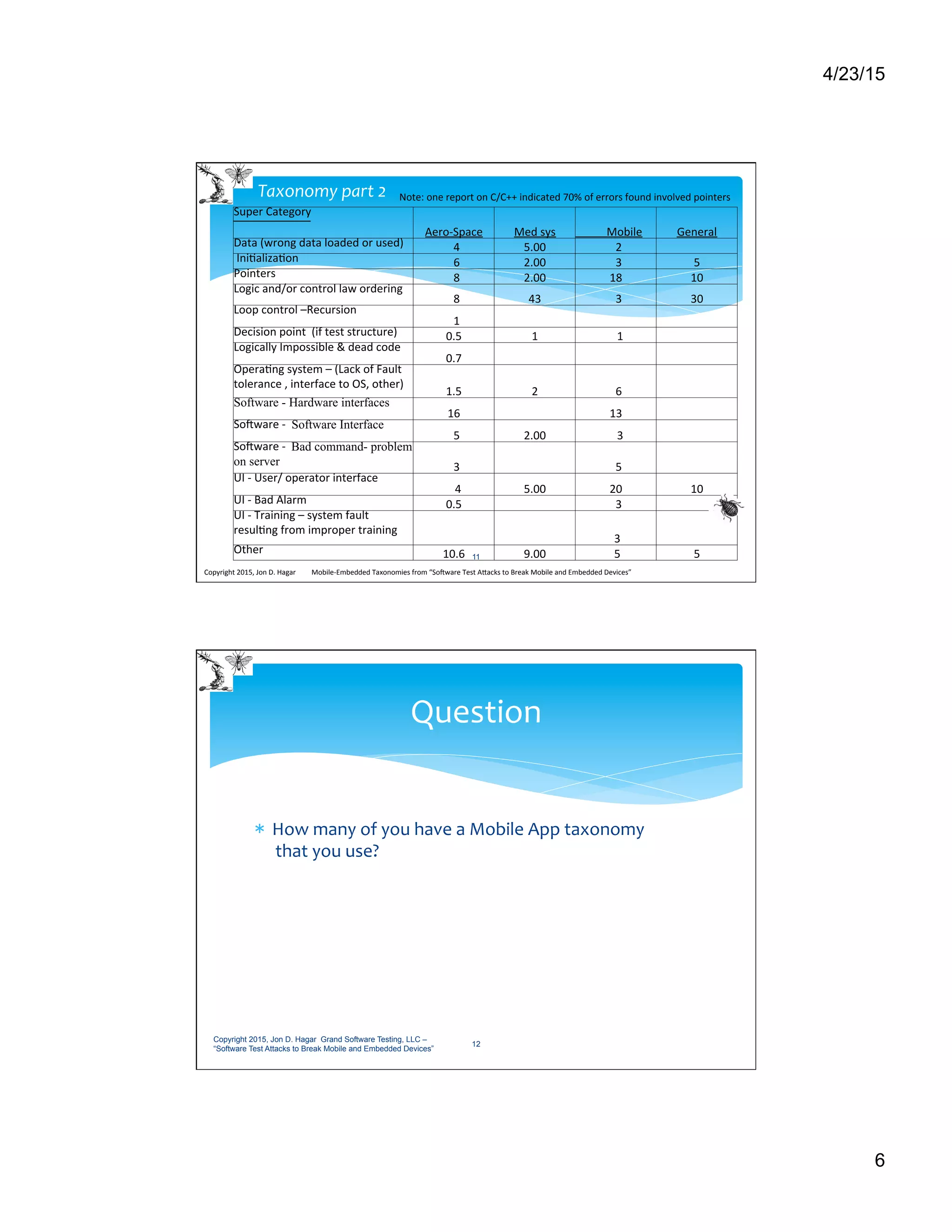
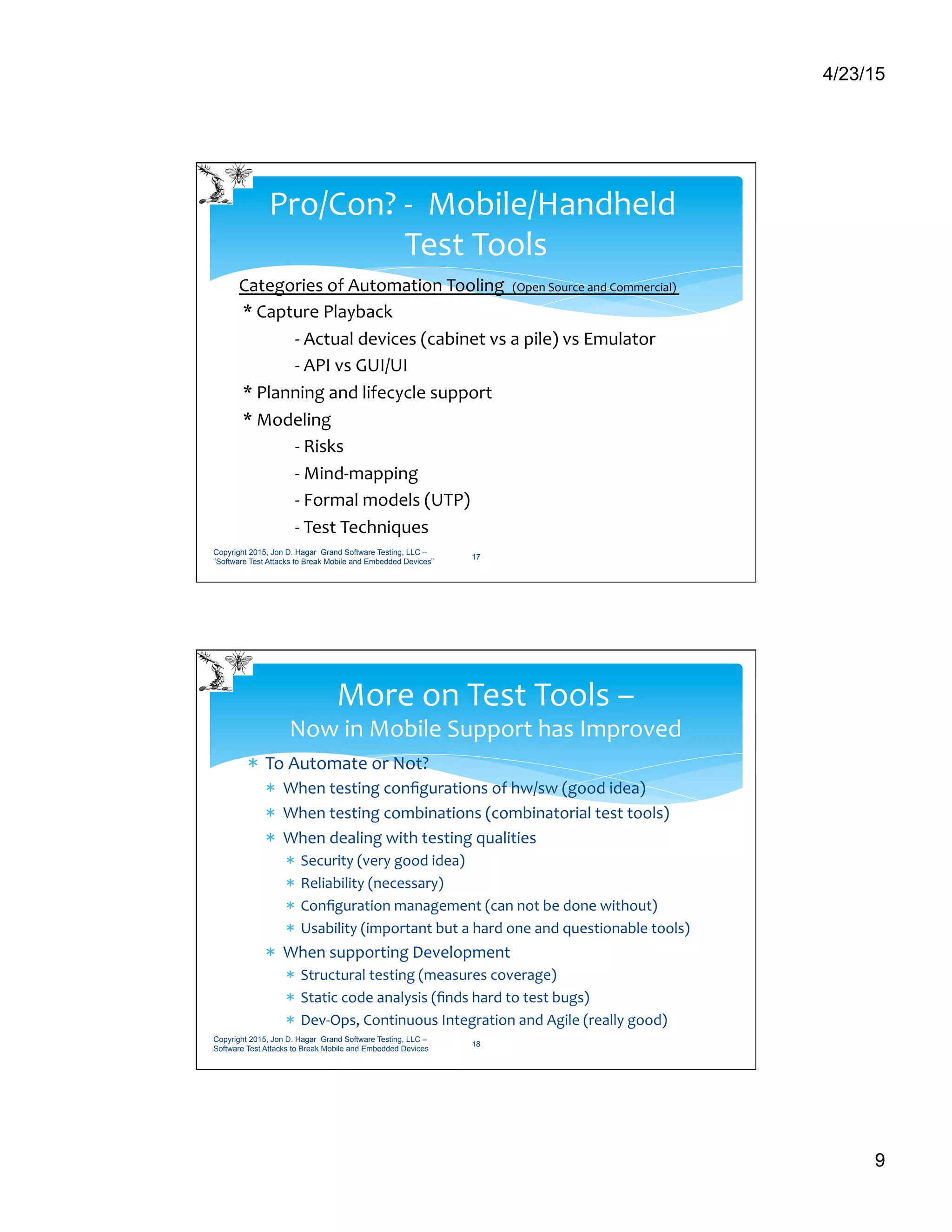
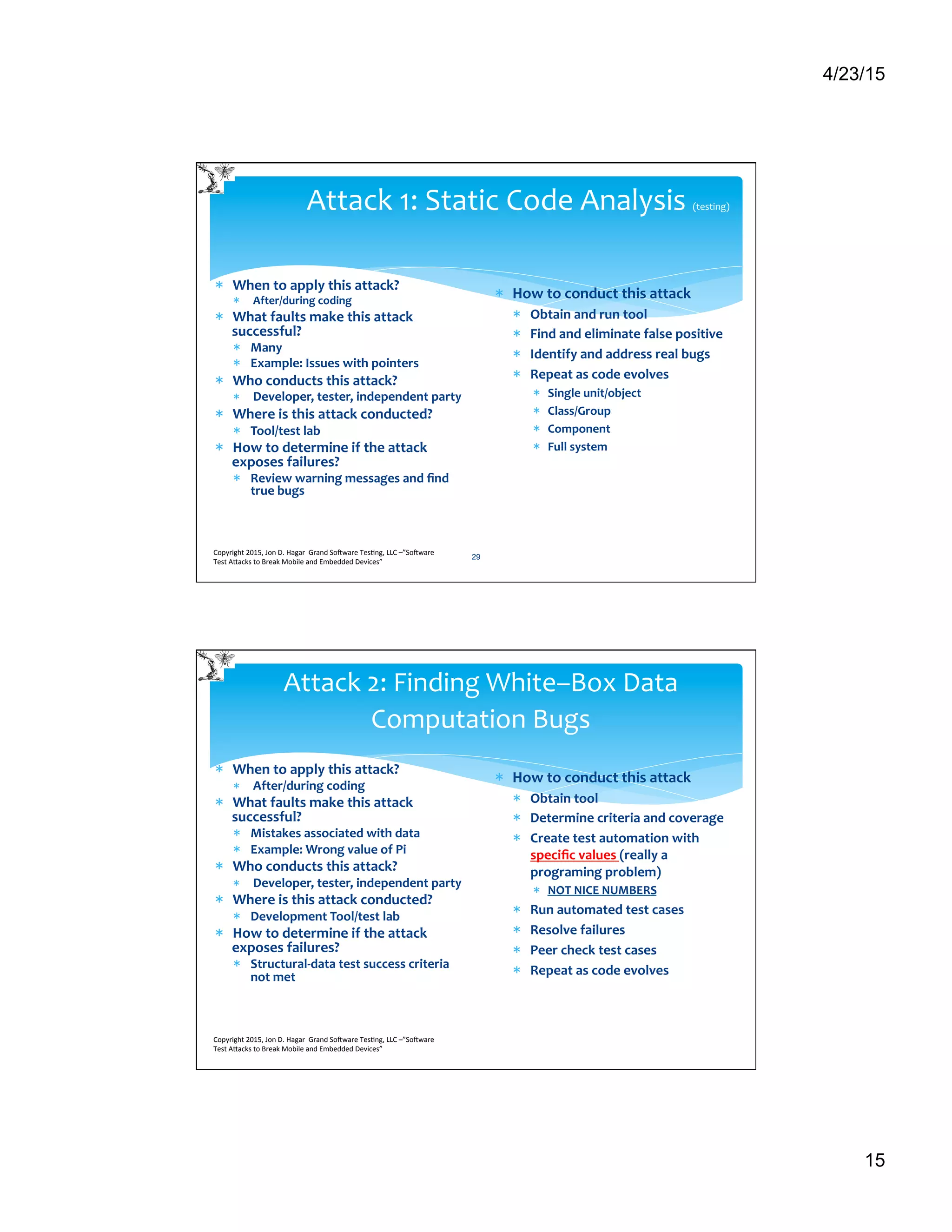
The document discusses mobile application testing and provides examples of issues that can arise. It describes current problems like management not allowing enough testing time or prioritizing speed over quality. This can lead to bugs being missed and poor user experiences. The document also introduces taxonomies to help categorize different types of bugs, like those related to timing, to aid in more effective testing. Overall, it advocates for improved mobile app testing practices to avoid common pitfalls and ensure high quality user experiences.