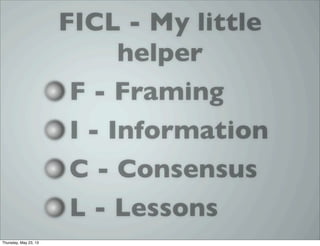
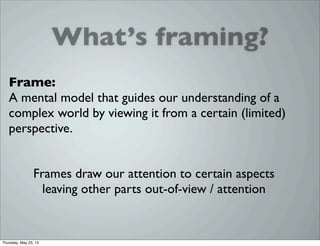
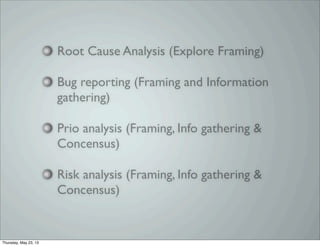
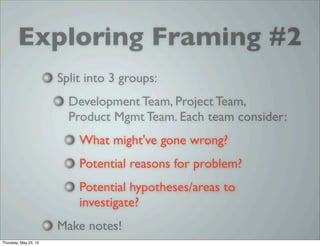
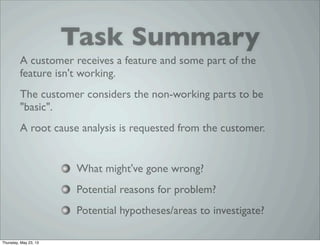
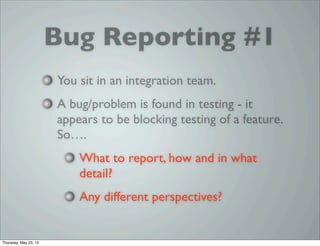
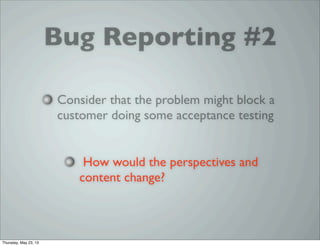
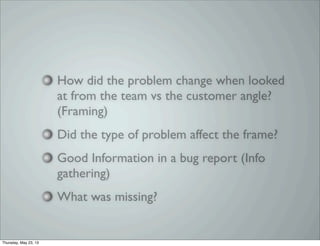
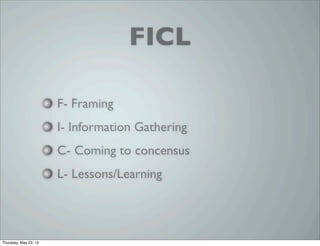
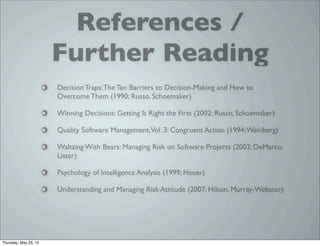
The document discusses the importance of framing and analysis skills in testing and software development, addressing how different perspectives can lead to various interpretations of problems. It explores exercises related to root cause analysis, bug reporting, and risk assessment to improve understanding of quality and testing issues. Additionally, it emphasizes the gathering of information and reaching consensus among teams to enhance decision-making processes.