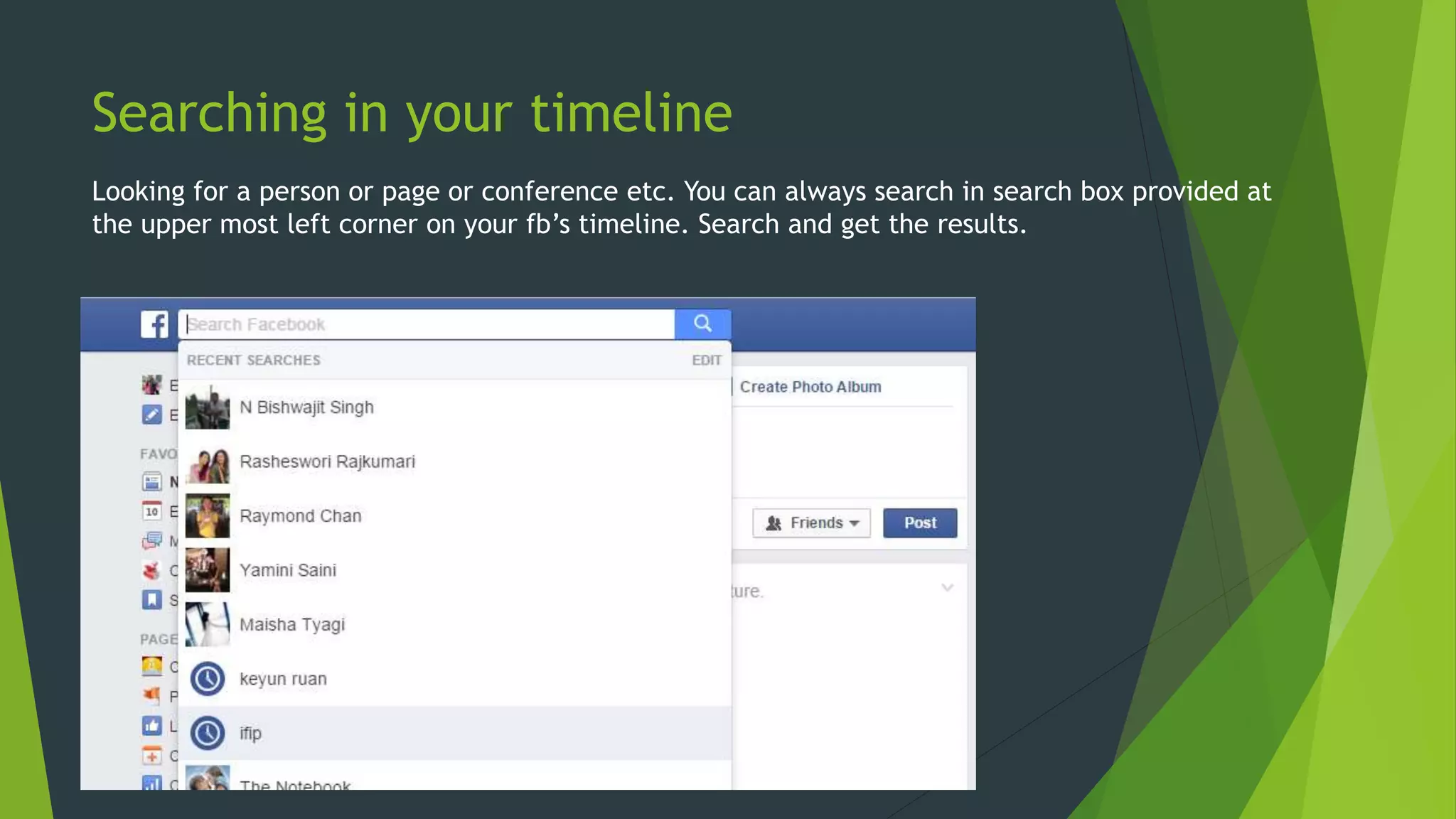
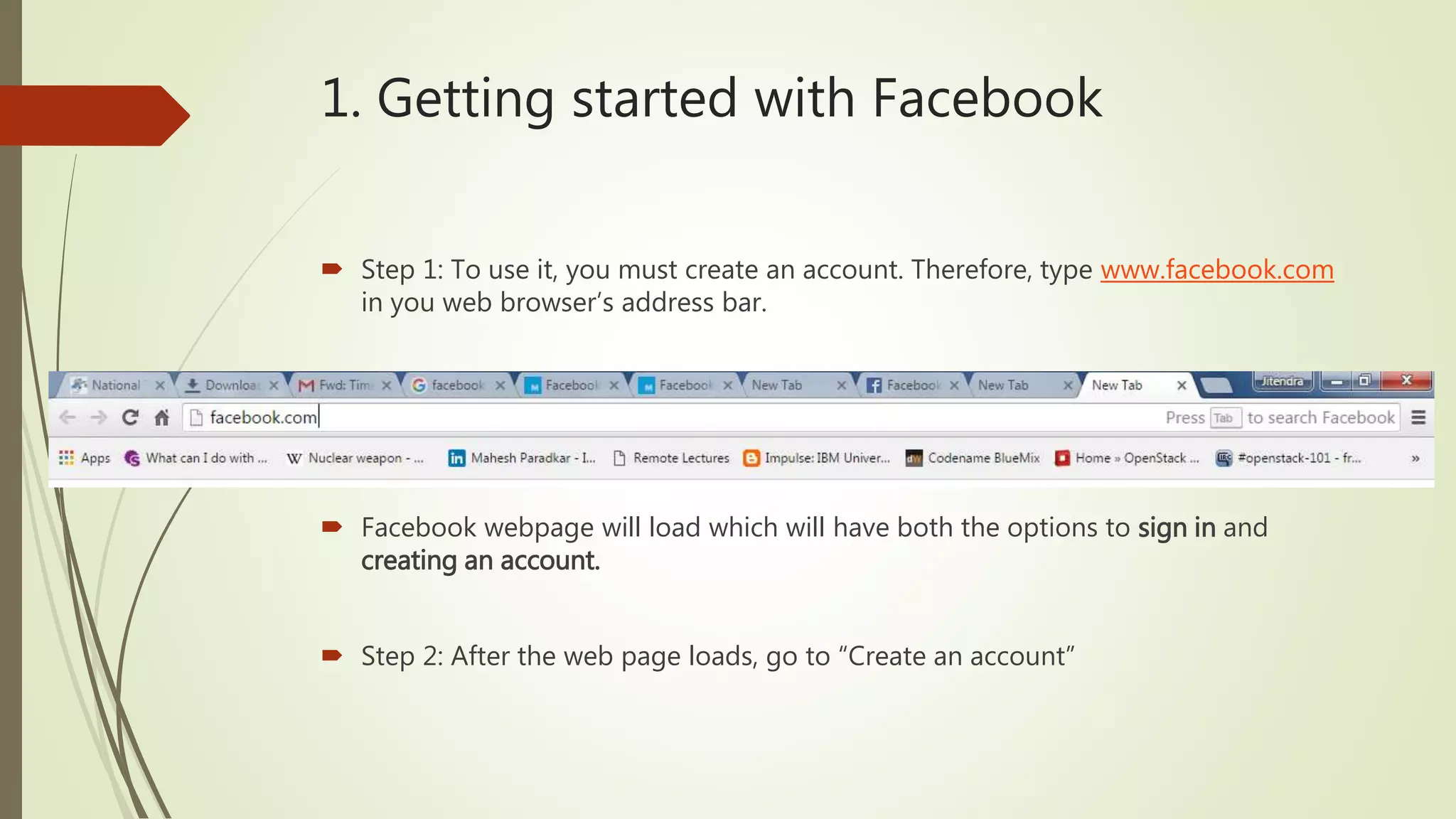
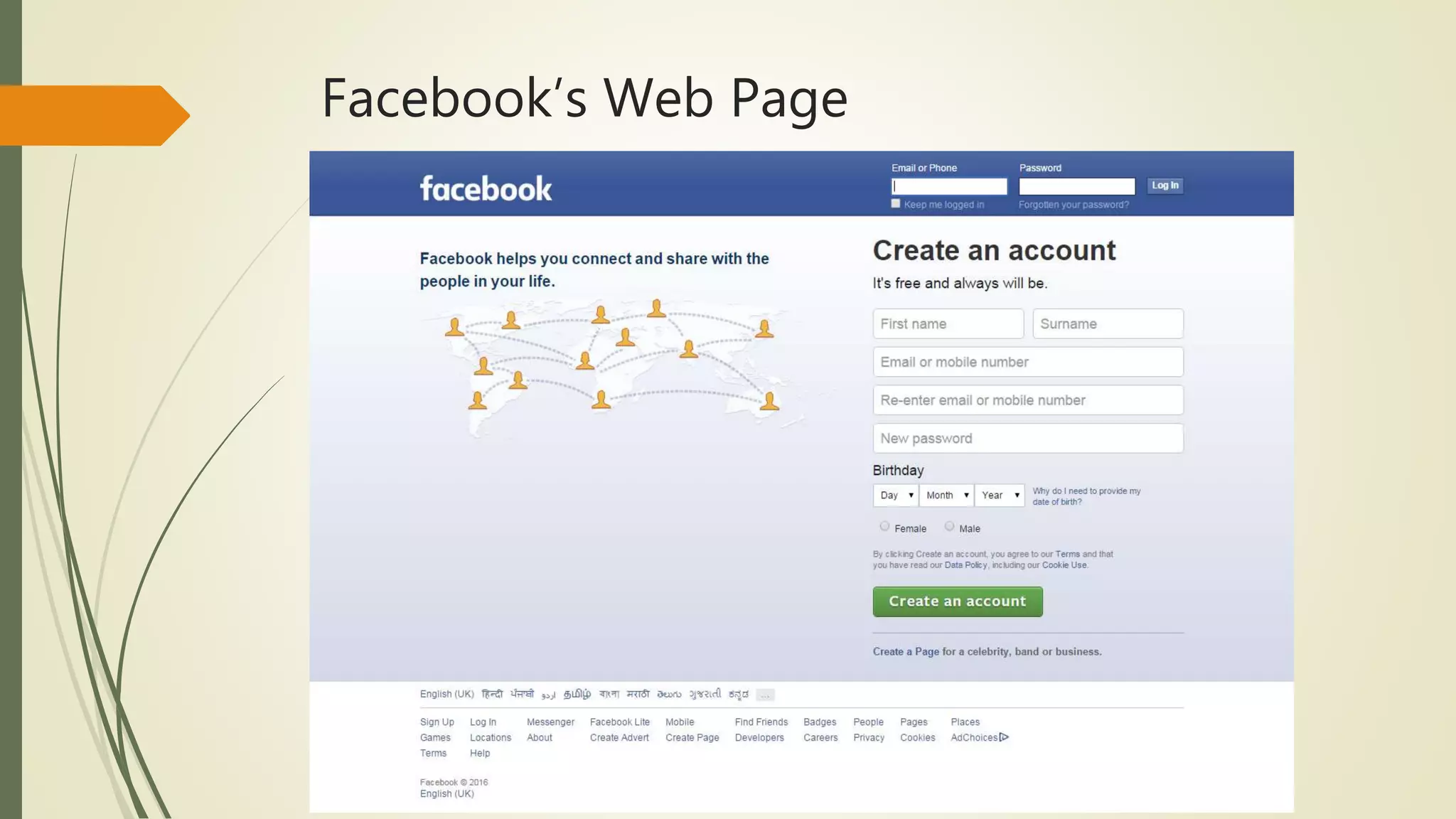
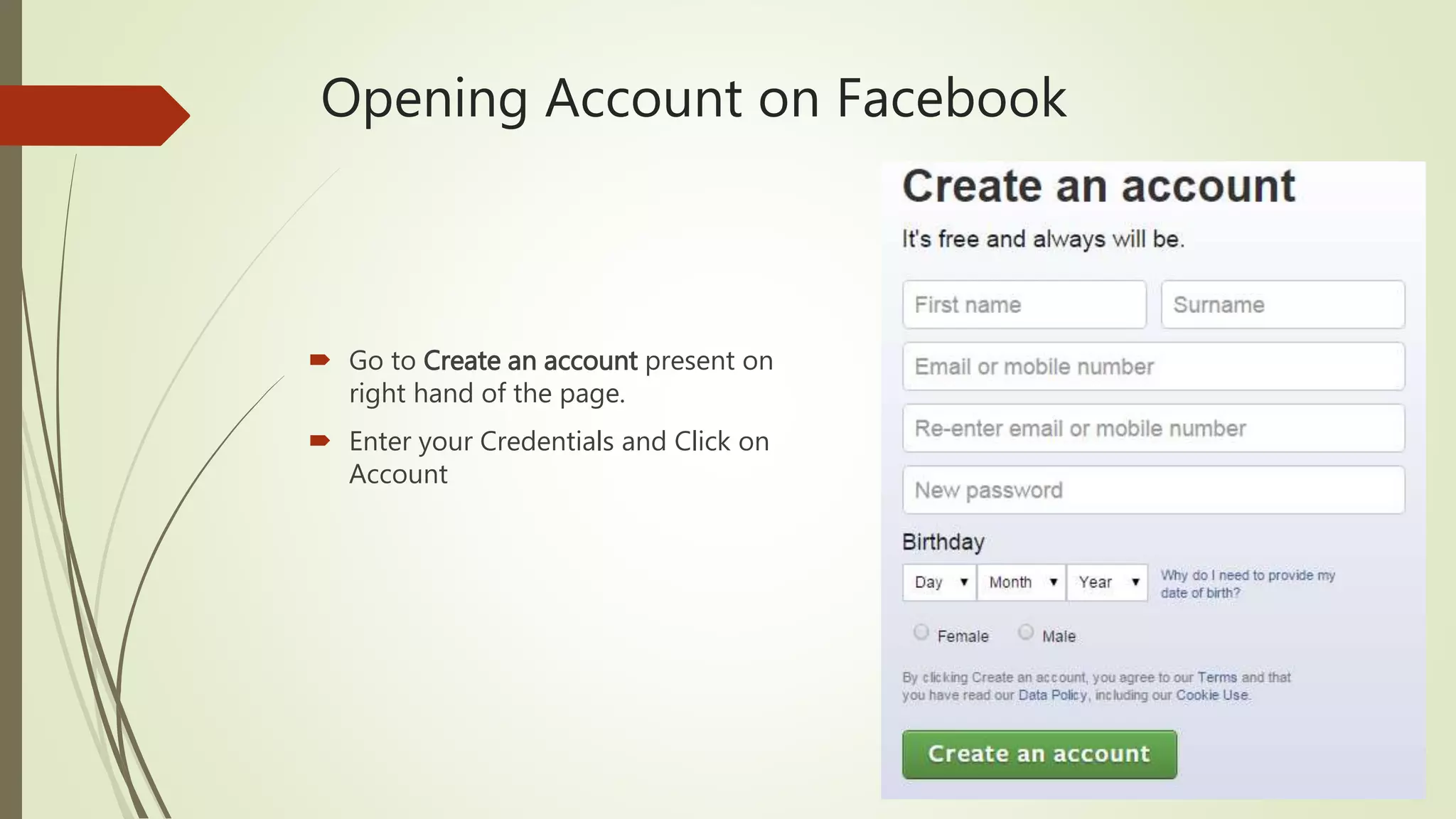
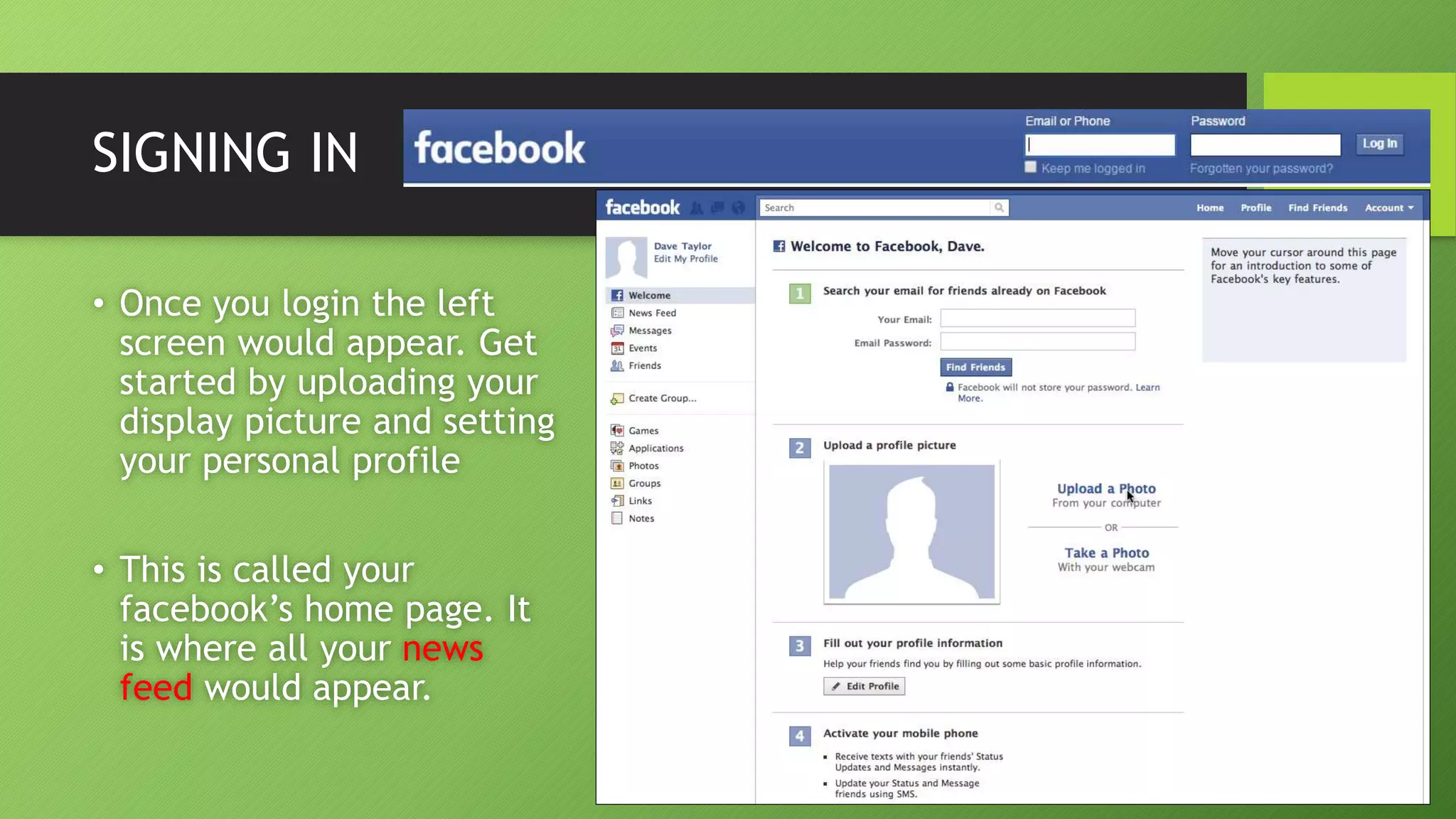
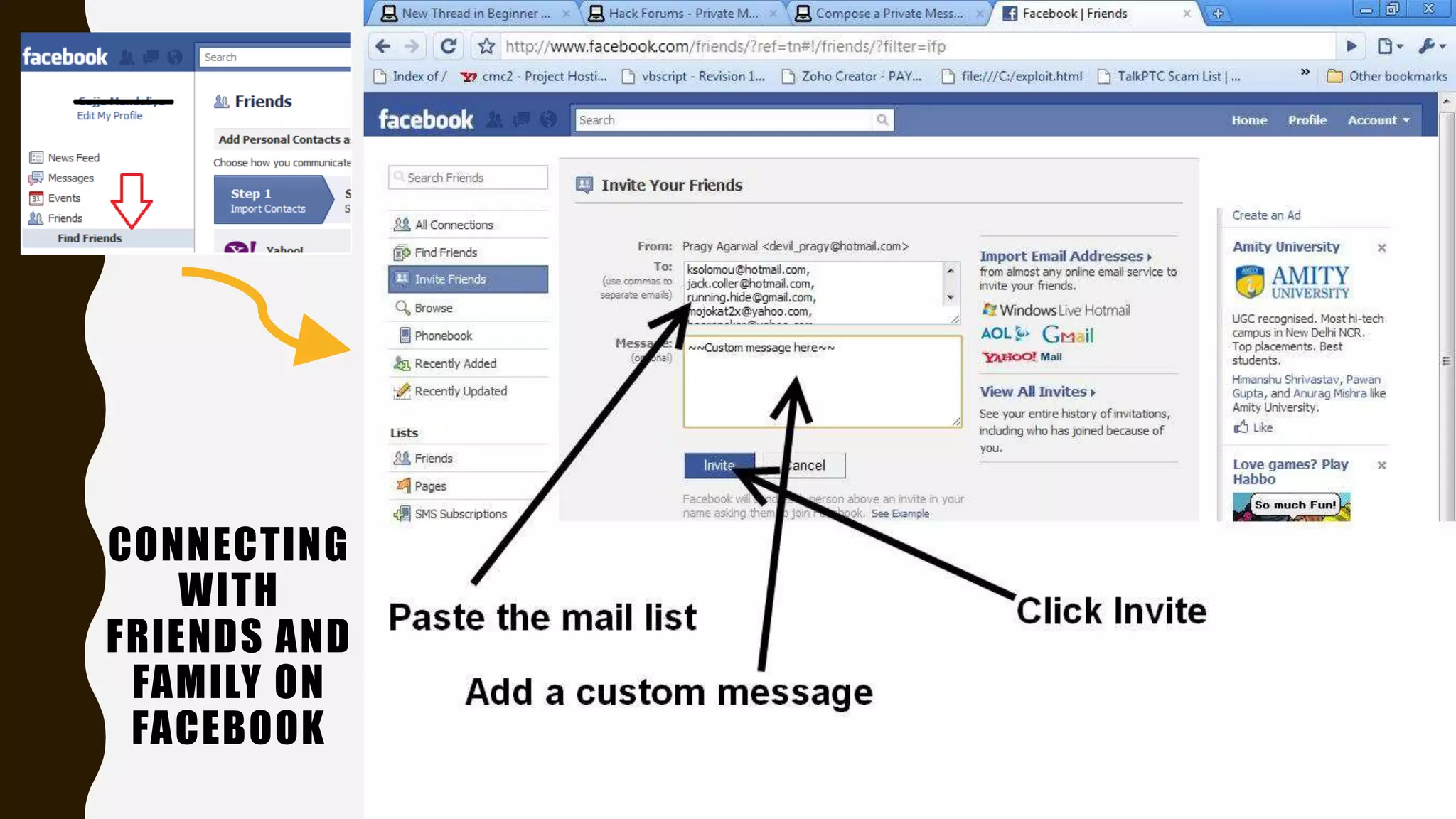
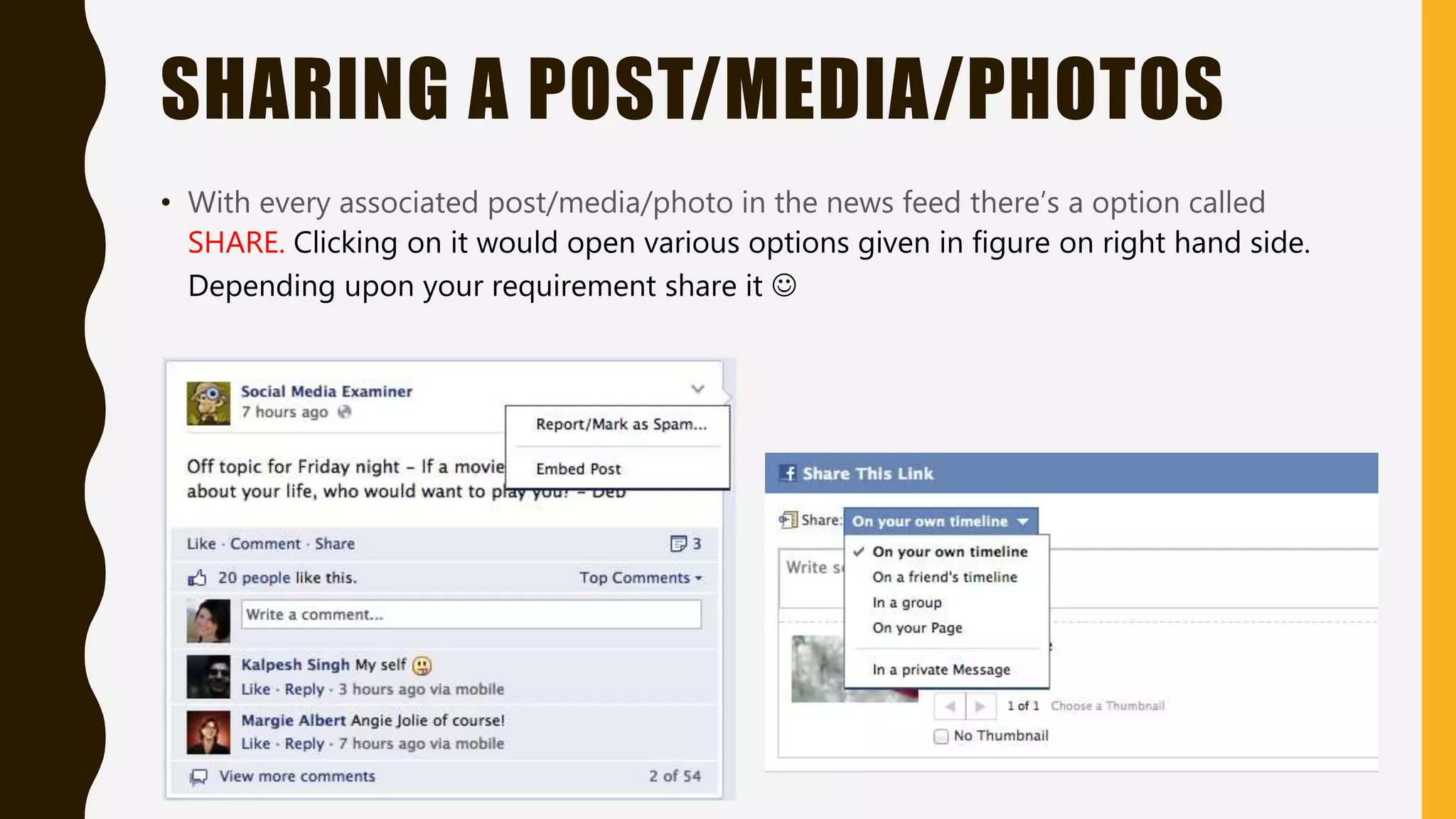
The document serves as a guide for new Facebook users, detailing the steps to create an account, connect with friends and family, and make posts. It explains key features such as the news feed, chat functionality, and photo sharing options. Additionally, it covers how to search the timeline and log out of Facebook.



![USING CHAT ON FB
• On the bottom right most corner on your fb’s page you see friends who are online or
who have recently gone offline.
• You can always start a chat by clicking on a name and a chat box would appear [See
the figure.]](https://image.slidesharecdn.com/facebook-160111131318/75/Introduction-to-Facebook-12-2048.jpg)

![Creating Photo Album
• To upload a photo album on Facebook’s timeline, press on
• A pop up would appear which tells you to locate the photos on your personal
computer.
• Locate the file and click on Open. Once the photos gets loaded the following
picture will appear. [See next slide]](https://image.slidesharecdn.com/facebook-160111131318/75/Introduction-to-Facebook-15-2048.jpg)