Embed presentation
Downloaded 72 times


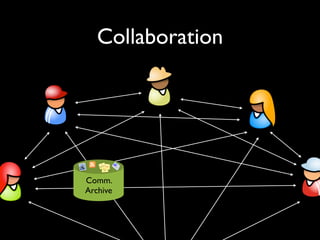
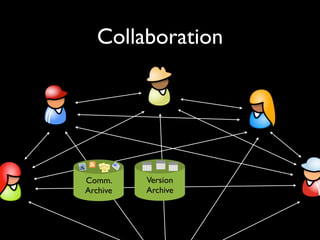
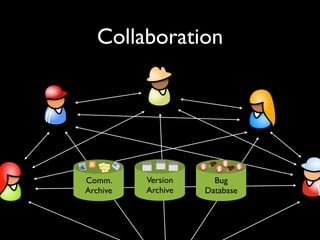
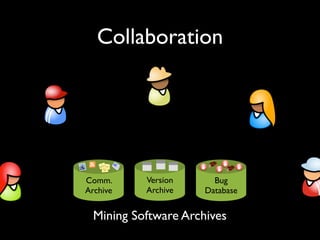



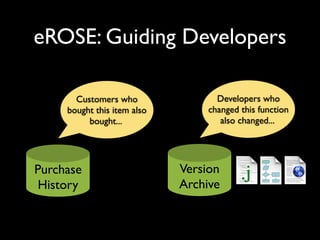
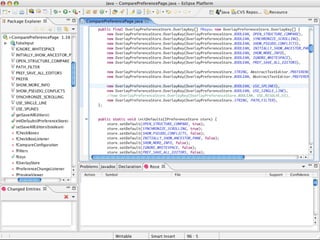
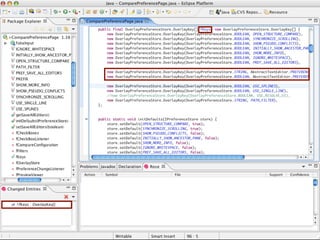
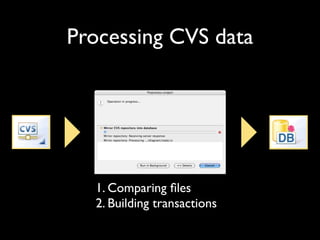
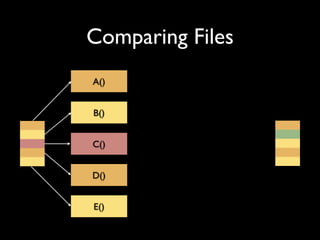
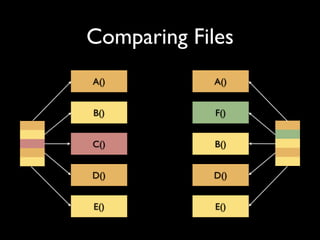
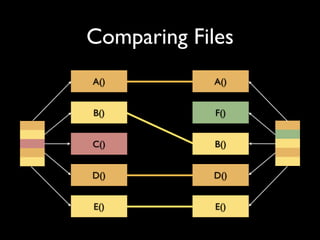
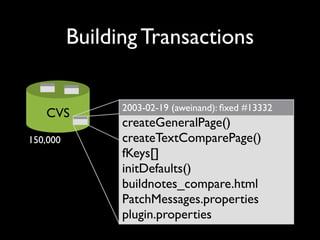
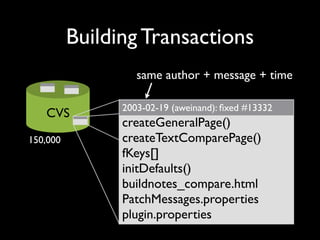

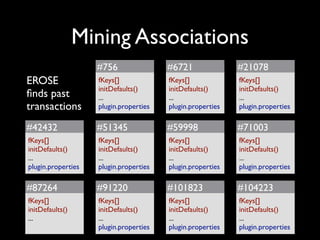



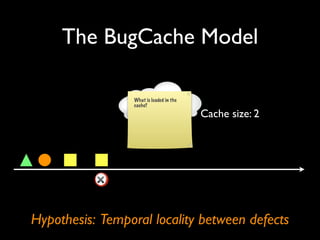
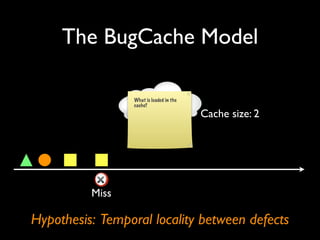
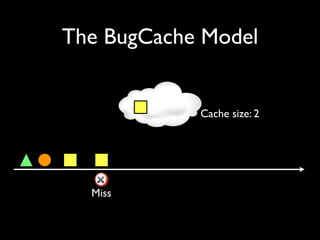
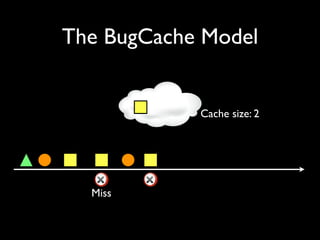
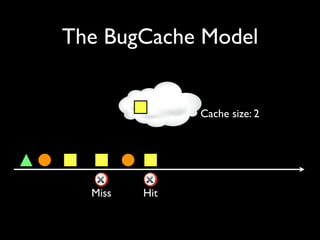
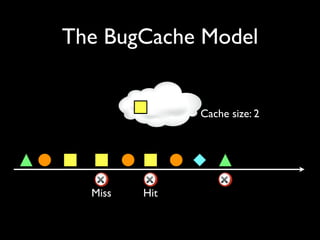
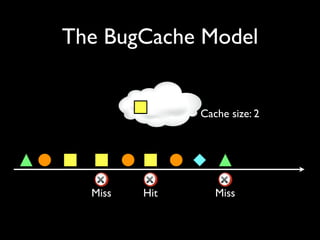
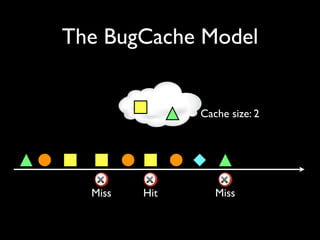
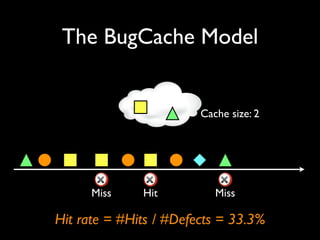
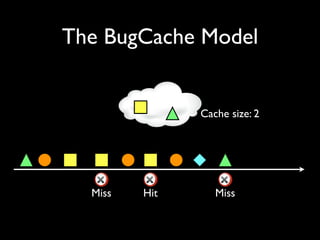
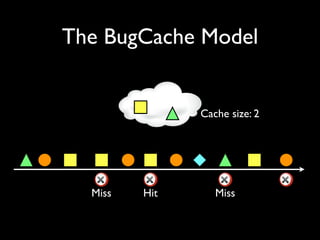
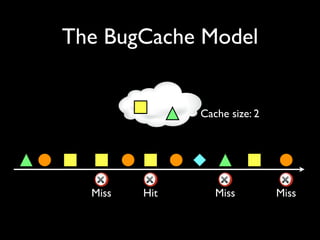
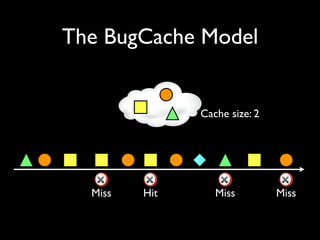
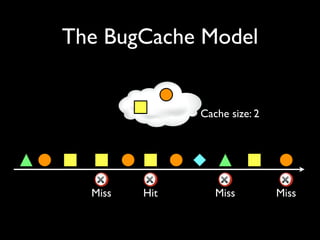
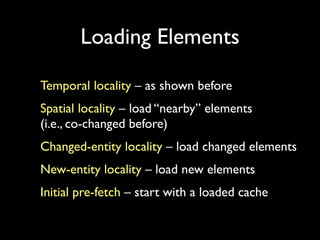

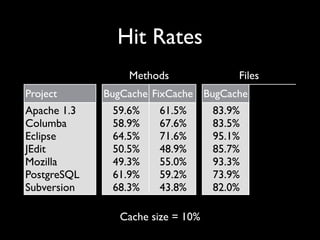
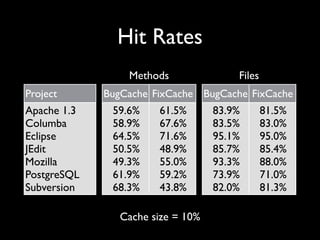
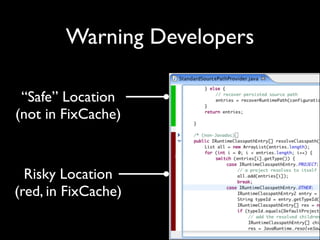

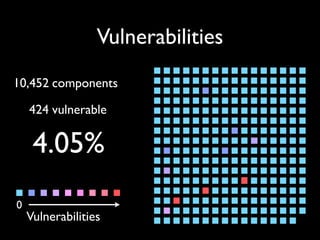
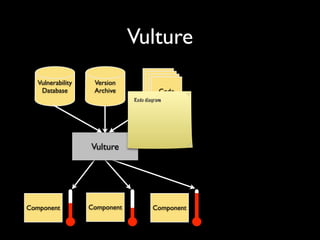
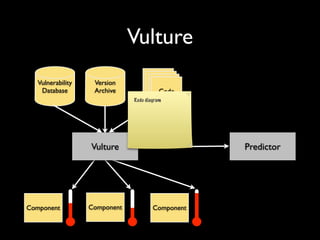
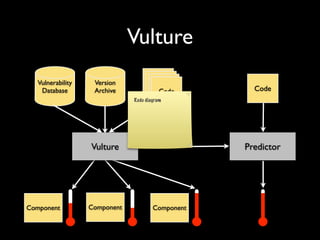

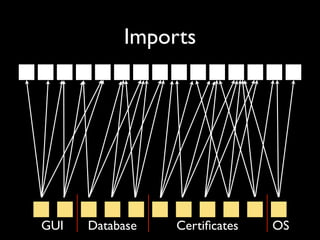
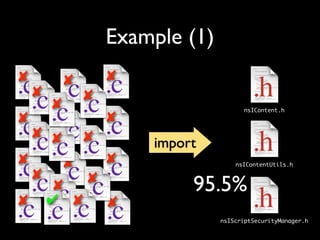
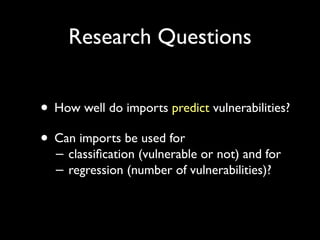
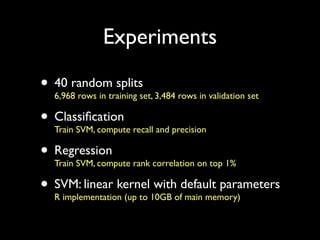
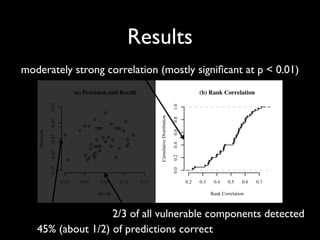
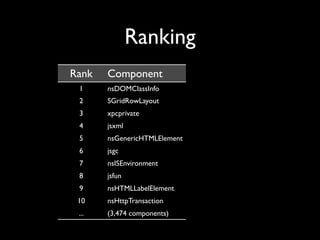
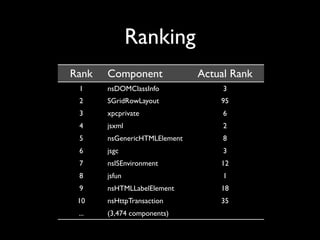
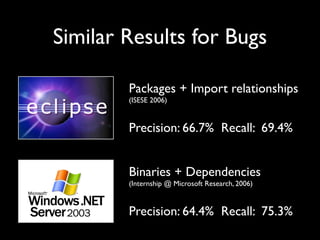




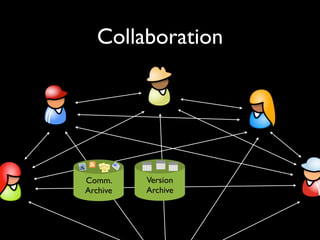
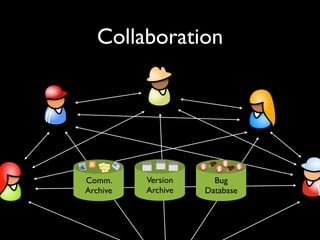
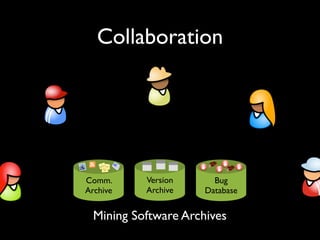
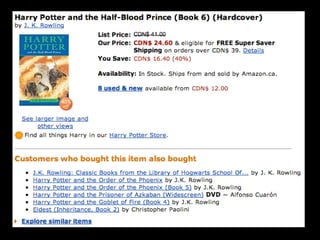
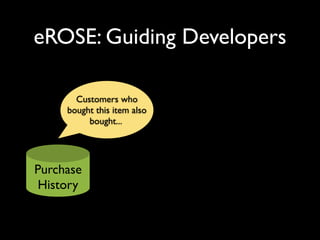
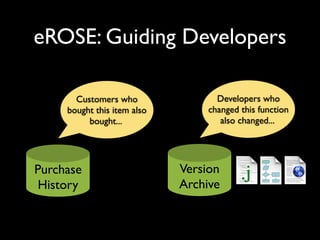
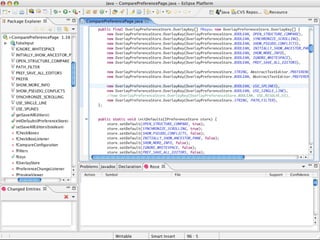
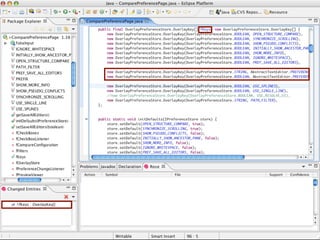
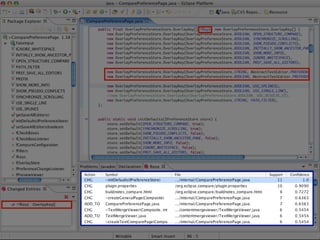
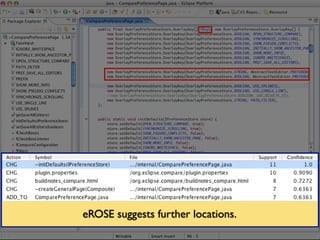
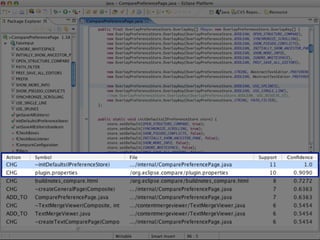
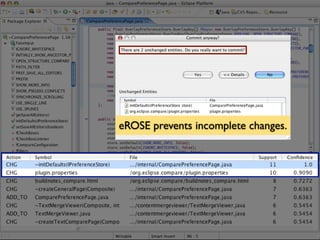
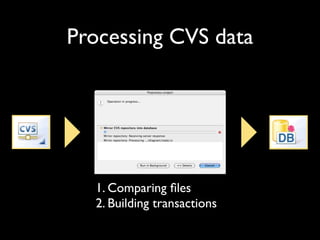
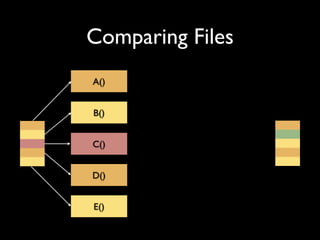
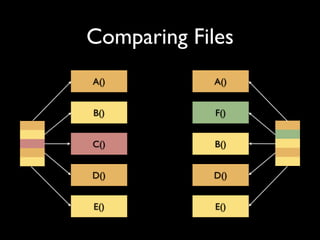
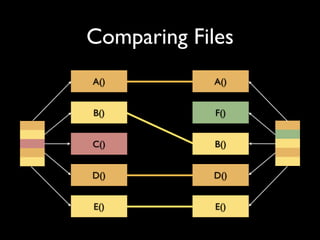
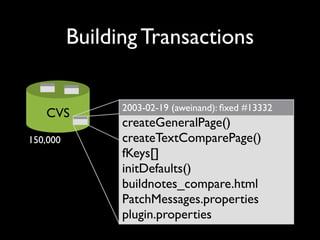
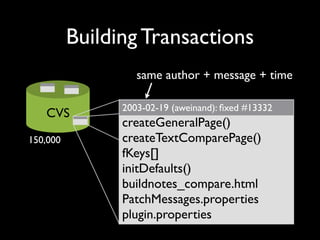
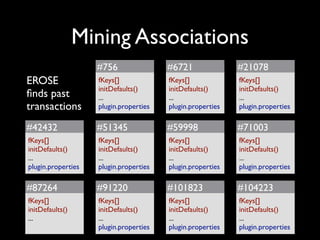
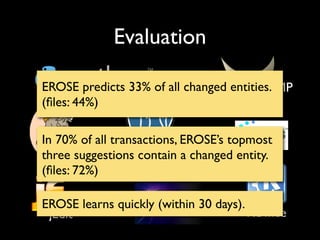
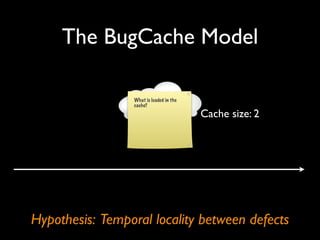
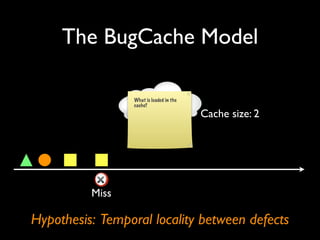
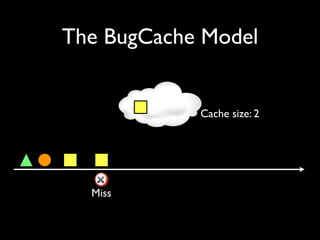
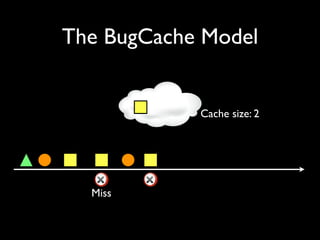
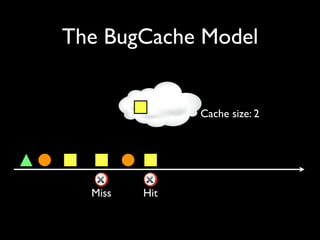
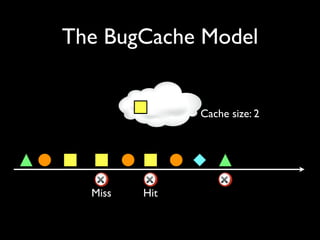
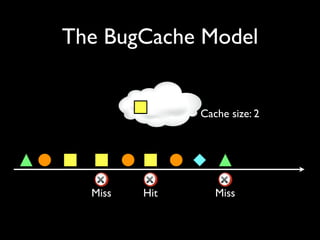
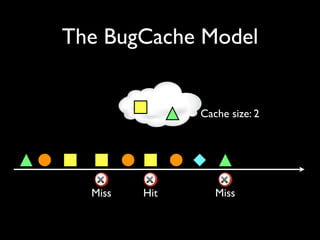
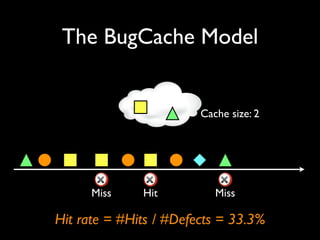
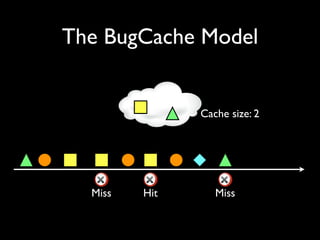
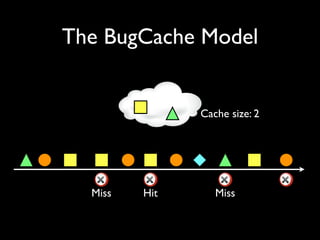
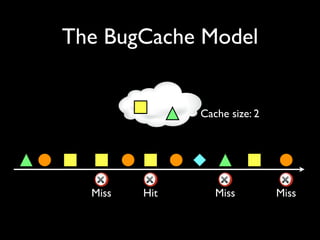
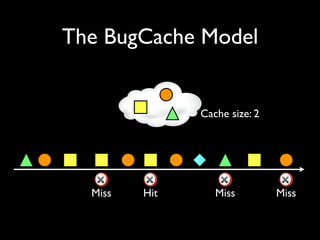
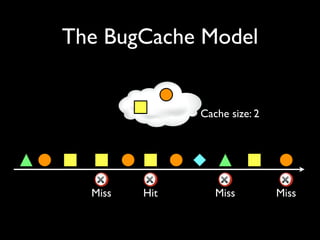
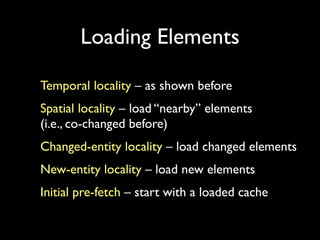
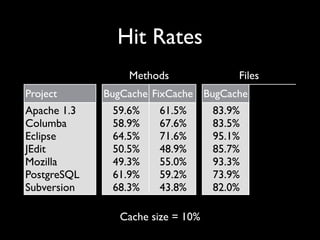
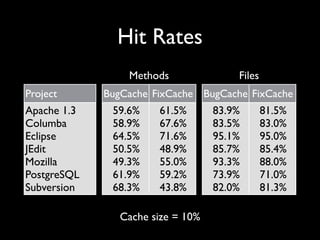
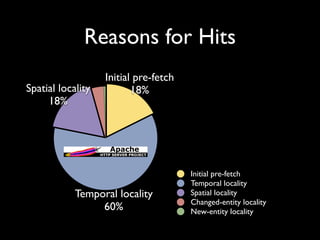
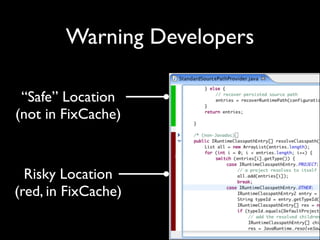
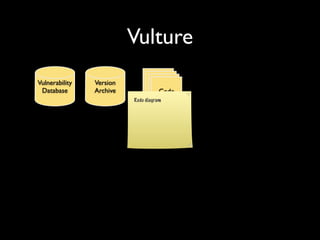
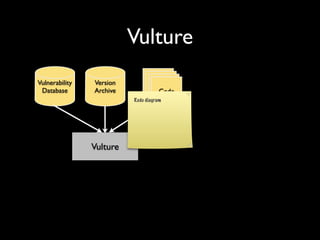
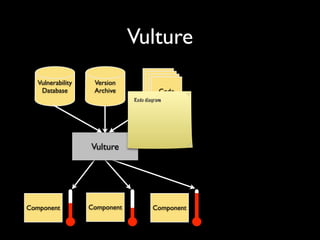
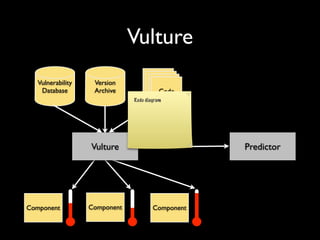
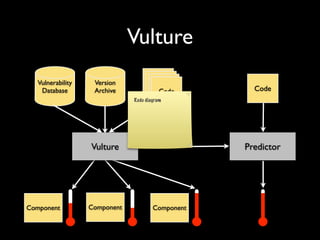
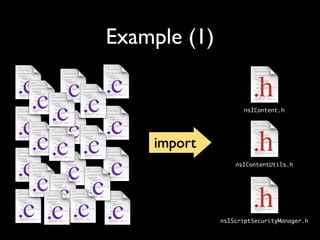
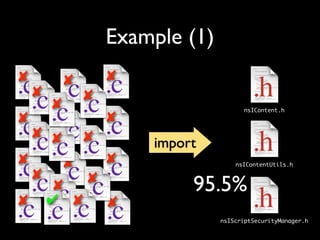
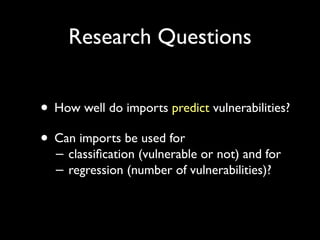
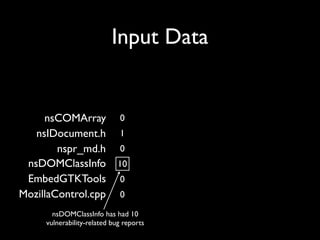
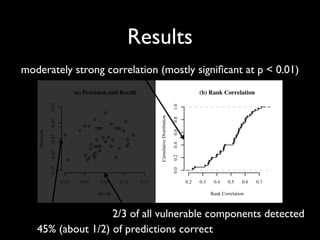
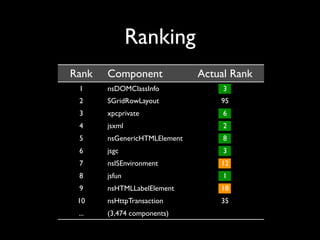
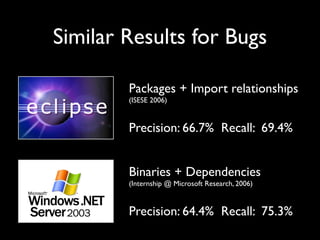
1. The document discusses mining software archives and repositories to help guide software developers and predict defects. 2. It describes the eROSE tool which mines past associations between code changes to suggest related files and locations to developers. 3. The BugCache model predicts future defects based on the hypothesis that defects are temporally local, with a cache that loads elements likely to have defects.