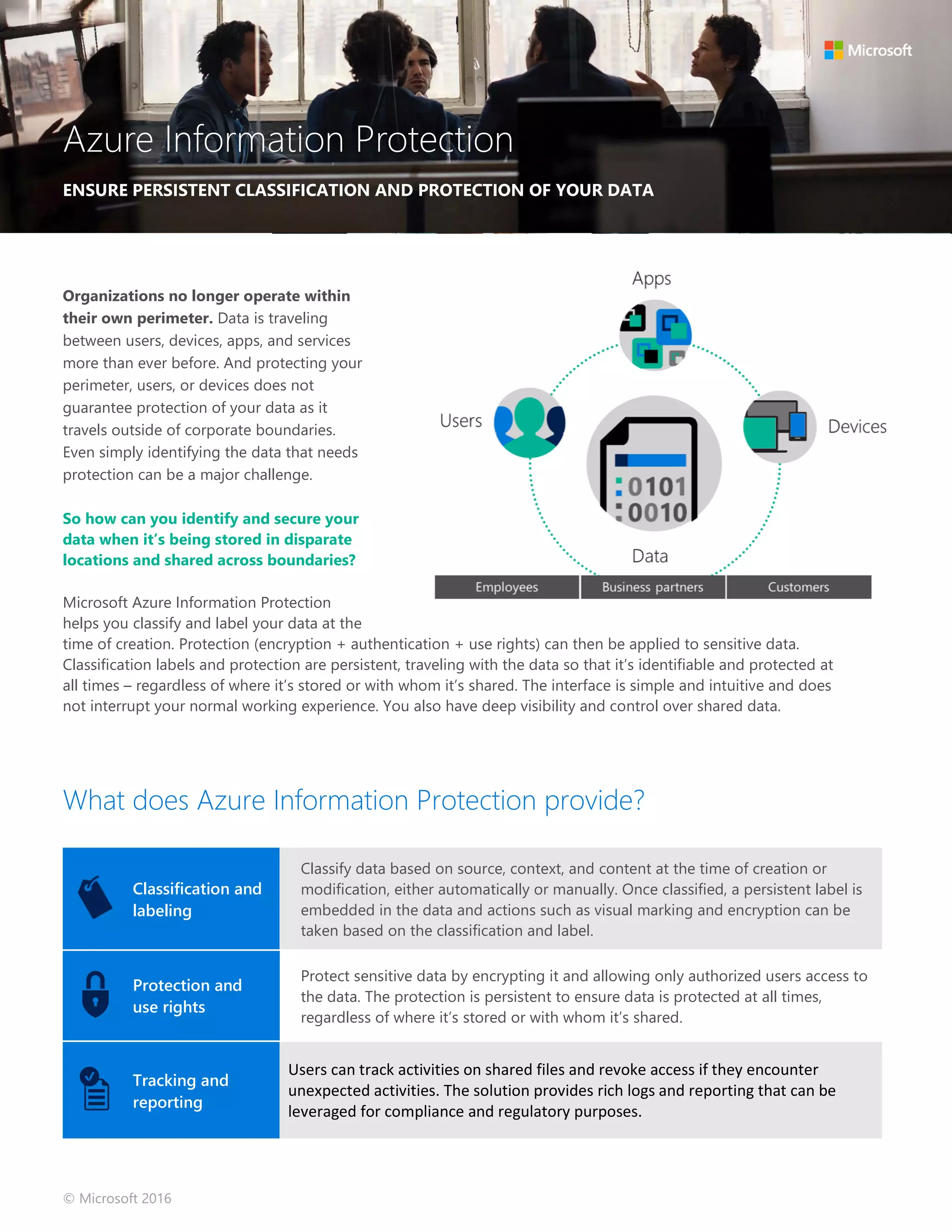
Microsoft Azure Information Protection helps organizations classify and protect sensitive data across devices and locations. It allows automatic or manual classification of data based on content, context and source. Once classified, a persistent label is embedded with the data and optional encryption can be applied. This ensures the data remains protected regardless of where it is stored or shared. The solution provides visibility into how data is used through tracking and reporting features.