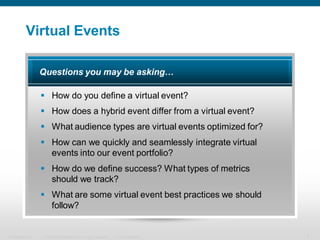
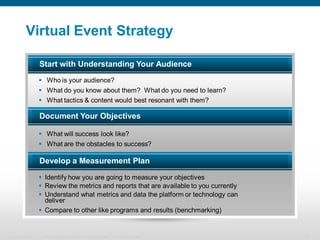
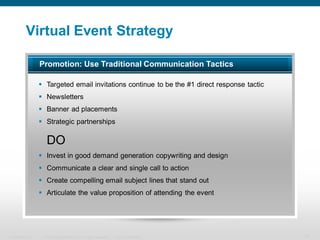
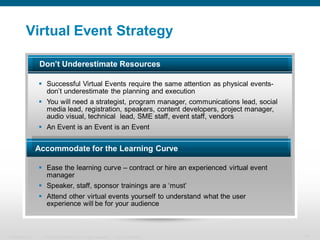
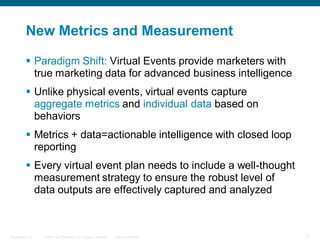
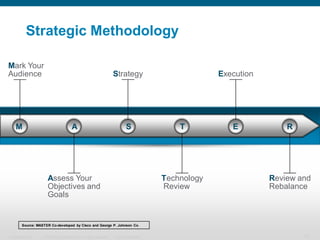
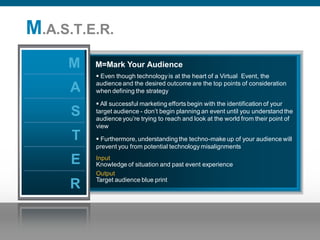
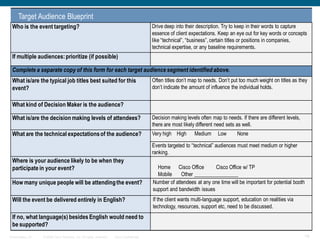
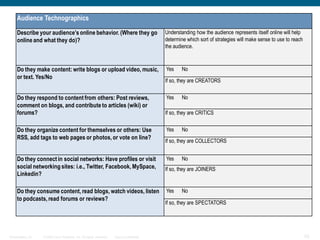
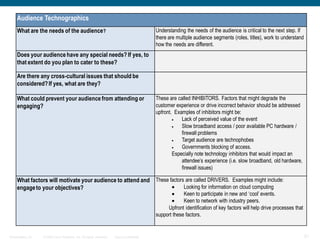
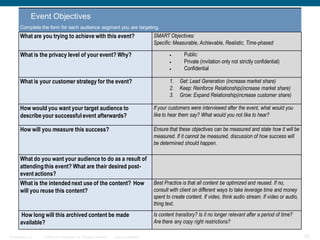
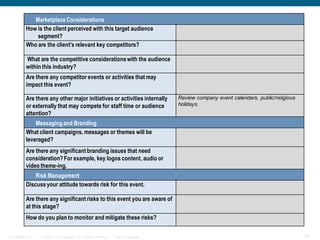
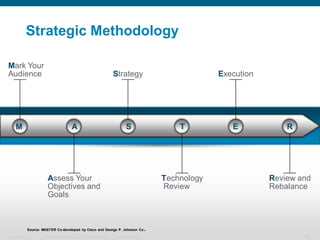
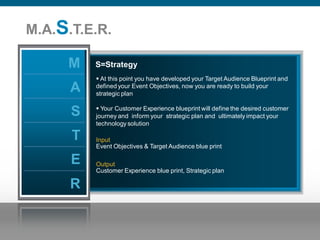
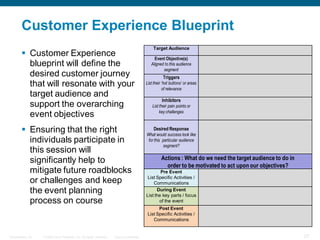
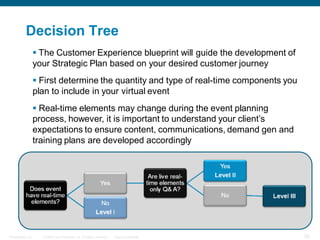
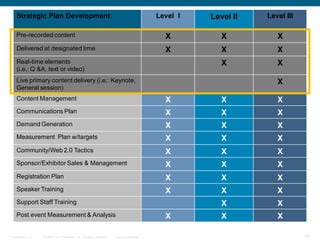
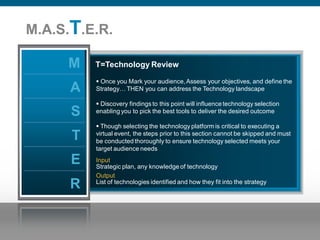
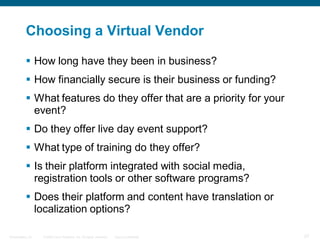
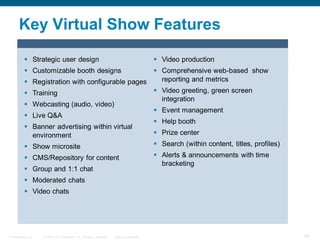
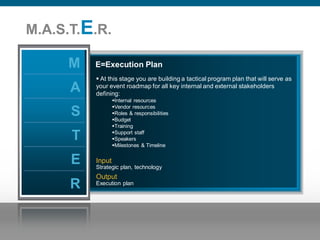
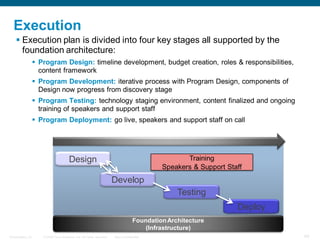
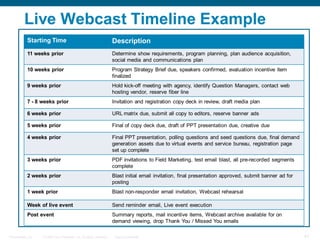
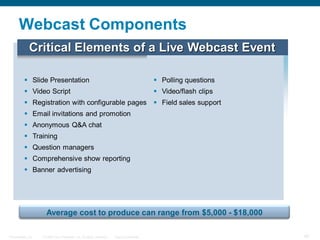
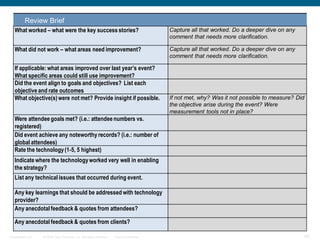
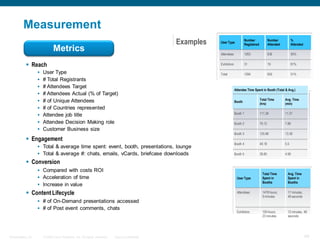
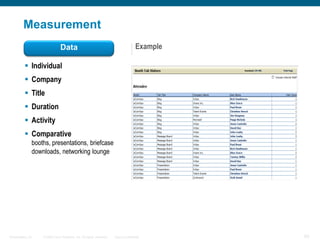
The document discusses strategies for planning and executing a successful virtual event. It covers defining a virtual event, developing a strategy, creating a methodology blueprint, and measuring success. The strategy involves understanding the audience, setting objectives, developing a measurement plan, using various promotion tactics, allocating proper resources, and embracing new metrics. The methodology blueprint involves marking the audience, assessing objectives and goals, developing a strategy, reviewing technology, and rebalancing as needed.