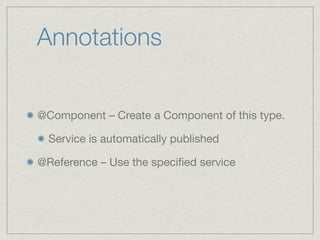
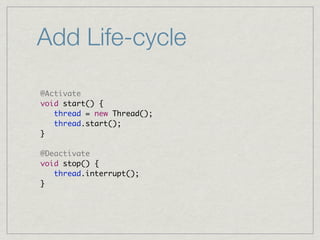
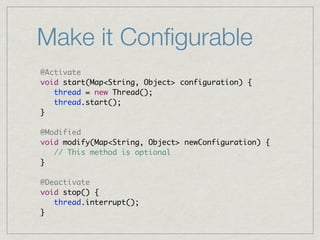
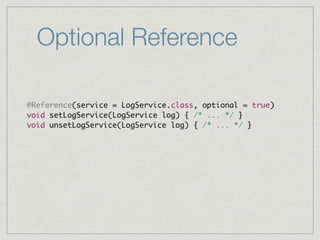
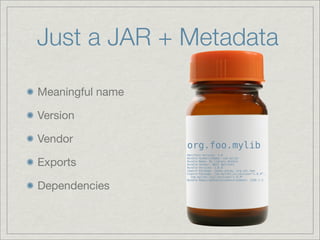
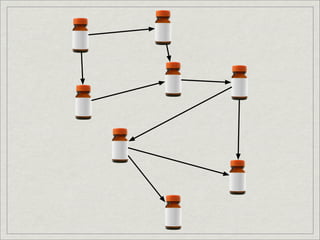
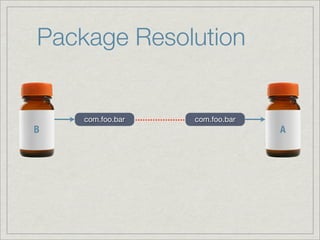
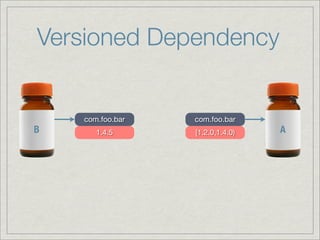
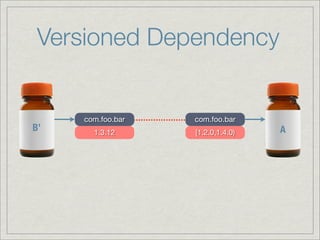
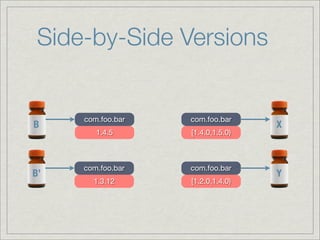
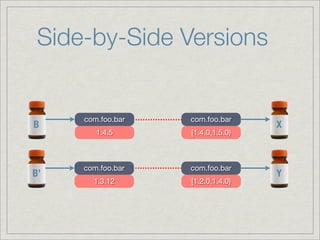
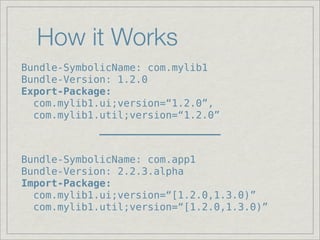
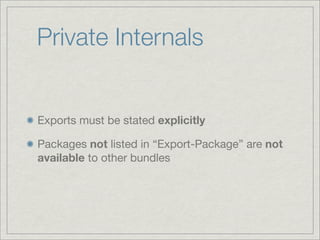
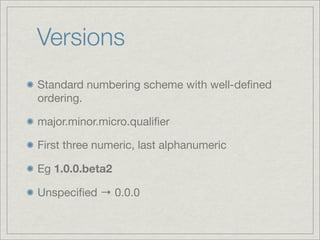
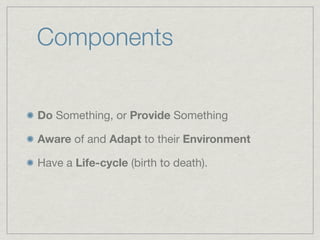
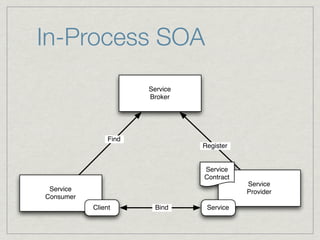
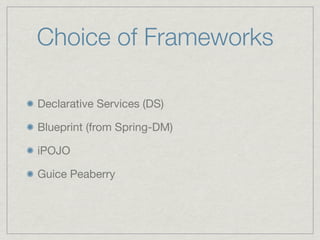
OSGi provides a module system for Java applications by treating JAR files as bundles with additional metadata specifying things like name, version, dependencies, and exports/imports. This allows for greater modularity by resolving dependencies and supporting side-by-side versions. Components in OSGi are bundles that can be dynamically installed, updated, and uninstalled. Annotations and services allow bundles to be configured and discover other bundles at runtime.







![Version Ranges
Open, closed or implicit
[1.0.0, 2.0.0] ! 1.0.0 ! version ! 2.0.0
[1.0.0, 2.0.0) ! 1.0.0 ! version < 2.0.0
Informally “1.*”
1 ! [1.0.0, ")
Unspecified ! [0.0.0, ")](https://image.slidesharecdn.com/jjugintrotoosgi-091227061946-phpapp01/85/Introduction-to-OSGi-Tokyo-JUG-27-320.jpg)




















![Starting Point...
import javax.sql.DataSource;
public class DbMailbox implements Mailbox {
private DataSource dataSource;
void setDataSource(DataSource ds) { /*...*/ }
void unsetDataSource(DataSource ds) { /*...*/ }
public long[] getAllMessages() {
// ...
}
}](https://image.slidesharecdn.com/jjugintrotoosgi-091227061946-phpapp01/85/Introduction-to-OSGi-Tokyo-JUG-86-320.jpg)
![Starting Point...
No OSGi API Used
import javax.sql.DataSource;
public class DbMailbox implements Mailbox {
private DataSource dataSource;
void setDataSource(DataSource ds) { /*...*/ }
void unsetDataSource(DataSource ds) { /*...*/ }
public long[] getAllMessages() {
// ...
}
}](https://image.slidesharecdn.com/jjugintrotoosgi-091227061946-phpapp01/85/Introduction-to-OSGi-Tokyo-JUG-87-320.jpg)
![Starting Point...
No OSGi API Used
import javax.sql.DataSource;
public class DbMailbox implements Mailbox {
private DataSource dataSource;
void setDataSource(DataSource ds) { /*...*/ }
void unsetDataSource(DataSource ds) { /*...*/ }
public long[] getAllMessages() {
// ...
}
} JavaBeans Style => Testable](https://image.slidesharecdn.com/jjugintrotoosgi-091227061946-phpapp01/85/Introduction-to-OSGi-Tokyo-JUG-88-320.jpg)
![Make it a Component
import javax.sql.DataSource;
@Component
public class DbMailbox implements Mailbox {
private DataSource dataSource;
@Reference(service = DataSource.class)
void setDataSource(DataSource ds) { /*...*/ }
void unsetDataSource(DataSource ds) { /*...*/ }
public long[] getAllMessages() {
// ...
}
}](https://image.slidesharecdn.com/jjugintrotoosgi-091227061946-phpapp01/85/Introduction-to-OSGi-Tokyo-JUG-89-320.jpg)