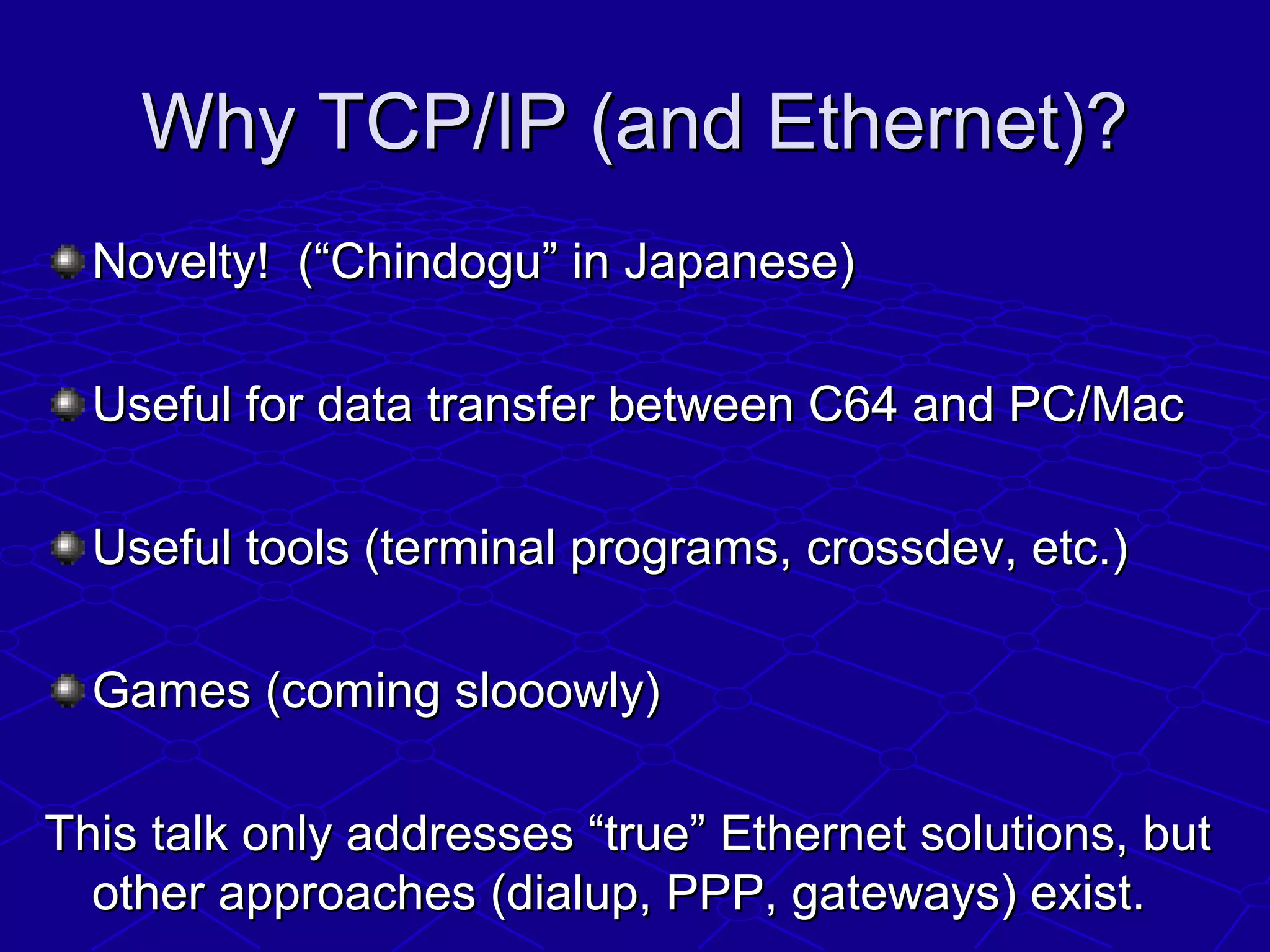
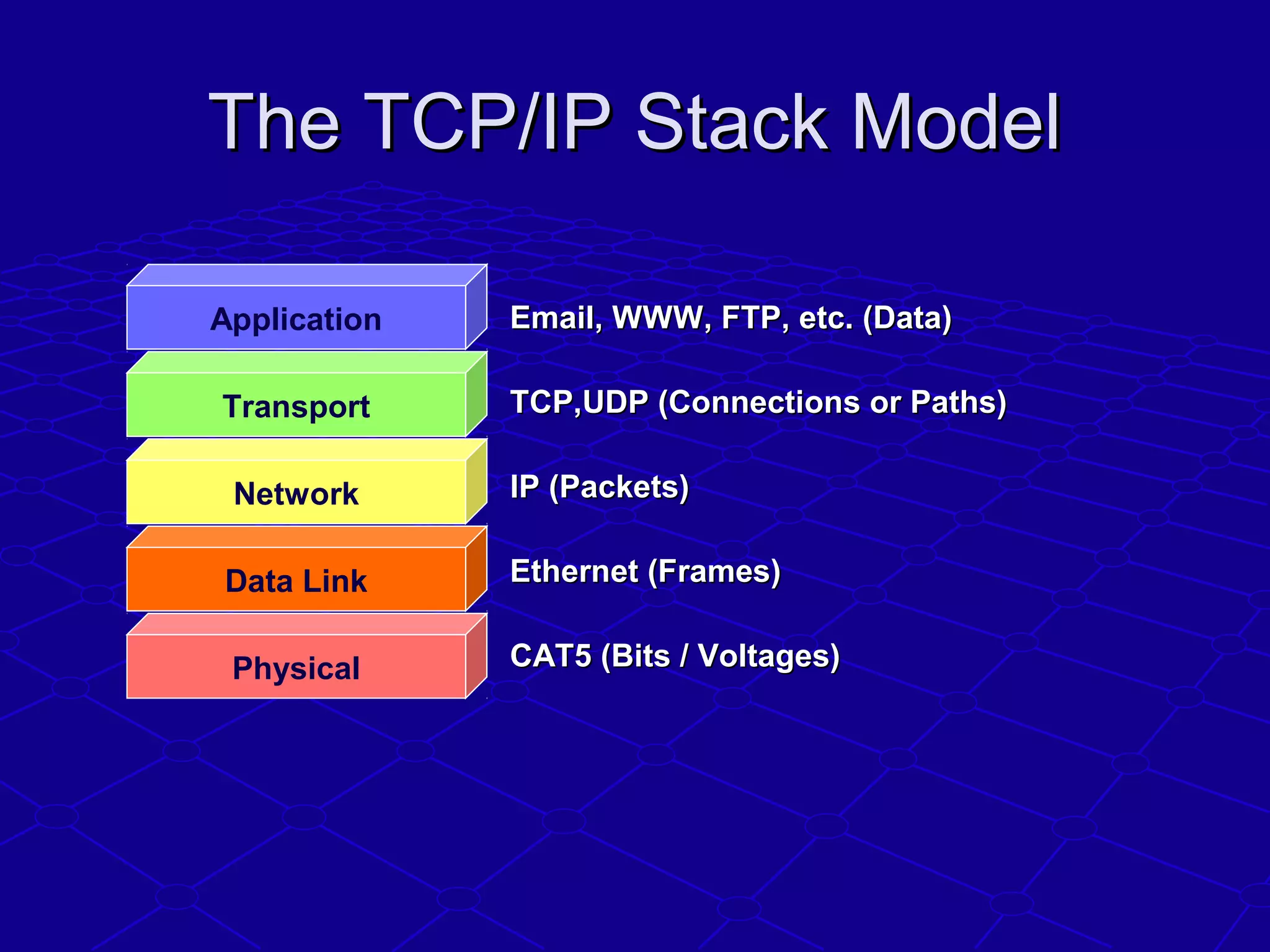
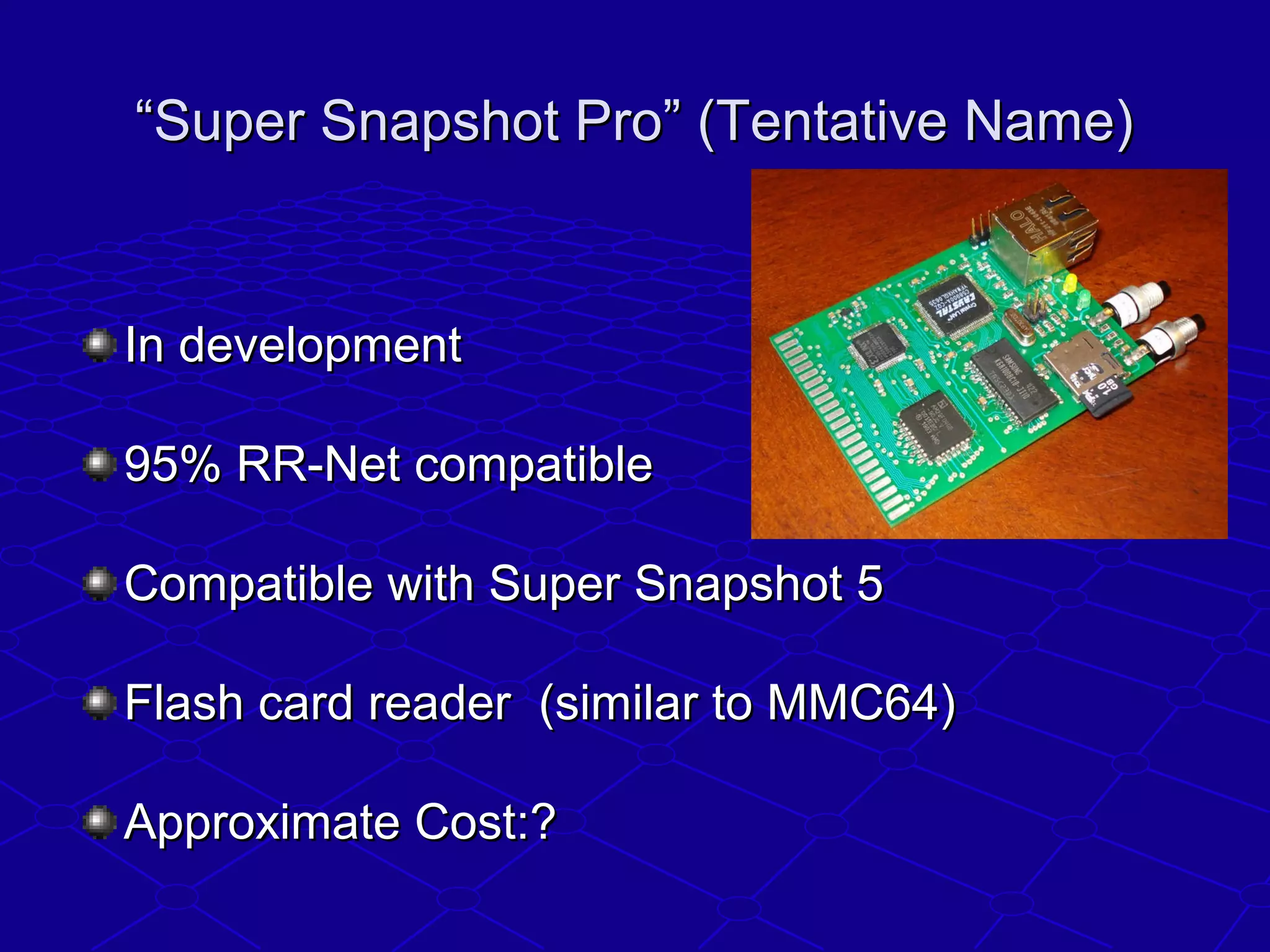
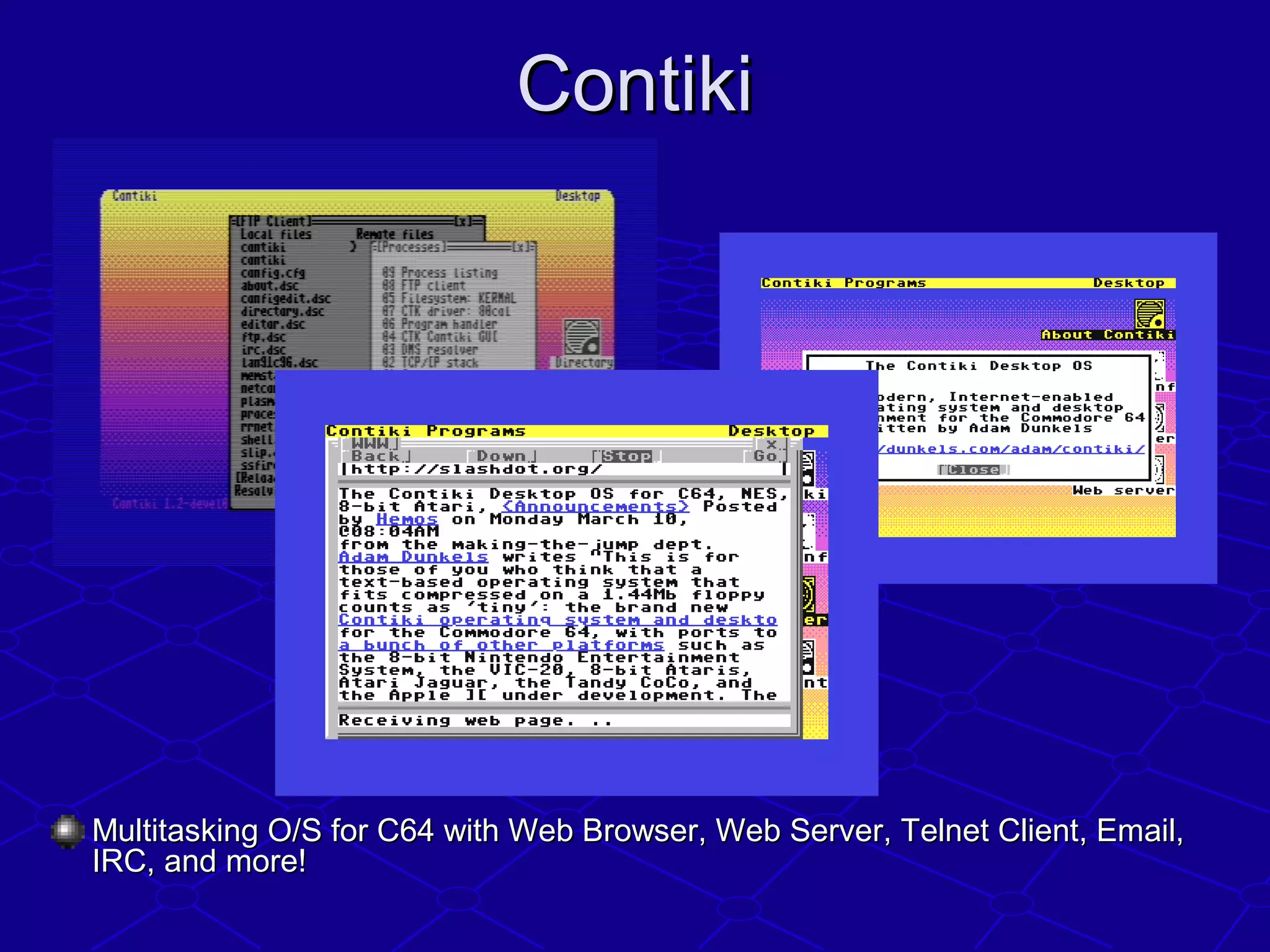
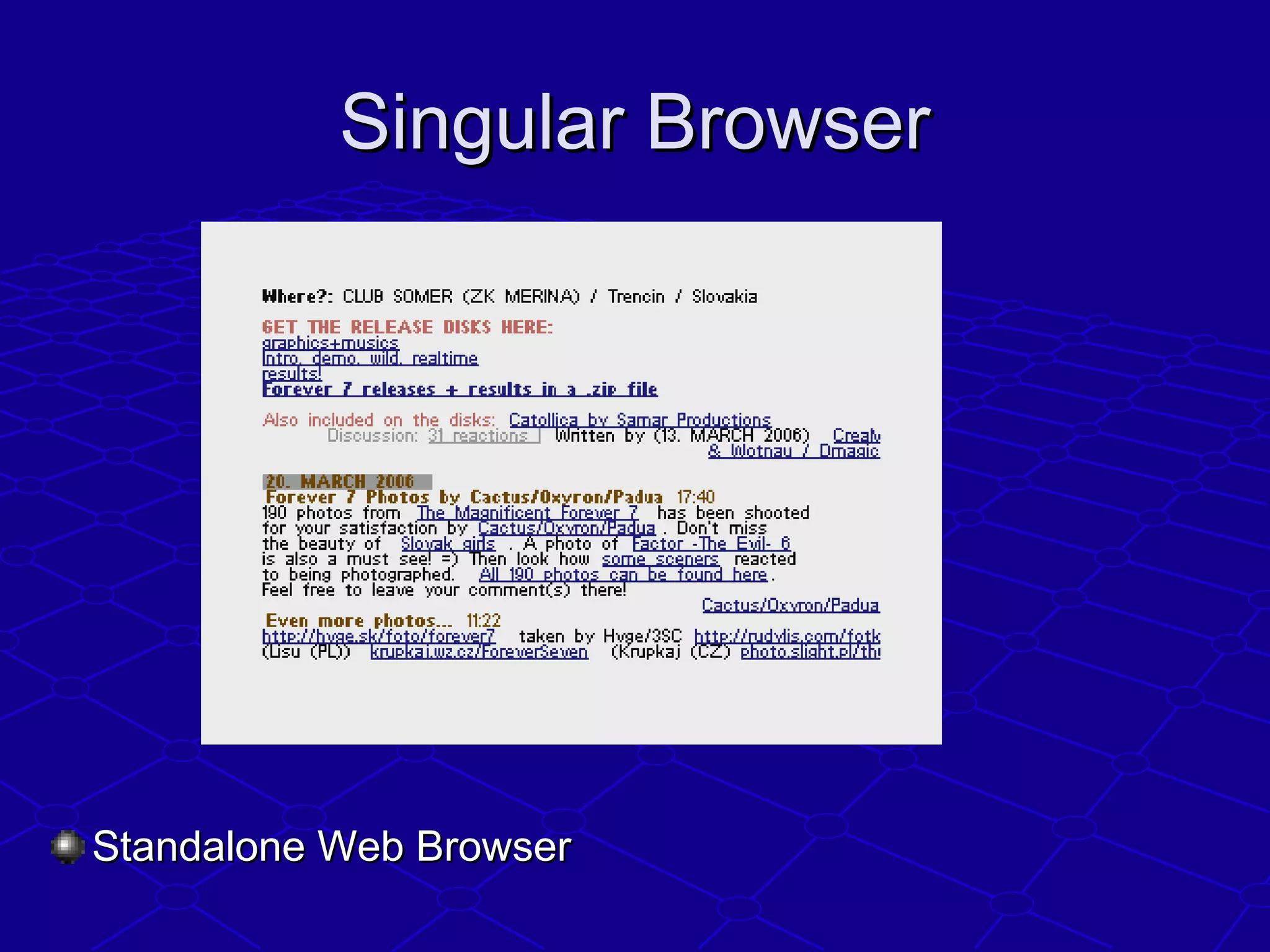
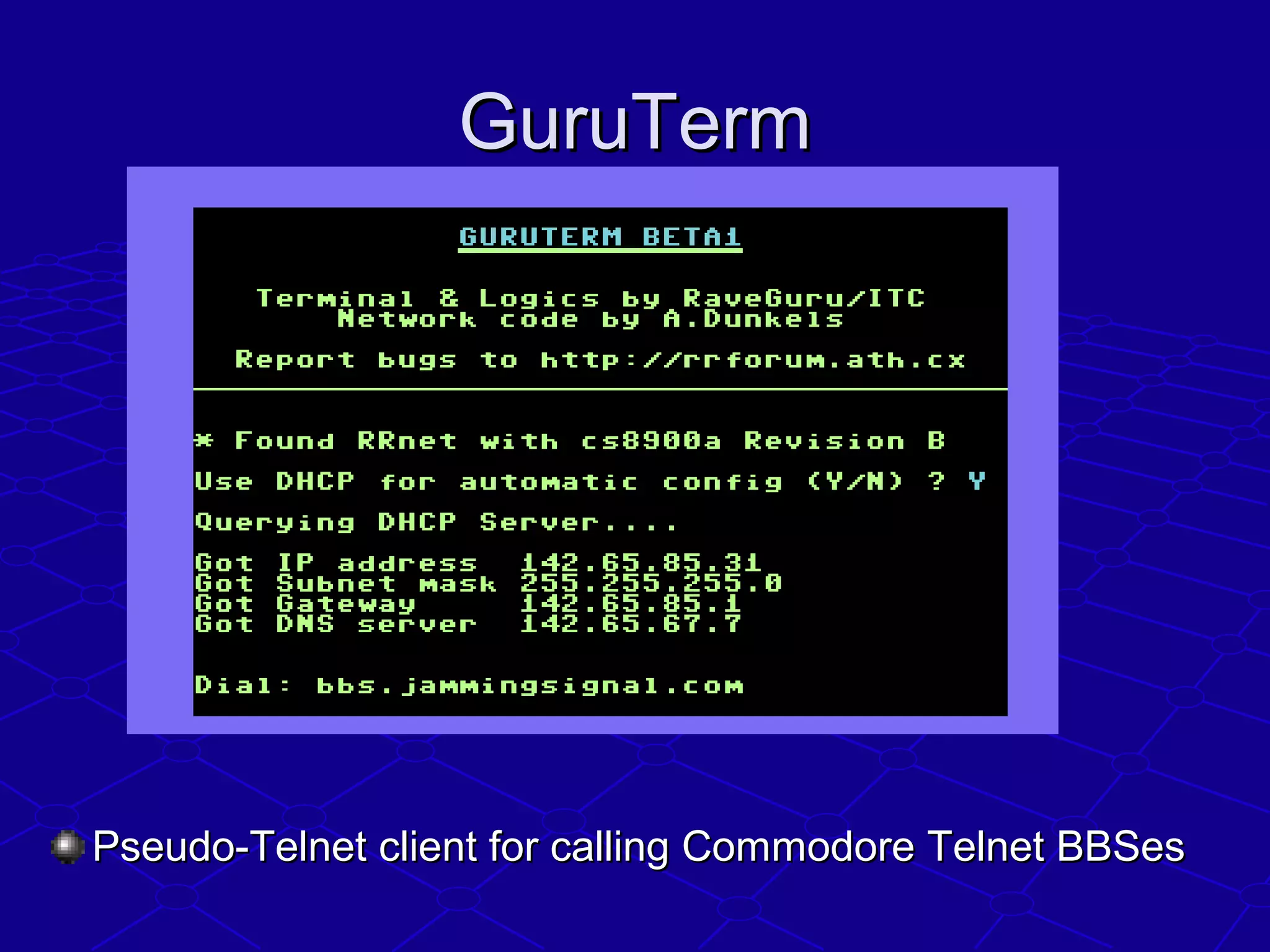
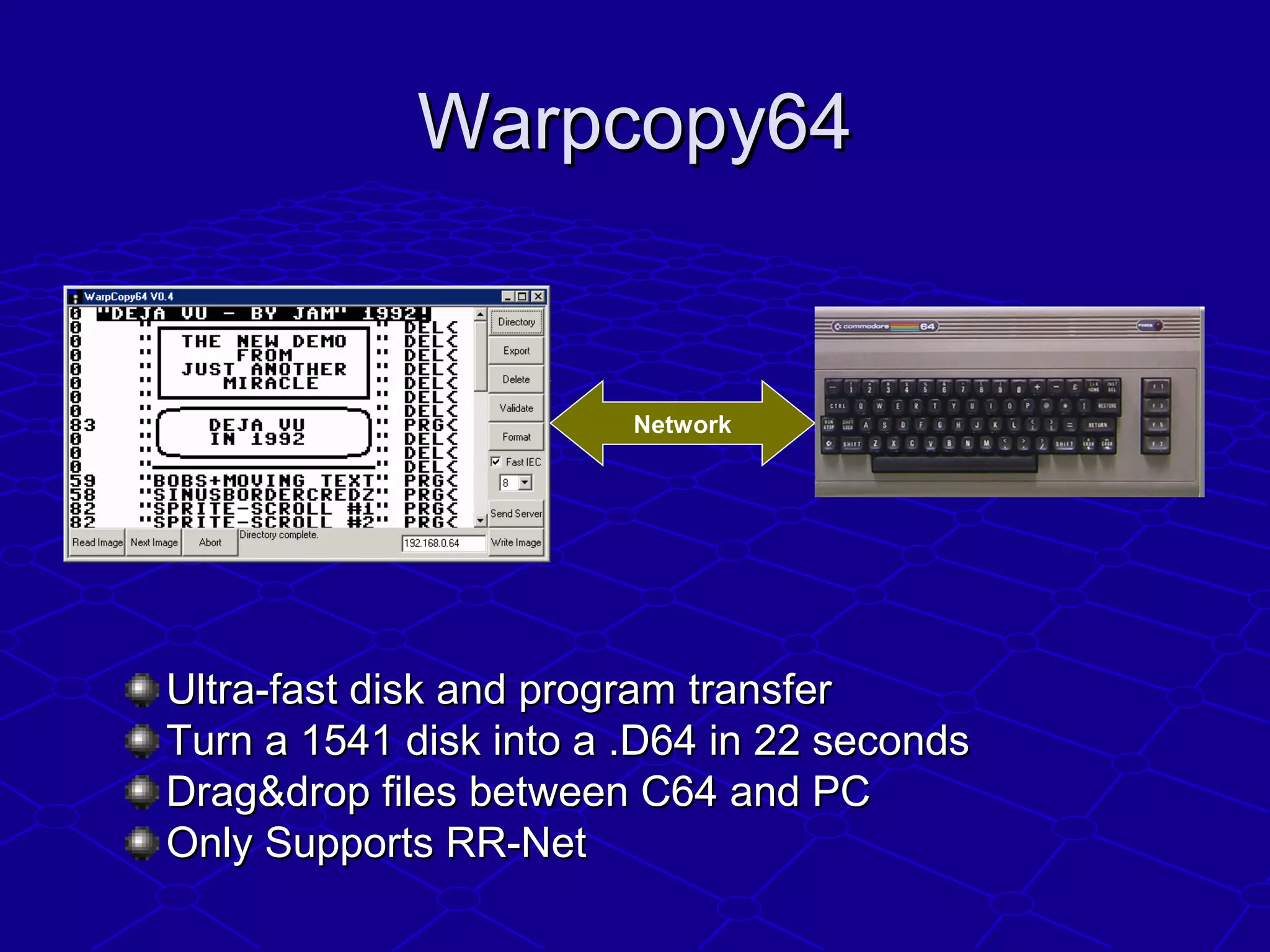
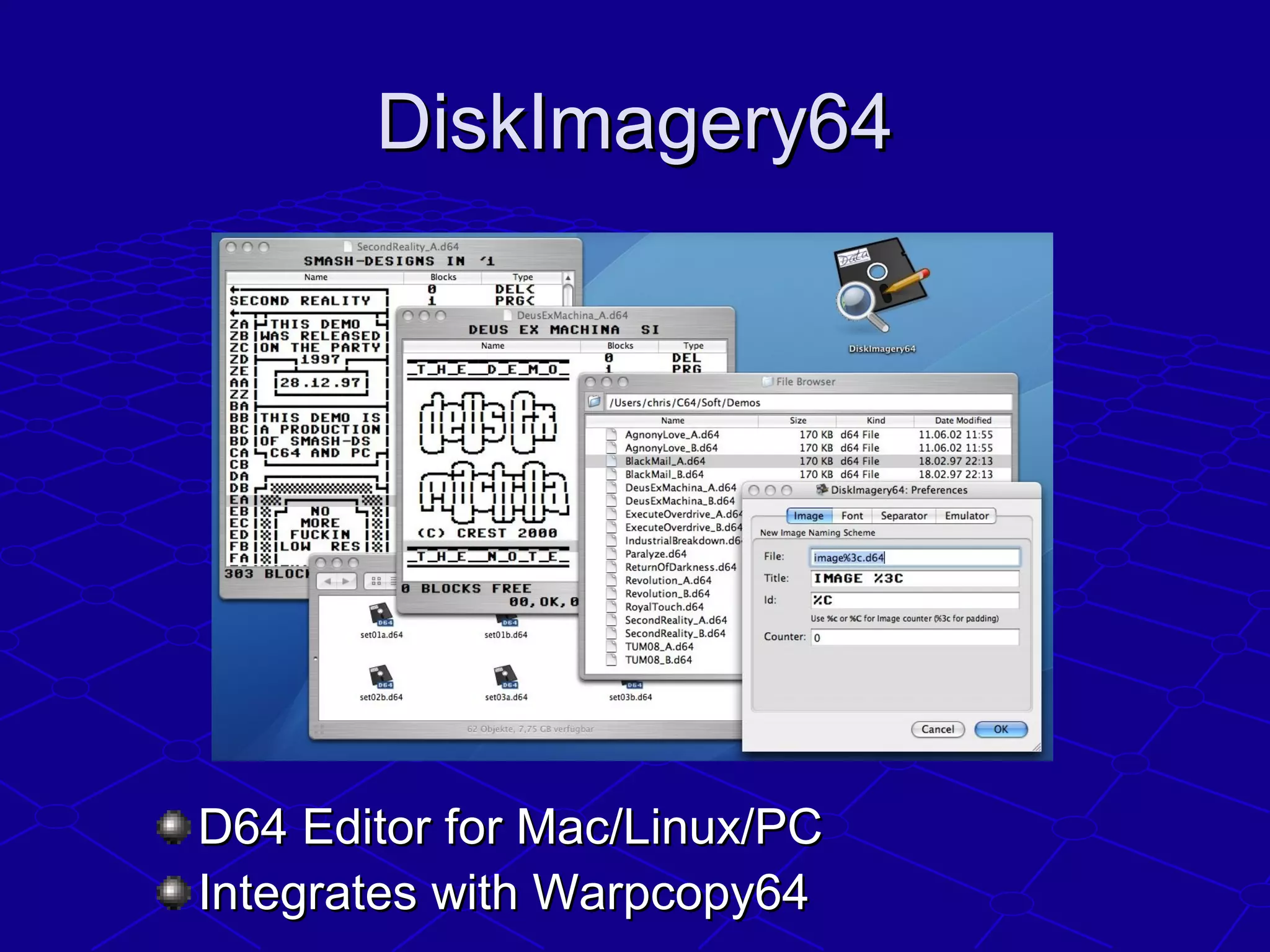
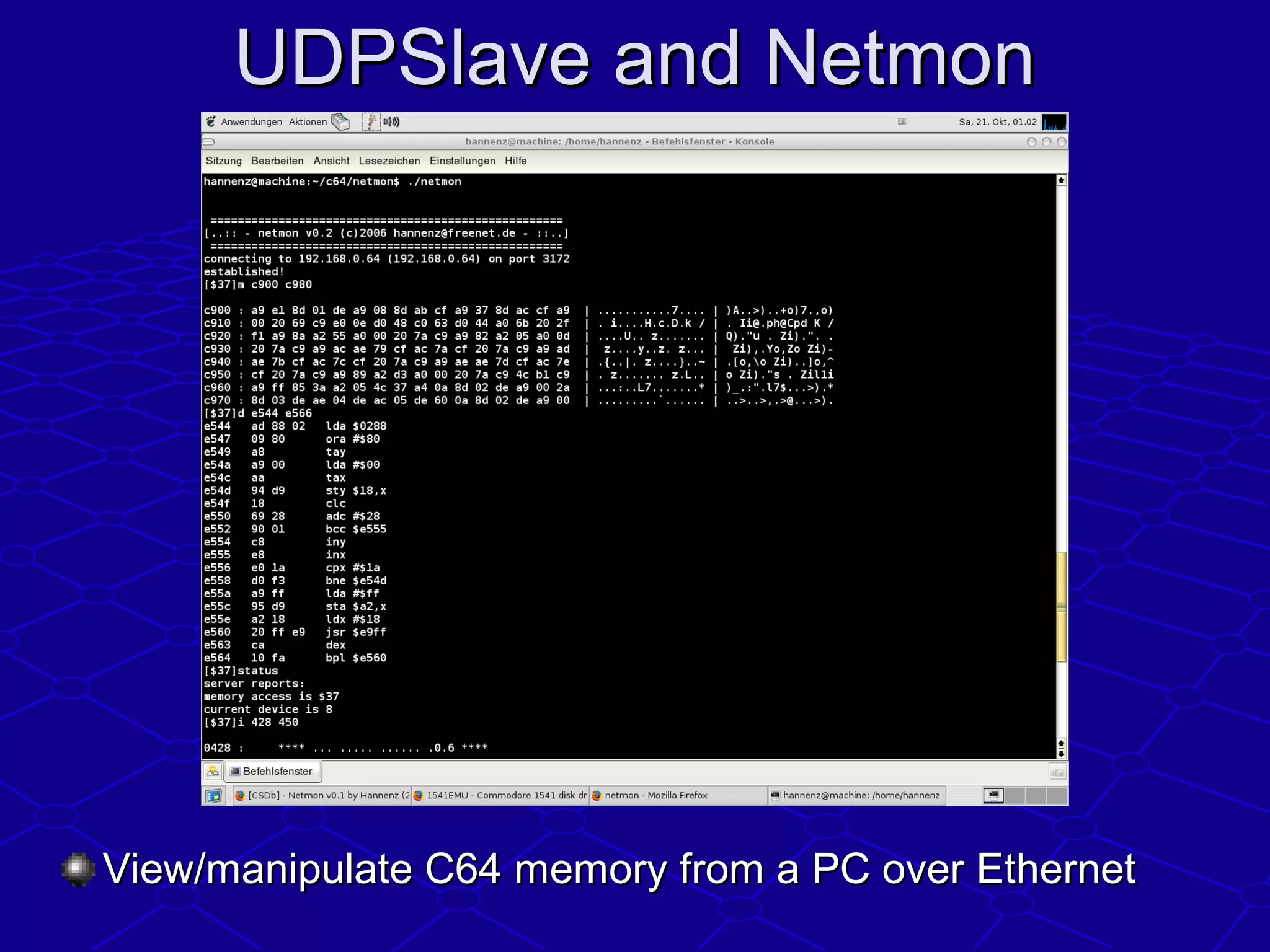
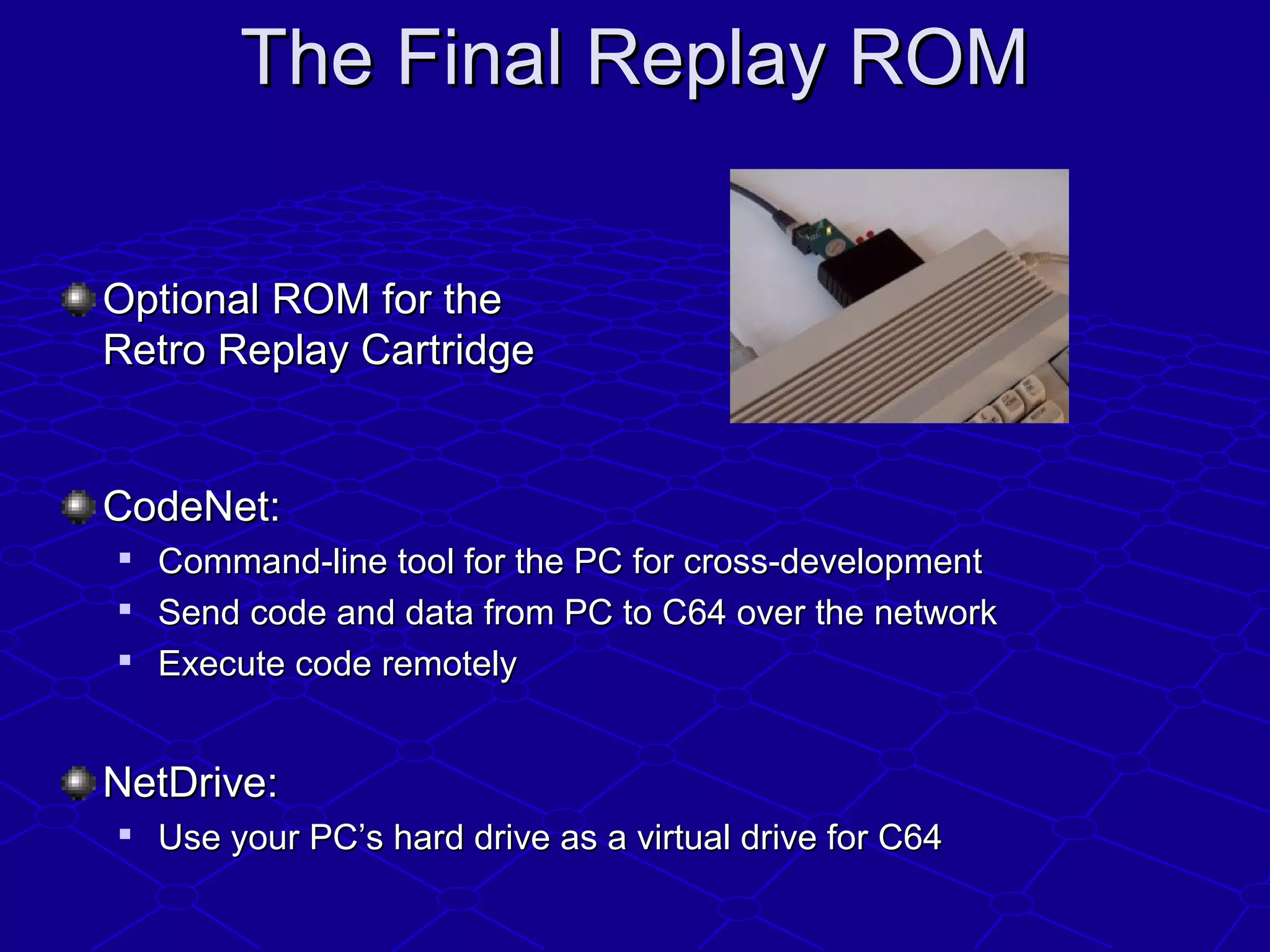
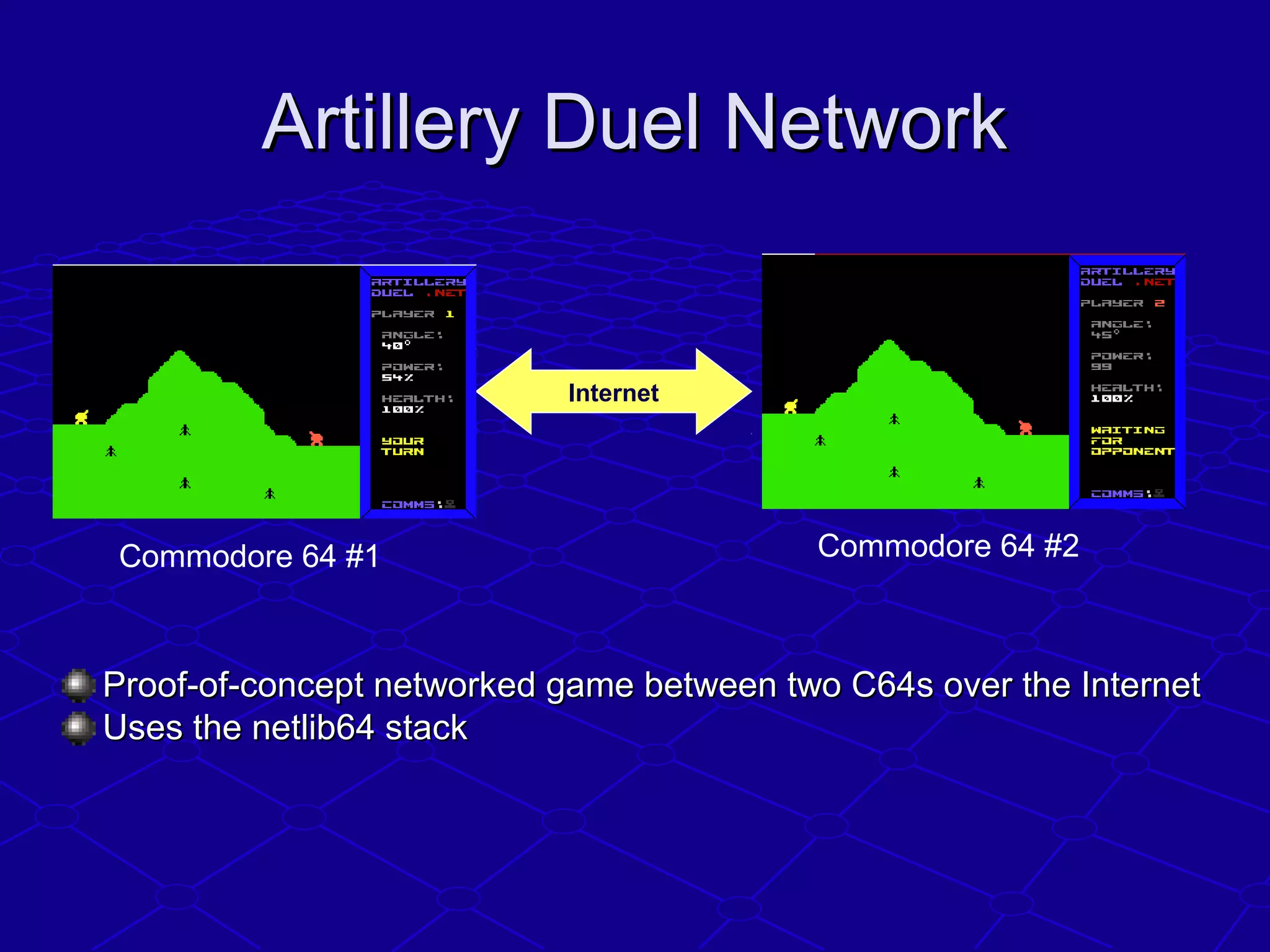
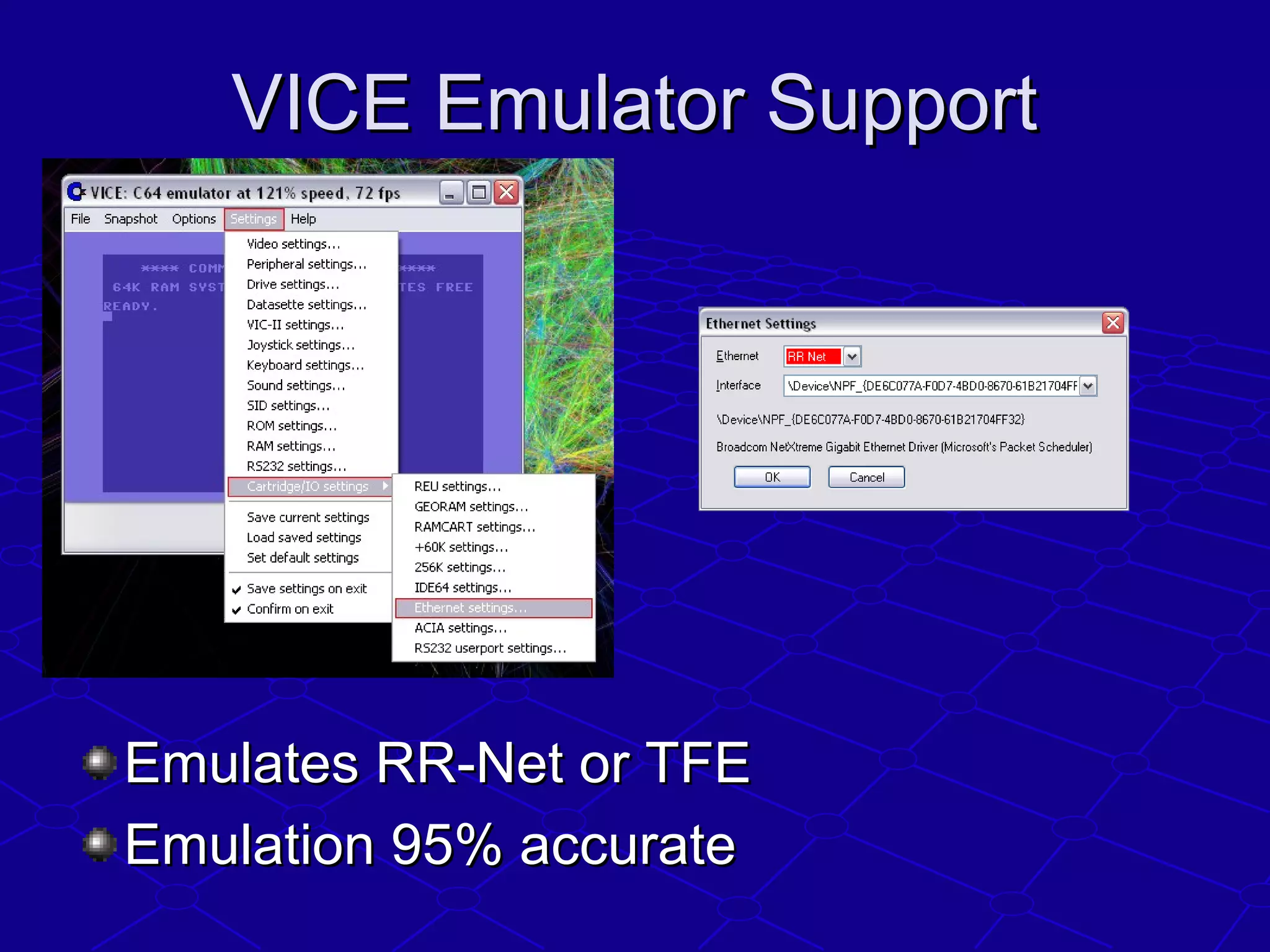
The document discusses internet technology for the Commodore 64, highlighting the importance of TCP/IP and Ethernet for data transfer between devices. It covers hardware and software options, including various network solutions and tools available for enhanced connectivity and functionality. The presentation also outlines future aspirations for standalone Ethernet cartridges and increased gaming possibilities.