This document provides information about the INF4015W course, including:
- The course covers system delivery methods, relevant technologies, strategic IT management, and project management.
- It is intended for students with work experience in IT and aims to impart current knowledge in key IT areas.
- The course content is delivered through lectures, assignments, presentations, and exams over several modules covering topics such as object-oriented systems, technologies, project management, and strategic IT management.


![9
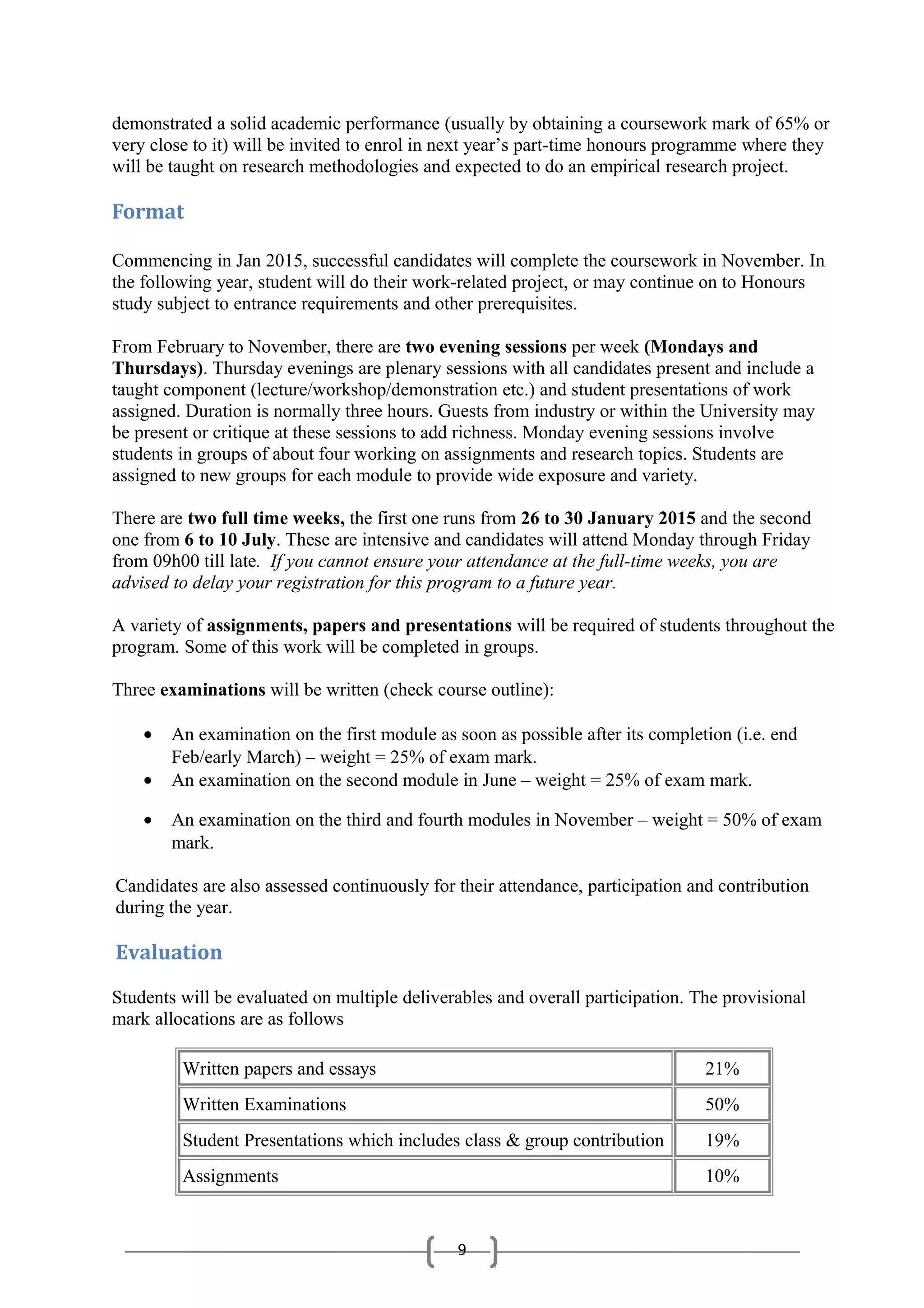
UCT Staff Involved with the Course
Role Name Room Tel: 021- email
Course Convenor Jean-Paul Van Belle 3.41 6504256 Jean-Paul.VanBelle@uct.ac.za
Other Lecturers Maureen Tanner
Ulrike Rivett
Michael Kyobe
Mike Hart
Sumarie Roodt
3.42
3.48
3.44
3.10
3.35
6504860
6504218
6502597
6502286
6502286
Maureen.Tanner@uct.ac.za
Ulrike.Rivett@uct.ac.za
Michael.Kyobe@uct.ac.za
Mike.Hart@uct.ac.za
Sumarie.Roodt@uct.ac.za
Course
Administrator
Nocky Bobo 3.01.3 6504670 Nocky.Bobo@uct.ac.za
Provisional Lecture Schedule
This is the current INF4015W lecture outline for 2015.
Relevant updates are made continuously.
Full-time week lectures are scheduled 9:00-18:00 but allow for evening group work
Thursday evening lectures scheduled 17:30-20:30 in IS Seminar Room LC3.12
1st Module System Delivery Module
(Maureen Tanner)
Full Time Week - System Delivery (Venue: IS Seminar Room Leslie Commerce
LC3.12)
9:00 till late evening; Monday, Tuesday & Wednesday may have evening group
work
26-Jan 9:00 Welcome & Course overview [JP] & Q&A
10:00 Registration
11:00 Changing the paradigms - Object Orientation and Iterative Development
27-Jan Modelling User Requirements
28-Jan Modelling Structure and Behavior
29-Jan Scrum Bootcamp
15:00-17:00 Library Tour (TBC)
30-Jan Scrum Bootcamp
Mon 2-Feb Academic skills: writing & presentation skills and assignments [JP]
05-Feb Object Oriented Concepts: Components, Patterns and Model Driven Architecture
Mon 9-Feb Group presentation exercise (Handin by 5-Mar)
12-Feb Agile Methodologies: XP, Kanban and Lean + Exam Prep
Prep for SD Examination in your own groups
Thu 26-
Feb
17:30-20:00 Examination: SD Module
(the paper is 2 hours + 20 minutes reading time)
2nd
Module
Technology Module
(Jean-Paul Van Belle)
Mondays: Student Group Sessions (not listed below)
Thursdays 17:30-21:30: Lecture Sessions (topic list below)
05-Mar S1 Building Blocks for Better Information Systems: The What Why Who and
How of Architectural Thinking in IS
(JP) Architectural frameworks e.g. Zachman and TOGAF.](https://image.slidesharecdn.com/9c1e5f62-ceaa-4e73-a19c-a45273096499-150413040853-conversion-gate01/75/INF4015-2015-Course-Outline-v1-5-2048.jpg)
![9
12-Mar S2 Hardware Architectures: Do you want Moore chips with that?
- Chip architectures: More from Moore’s Law. (History and evolution of CPU, CPU
architectures, vendors, RAM, future trends)
- Who’s there? Biometric input/output devices. (Types of biometrics, use cases &
models of deployment, issues)
- Mass storage architectures: SAN, RAID and clouds. (Storage technologies,
architecture and governance/management of SAN, RAID and cloud storage, use
cases)
- Emerging technologies: 3D printing, Wearable Technologies, Virtual Reality,
Quantum Computing, ...
19-Mar S3 Software Architectures: From OSS to OSs, the tale of Open Source Software
and Operating Systems
- Operating systems for desktop computing: Gates, Apples and Penguins.
(Architecture and distinguishing features of MS-Windows, OS X and Linux. Current
status and future trends)
- The battle for the mobile market: the ecosystems of mobile devices. (Smartphones,
e-readers and tablets: standards, business and societal impacts, use cases, trends)
- Punching in the heavy league: the role and nature of server operating systems.
(How are they different from desktop OS, architecture, components, bundled app
server options, Windows vs Unix)
- System Virtualization (what, architectures, products) & Storage Virtualization
- Open Source Software vs Proprietary Software (from a corporate perspective):
History, Philosophy, Issues, Current Status, Quo Vadis.
26-Mar S4 Computer Network Architectures: LANs, WANs and MANs.
- Wired LANs: topologies and technologies
- Wireless LAN technology: from Bluetooth to WiFi
- WAN concepts, technologies and architectural options
- WWANs Mobile Commerce: architectures, technical platforms, supporting tools,
mobile services and business models.
- Telkom: Welcome or Hellkom? Telecom services available from Telkom (and
Neotel, MTN, Vodacom, etc.)
- Unified Communications
- Network diagnostics, monitoring, optimization and management tools.
02-Apr S5 System and Integration Architectures: High-Availability, Cloud Computing,
SaaS, SOA, Middleware
- From mission-critical, High-availability systems (e.g mainframe operating systems,
Himalaya ServerNet, Compaq VMS, IBM Sysplex etc.) to architectures for High
Performance systems; Distributed Systems and Massively Parallel Clusters.
- Client-server and multi-tier application architectures
- Middleware: Types, RPC, Messaging, TPM, ORBs
- Web Service Architectures and Technologies: the .NET view vs the Java view
- Cloud Computing: concepts, types, architectures, benefits & issues, current status,
vendors, case study or demo
09-Apr S6 The Architecture of the Internet: Building the Web 3.0
- HTML and its short-comings. Overview of common server-side and client-side
technologies. (Brief introduction to Internet 2) [Ryan Carty & Igetia Themba]
- Web servers (software eg IIS, Apache) & Web CMS (eg Joomla, Drupal,
WordPress). Comparison of the leading three packages/systems (at least on OSS) in
each of the categories by feature, vendor, market share, mind share, performance,
requirements etc.
- Web 2.0 What, who, why, why not? Technologies & applications with businesss
opportunities/uses (including blogosphere, podcasting, wikis, RSS and social
computing networks such as Facebook, MySpace, YouTube)](https://image.slidesharecdn.com/9c1e5f62-ceaa-4e73-a19c-a45273096499-150413040853-conversion-gate01/75/INF4015-2015-Course-Outline-v1-6-2048.jpg)
![9
16-Apr S6 The Architecture of the Internet: Building the Web 3.0
- HTML and its short-comings. Overview of common server-side and client-side
technologies. (Brief introduction to Internet 2)
- Web servers (software eg IIS, Apache) & Web CMS (eg Joomla, Drupal,
WordPress). Comparison of the leading three packages/systems (at least on OSS) in
each of the categories by feature, vendor, market share, mind share, performance,
requirements etc.
- Web 2.0 What, who, why, why not? Technologies & applications with businesss
opportunities/uses (including blogosphere, podcasting, wikis, RSS and social
computing networks such as Facebook, MySpace, YouTube)
23-Apr S7 Information System and Application Architectures
- SaaS: types, concepts, benefits & issues, current market status, vendors. [B-Abee
Toperesu]
- Typical enterprise-wide systems: ERP, CRM, DMS [Richard Russman & Tiaan de
Jager].
- Content Management Systems and Web CMS: What, why, typical architectures,
market overview (including OSS)
30-Apr S8 Information Architectures: from databases to business intelligence and
knowledge management.
- Relational Database Architectures, products and SQL
- BI: OLAP, data cubes, data mining: overview, tools and vendors
- The What and How of Knowledge Management
- Other (non-relational) Database Models: NoSQL, Object Orientation, XML,
Semantic Databases
- Big data
- Data Vizualization
07-May no lecture
14-May S9 Security Architectures: Security, Malware & Identity Management
- Malware technologies and architectures: viruses, trojan horses, common web-
hacking techniques
- Security, encryption & cryptography: principles and Internet applications:
- Identity Management. Give an overview of some important needs not addressed by
the network operating system and how these are being met by a selection of add-on
commercial products.Includes tools for enterprise security management (tools),
identity management, risk identification, authentication
- Enterprise Security Management
21-May S10 Capita Selecta & Make-up Session & Exam Prep
choose your own technology topic in consultation with JP - sample topics include:
- Semantic technologies
- Artificial Intelligence paradigms, techniques and real world business applications
- Complex Event processing technologies.
- Green IT
04-Jun 17:30 - 20:00 Examination: Technology Module
(the paper is 2 hours + 20 minutes reading time)
Venue: TBA
5June-
5July
mid-year break
3rd Module Project Management Module
(Prof Ulrike Rivett)
Full Time Week - Project Management [9:00-late] [venue TBC]
06-Jul Day 1 - Evolution of PM practice and PMBOK, complexity in PM
07-Jul Day 2 - PMBOK overview, language and communication
08-Jul Day 3 - PMBOK overview (ctd), systems thinking, rethinking PM](https://image.slidesharecdn.com/9c1e5f62-ceaa-4e73-a19c-a45273096499-150413040853-conversion-gate01/75/INF4015-2015-Course-Outline-v1-7-2048.jpg)



