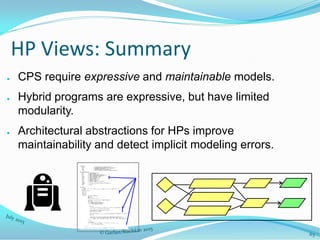
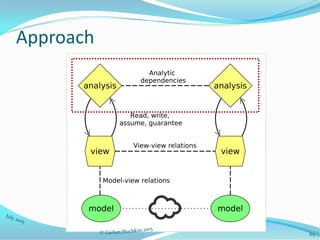
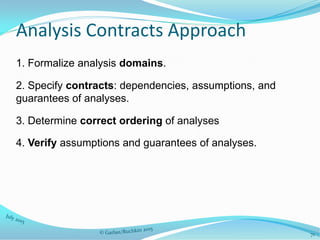
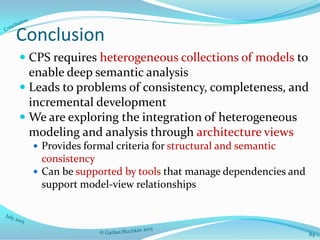
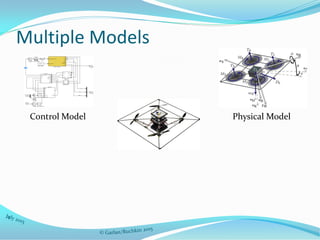
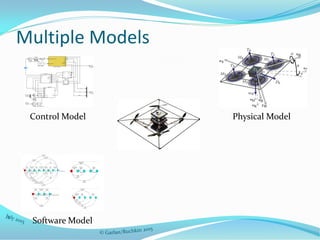
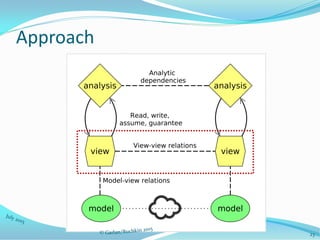
The document discusses the complexities of designing cyber-physical systems (CPS) due to challenges such as maintaining model consistency and integrating various modeling approaches. It proposes a unified architectural framework that leverages architectural views to support heterogeneous modeling, enabling effective trade-off analysis and ensuring the completeness of designs. The approach emphasizes the importance of tools for dependency analysis and the incremental evolution of models to address these issues.



























![48
Background: Hybrid Programs (HPs) [1]
● A; B – execute A, then B
● A* - execute A zero or
more times
● ?P – test P; continue if
A holds, abort otherwise
● { x1' := F1 … xn' := Fn & P } – evolve along differential equations within
region P
● A U B – execute either A or B
● x := S – assign S to
variable x
● x := * - assign an arbitrary
value to variable x
[1] A. Platzer. Logical Analysis of Hybrid Systems: Proving Theorems for Complex Dynamics. 2010.
Robot ::== (
a := *;
? b <= a <= A;
{ v' = a, x' = v, v >= 0 }
)*
x
v
a](https://image.slidesharecdn.com/cmujpltalk2015-150731151950-lva1-app6891/85/Identifying-and-Resolving-Consistency-Issues-between-Model-Representations-37-320.jpg)









![59
Architectural DDL Formula
Architectural DDL Formula (ADDL) – a DDL formula over HP views.
Example: “the robot behaves in a way that gives the obstacle an
opportunity to stop.”
Init → [HP View 1] (RobotFar ∧ (ObstFar → <HP View 2> Safe))
HP View 1:
- robot is moving
- obstacle (abstract) is moving
HP View 2 :
- robot is stopped
- obstacle (concrete) is
given a chance to stop](https://image.slidesharecdn.com/cmujpltalk2015-150731151950-lva1-app6891/85/Identifying-and-Resolving-Consistency-Issues-between-Model-Representations-48-320.jpg)

![61
Evaluation
● Method: “architecturalized” 15 model variants in an existing
case study [2]; observed extent of reuse and errors found by
analysis.
● Reuse results:
– Sensing connectors: average 2 connectors per variant.
– Actor physics types are widely used, up to 5-7 times in 15
models
[2] S. Mitsch, K. Ghorbal, and A. Platzer. On provably safe obstacle avoidance for autonomous
robotic ground vehicles. 2013.](https://image.slidesharecdn.com/cmujpltalk2015-150731151950-lva1-app6891/85/Identifying-and-Resolving-Consistency-Issues-between-Model-Representations-50-320.jpg)