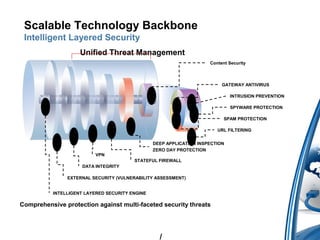
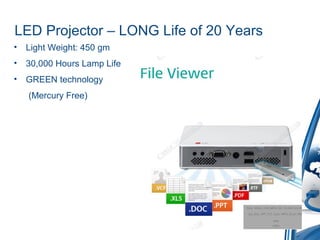
This document discusses education technology solutions offered by Medley Marketing Pvt Ltd including secure wireless networks, computer labs, CCTV surveillance, smart classrooms, digital notice boards, internet security, storage solutions, and video conferencing. It provides details on wireless networking products, centralized management, intelligent security engines, application controls and content filtering. Product information is given for surveillance cameras, digital signage, interactive whiteboards, LED projectors, and training room solutions. Contact information is provided for further discussions.