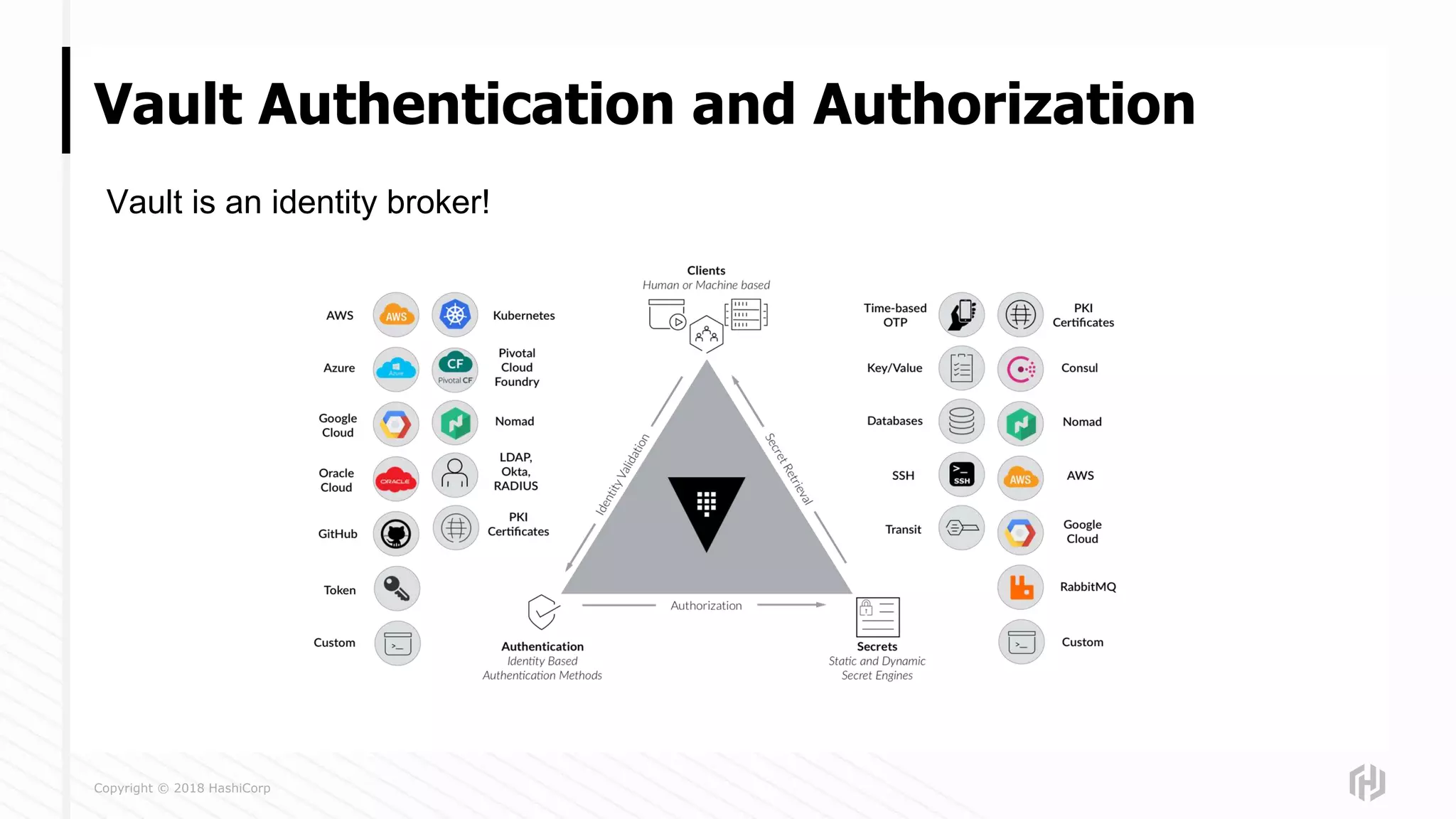
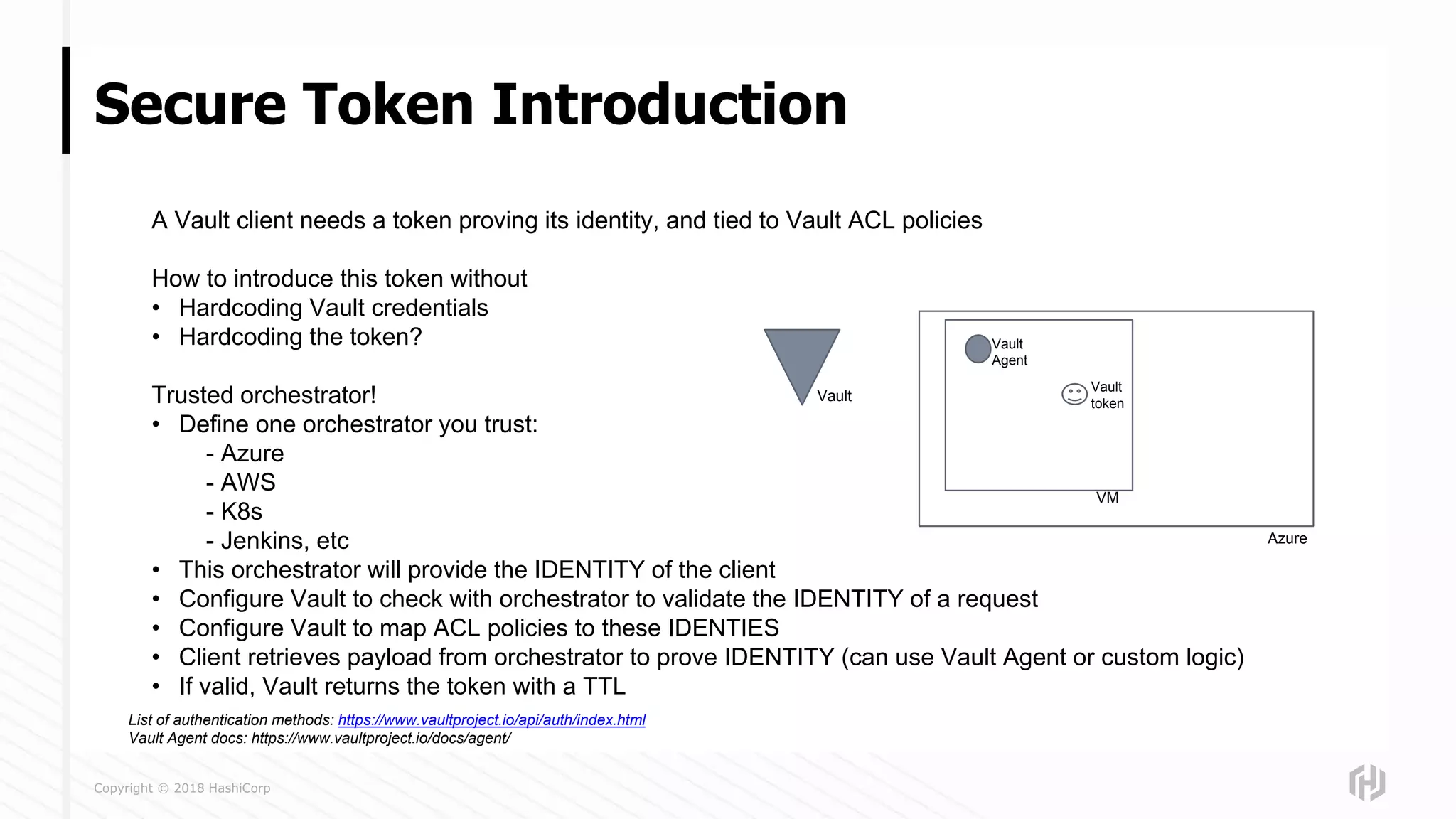
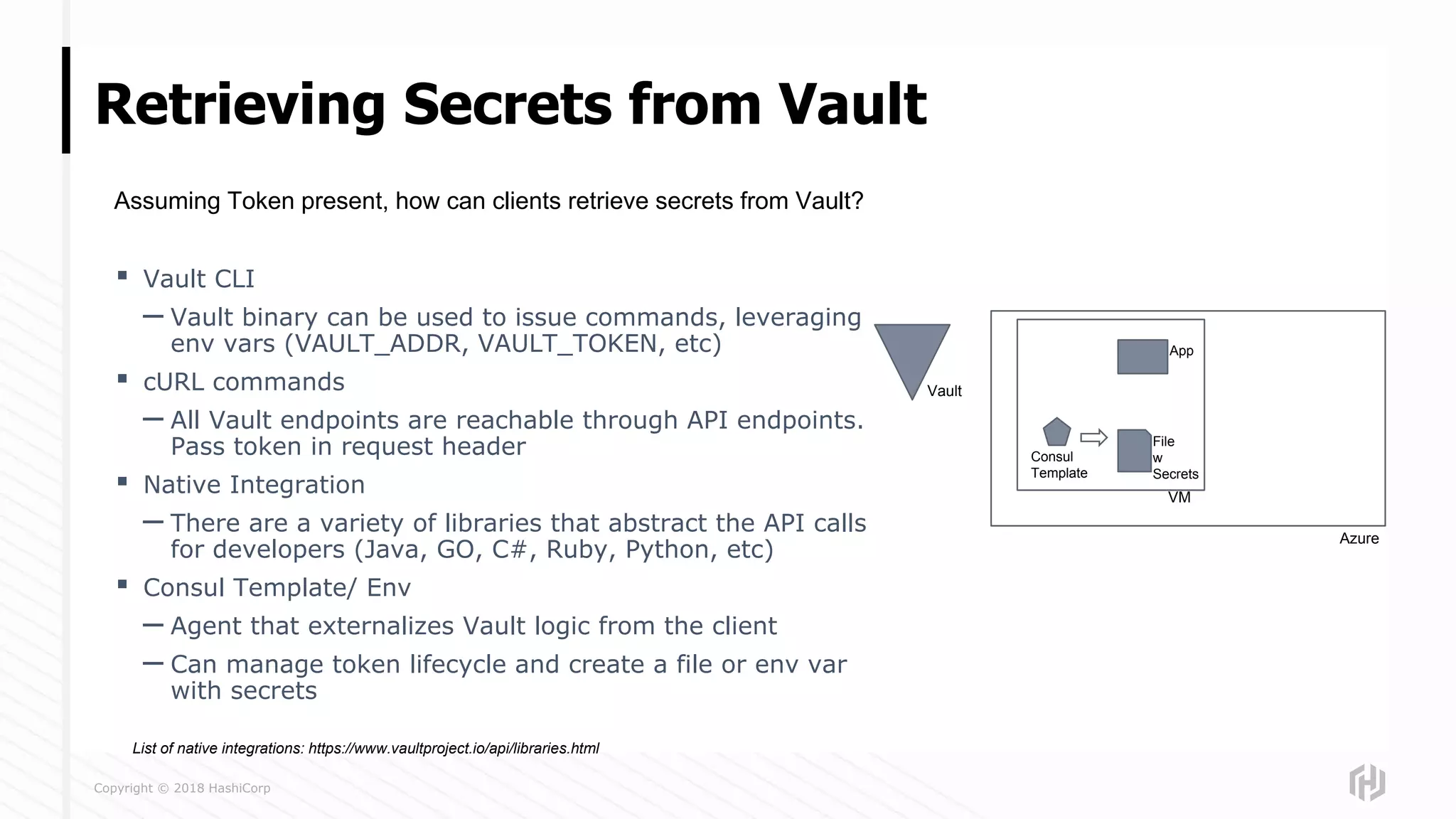
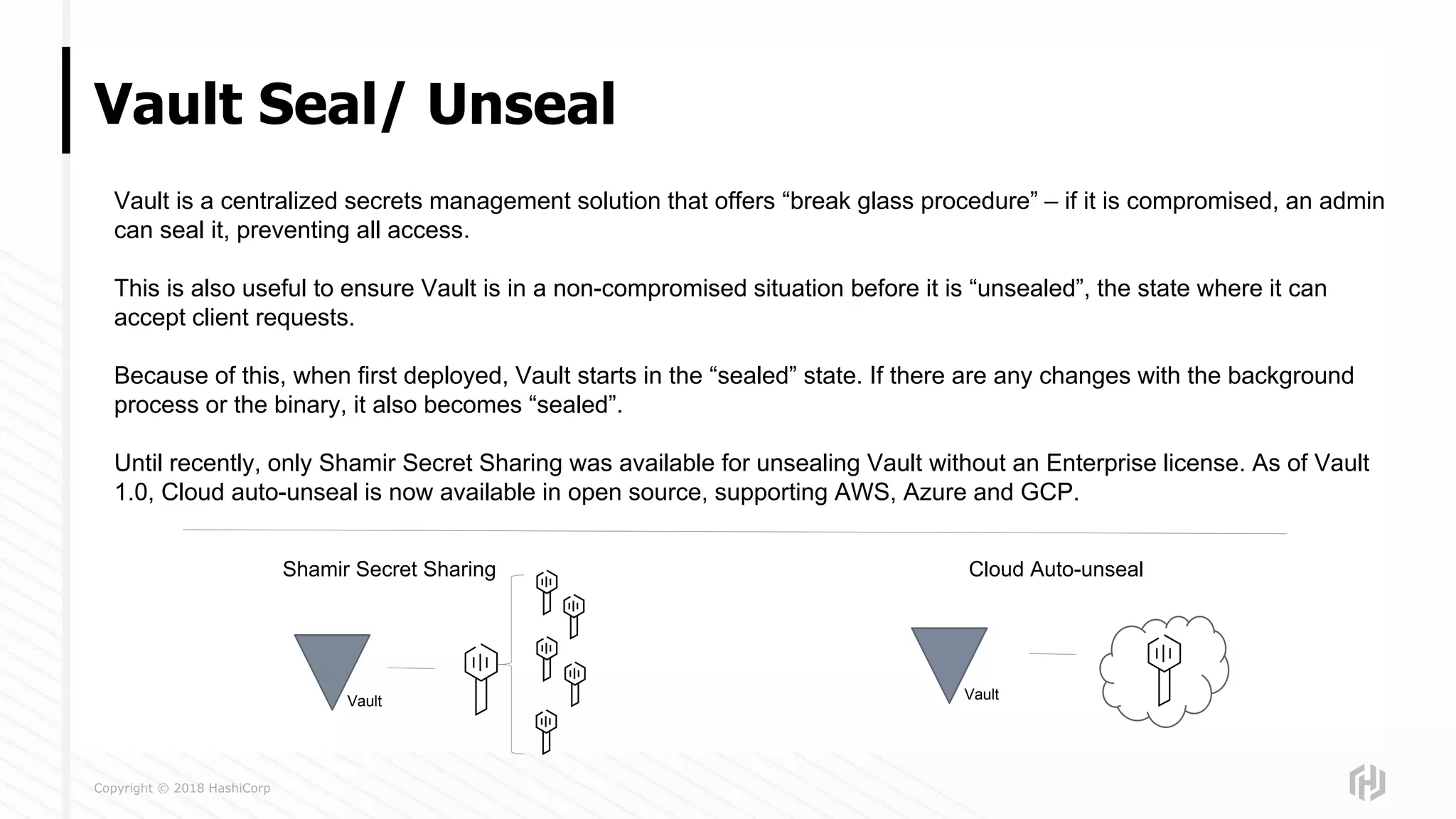
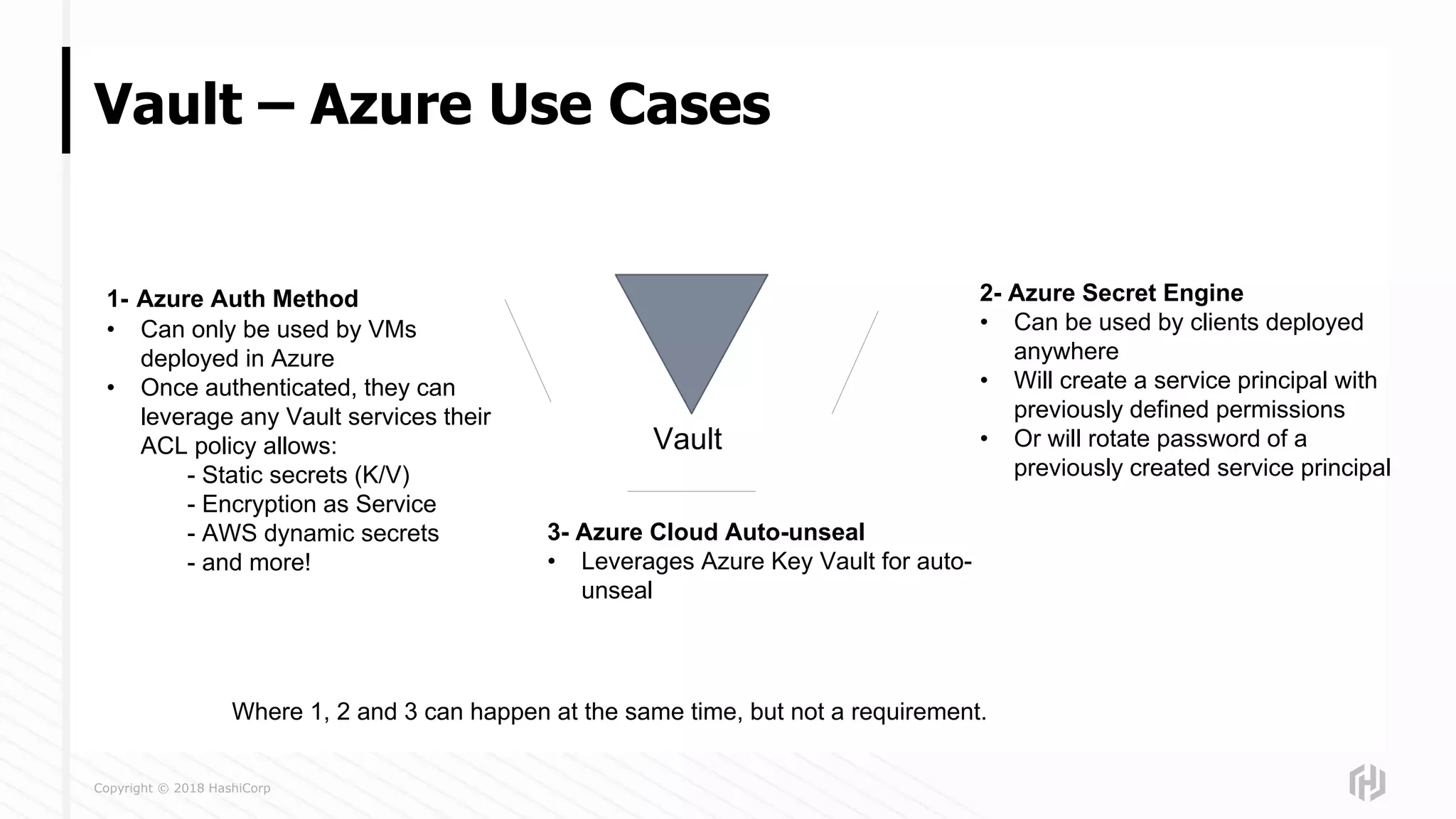
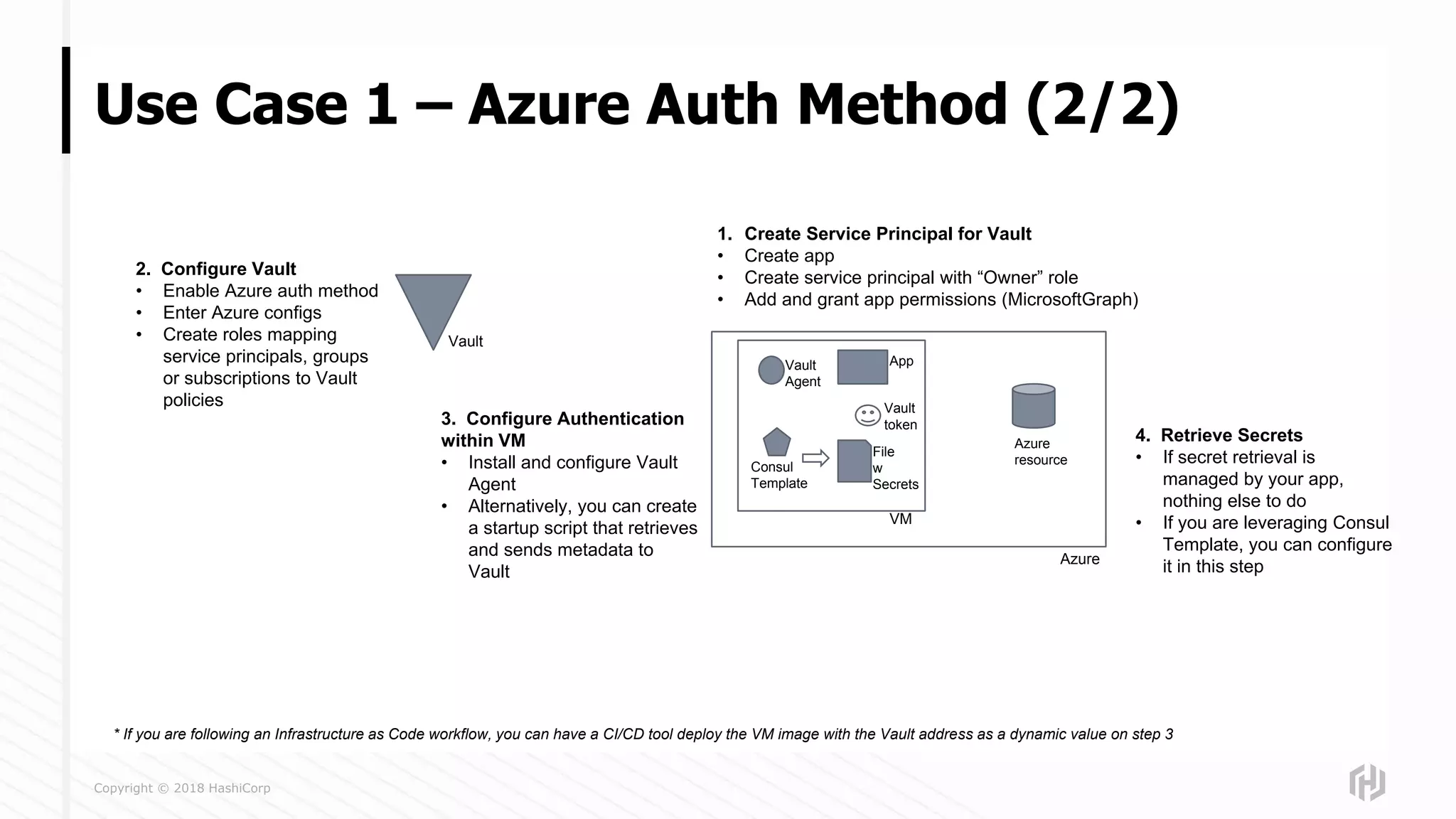
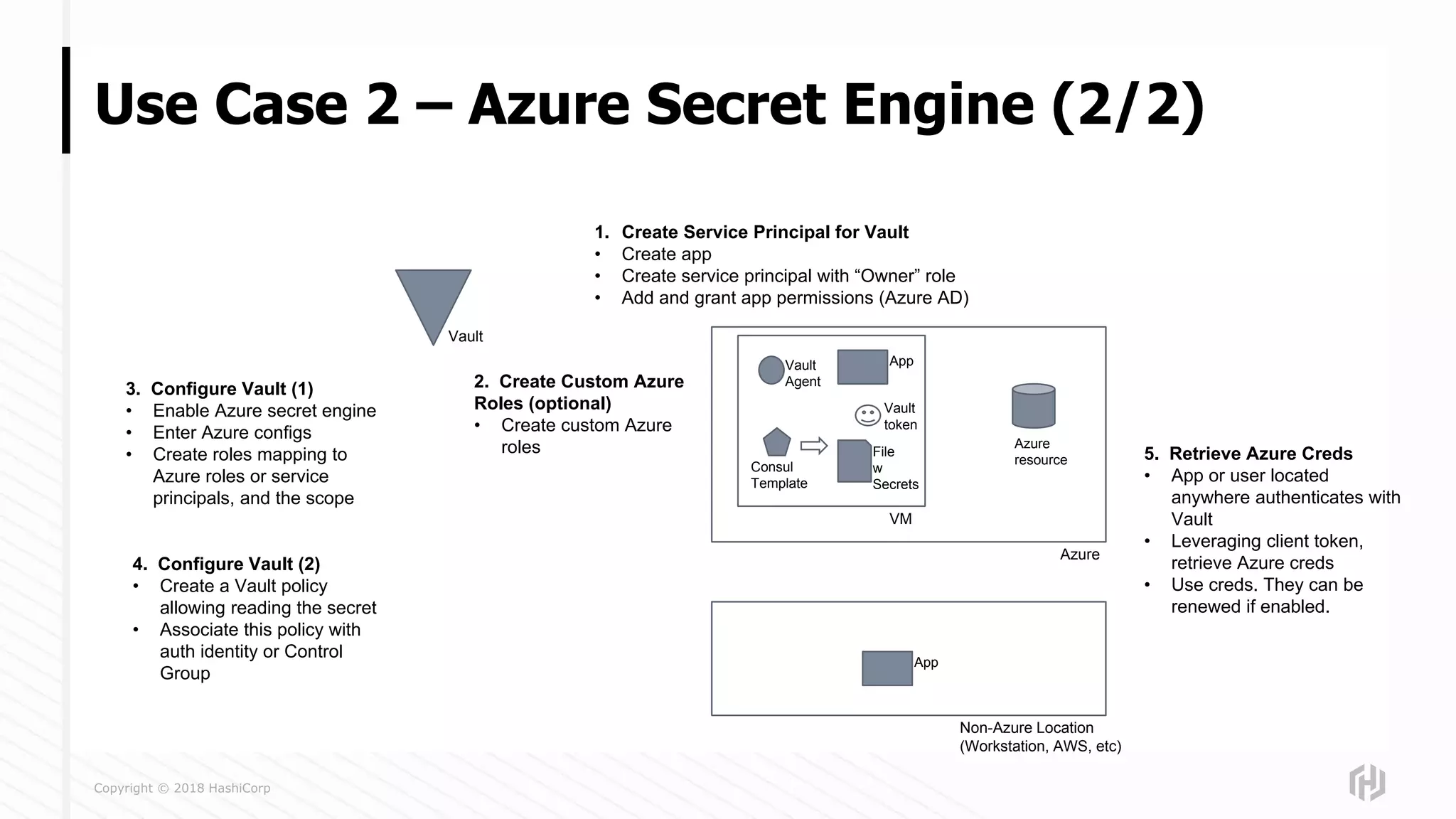
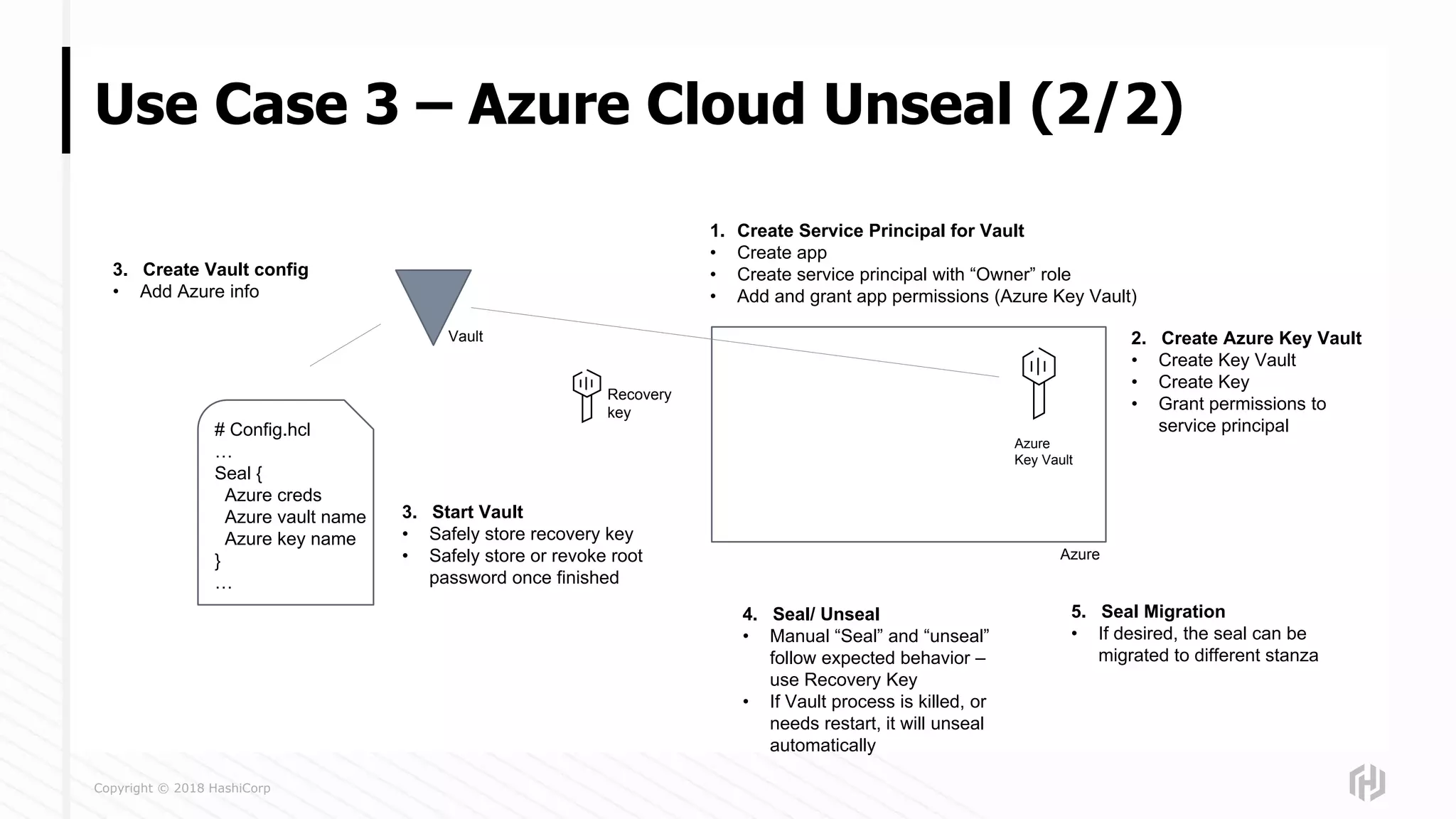
The document presents an overview of using HashiCorp Vault and Terraform for secure and automated workflows in Azure, detailing authentication methods, secret retrieval, and cloud unsealing. It discusses various use cases including the Azure auth method, Azure secret engine, and Azure cloud auto-unseal, highlighting best practices for managing secrets in cloud environments. Additionally, it provides an introduction to Vault's centralized secrets management, token-based authentication, and the capabilities for dynamic secrets in an infrastructure as code context.