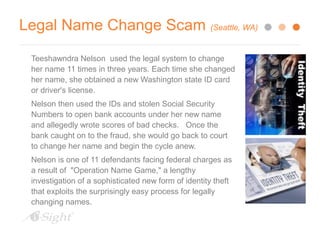
The document, authored by Kelly E. Riddle, delves into the complexities of insurance fraud and the intricacies of insurance practices. It discusses the history of insurance, definitions, responsibilities of the insured, and identifies various types of fraud, including identity theft and vendor fraud. Furthermore, it outlines investigative techniques and methods used to combat fraudulent claims in the insurance industry.