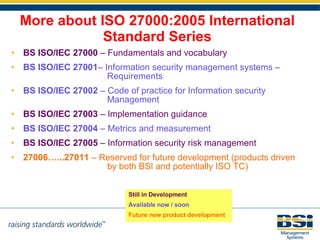
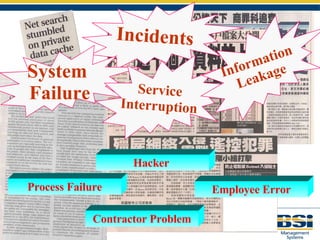
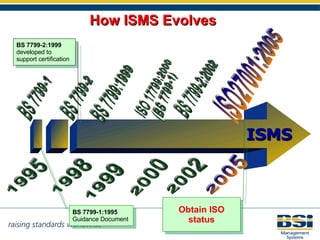
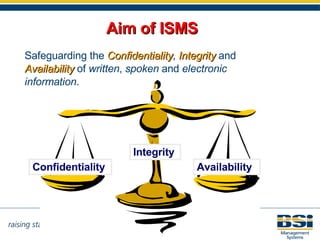
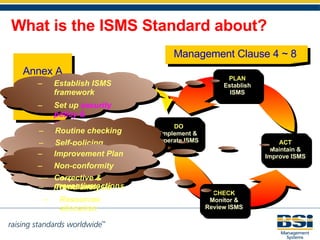
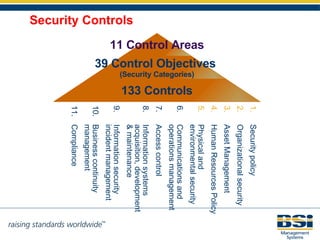
The document introduces the International Standard ISO 27001 for information security management systems. It discusses the evolution of the standard from earlier versions like BS 7799. ISO 27001 provides requirements and guidance for establishing, implementing, maintaining and improving an information security management system. The standard aims to safeguard the confidentiality, integrity and availability of information by implementing 133 controls across 11 control areas. Certification to ISO 27001 demonstrates an organization's commitment to information security and can help fulfill contractual requirements, reduce risks, increase confidence and provide a competitive advantage.



![For more ISO17799 & ISO27001 Pease contact our: Sales, Marketing & Training Department Tel: +852 3149-3300 / 3149-3320 Fax: +852 2743-8727 / 8343-7336 Email mkt. [email_address]](https://image.slidesharecdn.com/iso27001-isaca-seminar-23-may-08-1211729052746620-8/85/Iso27001-Isaca-Seminar-23-May-08-26-320.jpg)