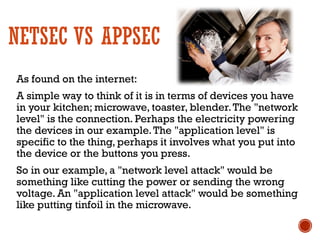
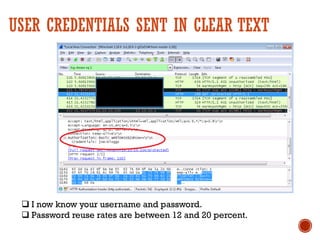
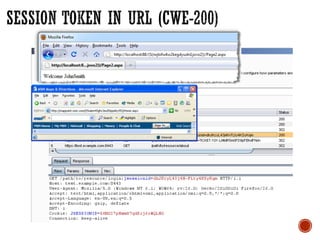
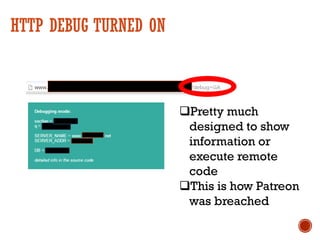
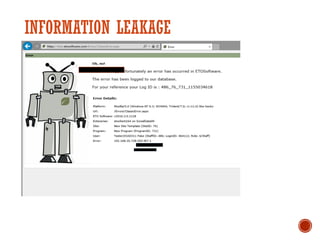
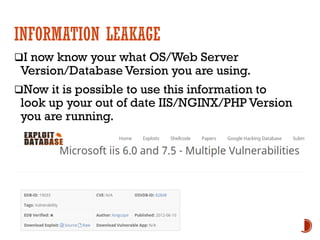
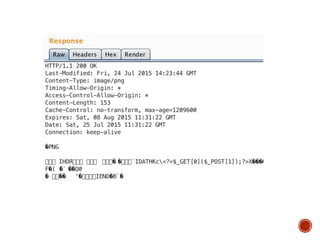
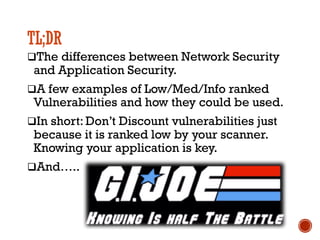
Low and medium vulnerabilities found by vulnerability scanners in web applications can still pose serious risks if exploited. Some examples provided include clear text transmission of credentials, which could enable credential reuse on other sites; HTTP debug being turned on, which was how the Patreon breach occurred; and information leakage revealing version numbers that can be used to exploit known vulnerabilities. The presentation emphasized that application security requires understanding how specific vulnerabilities could impact an individual application beyond the generic risk rating.