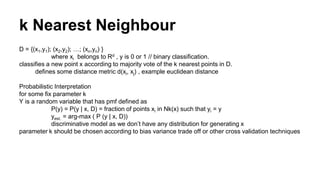
Machine learning algorithms infer unknowns from knowns through statistical inference. Common machine learning applications include spam identification, handwriting recognition, image recognition, speech recognition, recommendation systems, and climate modeling. These applications can be grouped into supervised learning (classification and regression) and unsupervised learning (clustering, density estimation, dimensionality reduction). Generative models model the joint distribution of all variables, while discriminative models model only the target variables conditional on observed variables. K-nearest neighbors is a discriminative classification algorithm that classifies a new data point based on the labels of its k nearest neighbors.