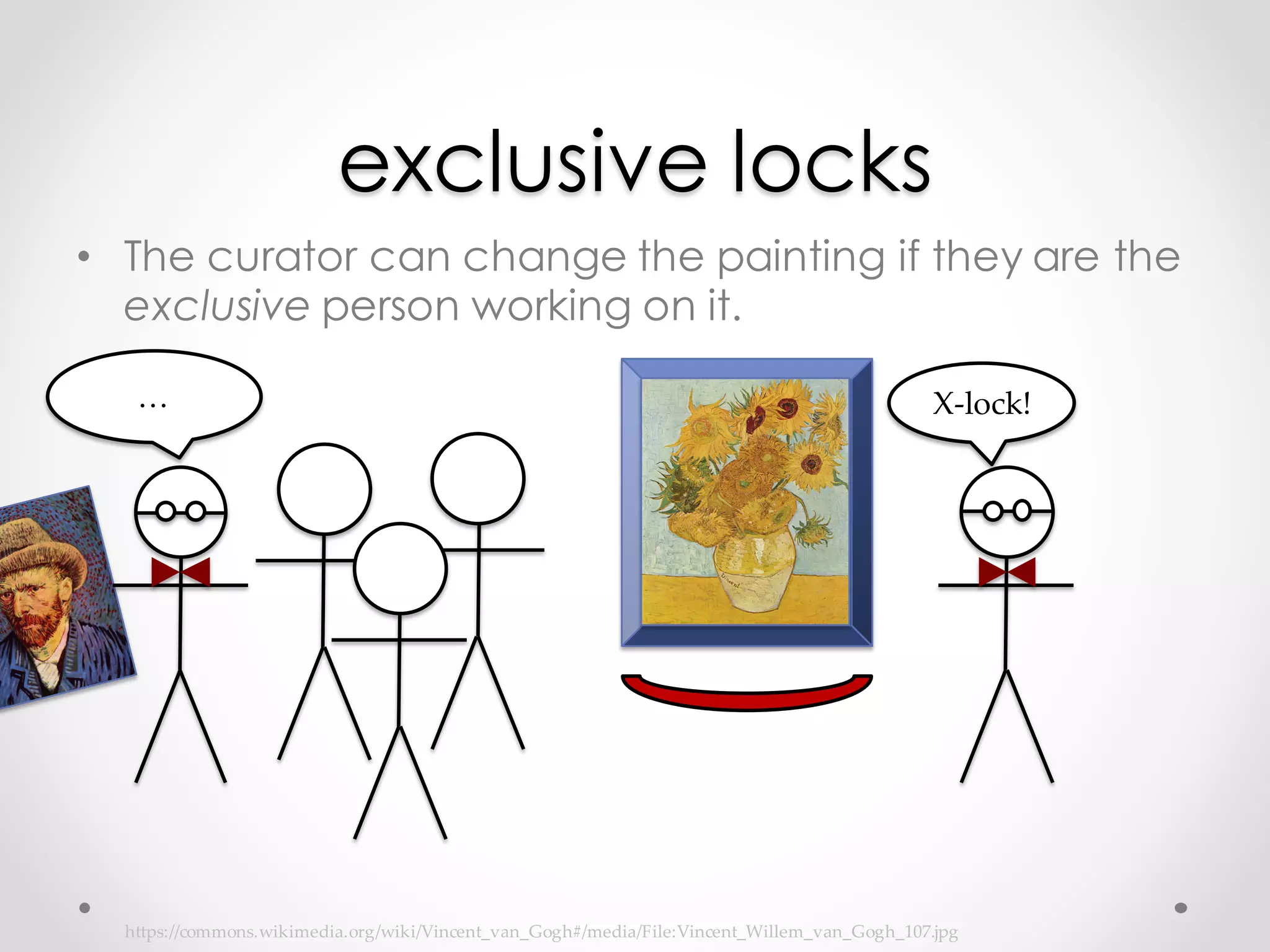
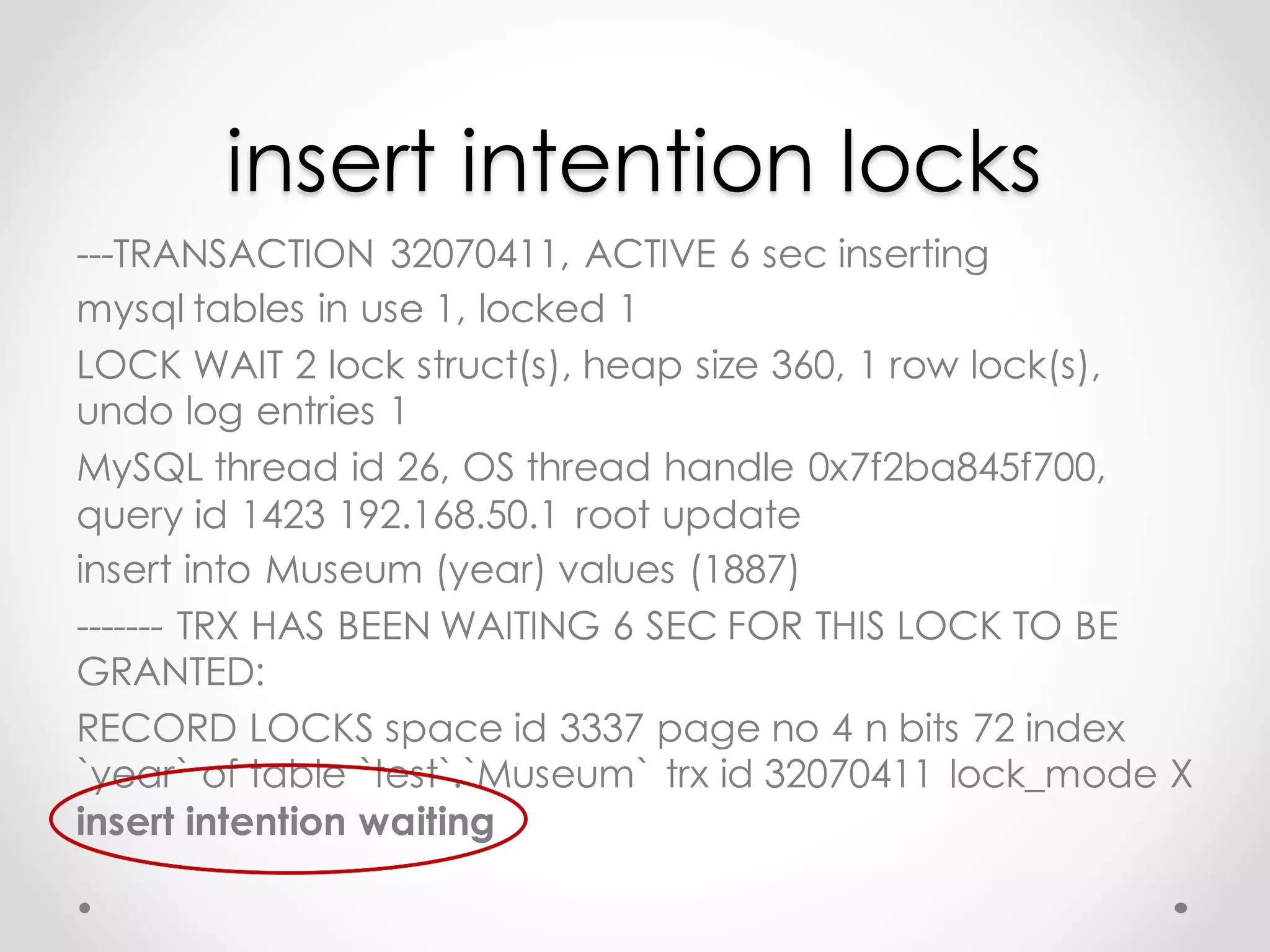
The document explains InnoDB locking mechanisms in a database context using museum analogies to illustrate concepts such as exclusive locks, shared locks, intention locks, and gap locks. It discusses how these locks prevent data conflicts during concurrent database transactions and describes potential issues like deadlocks. Additionally, it emphasizes the implications of using different transaction isolation levels on lock behavior and system performance.