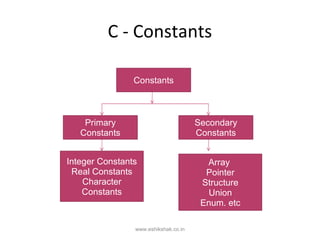
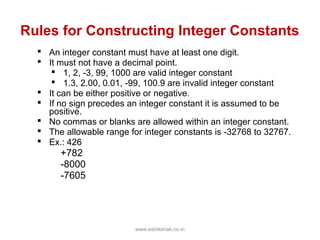
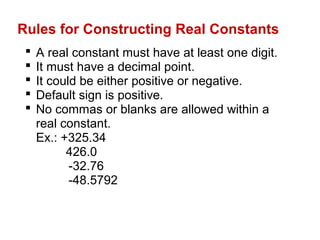
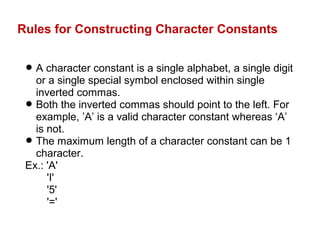
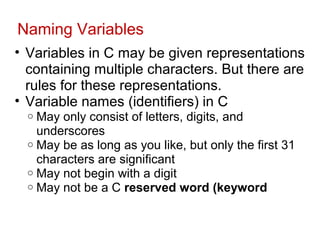
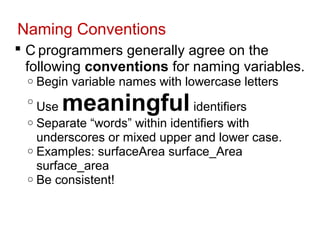
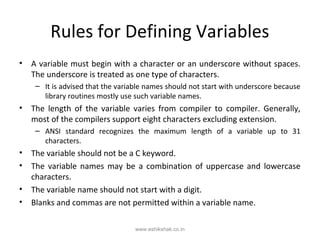
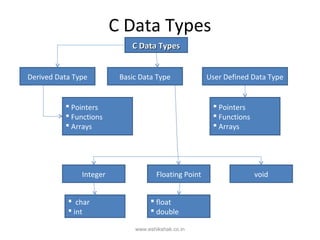
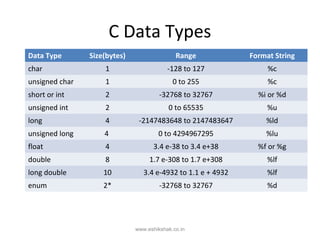
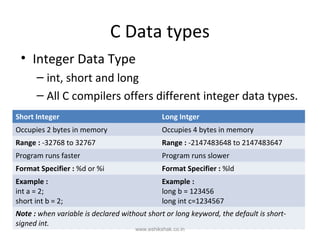
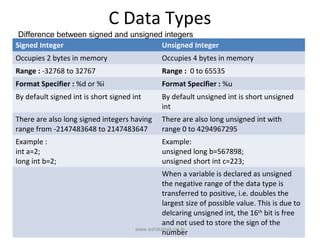
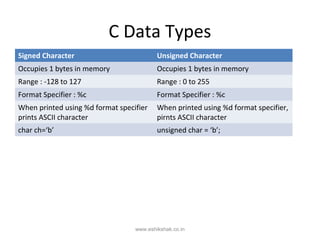
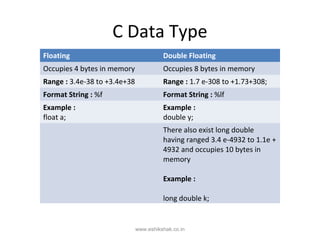
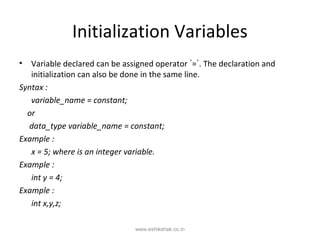
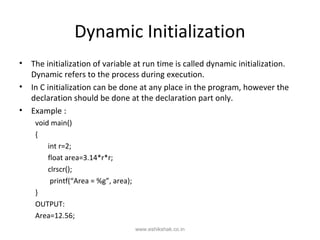
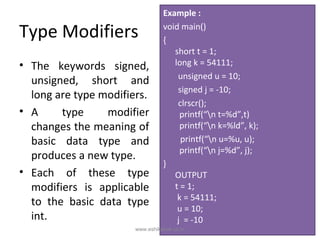
The document discusses various types of constants and variables in C programming. It describes primary constants like integer, real, and character constants and defines rules for constructing each type. Secondary constants include arrays, pointers, structures, and unions. Variables represent unknown values that can change during program execution. The document outlines naming conventions and rules for defining variables. It also covers C data types like integer, floating point, characters, and void and provides details on their sizes and ranges. Initialization of variables through assignment at declaration or dynamically at runtime is also summarized.