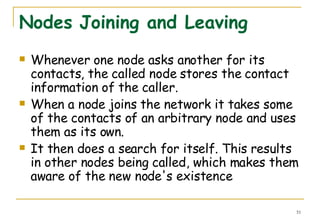
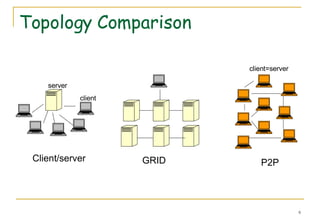
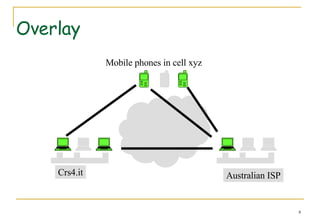
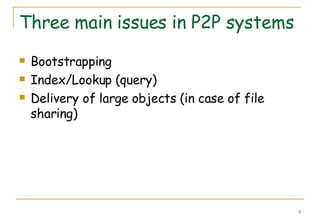
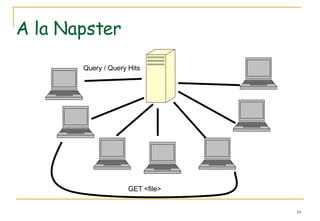
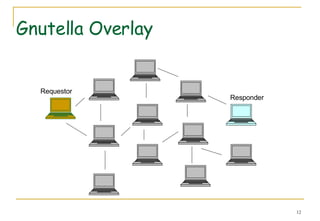
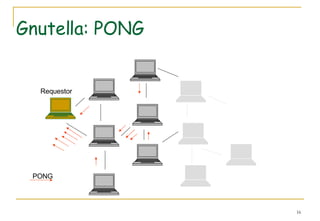
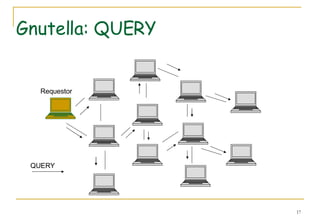
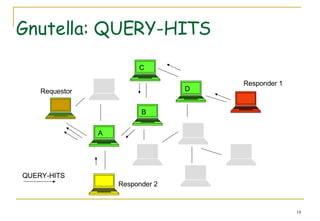
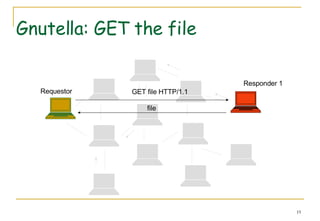
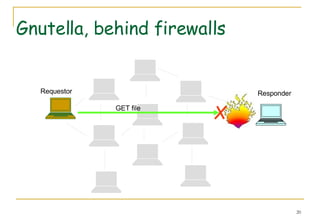
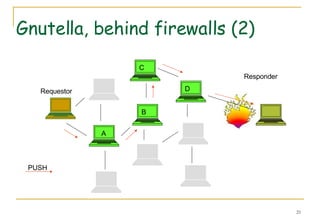
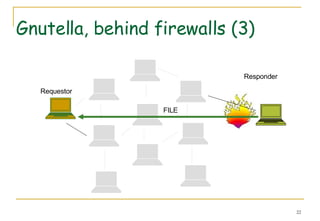
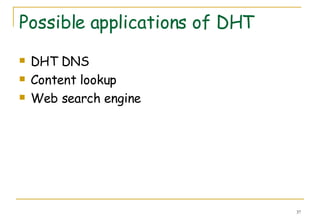
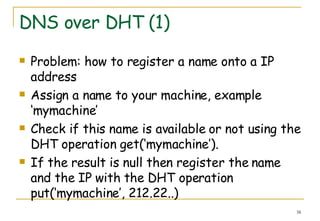
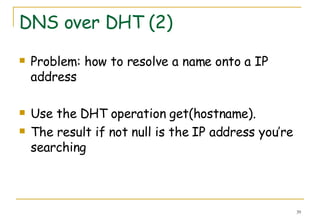
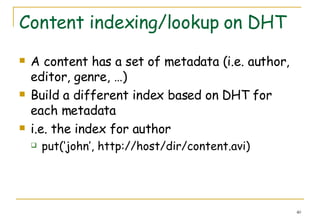
This document provides an introduction to peer-to-peer (P2P) computer networks. It discusses how P2P networks rely on the computing power and bandwidth of participants rather than centralized servers. The document then covers several examples of P2P networks including Gnutella and Kademlia, and discusses techniques like distributed hash tables, queries, and node joining/leaving.
![P2P and GRID From Wikipedia Grid computing […] performs higher throughput computing by taking advantage of many networked computers to model a virtual computer architecture.](https://image.slidesharecdn.com/introduction-p2p3978/85/Introduction-P2p-5-320.jpg)
![Web crawlers and DHT Assume a network of nodes in a DHT Assume each node runs also a crawler. For each word in a Web page it performs Put(word,URL) So a distributed index of the Web is built[1]](https://image.slidesharecdn.com/introduction-p2p3978/85/Introduction-P2p-42-320.jpg)
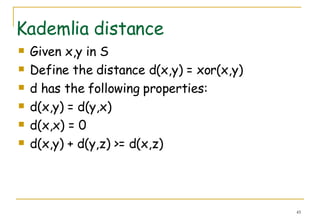
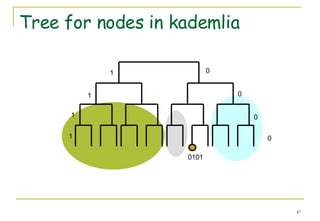
![Kademlia S = [00 ....0 - 11 ...1] the set of 160bit strings Each node has a node ID in S For each 'key' hash(key) is in S](https://image.slidesharecdn.com/introduction-p2p3978/85/Introduction-P2p-44-320.jpg)
![k-Buckets in kademlia Each node stores an array of lists: list[i] i = 0,1, ... , 159 list[i] stores up to k tuples: (IP,port,ID) list[i] stores tuples whose ID is: 2^i <= D(this,ID)< 2^(i+1) list[i] is ordered as LRS (last recent seen)](https://image.slidesharecdn.com/introduction-p2p3978/85/Introduction-P2p-46-320.jpg)
![k-Buckets in kademlia For small values of i, list[i] has few elements For larger values of i, list[i] is likely to contain more elements.](https://image.slidesharecdn.com/introduction-p2p3978/85/Introduction-P2p-48-320.jpg)
![Lookup in Kademlia FIND_NODE(hash(k)) Compute D=xor(this,hash(key)) Find a tuples in list[i] (i.e. a=3) Send FIND_NODE(hash(key)) to the 3 nodes I receive other node addresses. Reiterate FIND_NODE(hash(key)) on them. Stop when no new addresses are received](https://image.slidesharecdn.com/introduction-p2p3978/85/Introduction-P2p-50-320.jpg)