This document provides a sample cloud applications security and operations policy to guide organizations in developing security policies for cloud applications. It includes sections on authentication and administration, auditing, business continuity, data security, communication security, vendor governance, and brand reputation. For each section, it outlines baseline requirements and additional requirements for applications handling data at different security levels (1-3), based on the potential impact of unauthorized access. The goal is to balance security and usability by applying more stringent requirements to higher risk or sensitive data.
![V 1.0 ©2015 LinkedIn Corporation. This document is licensed under a Creative Commons Attribution-
NonCommercial-ShareAlike 4.0 International license.
4
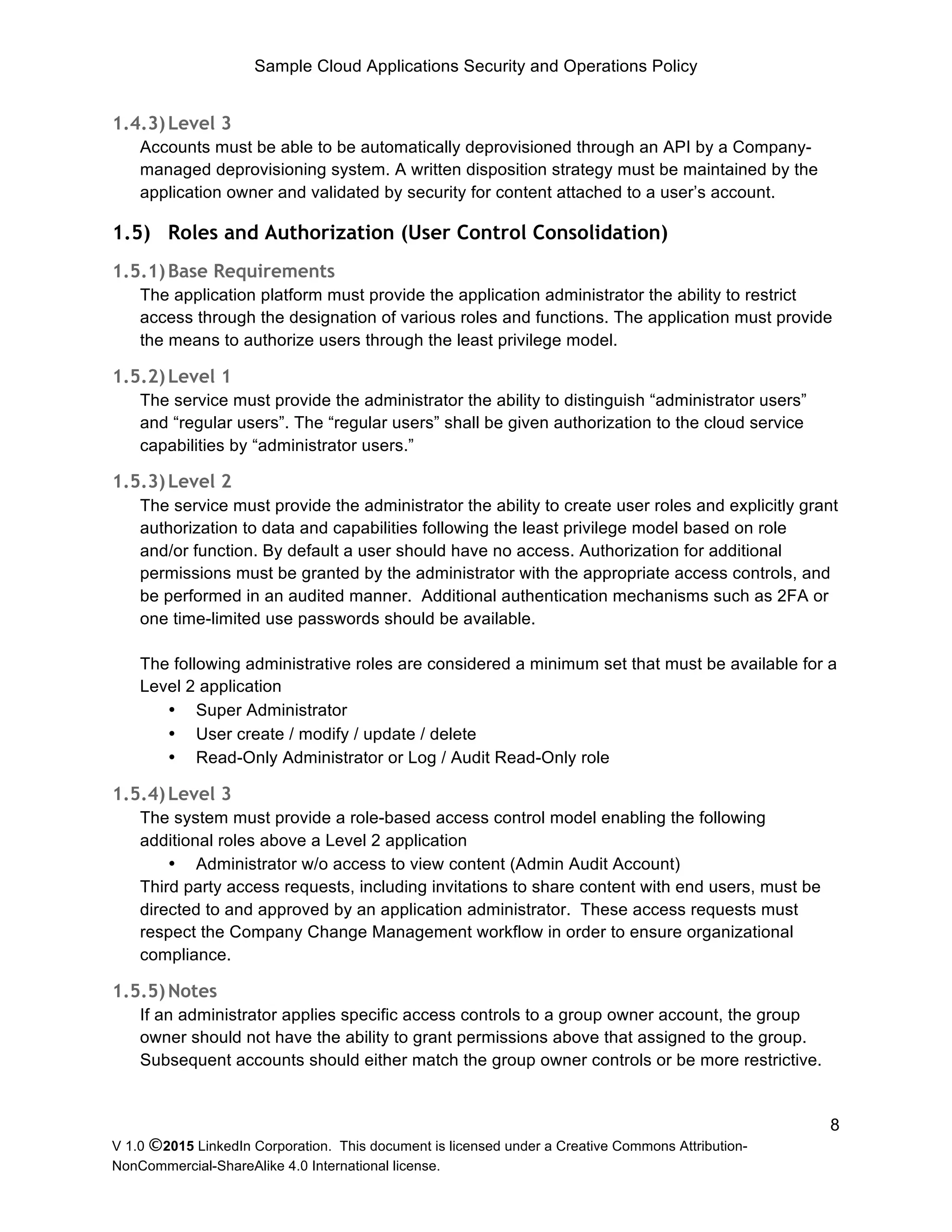
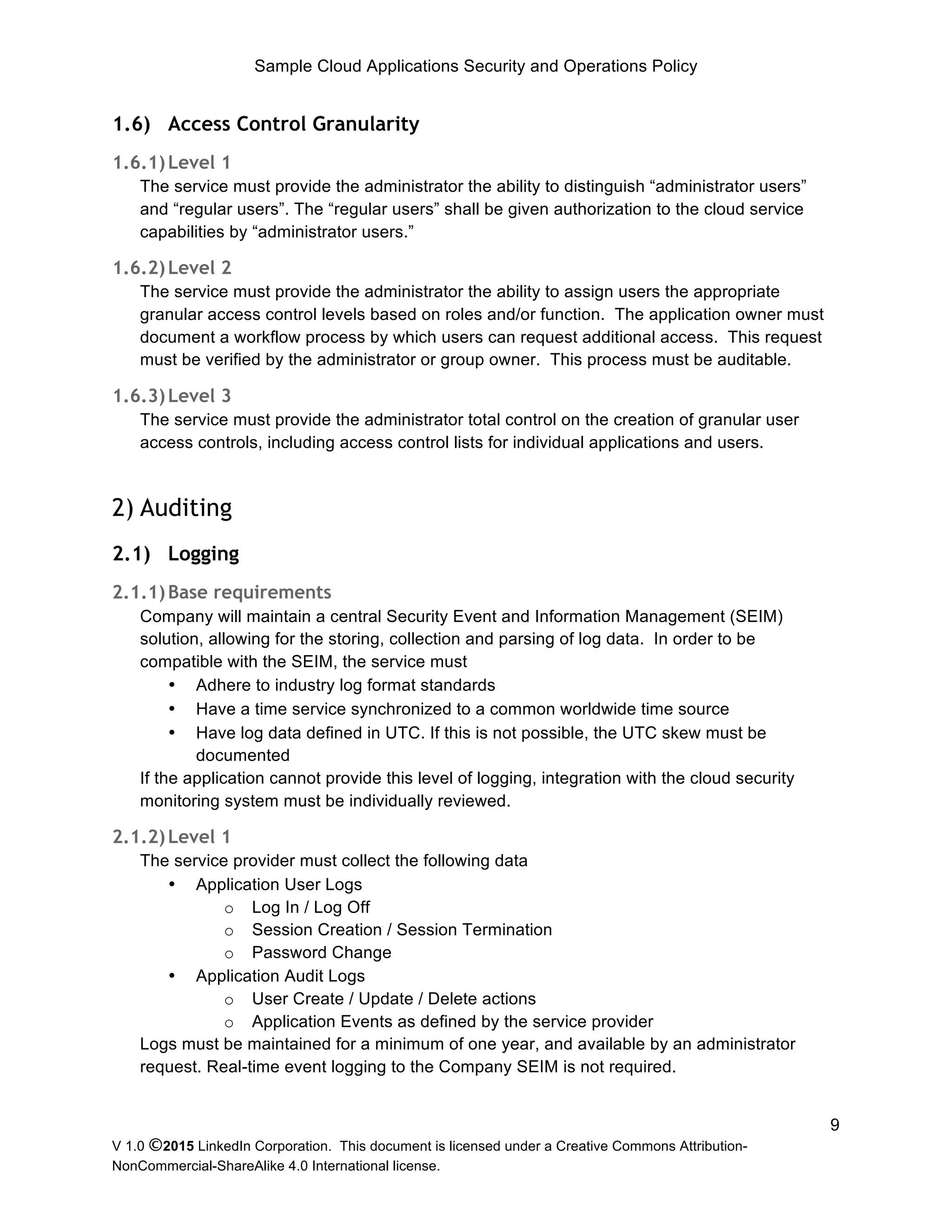
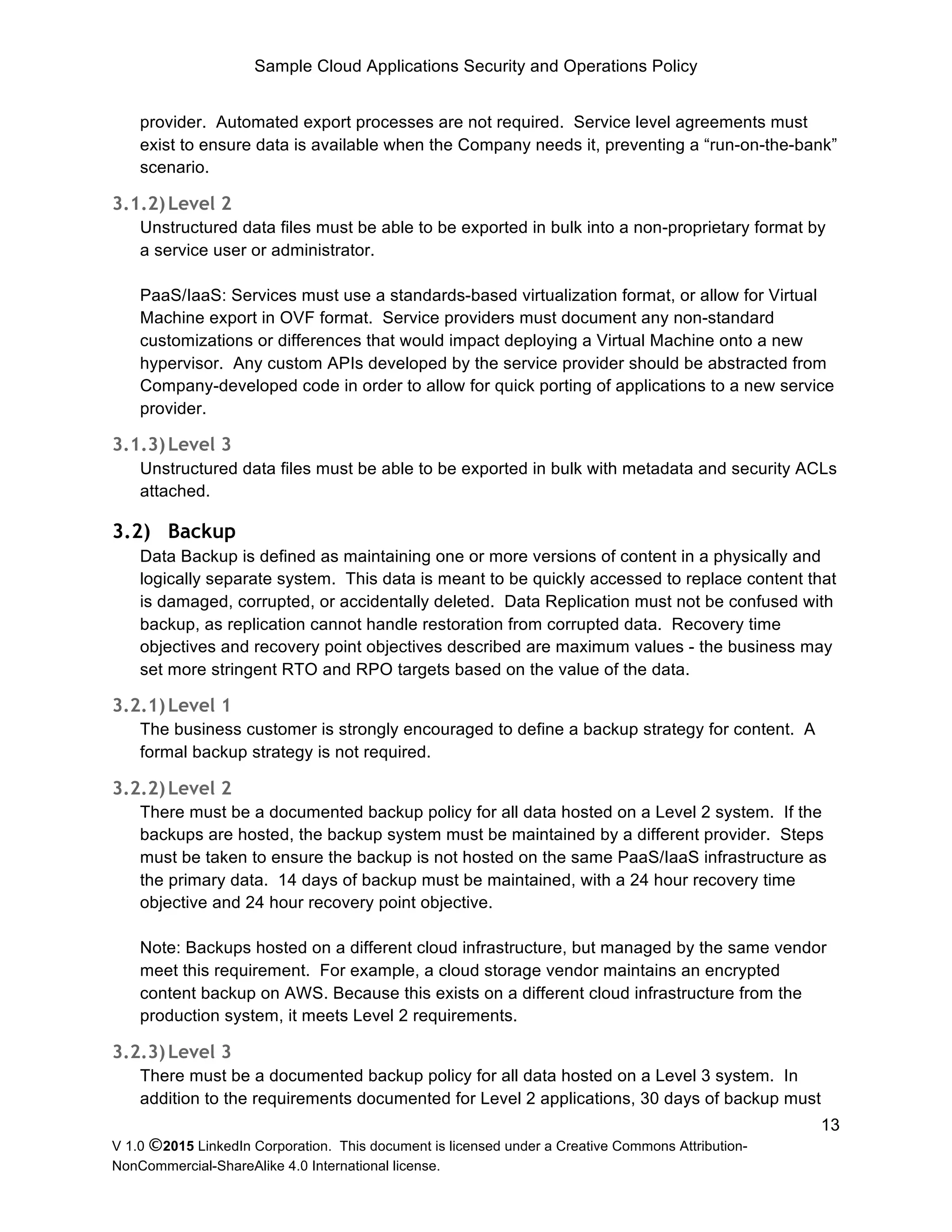
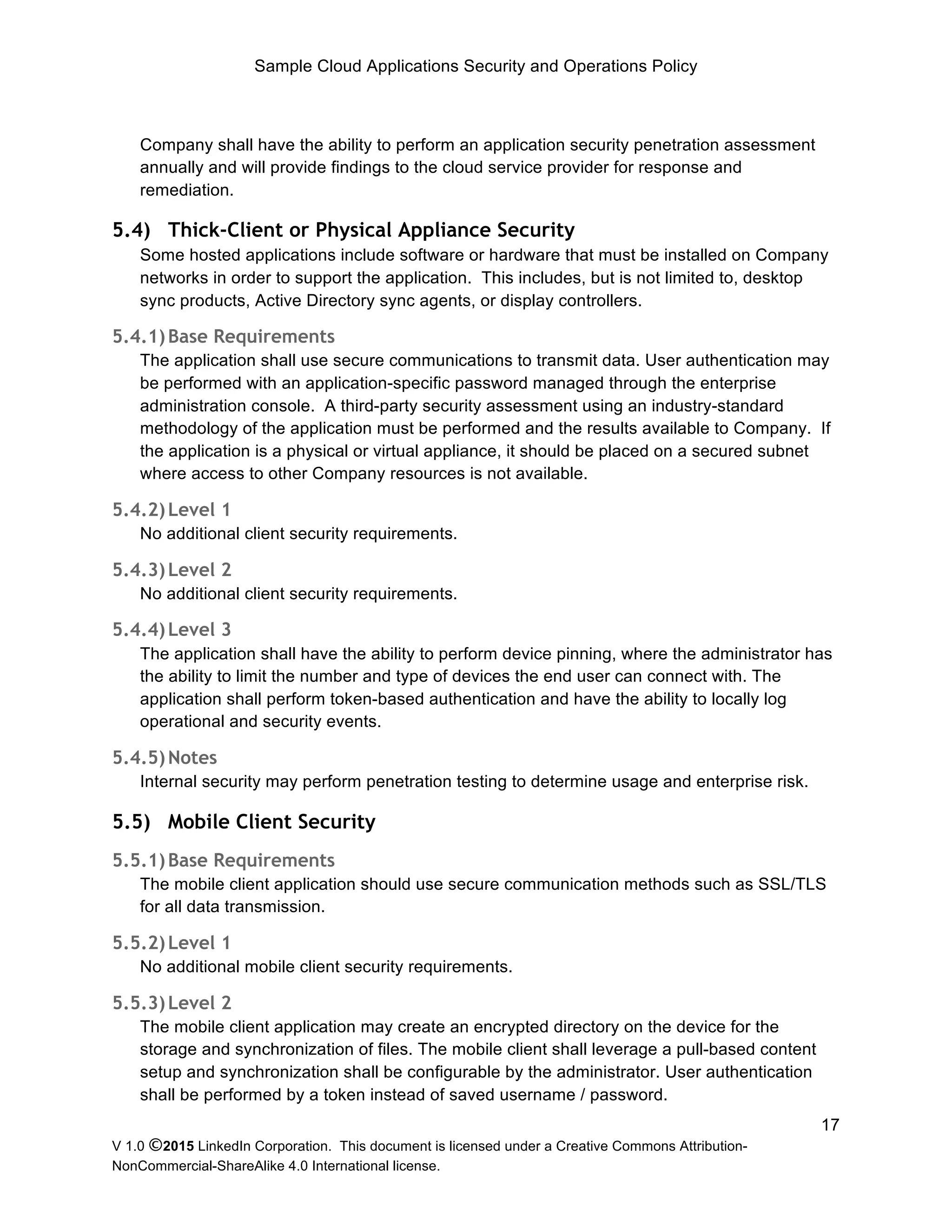
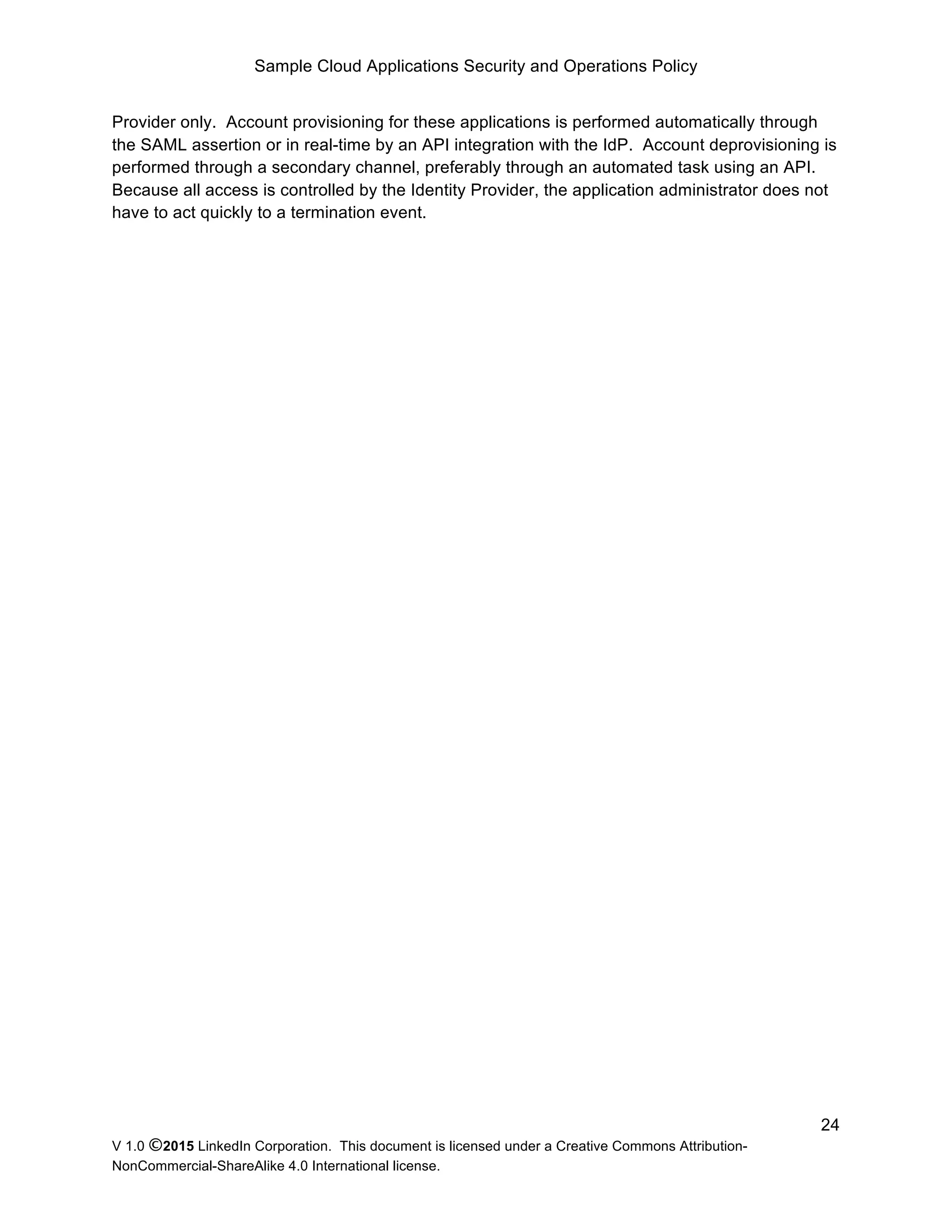
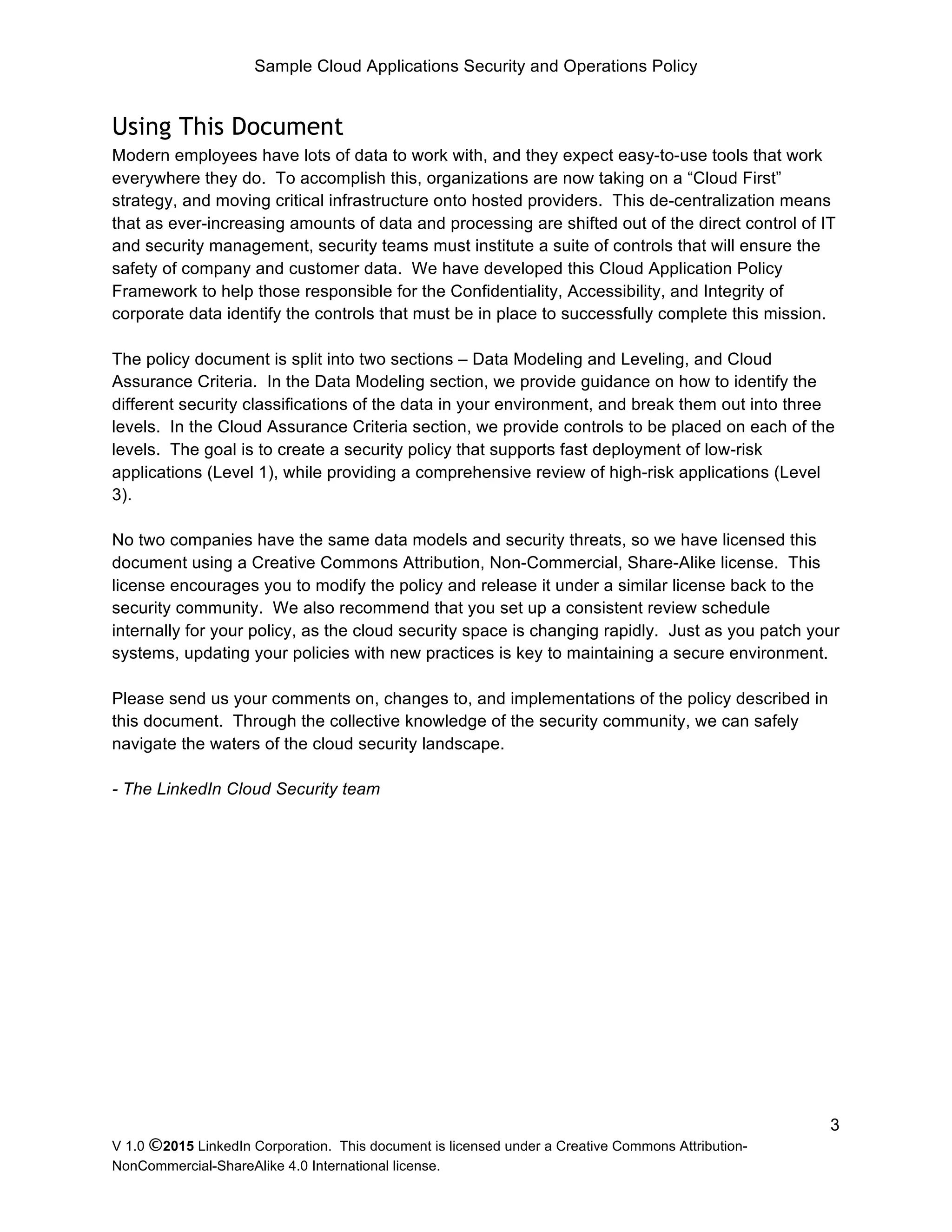
Data Modeling and Leveling
In order to develop a balance between security and usability, the policy has been written to
support three levels of application security, based on the US NIST 800-60 framework. NIST
800-60 assists administrators with classification of their data by defining the potential impact
unauthorized disclosure, modification, and disruption would have on the business. Begin by
identifying the different data types used in your organization. Most organizations will have 3
data types, representing data belonging to the Corporation, data belonging to Employees, and
data belonging to Customers. Once classified by type, objects should be classified by potential
impact, as defined by the NIST framework.
POTENTIAL IMPACT
Security Objective LOW (Level 1) MODERATE (Level 2) HIGH (Level 3)
Confidentiality
Preserving authorized restrictions
on information access and
disclosure, including means for
protecting personal privacy and
proprietary information.
[44 U.S.C., SEC. 3542]
The unauthorized disclosure of
information could be expected to
have a limited adverse effect on
organizational operations,
organizational assets, or
individuals.
The unauthorized disclosure of
information could be expected to
have a serious adverse effect on
organizational operations,
organizational assets, or
individuals.
The unauthorized disclosure of
information could be expected to
have a severe or catastrophic
adverse effect on organizational
operations, organizational assets,
or individuals.
Integrity
Guarding against improper
information modification or
destruction, and includes
ensuring information non-
repudiation and authenticity.
[44 U.S.C., SEC. 3542]
The unauthorized modification or
destruction of information could
be expected to have a limited
adverse effect on organizational
operations, organizational assets,
or individuals.
The unauthorized modification or
destruction of information could
be expected to have a serious
adverse effect on organizational
operations, organizational assets,
or individuals.
The unauthorized modification or
destruction of information could
be expected to have a severe or
catastrophic adverse effect on
organizational operations,
organizational assets, or
individuals.
Availability
Ensuring timely and reliable
access to and use of information.
[44 U.S.C., SEC. 3542]
The disruption of access to or use
of information or an information
system could be expected to have
a limited adverse effect on
organizational operations,
organizational assets, or
individuals.
The disruption of access to or use
of information or an information
system could be expected to have
a serious adverse effect on
organizational operations,
organizational assets, or
individuals.
The disruption of access to or use
of information or an information
system could be expected to have
a severe or catastrophic adverse
effect on organizational
operations, organizational assets,
or individuals.
Table 1: NIST 800-60 Classification, from http://csrc.nist.gov/publications/nistpubs/800-60-rev1/SP800-
60_Vol1-Rev1.pdf
For each objective, determine if the potential impact for your data is limited, serious, or severe.
If during the course of your review, you have selected multiple levels, round up to determine
your final level (the high water mark). For example, a report containing employee names and
social security numbers may have High Confidentiality, but Moderate Integrity and Availability,
because it could be easily recreated. Because the Confidentiality rating is High, the document
must be ranked as High (Level 3). You will want to ensure an application handling that data
meets the Level 3 assurance requirements as documented below.
There will be cases where an application is unable to meet the requirements defined to handle
the appropriate data at the time of review. To accommodate these cases, the assessor will
suggest compensating controls that can be enforced.](https://image.slidesharecdn.com/samplecoudapplicationsecurityandoperationspolicyrelease-150122122842-conversion-gate02/75/Sample-Cloud-Application-Security-and-Operations-Policy-release-4-2048.jpg)