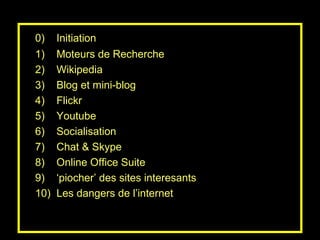
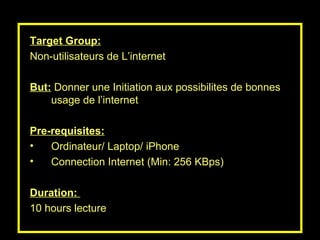
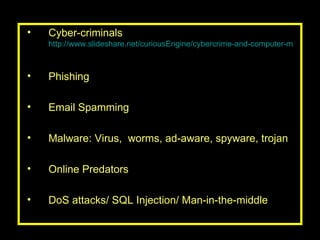
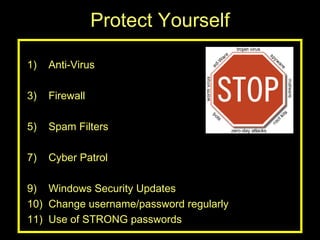
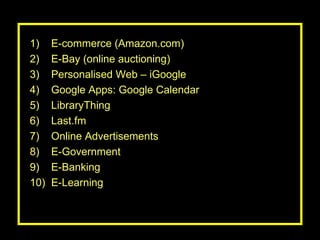
The document outlines a program aimed at introducing non-users to the internet, covering various tools and platforms such as search engines, social media, and online communication. It discusses the potential dangers of internet usage, including cybercrime and online predators, and provides guidelines for safe usage. Additionally, it highlights the various opportunities that the internet offers, such as e-commerce, e-learning, and online collaboration tools.