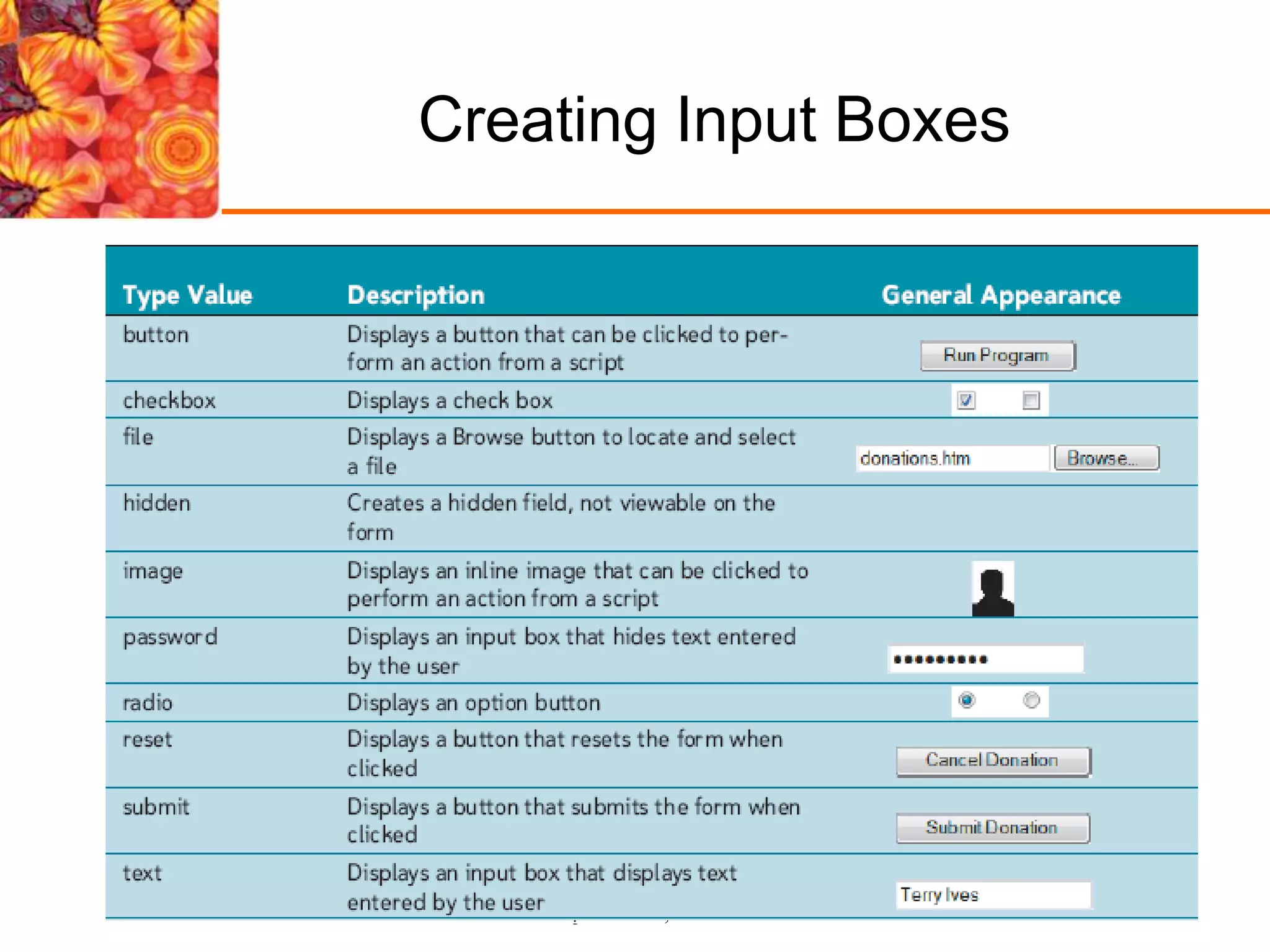
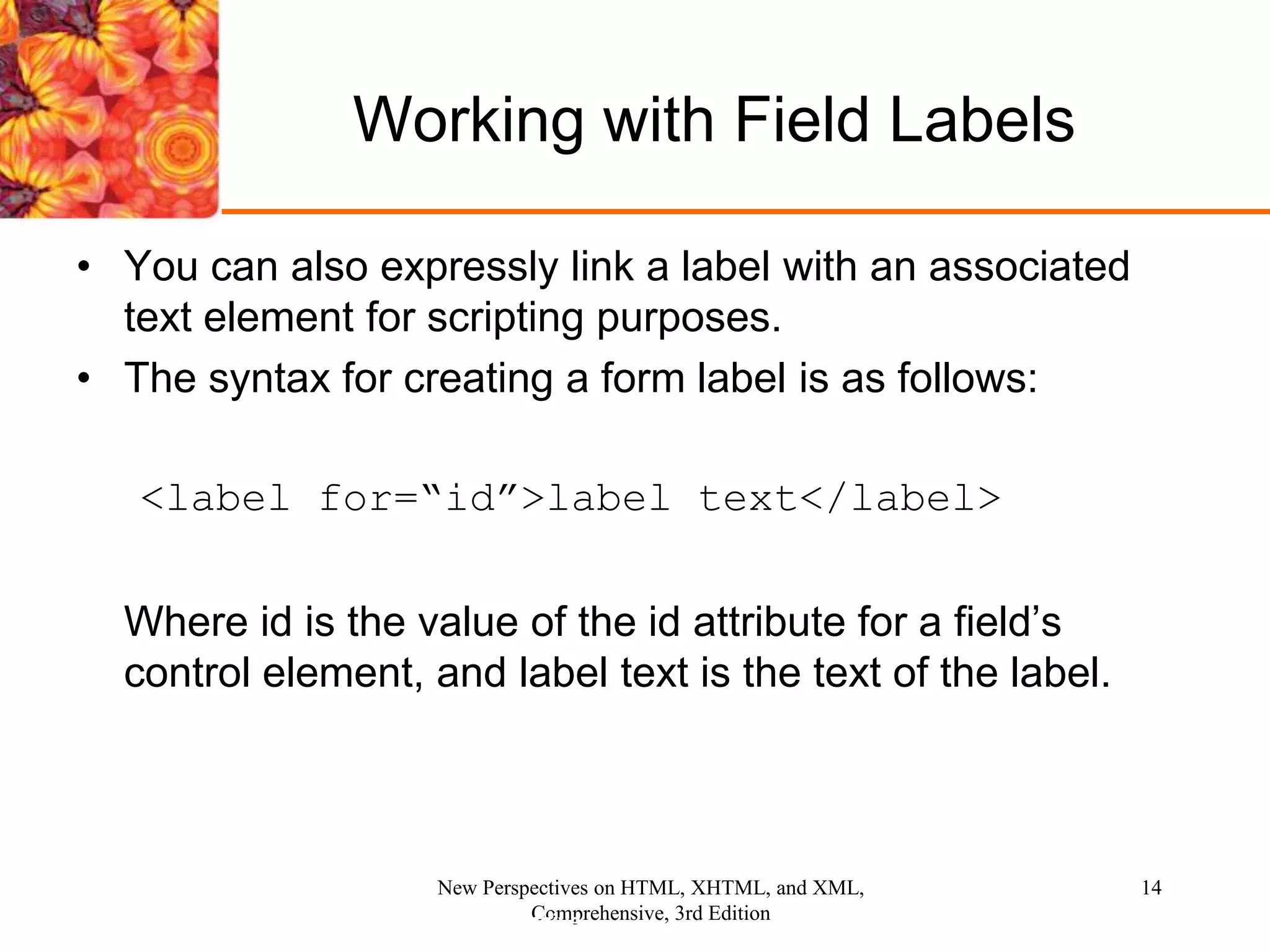
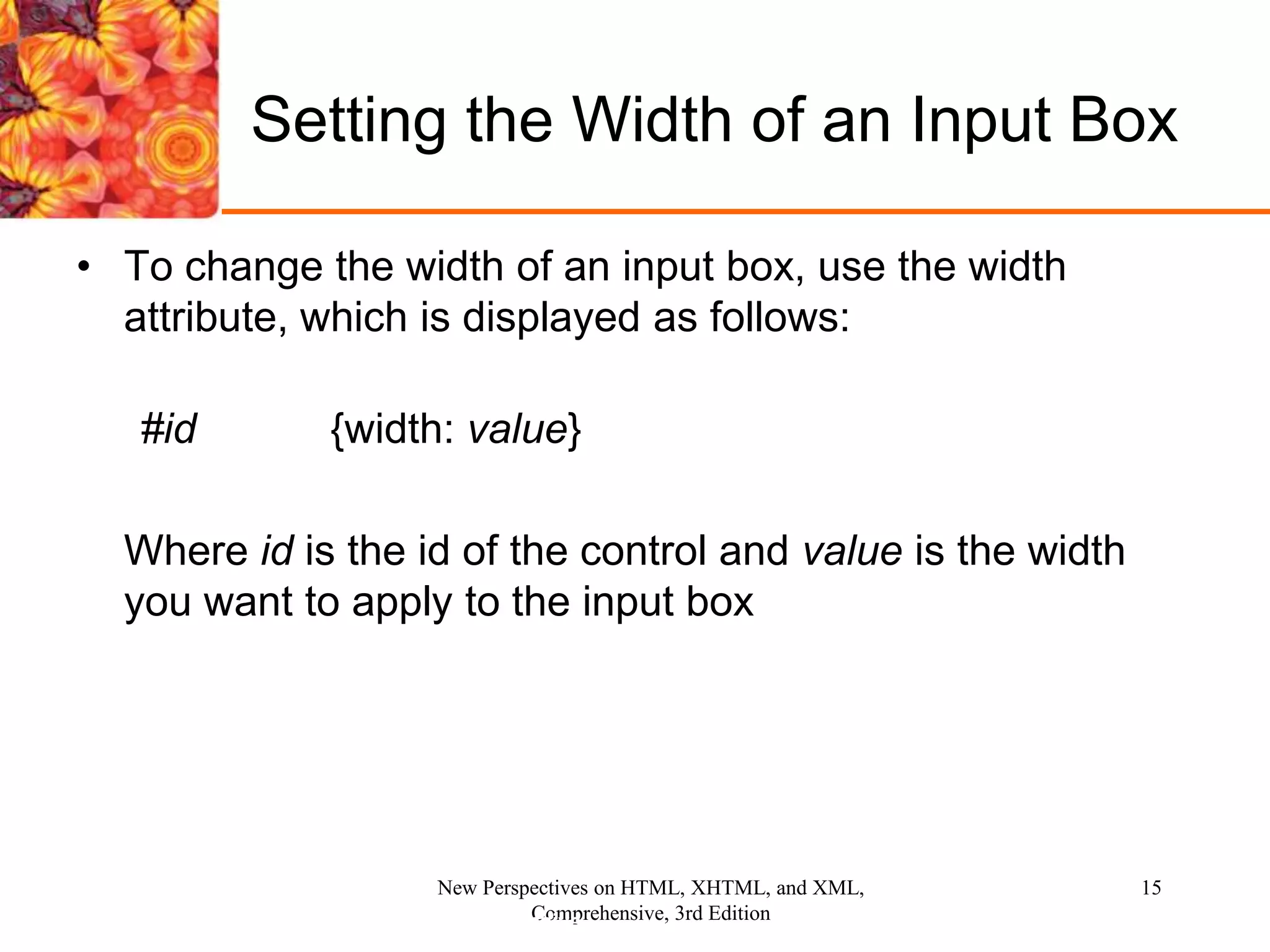
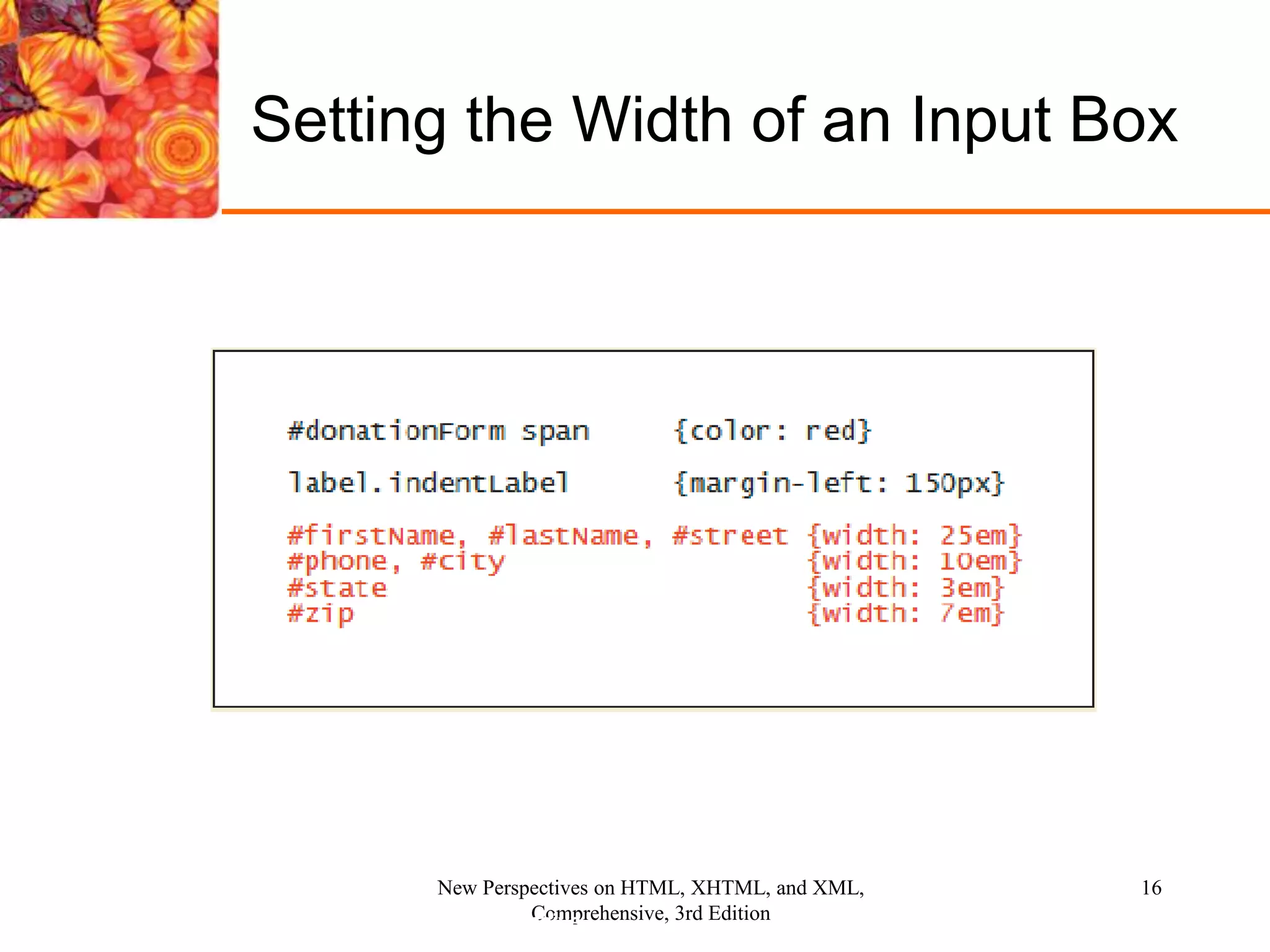
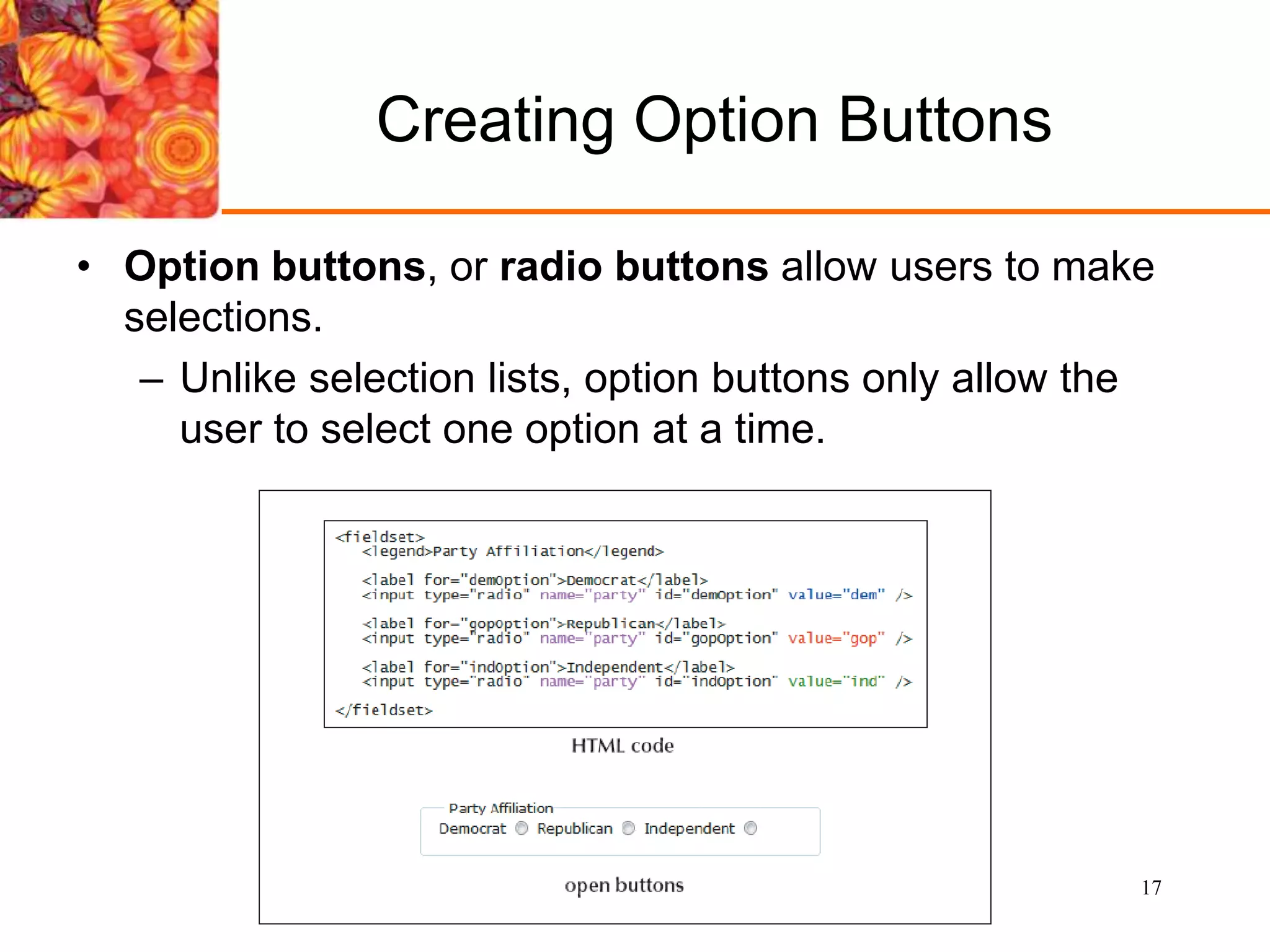
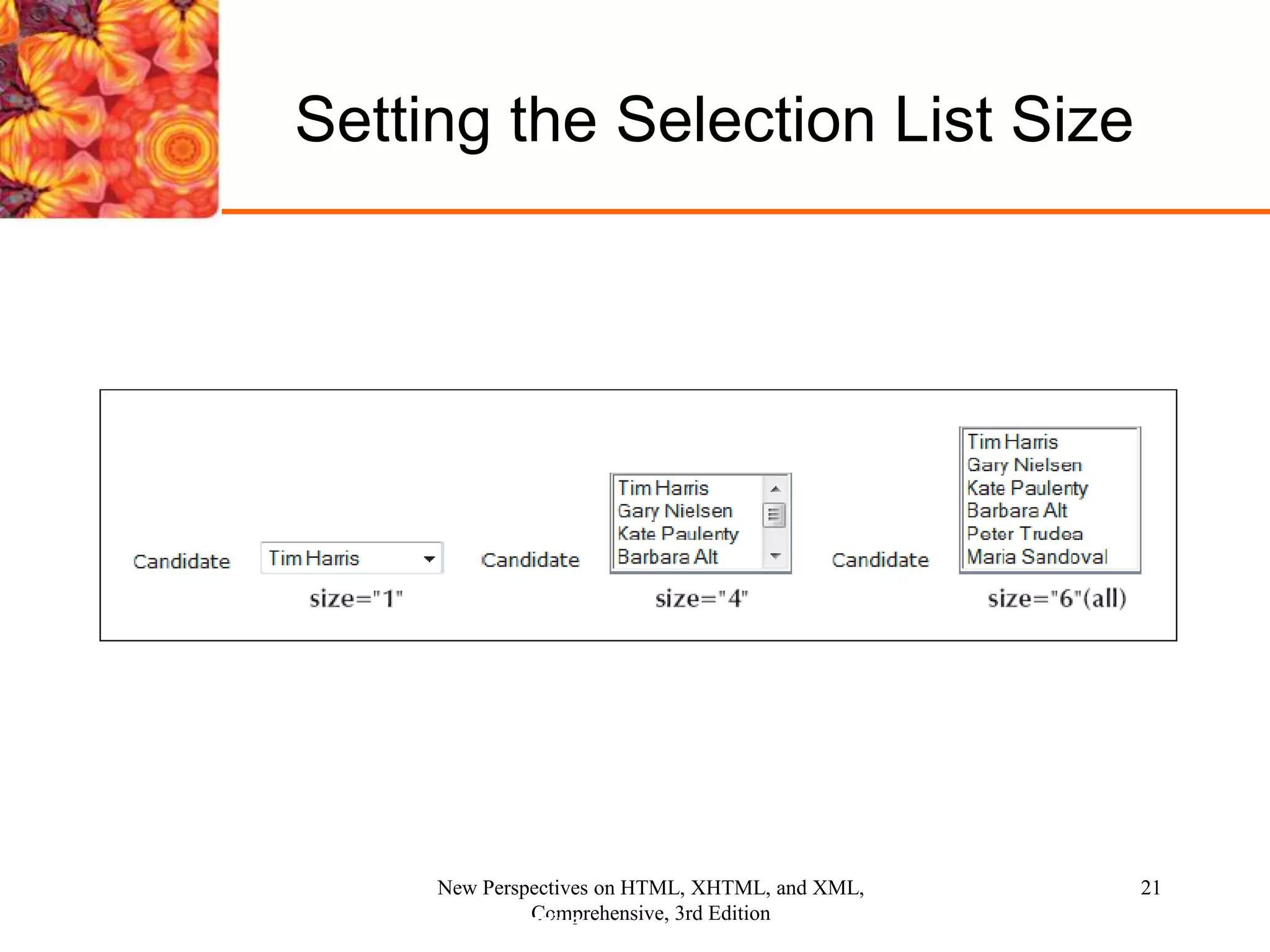
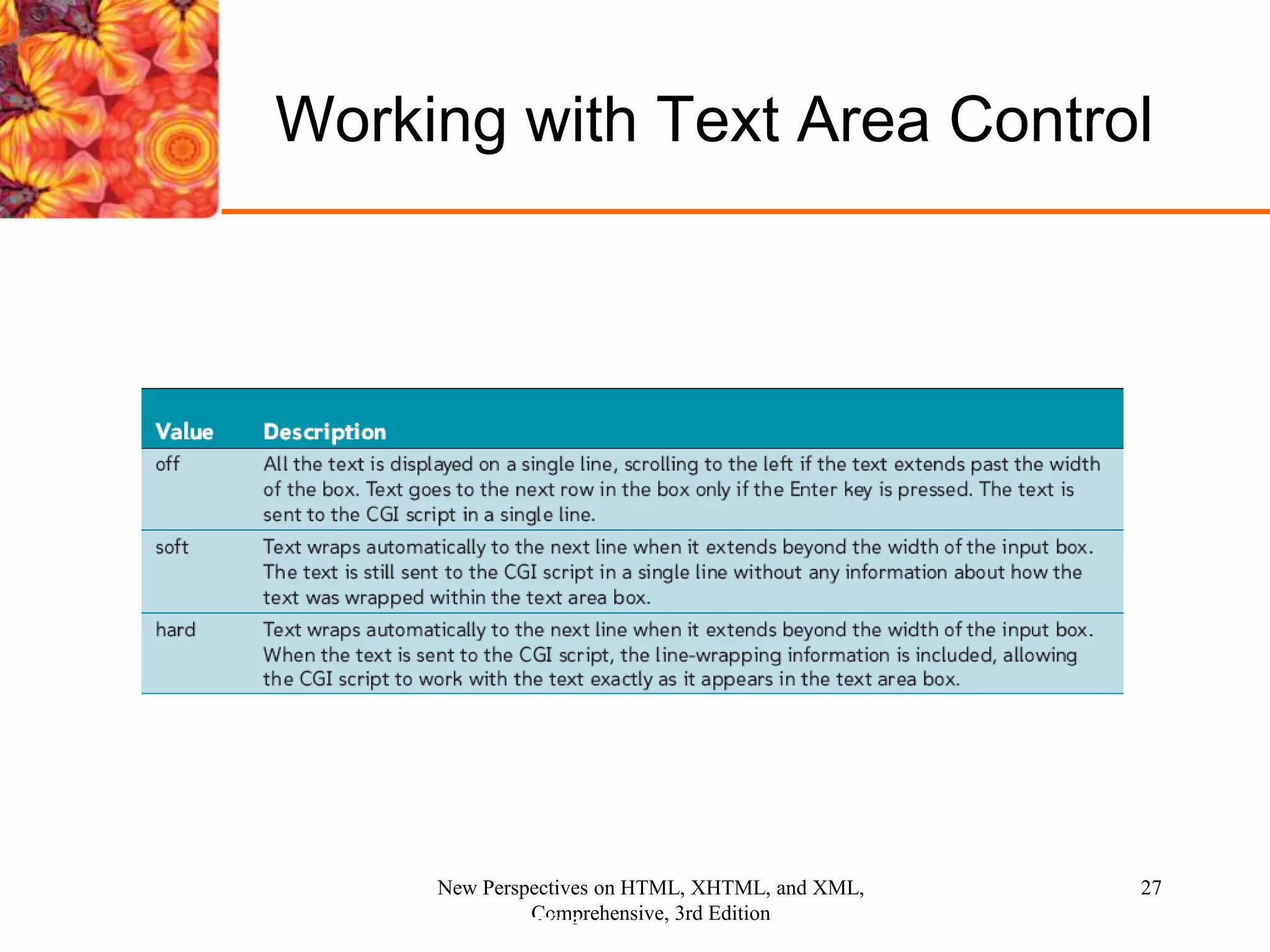
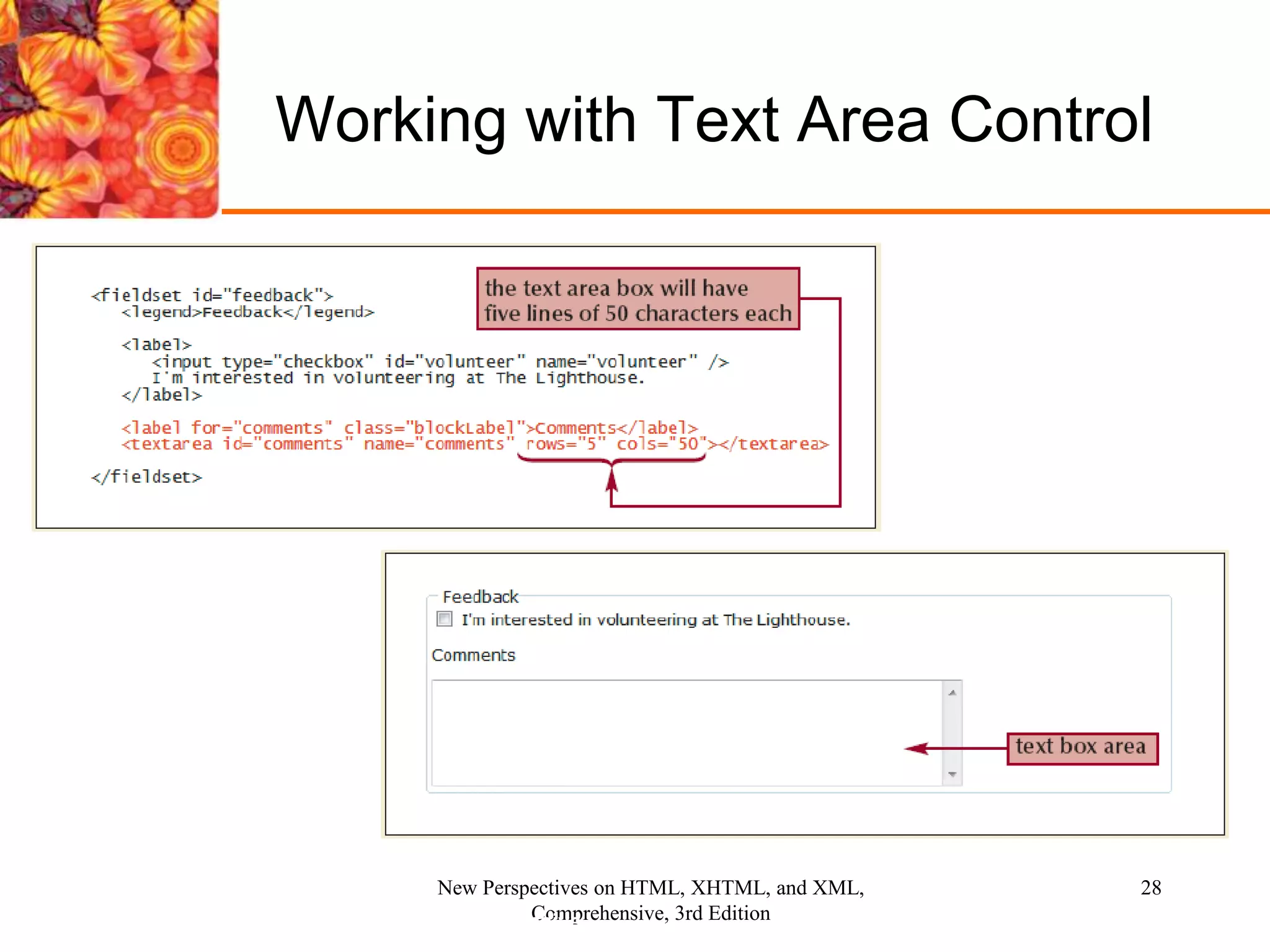
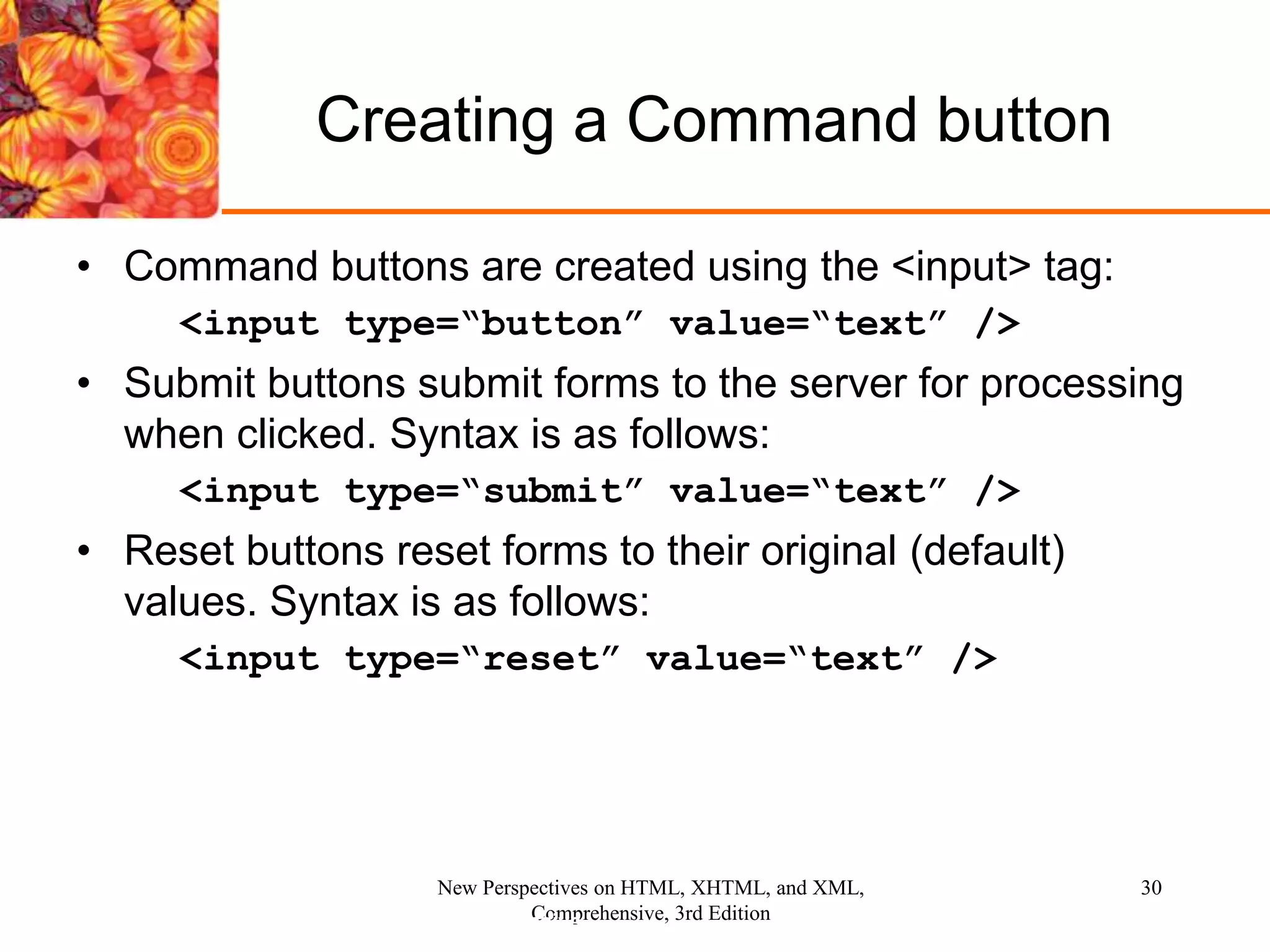
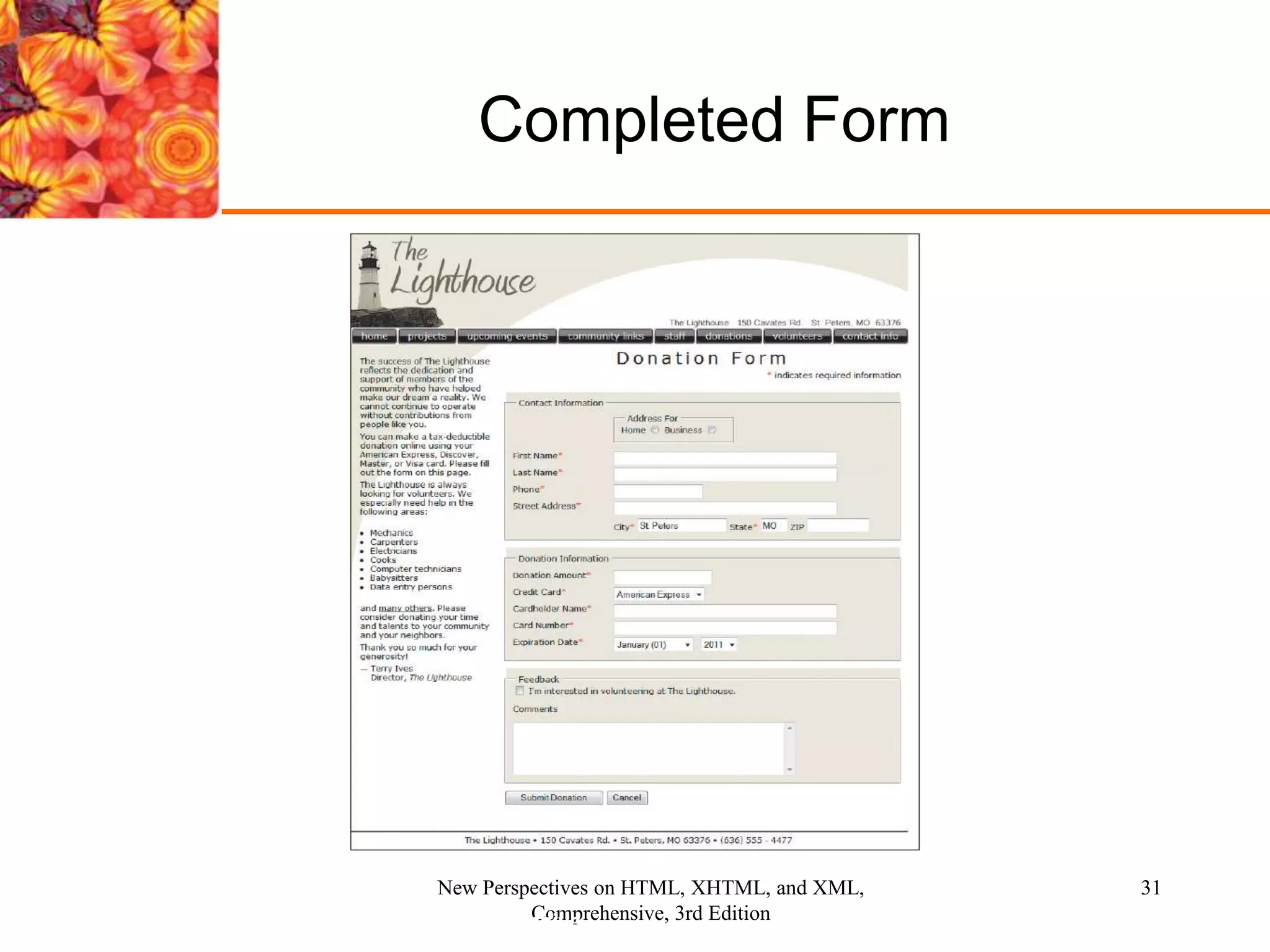
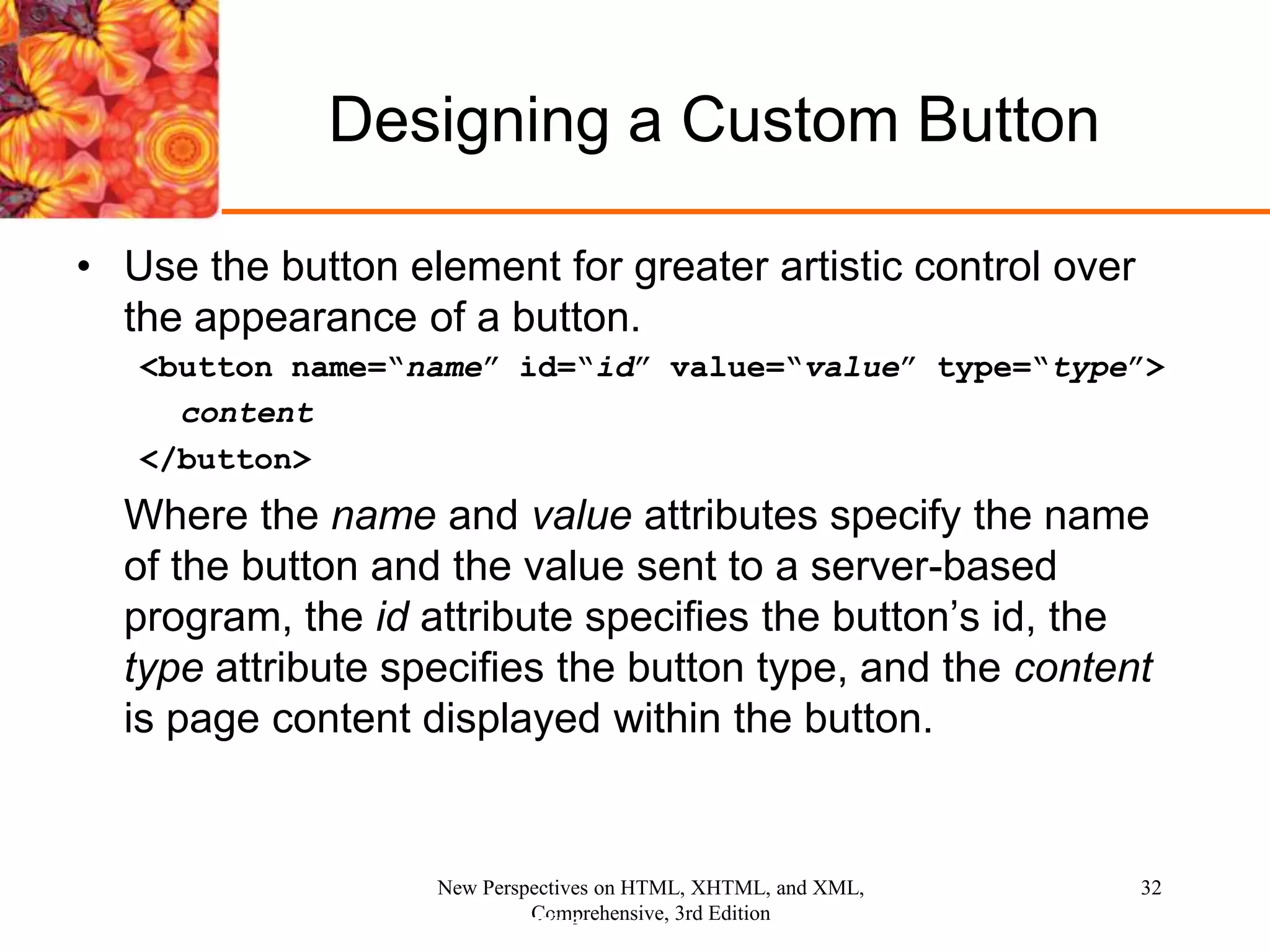
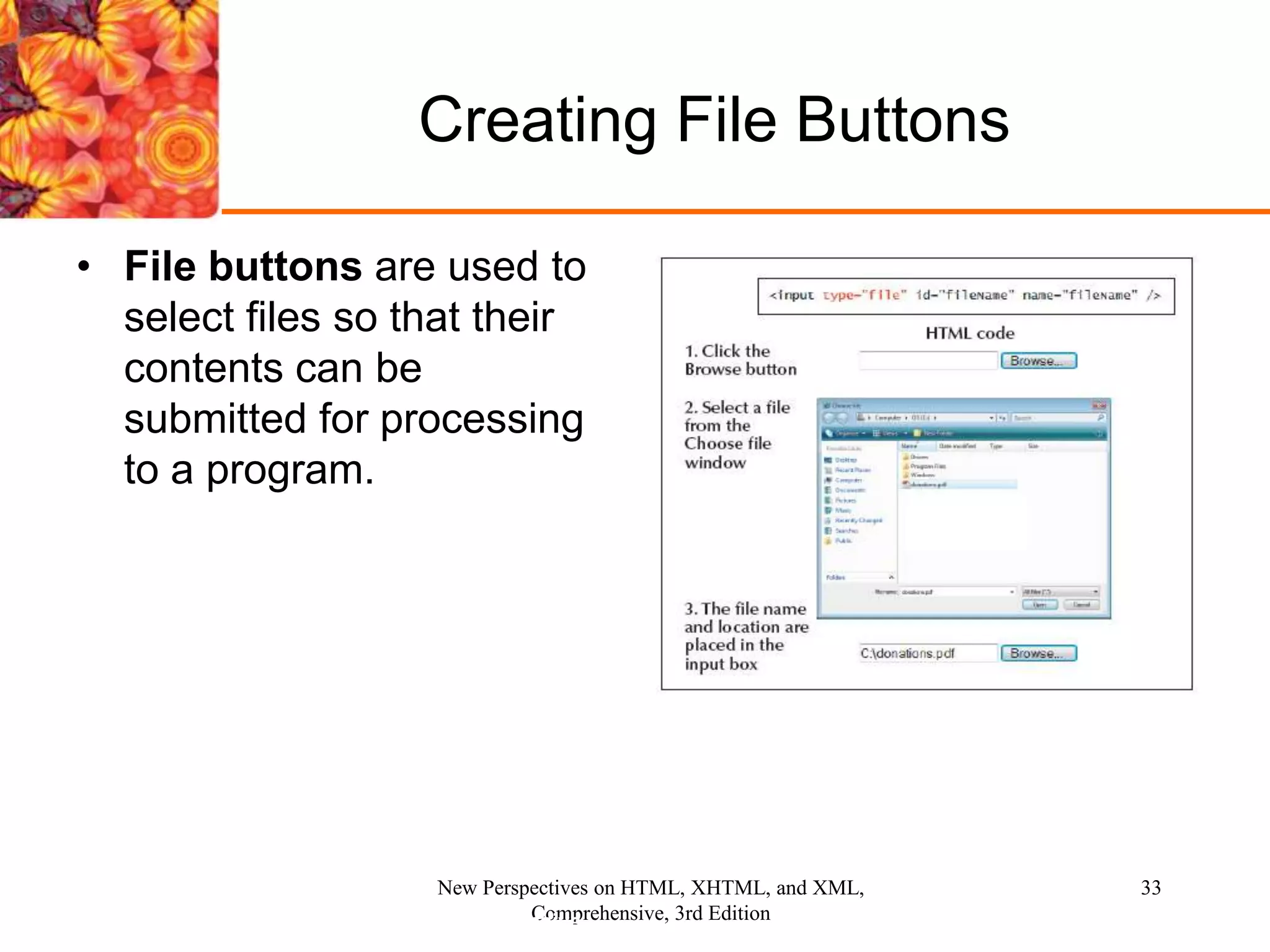
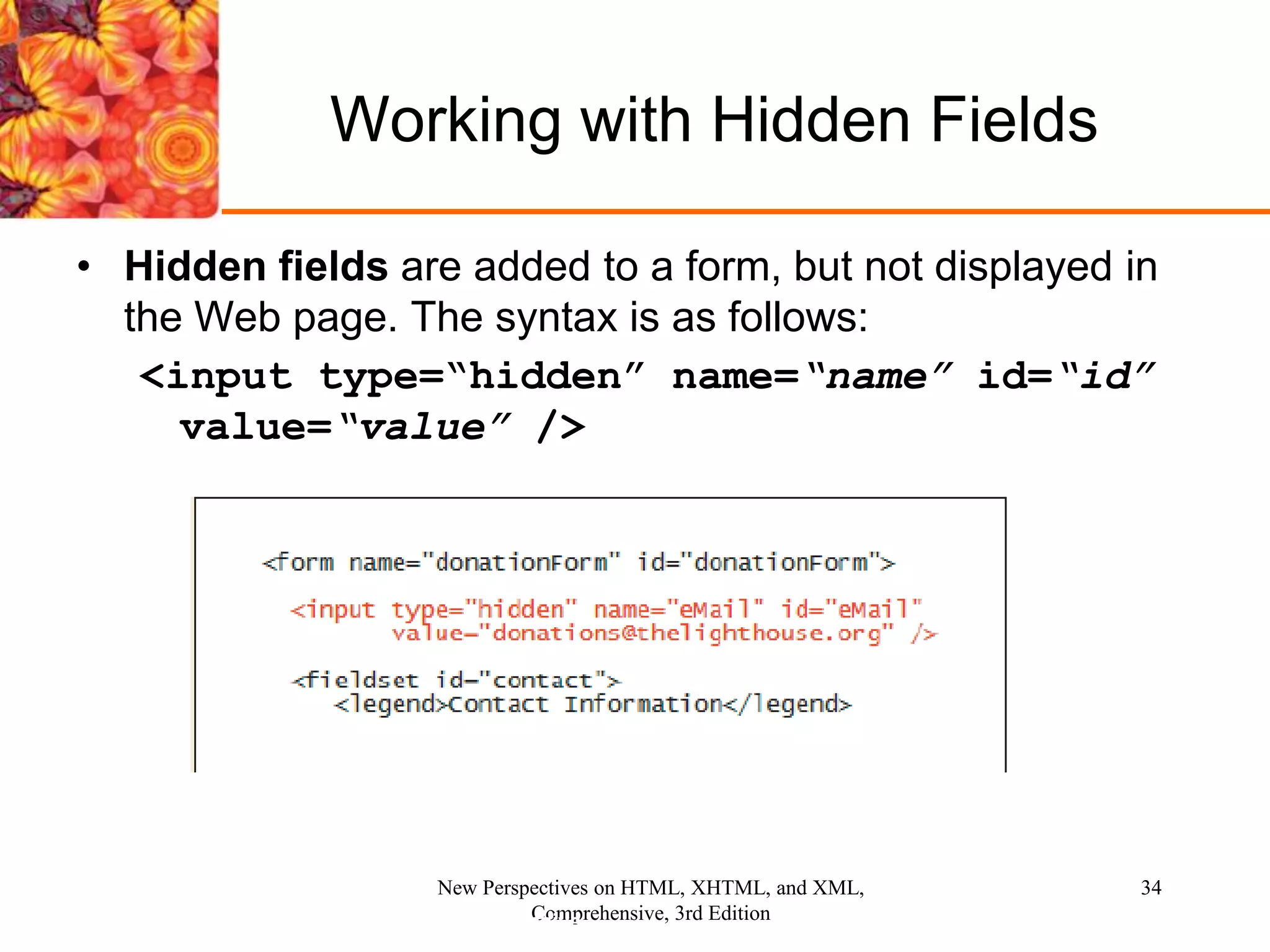
The document discusses creating and working with web forms in HTML, including adding different form elements like input boxes, radio buttons, drop-down lists, checkboxes, and text areas. It also covers setting attributes of forms and form elements, organizing fields using fieldsets, linking labels to fields, and submitting forms using buttons. The last few sections discuss hidden fields, specifying actions and methods for forms, and designing custom buttons.