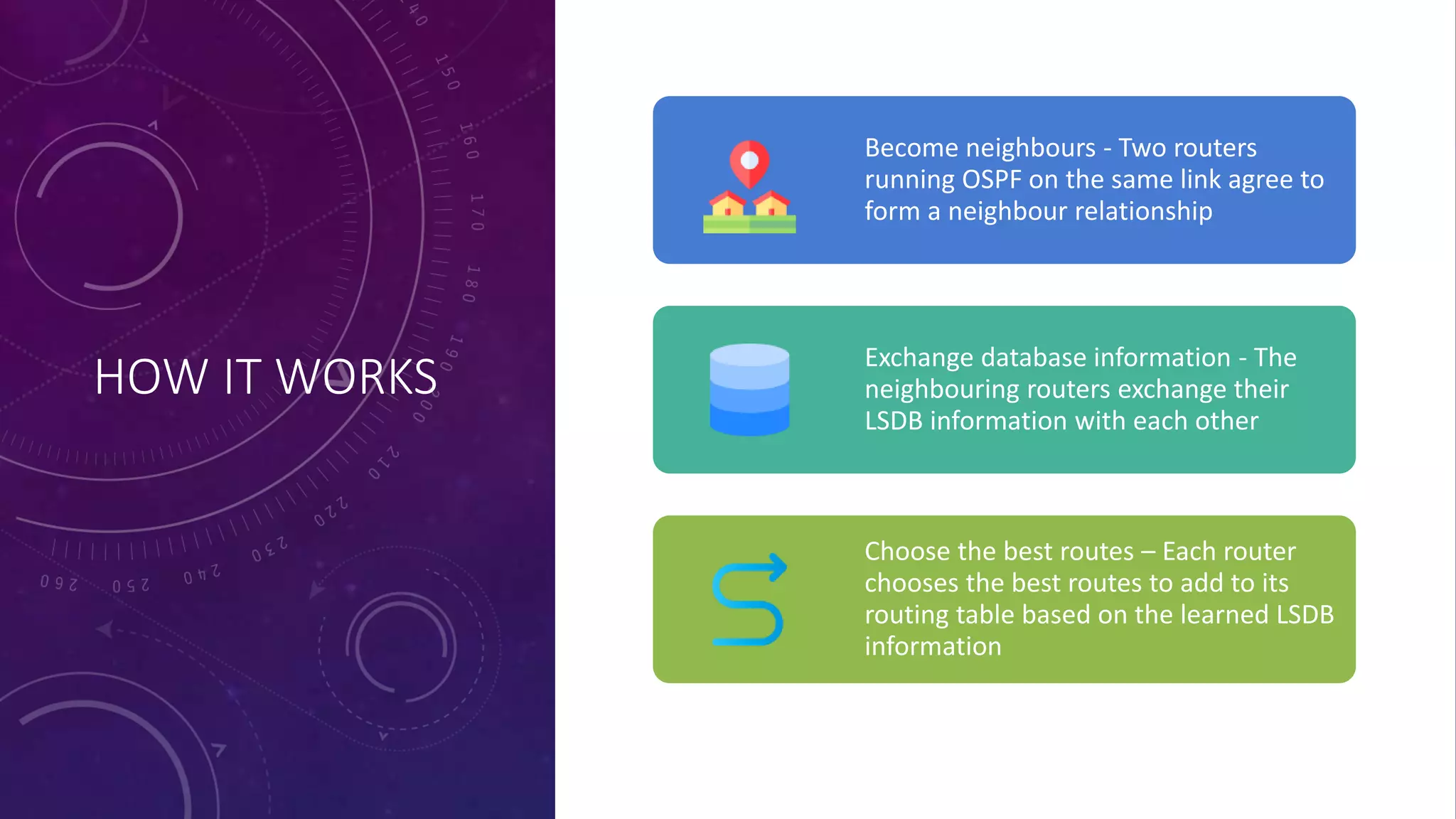
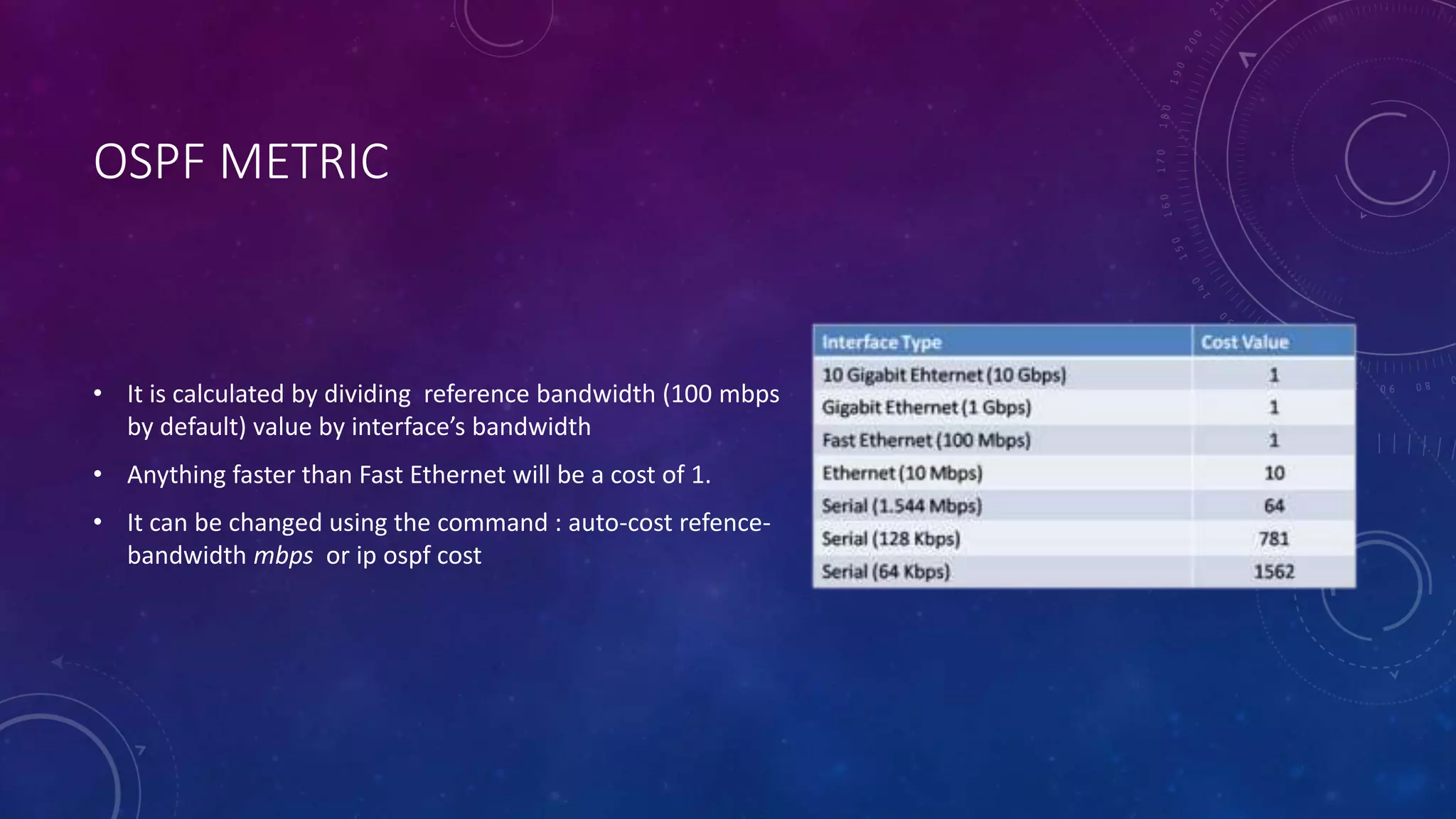
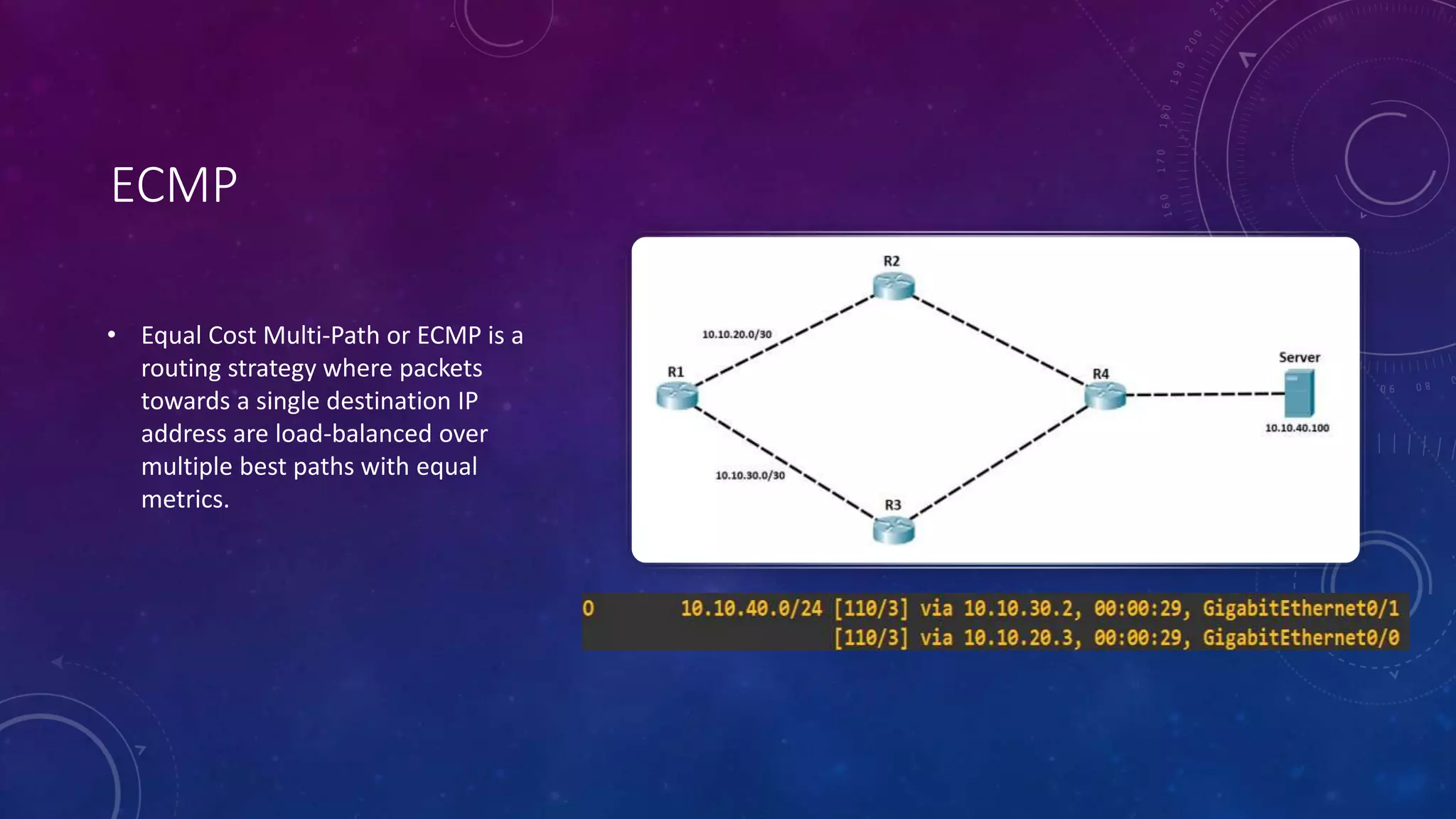
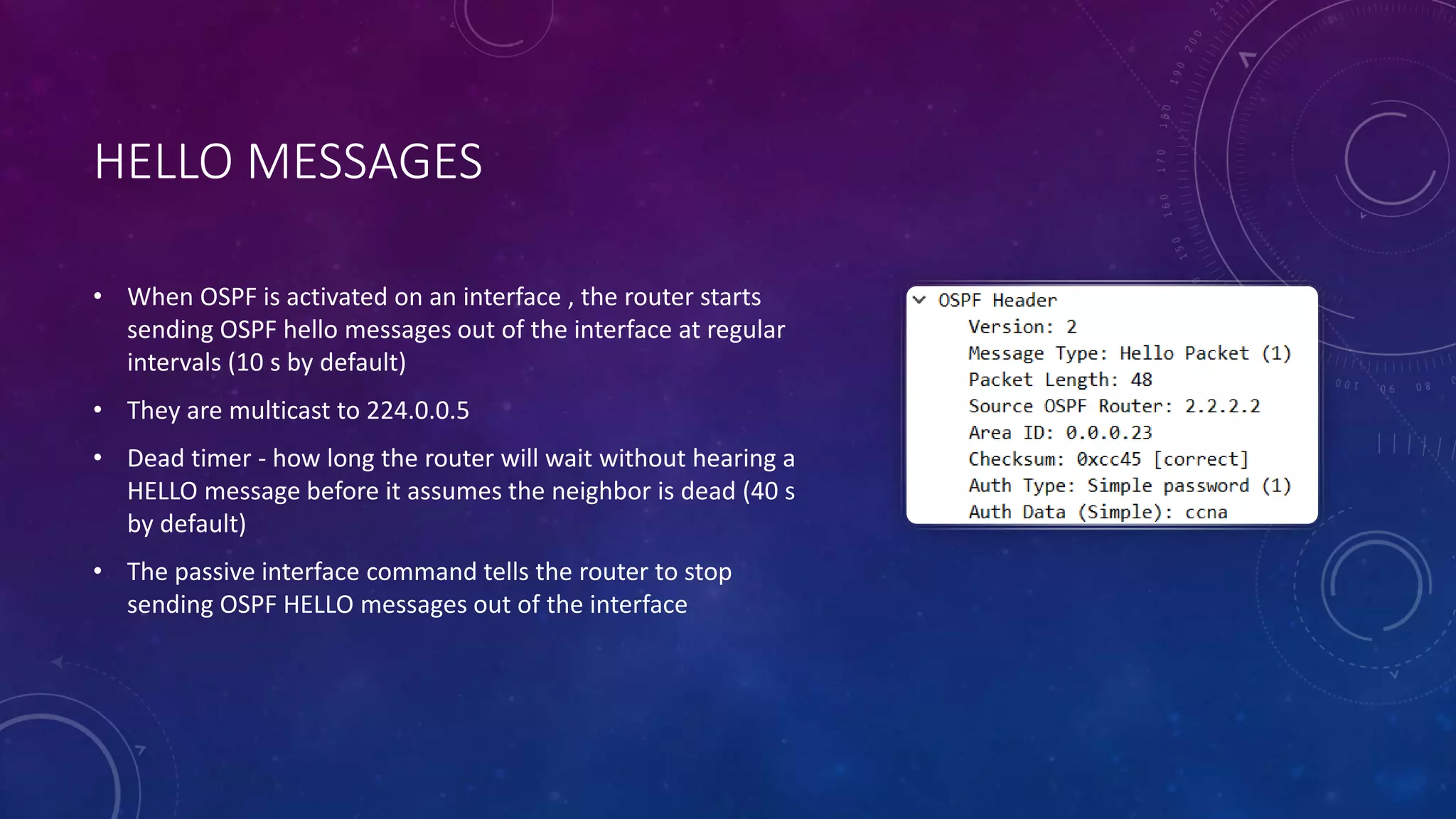
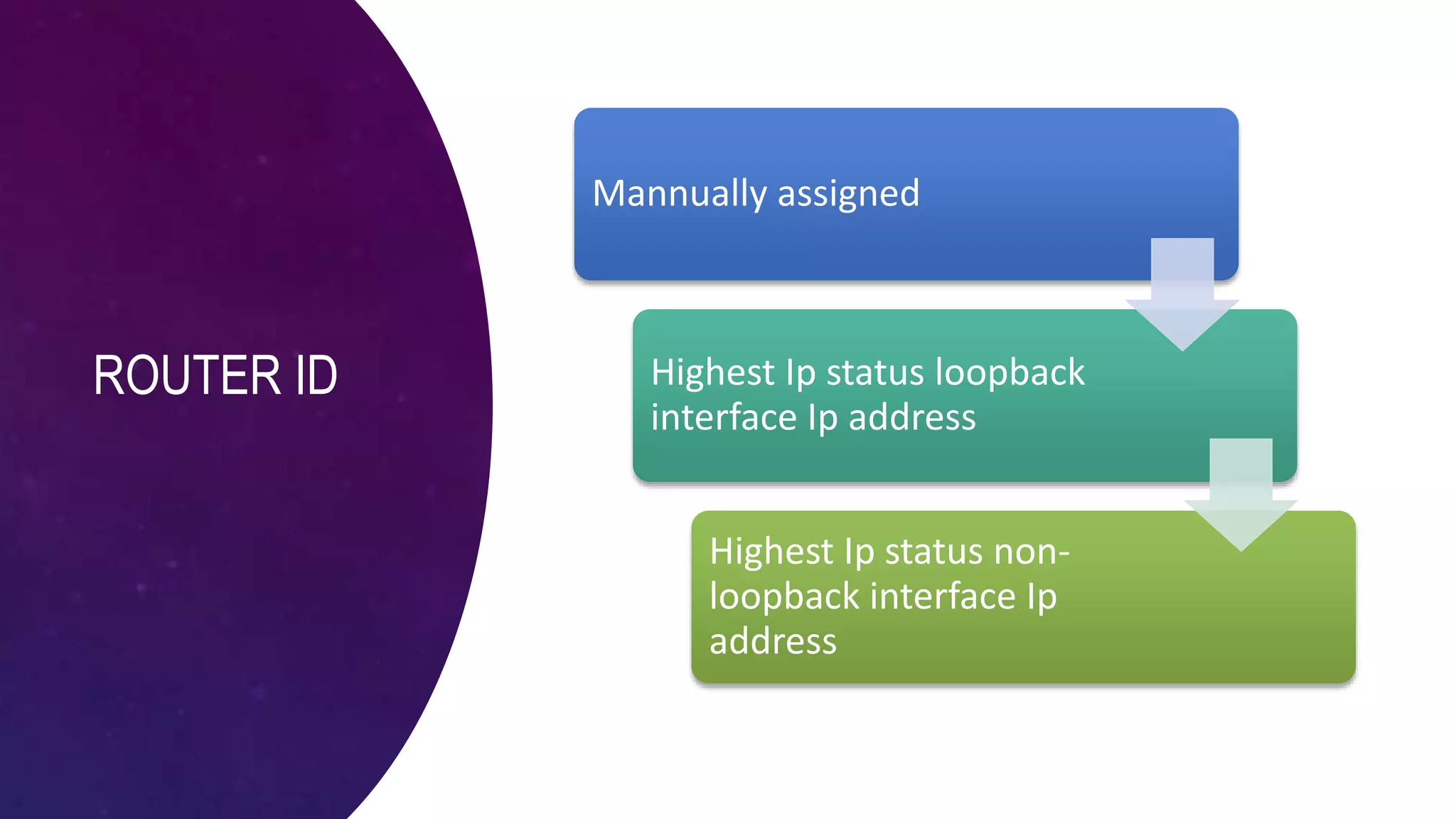
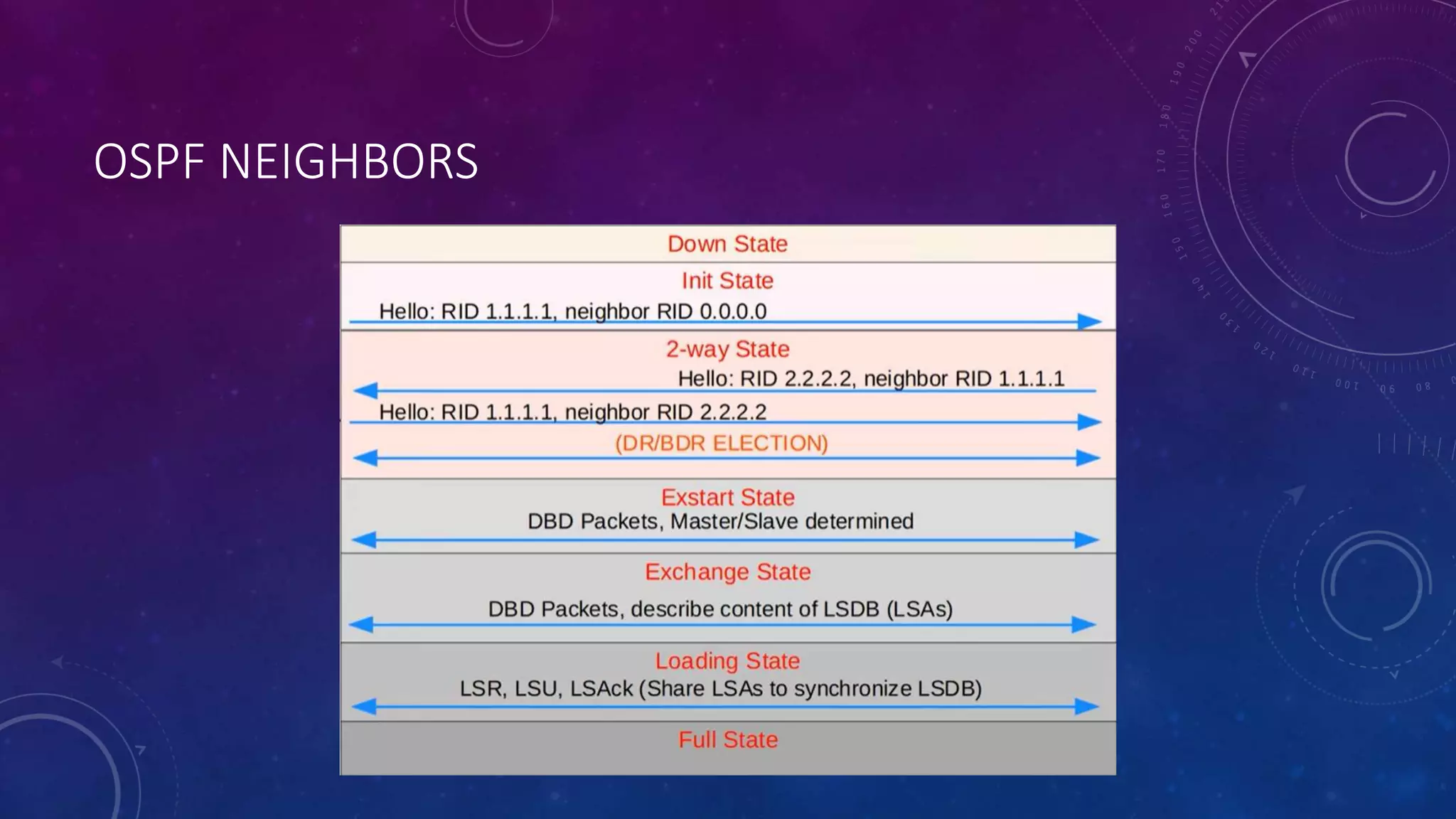
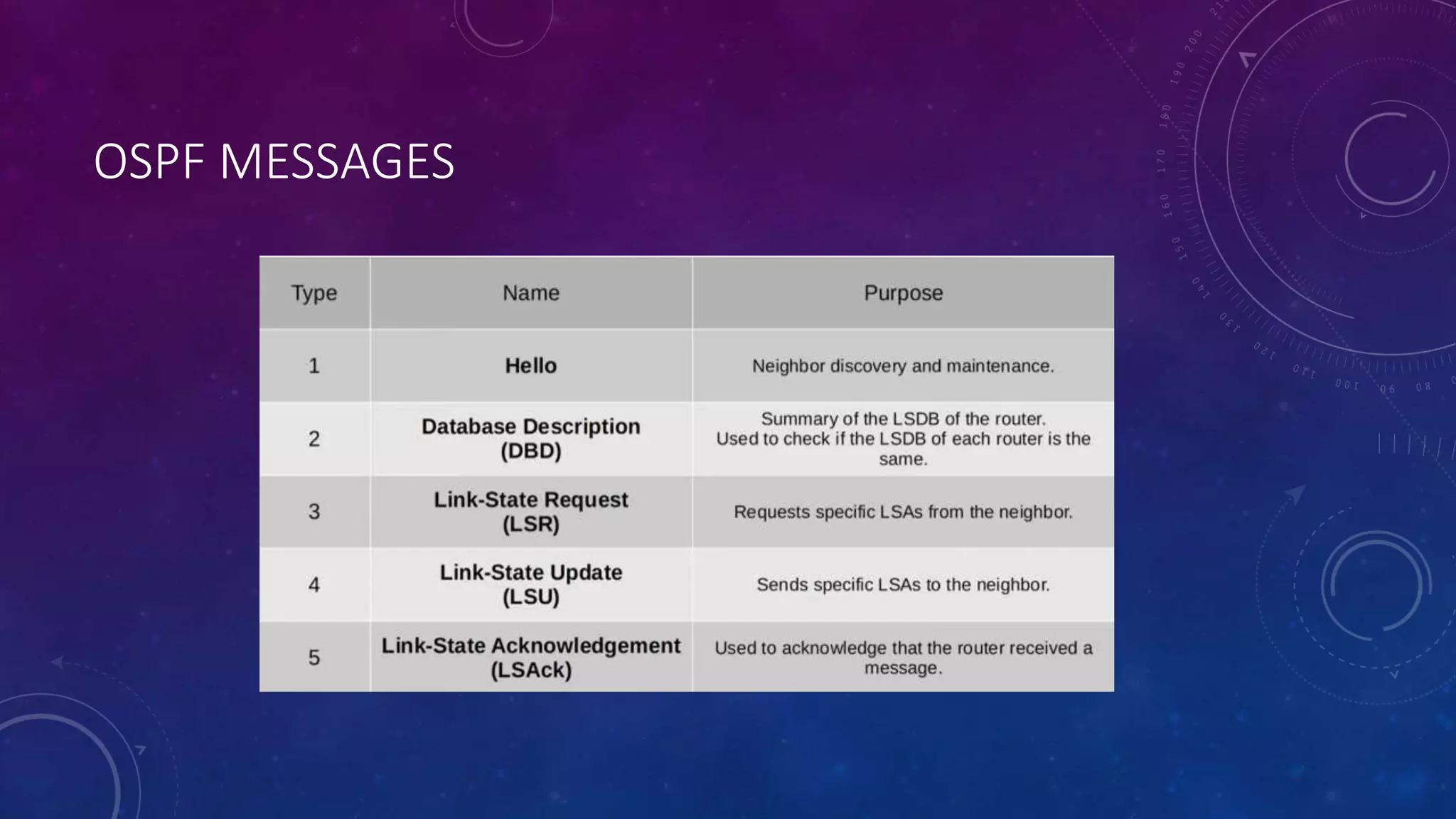
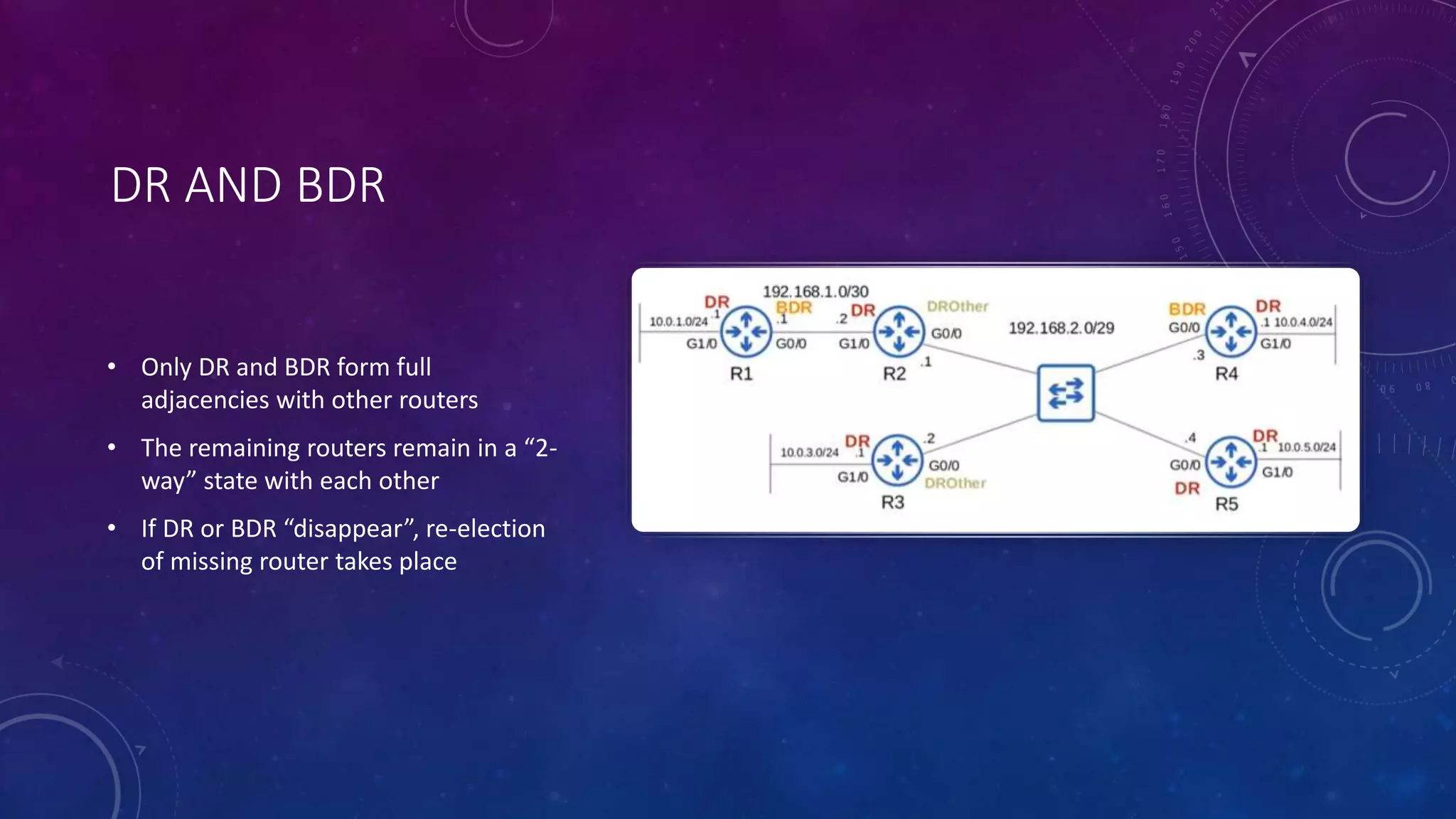
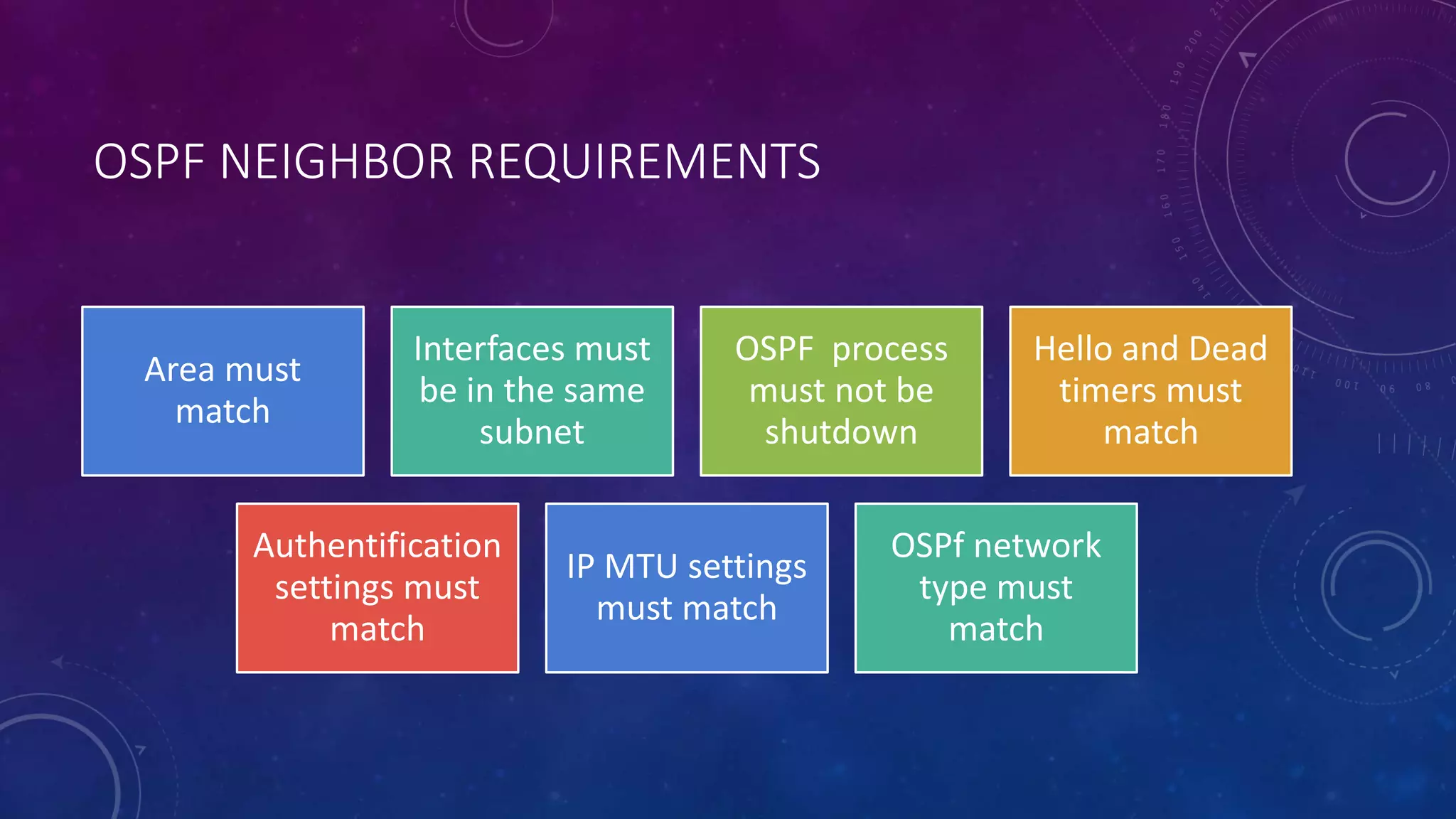
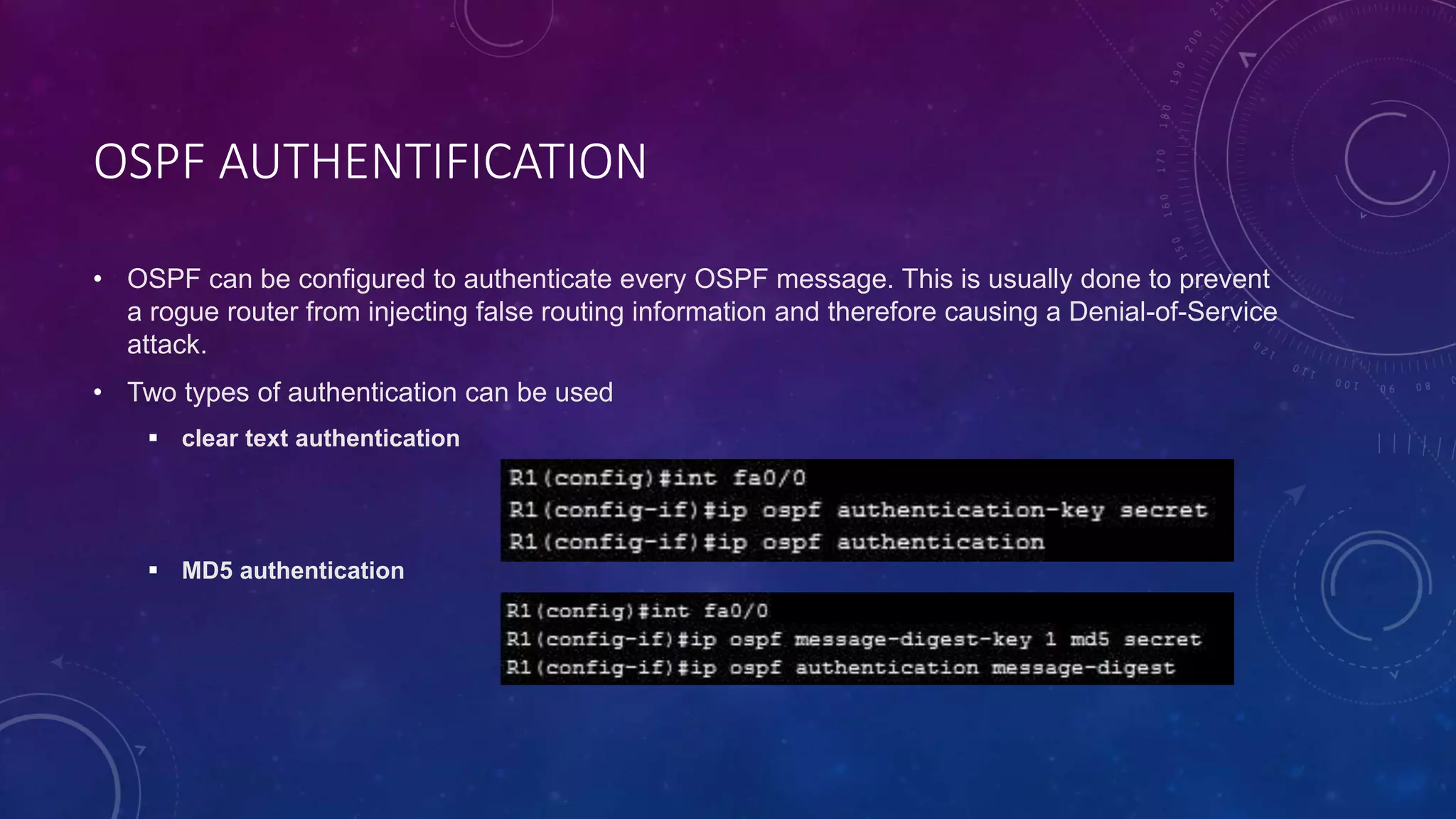
OSPF is a link-state interior gateway protocol that uses shortest path first algorithm to calculate routes. It elects a designated router that exchanges link-state advertisements and database information with other routers to choose the best routes. OSPF supports equal cost multi-path routing, uses different types of link-state advertisements, and allows dividing networks into areas to reduce routing overhead. It authenticates messages to prevent routing attacks.