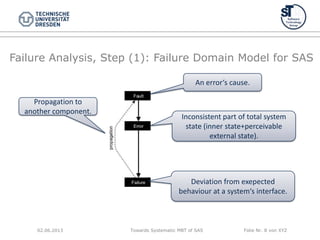
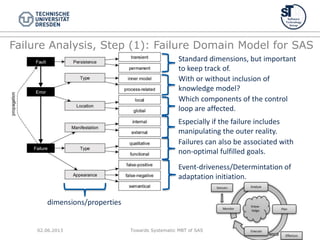
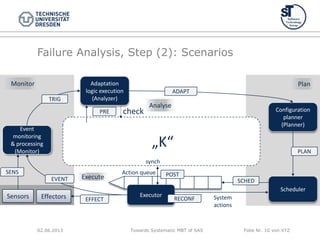
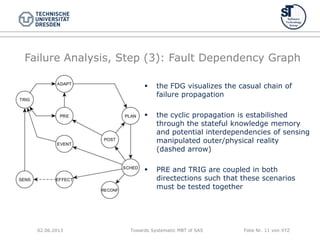
This document discusses model-based testing of self-adaptive software systems. It begins by motivating the need for new testing methods for these complex systems. It then performs a failure analysis to develop a failure domain model and fault dependency graph. From this, it derives 6+1 requirements that testing of self-adaptive systems should assure. Finally, it discusses future work in instantiating the requirements for specific projects and developing appropriate testing models and coverage criteria.
![Towards Systematic MBT of SAS Folie Nr. 4 von XYZ
Motivation II: Why should we generally….?
SAS conform to a feedback loop principle (e.g., MAPE-K [KC03])
Challenge:
“Creating validation and verification techniques to
test and evaluate control loops’ behaviour and
automatically detect unintended interactions.” [Cheng+08]
Are SAS special to testing?
As in design much more complex information has to be
specified.
As SAS run control loops, testing methods can be
specifically tailored to it.
Because of both, models should be to generate test cases.
(MBT – Model-based Testing)
02.06.2013](https://image.slidesharecdn.com/adaptive13test-130602151559-phpapp01/85/Adaptive13-test-4-320.jpg)
![Towards Systematic MBT of SAS Folie Nr. 5 von XYZ
Related Work: What was done before?
Gap (1): Besides challenge statements, analysis is rare.
Gap (2): Only a minority considers the interaction between running system
processes and adaptation. (Transactions? Order of actions?)
Gap (3): Generalization?
Gap (4): Many approaches base on @runtime self-testing.
But: For industry-ready and safe systems (e.g., with certification) we
require black box testing in advance (but before deployment)!
Some related approaches/methods:
DiVA offers a comprehensive strategy, split in two phases [DiVA]:
Early validation@design time: adaptation logic and context model are
executed in a simulation
Operational validation: deals with context changes, uses Multi-
dimensional Coverage Arrays (MDCA)
Testing strategy for context-adaptive systems: „Artificial Shake Table Testing“
coverage strategy to produce context test data [MB09]
Further strategies generate test cases from context and control flows
[TSE+04][Wang+07]
Cheng„s explicit test model of the total state space of an SAS. [Cheng+08]
02.06.2013](https://image.slidesharecdn.com/adaptive13test-130602151559-phpapp01/85/Adaptive13-test-5-320.jpg)
![Towards Systematic MBT of SAS Folie Nr. 7 von XYZ
Failure Analysis prerequisites:
Requirements and Assumptions
Following steps are performed in Failure Mode
and Effects Analysis (FMEA) [FMEA]:
1. Build Failure Domain Model (dimensions&properties)
2. Investigate scenarios
(3.) visualize fault propagation in a Fault Dependency
Tree/Graph
But: We require a common architectural
perspective of SAS!
Assumption: We do only consider SAS fulfilling the
MAPE-K principle.
02.06.2013](https://image.slidesharecdn.com/adaptive13test-130602151559-phpapp01/85/Adaptive13-test-7-320.jpg)
![Towards Systematic MBT of SAS Folie Nr. 16 von XYZ
References
[KC03] J. O. Kephart and D. M. Chess, “The vision of autonomic computing,” Computer, vol. 36, no. 1, Jan.
2003, pp. 41–50.
[Cheng+08] B. H. C. Cheng, D. Lemos, H. Giese, P. Inverardi, and J. M. et al., “Software engineering for self-
adaptive systems: A research roadmap,” in Dagstuhl Seminar 08031 on Software Engineering for Self-
Adaptive Systems, 2008.
[FMEA] H. E. Roland and B. Moriarty, System Safety Egnineering and Managemnent, 2nd edn. John Wiley &
Sons, Chichester, 1990, ch. Failure Mode and Effect Analysis.
[STA07] H. Sozer, B. Tekinerdogan, and M. Aksit, Archtitecting dependable systems IV. Springer, 2007, ch.
Extending failure models and effects analysis approach for reliability analysis at the software architecture
design level.
[TSA08] B. Tekinerdogan, H. Sozer, and M. Aksit, “Software architecture reliability analysis using failure
scenarios,” Journal of Systems and Software, vol. 81 (4), 2008, pp. 558–575.
[MB09] F. Munoz and B. Baudry, “Artificial table testing dynamically adaptive systems,” 2009.
[DiVA] A. Maaß, D. Beucho, and A. Solberg, “Adaptation model and validation framework final version (DiVA
deliverable D4.3),” 2010.
[Tse+04] T. Tse, S. Yau, W. Chan, H. Lu, and T. Chen, “Testing context-sensitive middleware-based software
applications,” 28th Annual International Computer Software and Applications Conference, 2004, pp. 458–466.
[Wang+07] Z. Wang, S. Elbaum, and D. S. Rosenblum, “Automated generation of context-aware tests,” 29th
International Conference on Software Engineering (ICSE), 2007, pp. 406–415.
02.06.2013](https://image.slidesharecdn.com/adaptive13test-130602151559-phpapp01/85/Adaptive13-test-16-320.jpg)