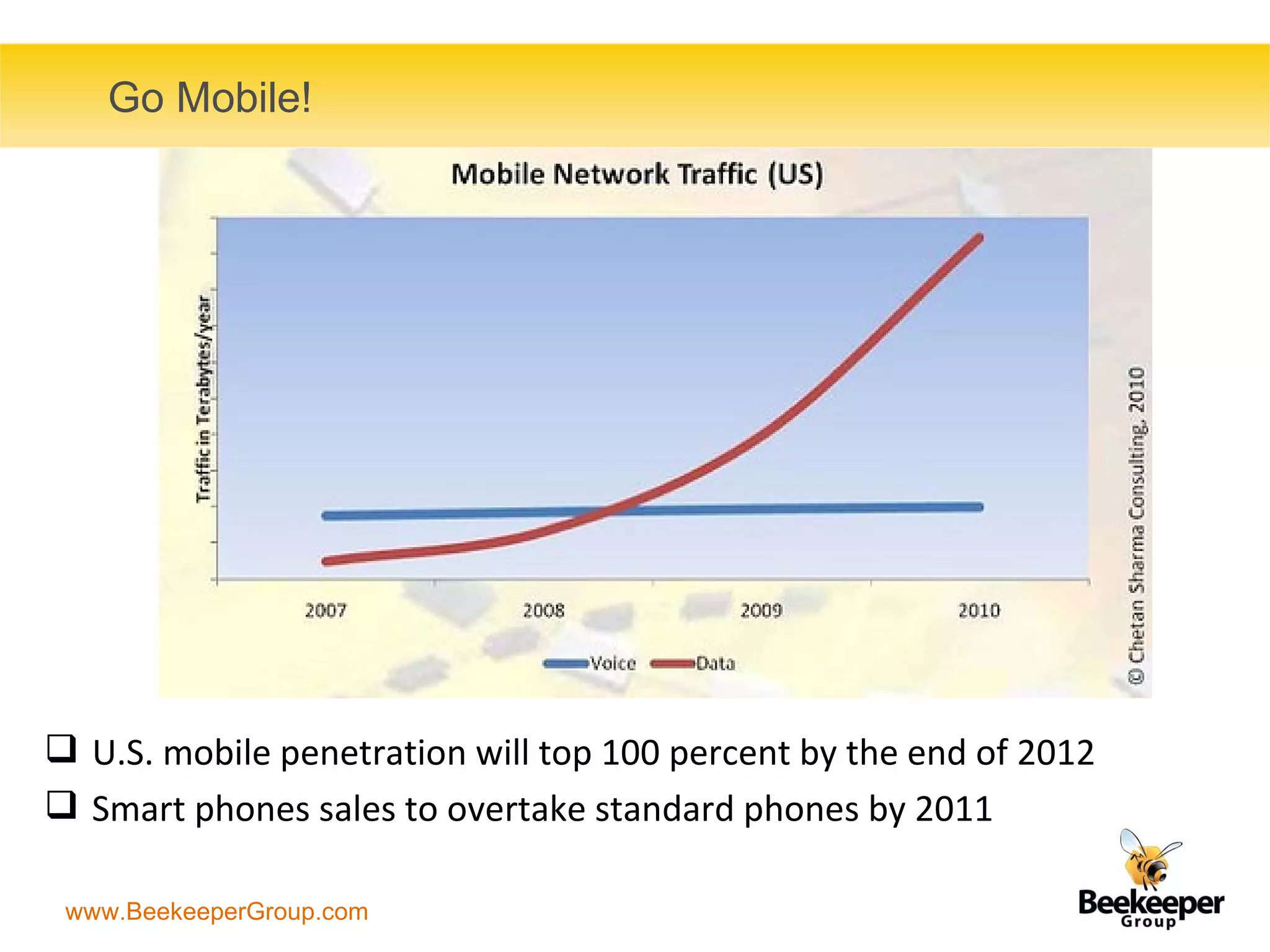
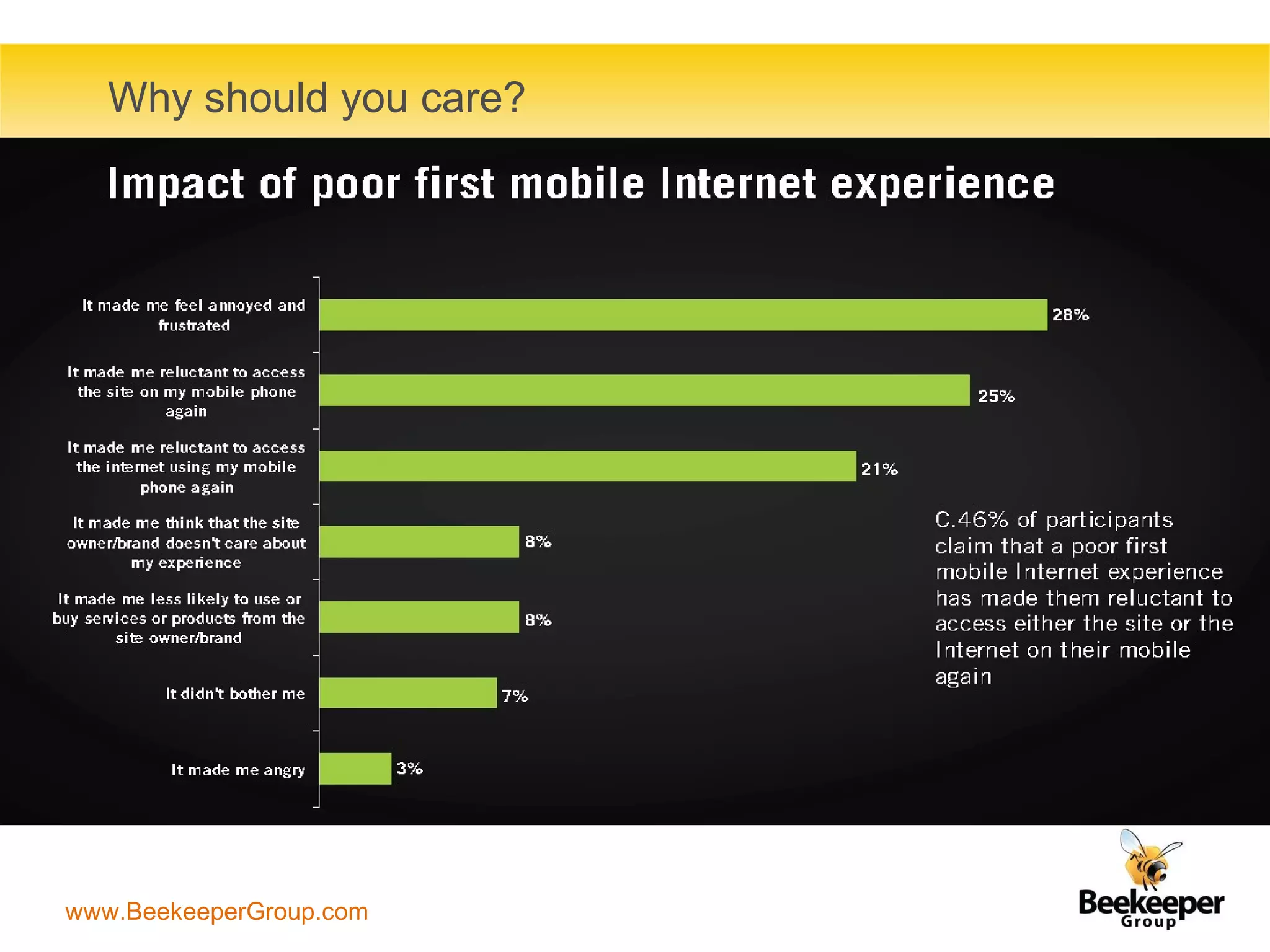
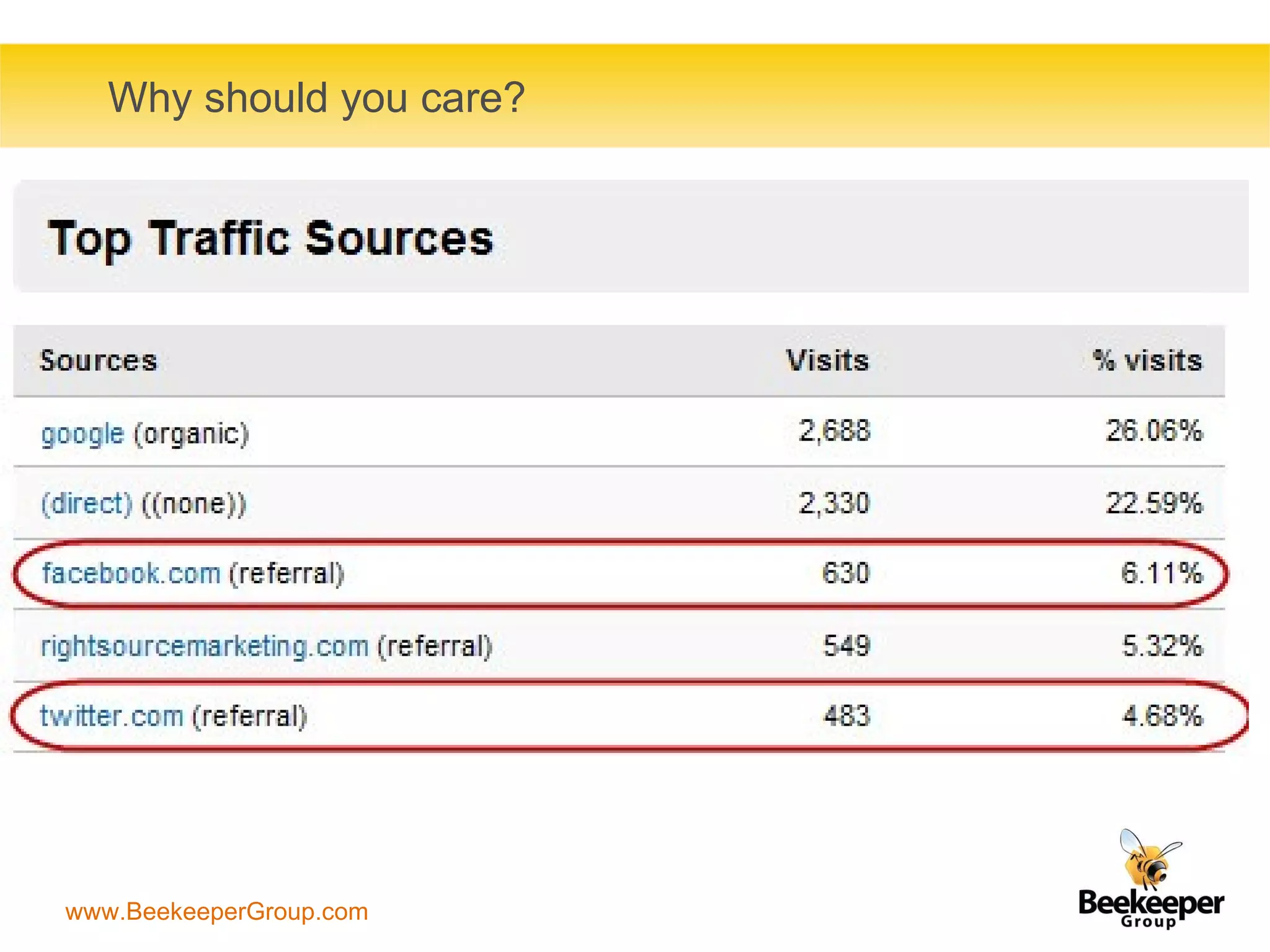
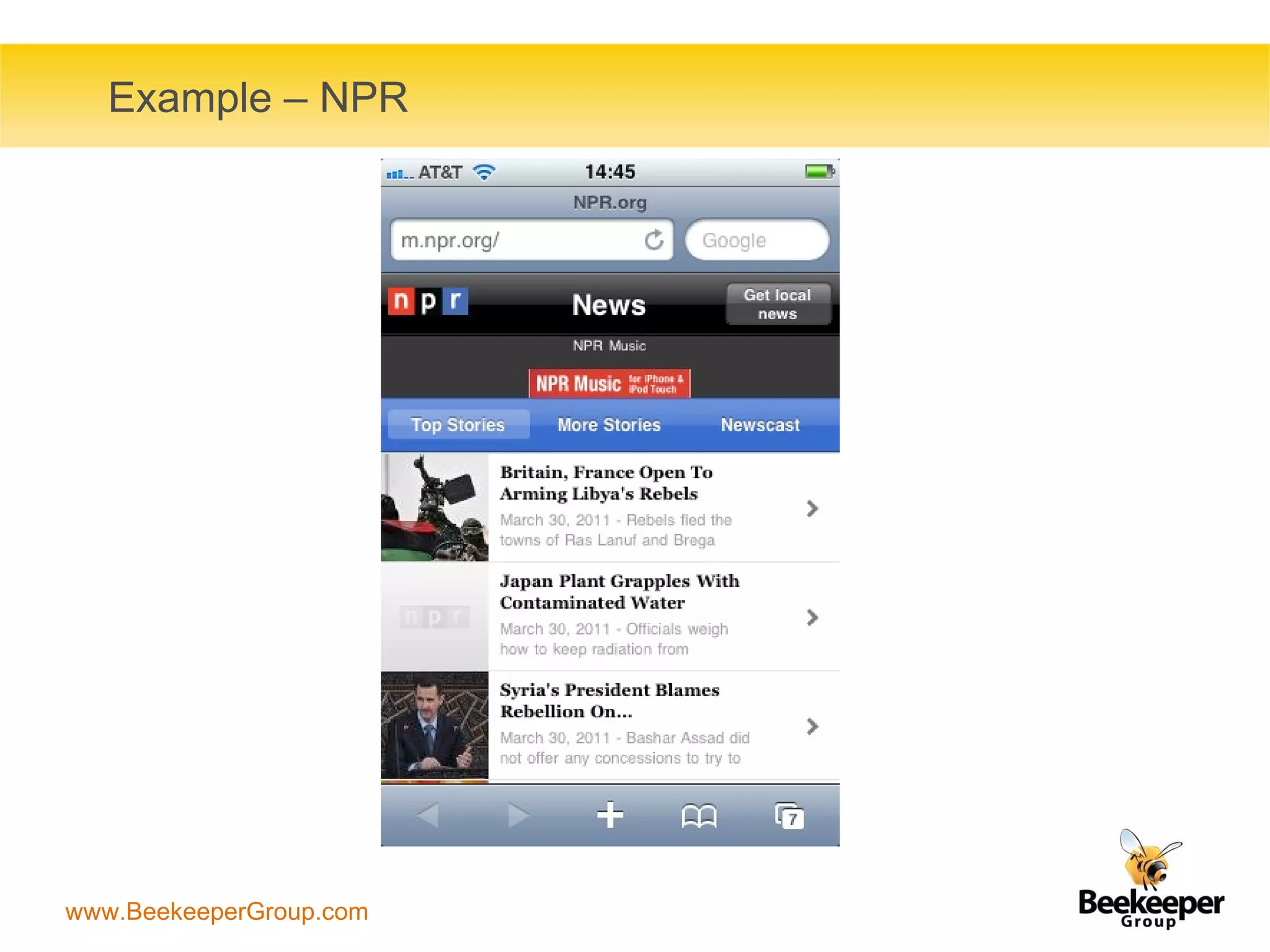
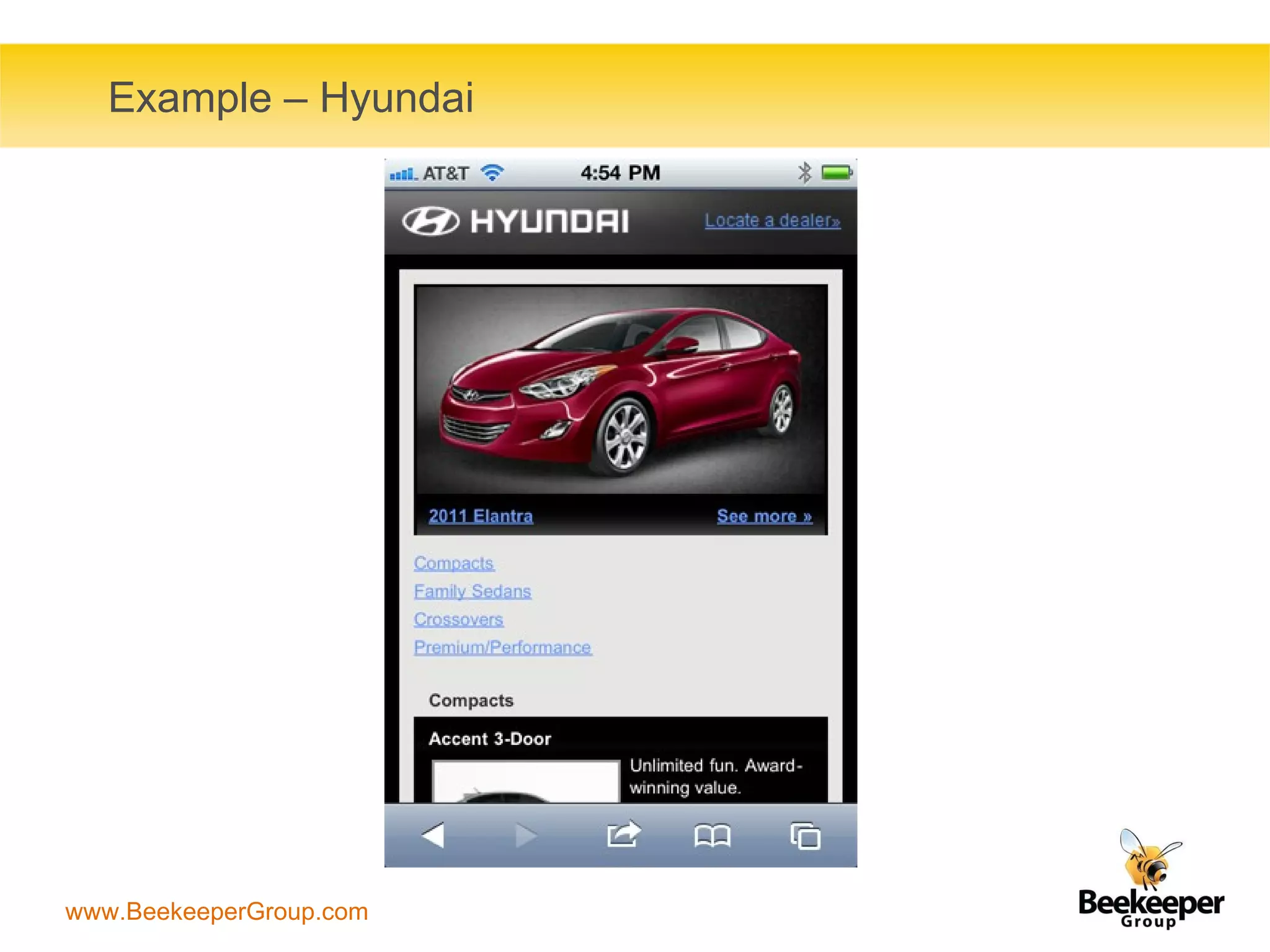
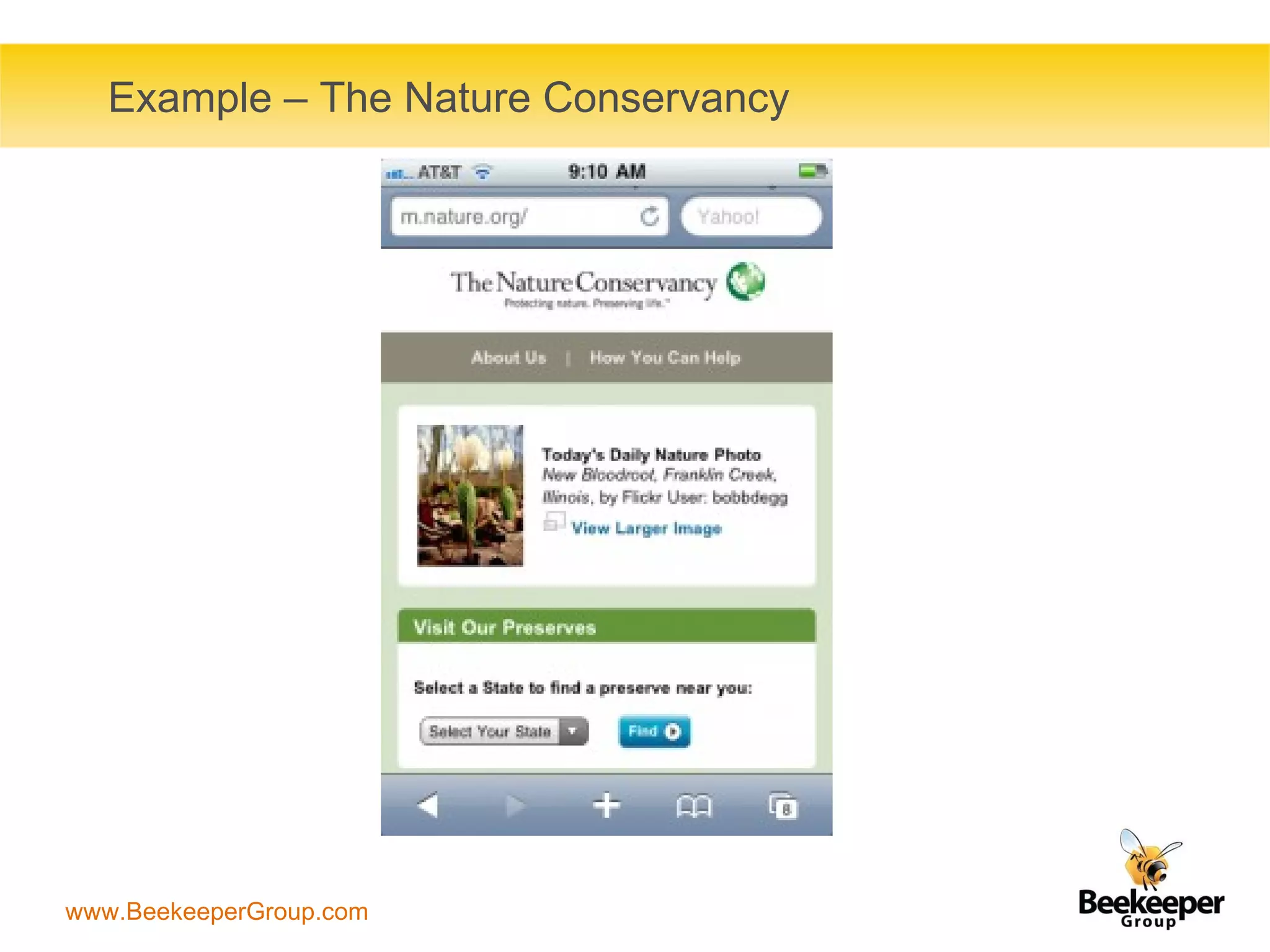
The document discusses the integration of social media with mobile sites and apps, emphasizing the importance of mobile internet access and the prevalence of smartphones. It outlines strategies for planning social media and mobile interactions, including the need for mobile-friendly designs and geo-social apps. It also provides examples from brands like Domino, NPR, and Hyundai to illustrate effective mobile-social media strategies.




![Thanks! Henri Makembe [email_address] @henrim](https://image.slidesharecdn.com/socialmediaandmobile-110504174413-phpapp01/75/Integration-of-Social-Media-and-Mobile-Websites-Apps-21-2048.jpg)