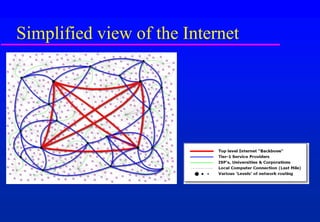
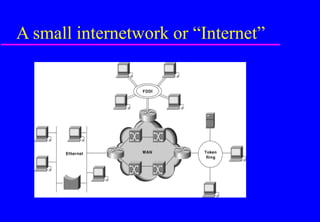
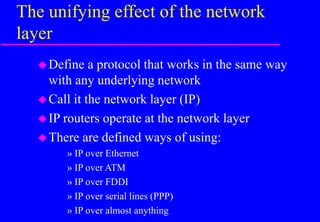
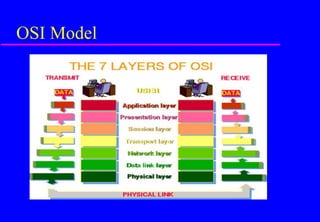
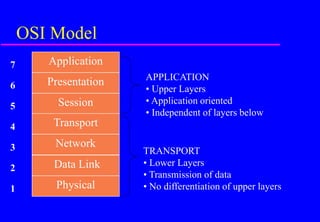
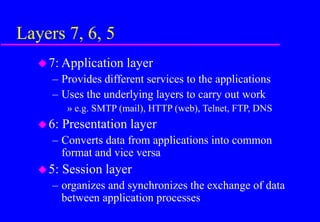
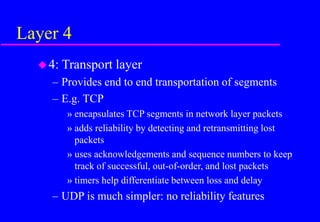
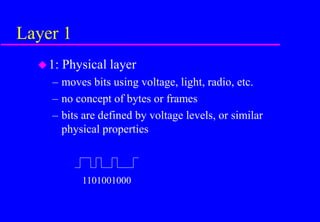
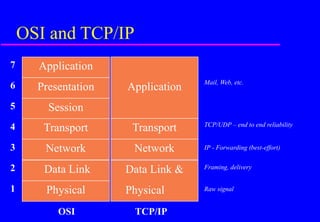
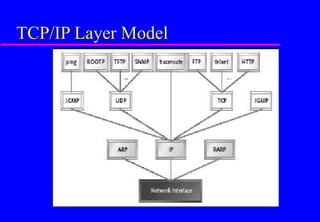
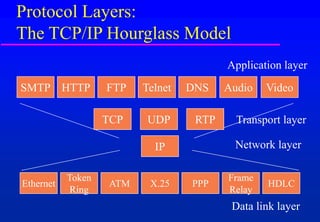
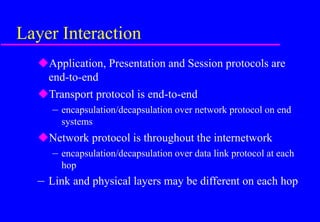
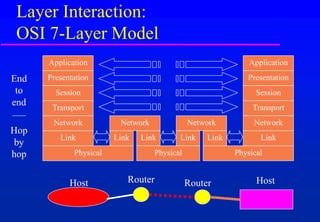
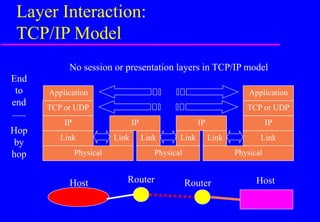
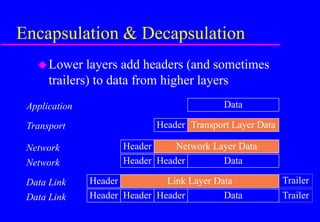
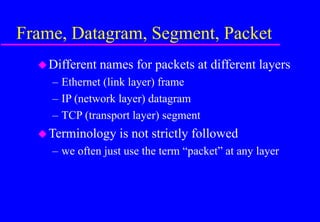
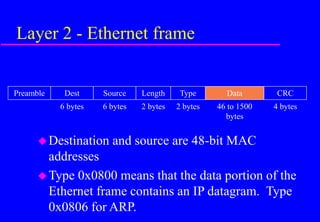
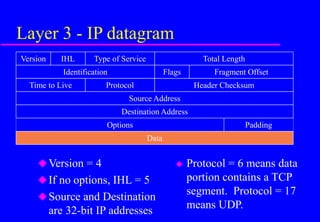
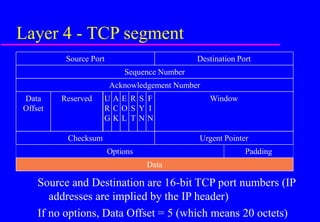
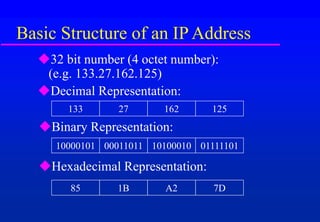
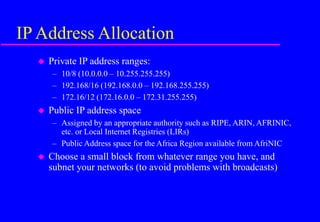
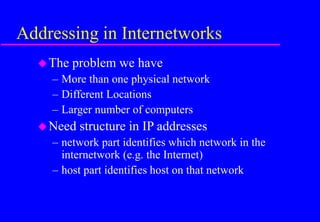
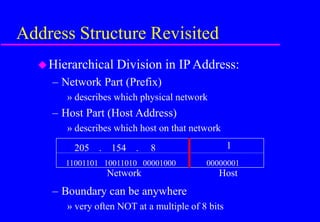
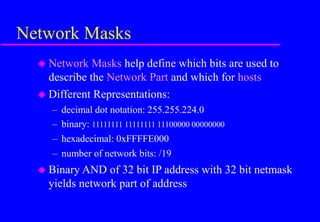
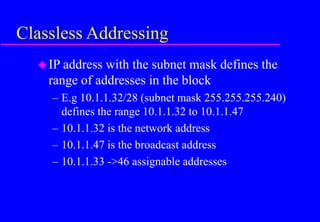
This document provides an overview of IP networking and TCP/IP basics. It discusses the origins of TCP/IP in the ARPANET project and the distributed network design. It describes the OSI model and compares it to the TCP/IP architecture. It also covers IP addressing and numbering, client-server architecture, IP forwarding, and some common network troubleshooting tools.