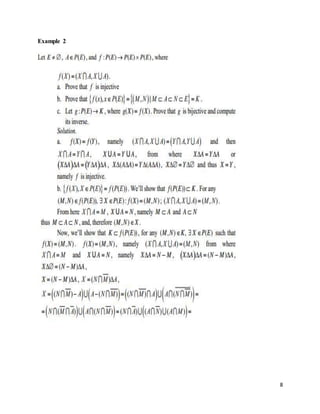
The document is an assignment from Bahir Dar University covering topics in complexity theory, including characteristic functions, complexity classes, and Big-O notation. It provides definitions, examples, and mathematical proofs related to Turing machines, deterministic and nondeterministic computation, and various complexity classes such as L and P. Key concepts discussed also include simulation and separation theorems, as well as the relationships between different computational models.











![11
computations that meet the defining resource bounds of another class. The containment of
nondeterministic logarithmic space (NL) in polynomial time (P), and the equality of the class P
with alternating logarithmic space, are simulation theorems. Separation theorems show that
certain complexity classes are distinct. Complexity theory currently has precious few of these.
The main tool used in those separation theorems we have is called diagonalization.
Time and Space Complexity Classes
DTIME[t(n)] is the class of languages decided by deterministic Turing machines of time com-
plexity t(n).
DSPACE[s(n)] is the class of languages decided by deterministic Turing machines of space
complexity s(n).
The following are the canonical complexity classes:
L (complexity)
In computational complexity theory, L (also known as LSPACE) is the complexity class
containing decision problems that can be solved by a deterministic Turing machine using a
logarithmic amount of memory space. Logarithmic space is sufficient to hold a constant number
of pointers into the input and a logarithmic number of Boolean flags and many basic log space
algorithms use the memory in this way.
L is a subclass of NL, which is the class of languages decidable in logarithmic space on a
nondeterministic Turing machine. A problem in NL may be transformed into a problem of
reachability in a directed graph representing states and state transitions of the nondeterministic
machine, and the logarithmic space bound implies that this graph has a polynomial number of
vertices and edges, from which it follows that NL is contained in the complexity class P of
problems solvable in deterministic polynomial time. Thus L ⊆ NL ⊆ P. The inclusion of L into P
can also be proved more directly: a decider using O(log n) space cannot use more than
2O(log n) = nO(1) time, because this is the total number of possible configurations.
L further relates to the class NC in the following way: NC1 ⊆ L ⊆ NL ⊆ NC2. In words, given a
parallel computer C with a polynomial number O(nk) of processors for some constant k, any
problem that can be solved on C in O(log n) time is in L, and any problem in L can be solved in
O(log2 n) time on C.](https://image.slidesharecdn.com/introductiontocomplexitytheory-assignment-160519035458/85/Introduction-to-complexity-theory-assignment-13-320.jpg)








