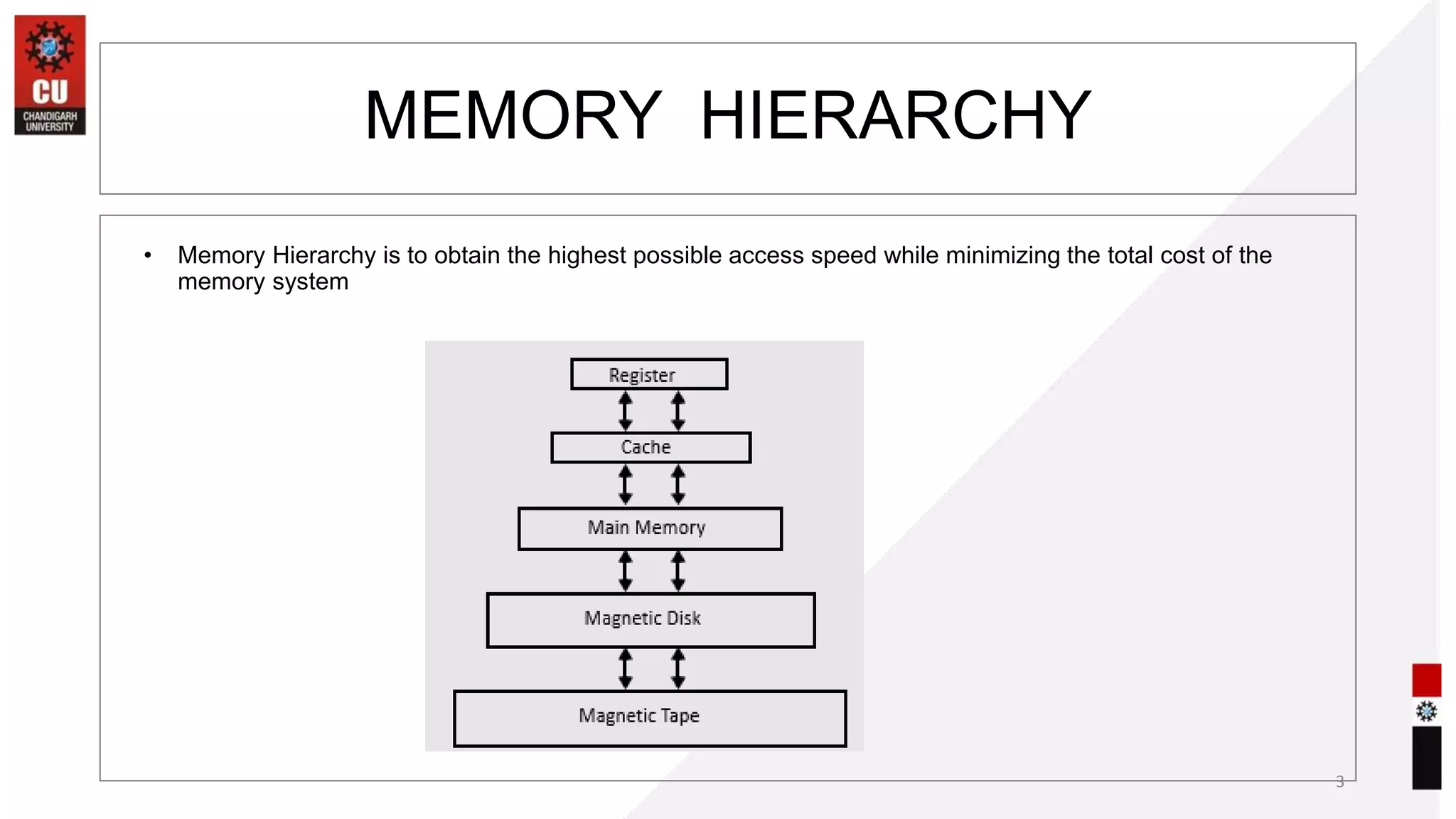
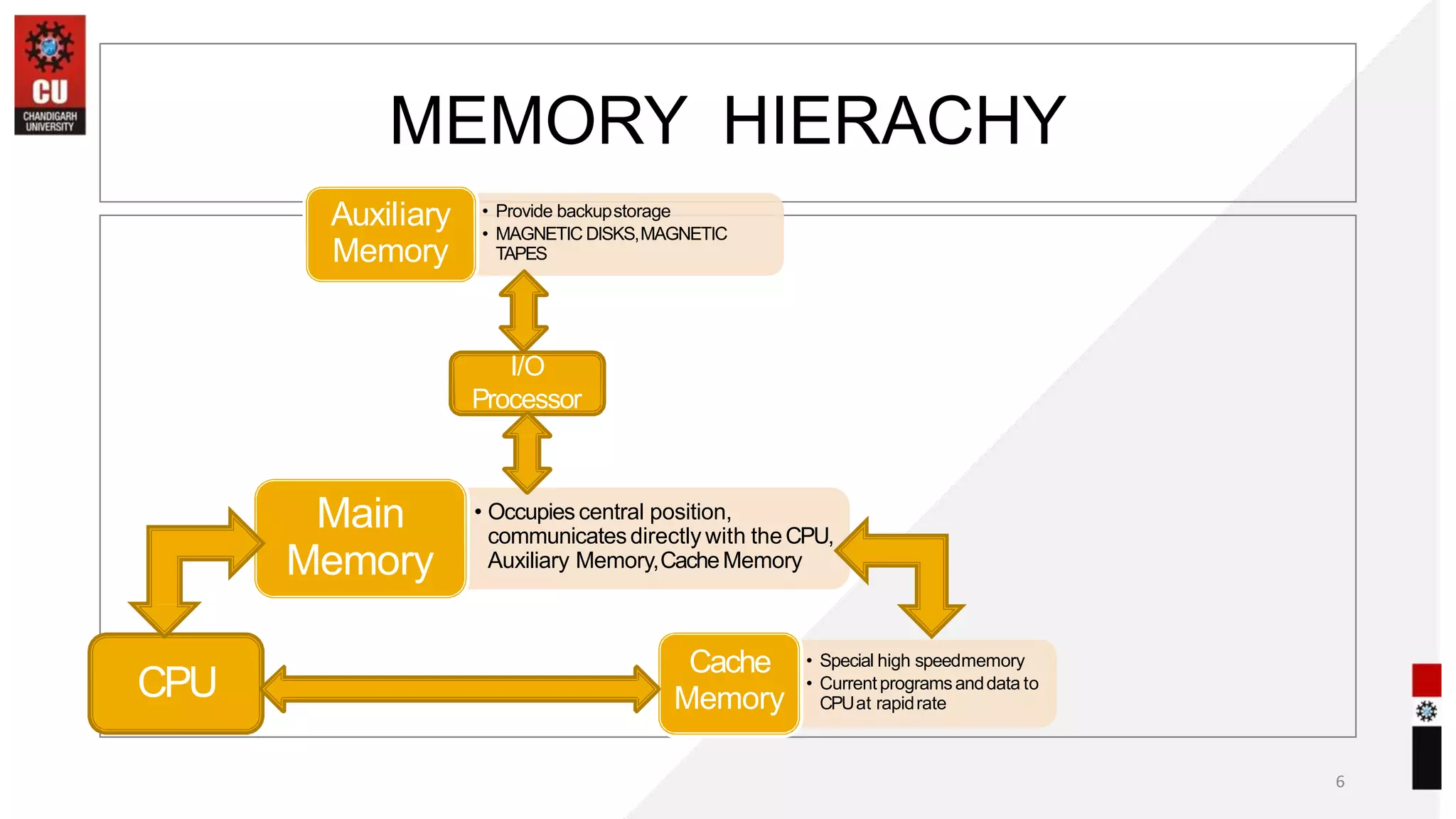
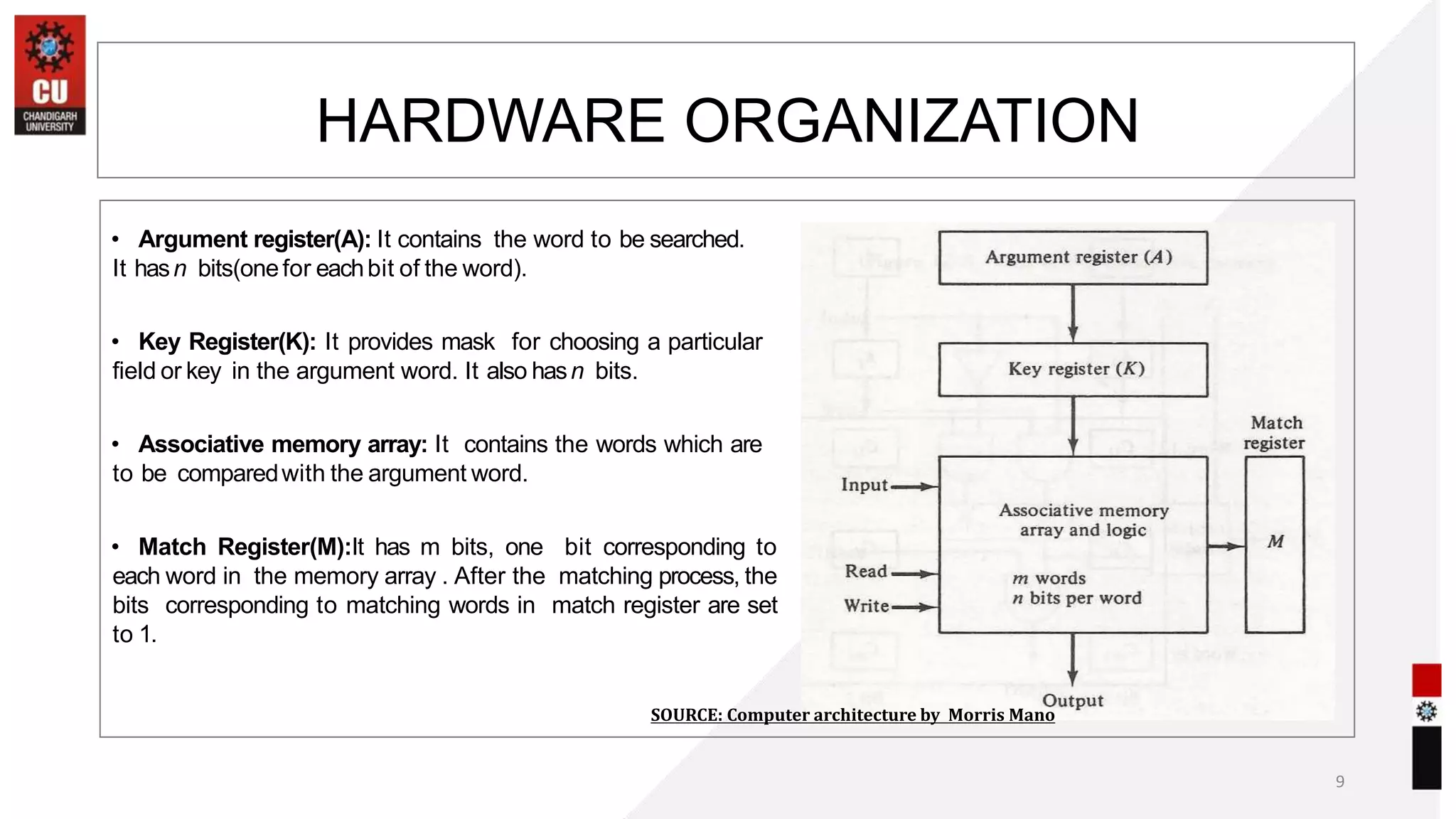
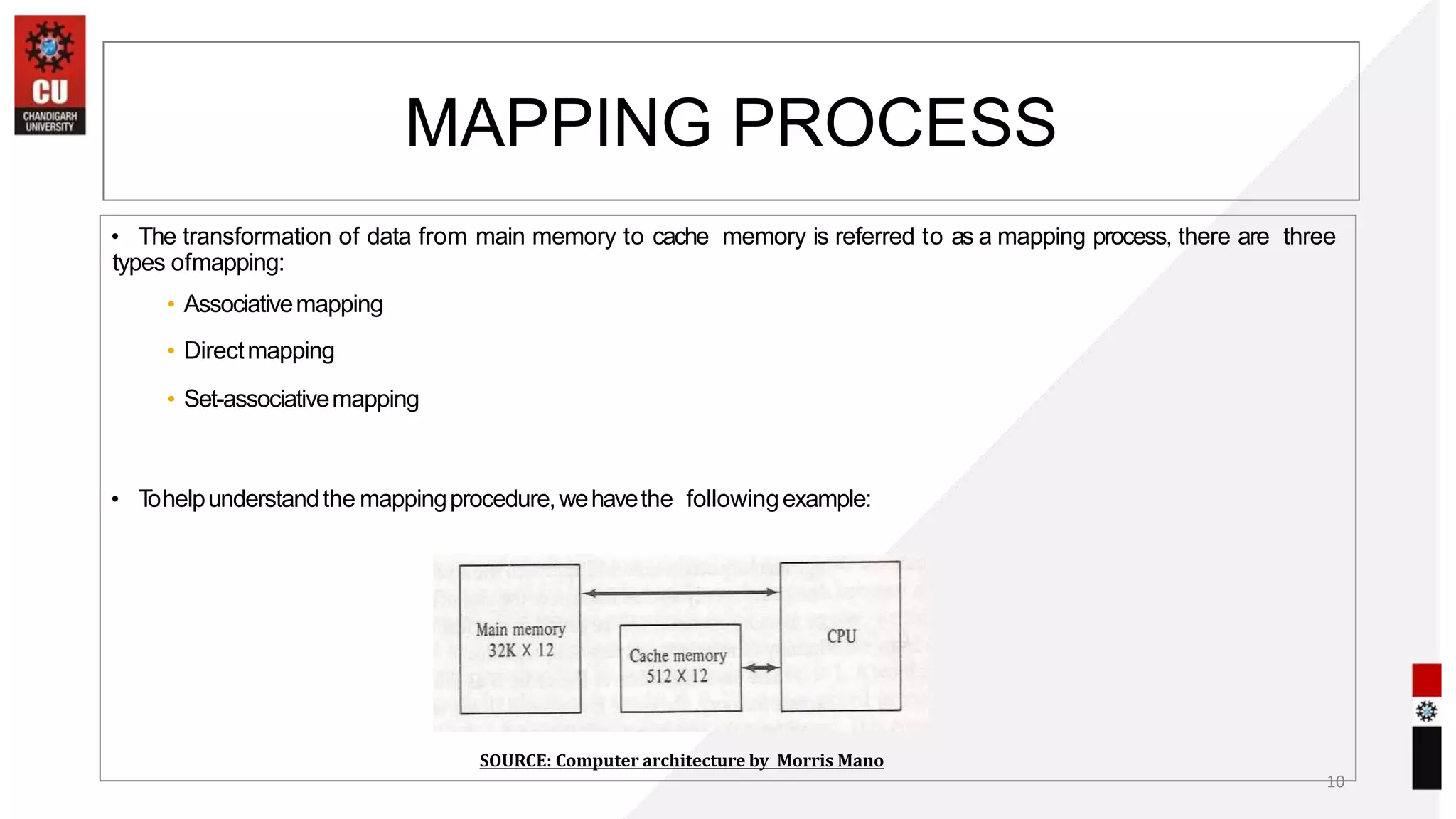
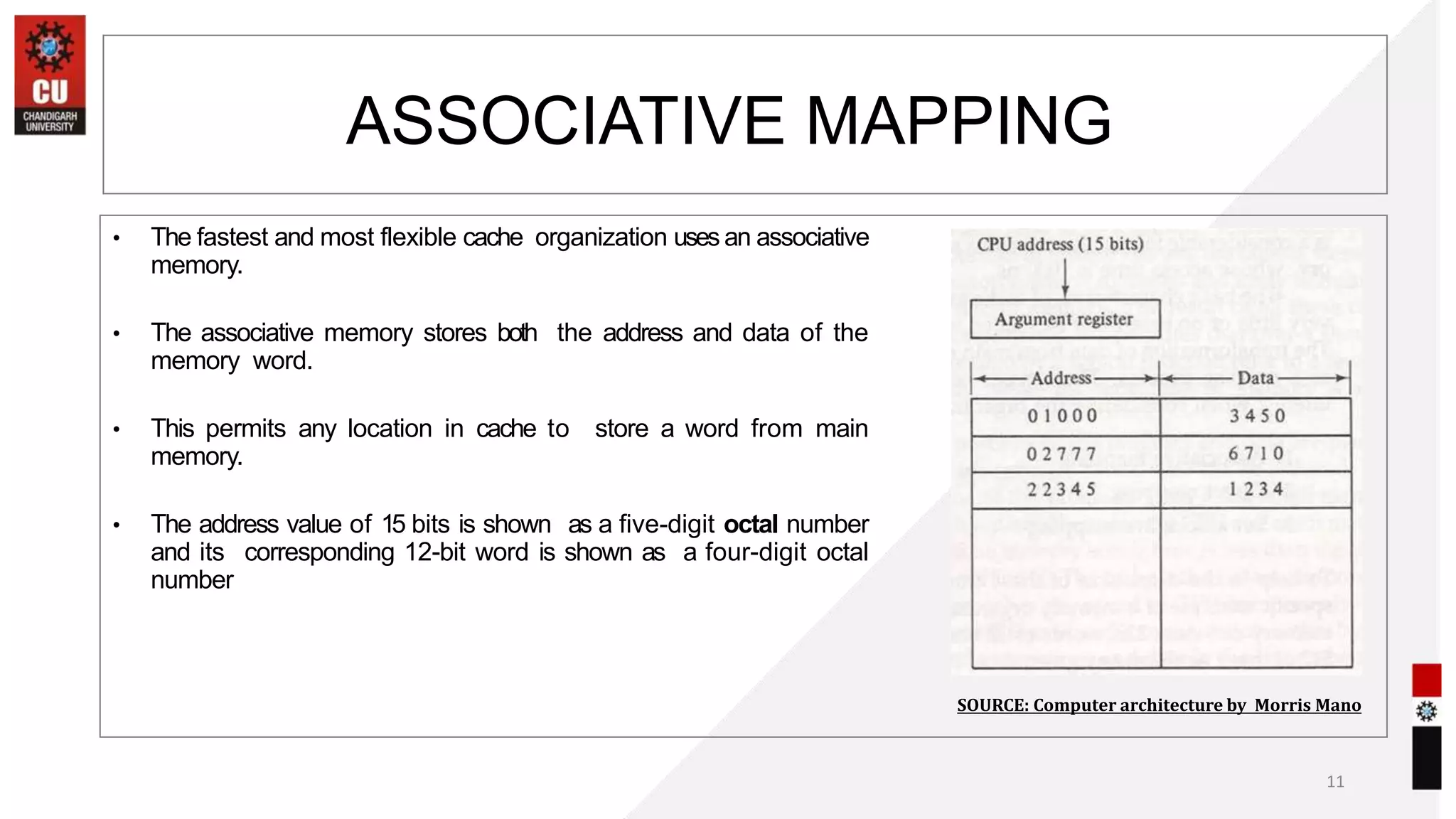
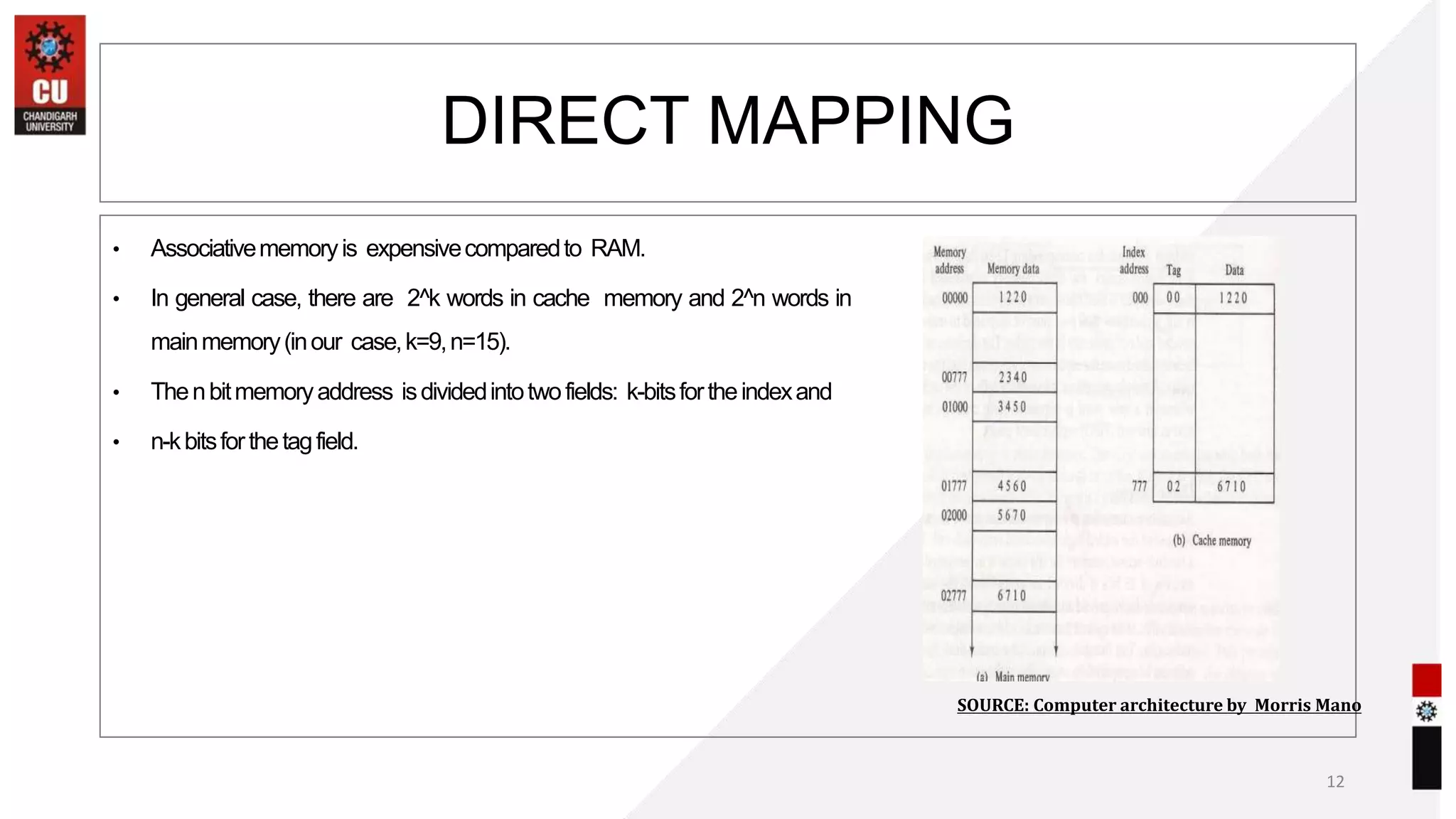
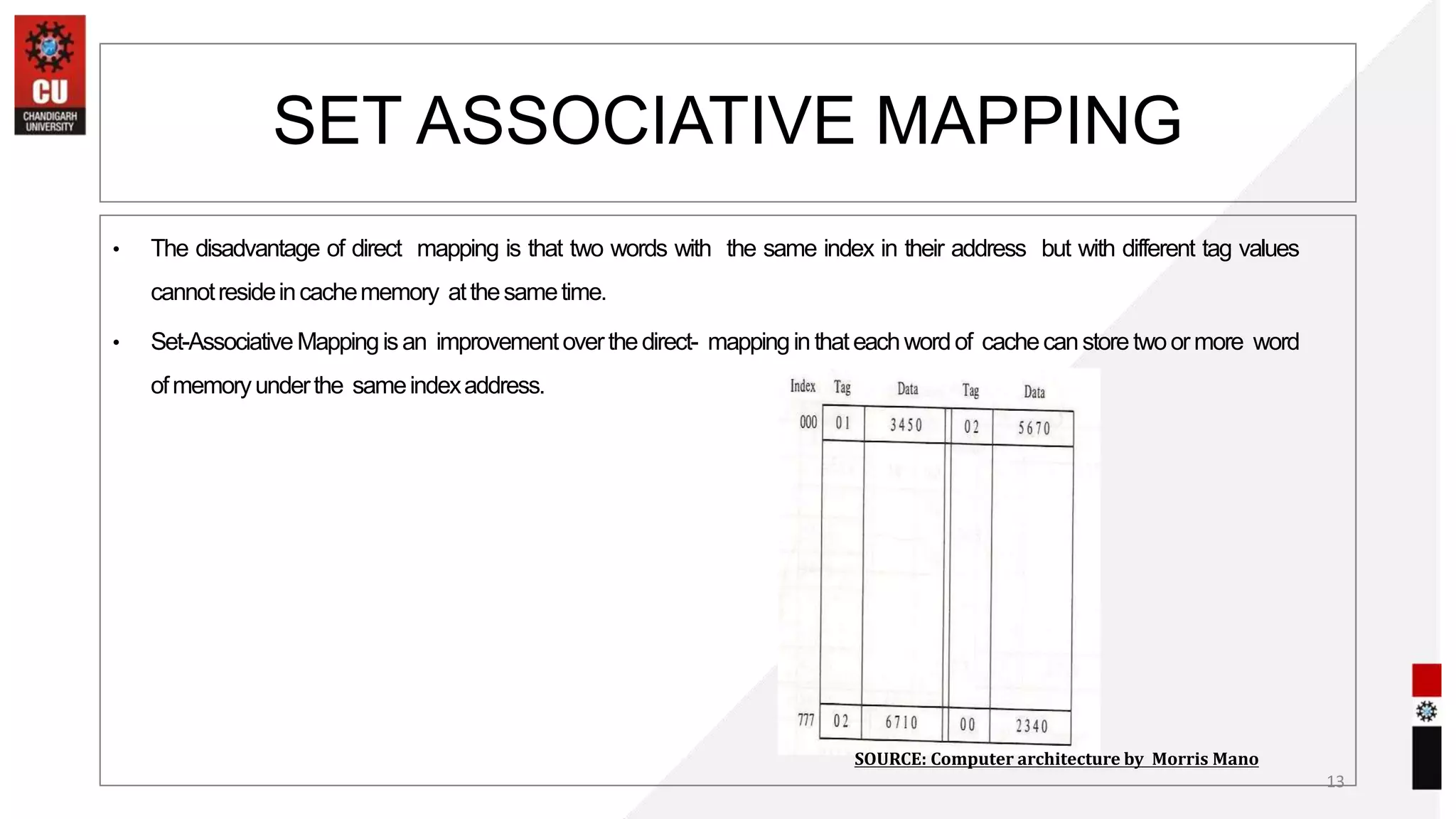
This document summarizes key concepts related to computer memory organization and hierarchy. It discusses how memory is organized from the fastest cache memory up to slower main memory and auxiliary storage. It covers cache mapping techniques like direct mapping, set associative mapping and associative mapping. Virtual memory and paging/segmentation techniques are also summarized. Replacement algorithms for cache memory like FIFO and LRU are discussed. The document provides an overview of computer architecture course topics and assessment patterns.