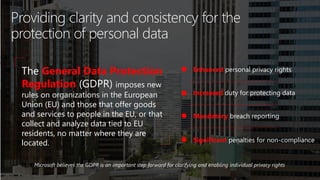
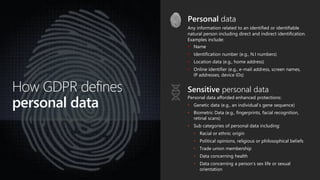
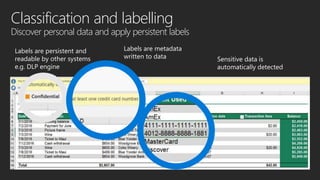
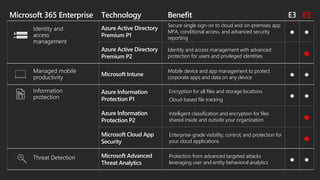
The document outlines the implications of the General Data Protection Regulation (GDPR) for organizations, including the need for improved data protection measures, enhanced personal privacy rights, and mandatory breach reporting. It details the responsibilities of organizations regarding personal data handling and the rights of individuals related to their data. Additionally, it discusses Microsoft 365 offerings that support compliance and security, highlighting the various subscription plans and features available for effective data governance.