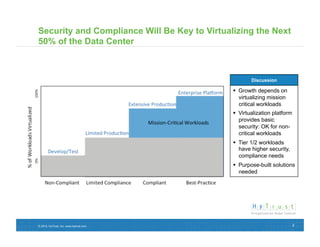
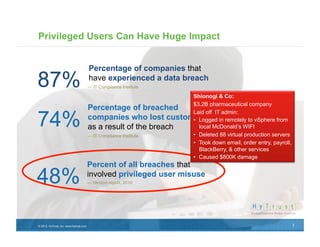
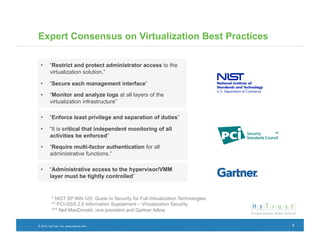
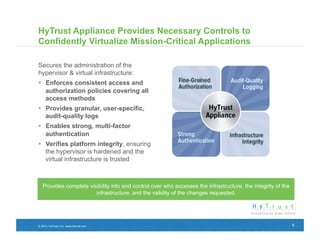
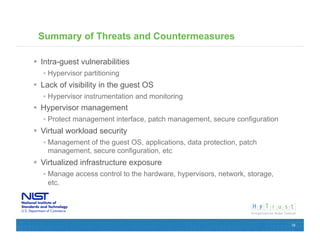
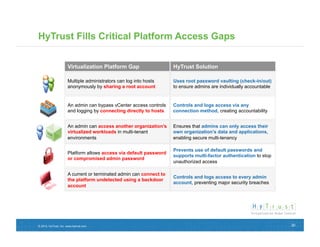
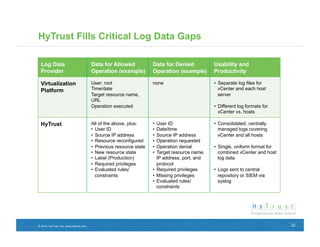
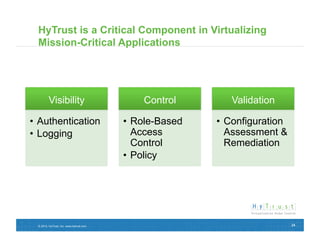
This document discusses securing virtual infrastructure while meeting compliance mandates. It notes that security and compliance will be key to virtualizing the next 50% of the data center, as tier 1 and 2 workloads have higher security and compliance needs than basic virtualization can provide. Purpose-built solutions are needed. It highlights how privileged users can impact organizations through data breaches or other incidents. Expert consensus recommends restricting administrator access and enforcing least privilege for virtualization solutions. The HyTrust Appliance is presented as providing necessary controls to securely virtualize mission-critical applications by enforcing access policies, providing auditing, and validating the integrity of the virtual infrastructure.