The document provides an introduction to Linux, including its history and origins. It discusses how Linux was originally developed by Linus Torvalds as an open source alternative to UNIX. It also summarizes some key Linux distributions like Red Hat Linux and describes basic Linux commands, file structures, and permissions.


![Group Administration in Terminal
• A group contain similar type of user as it members.
( Collection of users called as group)
• The Group Add :
Syntax : #groupadd [-g GID ] group name
Example : #groupadd –g 100 Linux-Admin
• The Group Modify:
Syntax : # groupmod [ -g new gid ] [ -n new name] group name
Example : #groupmod –g 109 –n mail-Admin Linux-Admin
• The Delete a Group:
Example : #groupdel Linux-Admin](https://image.slidesharecdn.com/redhatbycbitss-230405071136-43208e32/85/redhat_by_Cbitss-ppt-60-320.jpg)
![Lab step ( Client side)
• Linux M/C:
# netconfig
select : yes
select : dynamic automatic [DHCP]
#service network restart
• Windows M/C:
go to network then select obtain an IP address
automatic
set the dns master IP address means dhcp server
IP address.](https://image.slidesharecdn.com/redhatbycbitss-230405071136-43208e32/85/redhat_by_Cbitss-ppt-88-320.jpg)
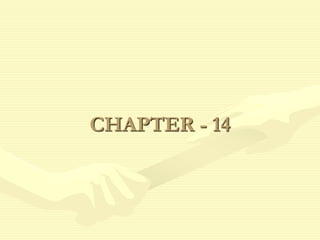
![Lab Steps
• Server Side :
1. To check the Package:
# rpm –qa vsftpd*
2. To enable the service
# service vsftpd restart
• Client Side:
1. To any (Operating System ) Platform :
#ftp 10.0.0.9
user name : murali
password : *****
ftp> get murali
ftp>put shankar
ftp>bye
#
* get ---------- Get the file [ Ex: ftp>get <filename>]
* put---------- Put the file [Ex: ftp>put<filename>]](https://image.slidesharecdn.com/redhatbycbitss-230405071136-43208e32/85/redhat_by_Cbitss-ppt-94-320.jpg)
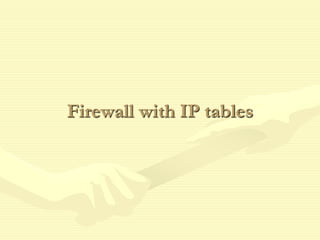
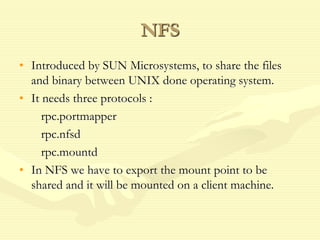
![• The Linux kernel contains advanced tools for packet filtering, the process of
controlling network packets as they attempt to enter, move through, and exit
your system.
• Structure:
#iptables [-t <table-name>] <command> <chain-name> <parameter-1>
<option -1> <parameter –n> <option –n>
• Commands :
-A – Append the iptables rule to end of the specified chain.
-D – Deletes a rule in a particular chain by number in a chain.
• INPUT:
All incoming package are checked against rules in the change.
• OUTPUT:
All outgoing package are checked against rules in the change.
• Packet Paten :
-s – All the packet are checked for a specific source IP.
• Block :
-j – The Packet’s is drop , no massage send to the requesting computer.
• Reject :
The Packet’s drop, an error massage send to the requesting computer.](https://image.slidesharecdn.com/redhatbycbitss-230405071136-43208e32/85/redhat_by_Cbitss-ppt-97-320.jpg)
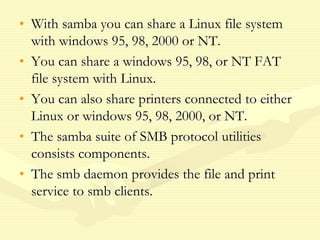
![Lab Steps
• Linux Machines :
1. To check the package
# rpm –qa samba*
2. To create a directory
#mkdir /opt/murali
# chmod 777 /opt/murali
3. To share the directory
# vi /etc/exports
/opt/murali *(rw,sync)
4. To config the service file
#vi /etc/samba/smb.conf
(go to last line entry the contented )
[murali]
path = /opt/murali
valid users = murali, shankar
writable = yes
#
5. To set the samba password
#smbpasswd –a murali
6. To enable the service
# service nfs restart
#service smb restart](https://image.slidesharecdn.com/redhatbycbitss-230405071136-43208e32/85/redhat_by_Cbitss-ppt-106-320.jpg)