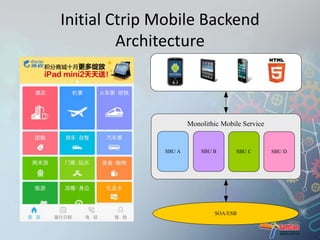
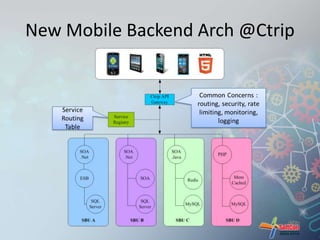
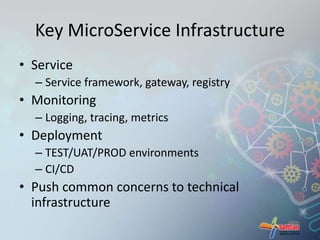
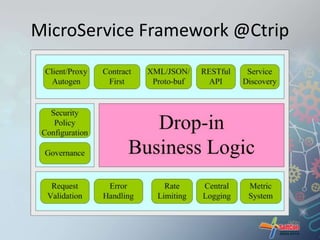
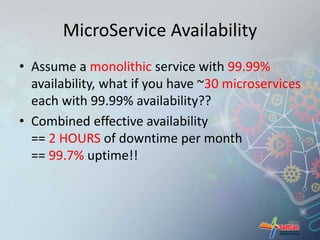
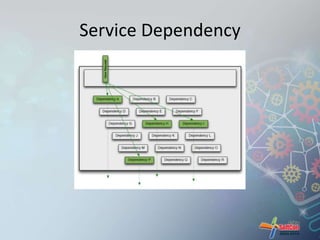
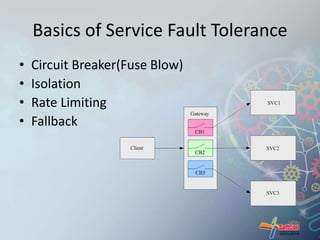
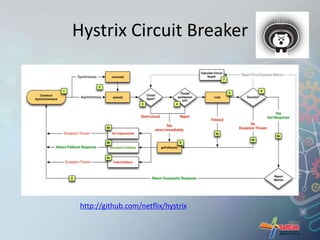
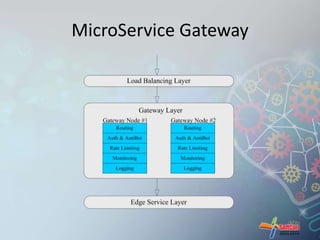
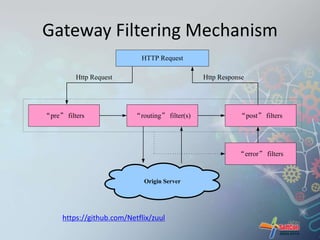
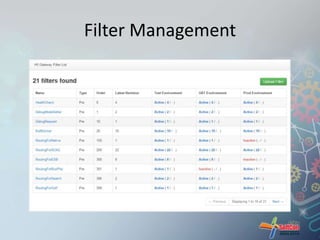
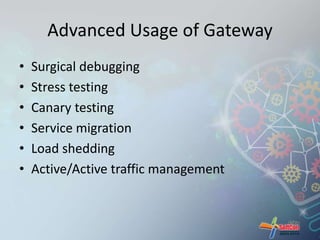
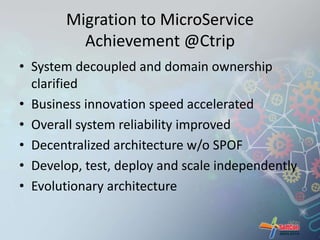
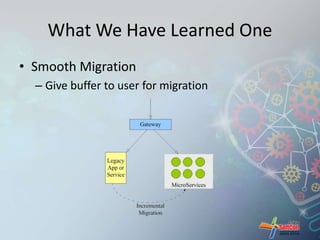
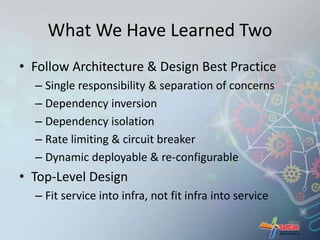
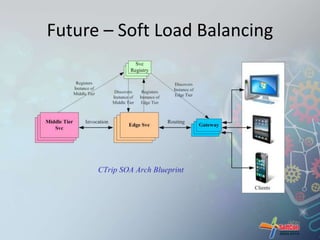
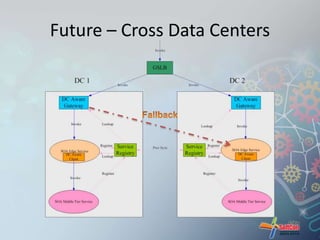
The document presents an overview of microservice architecture as implemented by Ctrip, discussing the advantages of system decoupling for deployability and scalability and the challenges of monolithic architectures. It highlights the migration process from a monolithic mobile backend to microservices, focusing on best practices, lessons learned, and the infrastructure required for successful implementation. The author emphasizes the importance of architecture design principles and acknowledges the operational overhead and complexities associated with microservices.