3 data security strategies organizations
•
1 like•2,530 views
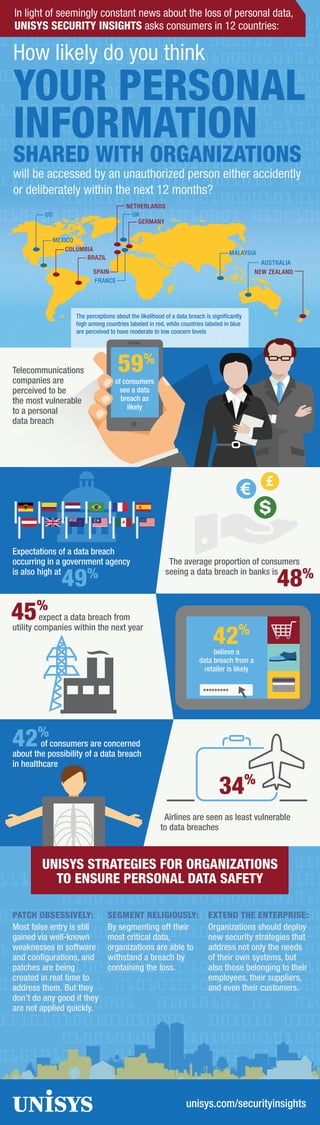
The document discusses strategies for organizations to ensure personal data safety in the face of increasing data breaches. It recommends that organizations extend security strategies beyond their own systems to include employee, supplier, and customer systems. It also advises segmenting critical data to contain losses from breaches and to obsessively apply software patches in a timely manner to address known weaknesses. A survey found that consumers have high expectations of data breaches occurring across many industries and geographic regions.
Report
Share
Report
Share
Download to read offline
Recommended
More Related Content
What's hot
What's hot (20)
2018 Survey: Consumer Attitudes in a Post-Breach Era - The Generational Gap

2018 Survey: Consumer Attitudes in a Post-Breach Era - The Generational Gap
Scared About Supply Chain Cybersecurity? 5 Reasons You Aren't Scared Enough

Scared About Supply Chain Cybersecurity? 5 Reasons You Aren't Scared Enough
Consumer Attitudes in a Post-breach Era: The Geographical Gap

Consumer Attitudes in a Post-breach Era: The Geographical Gap
Cost of Cybercrime Study in Financial Services: 2019 Report

Cost of Cybercrime Study in Financial Services: 2019 Report
Retail Industry Application Security Survey Insights

Retail Industry Application Security Survey Insights
Chief Audit Execs speak out: Cybersecurity & risk management

Chief Audit Execs speak out: Cybersecurity & risk management
The BYOD Trojan Horse: Dangerous Mobile App Behaviors and Back-Door Security ...

The BYOD Trojan Horse: Dangerous Mobile App Behaviors and Back-Door Security ...
Sameer Mitter |The impact of automation on the workforce

Sameer Mitter |The impact of automation on the workforce
Similar to 3 data security strategies organizations
Similar to 3 data security strategies organizations (20)
The Stand Against Cyber Criminals Lawyers, Take The Stand Against Cyber Crimi...

The Stand Against Cyber Criminals Lawyers, Take The Stand Against Cyber Crimi...
SVB Cybersecurity Impact on Innovation Report - Overview

SVB Cybersecurity Impact on Innovation Report - Overview
The Currency of Trust: Why Banks and Insurers Must Make Customer Data Safer a...

The Currency of Trust: Why Banks and Insurers Must Make Customer Data Safer a...
The impact of the bring your own device byod trend in the workplace

The impact of the bring your own device byod trend in the workplace
Perception Gaps in Cyber Resilience: What Are Your Blind Spots?

Perception Gaps in Cyber Resilience: What Are Your Blind Spots?
Enhancing Your Data Security: Closing the Gap on Unsecured Communications

Enhancing Your Data Security: Closing the Gap on Unsecured Communications
Booz Allen's 10 Cyber Priorities for Boards of Directors

Booz Allen's 10 Cyber Priorities for Boards of Directors
Ponemon Institute Data Breaches and Sensitive Data Risk

Ponemon Institute Data Breaches and Sensitive Data Risk
More from Unisys Corporation
More from Unisys Corporation (20)
Unisys Integrated Medical Device Management - Executive Brief

Unisys Integrated Medical Device Management - Executive Brief
SURVEY RESULTS: ACCELERATING INNOVATION AND THE DIGITAL JOURNEY - INFOGRAPHIC

SURVEY RESULTS: ACCELERATING INNOVATION AND THE DIGITAL JOURNEY - INFOGRAPHIC
Stealth Secures Along Every Step of Your Journey Infographic

Stealth Secures Along Every Step of Your Journey Infographic
DIE NEUE DIGITALE INFRASTRUKTUR FÜR DIGITALE MITARBEITER DER NÄCHSTEN GENERAT...

DIE NEUE DIGITALE INFRASTRUKTUR FÜR DIGITALE MITARBEITER DER NÄCHSTEN GENERAT...
STEHEN DIE ENDBENUTZER DER GENERATION „DIGITAL“FÜR DAS ENDE VON IT-TRANSPAREN...

STEHEN DIE ENDBENUTZER DER GENERATION „DIGITAL“FÜR DAS ENDE VON IT-TRANSPAREN...
DIE GENERATION DIGITAL UND DIE IT-LÜCKE IN UNTERNEHMEN.

DIE GENERATION DIGITAL UND DIE IT-LÜCKE IN UNTERNEHMEN.
Recently uploaded
Recently uploaded (20)
Swan(sea) Song – personal research during my six years at Swansea ... and bey...

Swan(sea) Song – personal research during my six years at Swansea ... and bey...
Handwritten Text Recognition for manuscripts and early printed texts

Handwritten Text Recognition for manuscripts and early printed texts
Tech-Forward - Achieving Business Readiness For Copilot in Microsoft 365

Tech-Forward - Achieving Business Readiness For Copilot in Microsoft 365
#StandardsGoals for 2024: What’s new for BISAC - Tech Forum 2024

#StandardsGoals for 2024: What’s new for BISAC - Tech Forum 2024
Integration and Automation in Practice: CI/CD in Mule Integration and Automat...

Integration and Automation in Practice: CI/CD in Mule Integration and Automat...
Injustice - Developers Among Us (SciFiDevCon 2024)

Injustice - Developers Among Us (SciFiDevCon 2024)
Breaking the Kubernetes Kill Chain: Host Path Mount

Breaking the Kubernetes Kill Chain: Host Path Mount
FULL ENJOY 🔝 8264348440 🔝 Call Girls in Diplomatic Enclave | Delhi

FULL ENJOY 🔝 8264348440 🔝 Call Girls in Diplomatic Enclave | Delhi
How to Remove Document Management Hurdles with X-Docs?

How to Remove Document Management Hurdles with X-Docs?
How to Troubleshoot Apps for the Modern Connected Worker

How to Troubleshoot Apps for the Modern Connected Worker
Enhancing Worker Digital Experience: A Hands-on Workshop for Partners

Enhancing Worker Digital Experience: A Hands-on Workshop for Partners
Beyond Boundaries: Leveraging No-Code Solutions for Industry Innovation

Beyond Boundaries: Leveraging No-Code Solutions for Industry Innovation
The 7 Things I Know About Cyber Security After 25 Years | April 2024

The 7 Things I Know About Cyber Security After 25 Years | April 2024
WhatsApp 9892124323 ✓Call Girls In Kalyan ( Mumbai ) secure service

WhatsApp 9892124323 ✓Call Girls In Kalyan ( Mumbai ) secure service
3 data security strategies organizations
- 1. 34% Airlines are seen as least vulnerable to data breaches 42% of consumers are concerned about the possibility of a data breach in healthcare EXTEND THE ENTERPRISE: Organizations should deploy new security strategies that address not only the needs of their own systems, but also those belonging to their employees, their suppliers, and even their customers. SEGMENT RELIGIOUSLY: By segmenting off their most critical data, organizations are able to withstand a breach by containing the loss. PATCH OBSESSIVELY: Most false entry is still gained via well-known weaknesses in software and configurations, and patches are being created in real time to address them. But they don’t do any good if they are not applied quickly. UNISYS STRATEGIES FOR ORGANIZATIONS TO ENSURE PERSONAL DATA SAFETY unisys.com/securityinsights 45% expect a data breach from utility companies within the next year ********* believe a data breach from a retailer is likely 42% The average proportion of consumers seeing a data breach in banks is 48% Expectations of a data breach occurring in a government agency is also high at 49% The perceptions about the likelihood of a data breach is significantly high among countries labeled in red, while countries labeled in blue are perceived to have moderate to low concern levels AUSTRALIA BRAZIL MEXICO US UK FRANCE MALAYSIA SPAIN NETHERLANDS COLOMBIA NEW ZEALAND GERMANY 59% of consumers see a data breach as likely Telecommunications companies are perceived to be the most vulnerable to a personal data breach In light of seemingly constant news about the loss of personal data, UNISYS SECURITY INSIGHTS asks consumers in 12 countries: How likely do you think YOUR PERSONAL INFORMATION SHARED WITH ORGANIZATIONS will be accessed by an unauthorized person either accidently or deliberately within the next 12 months?
