INFOGRAPHIC: The Evolution of Data Privacy
•
1 like•1,555 views
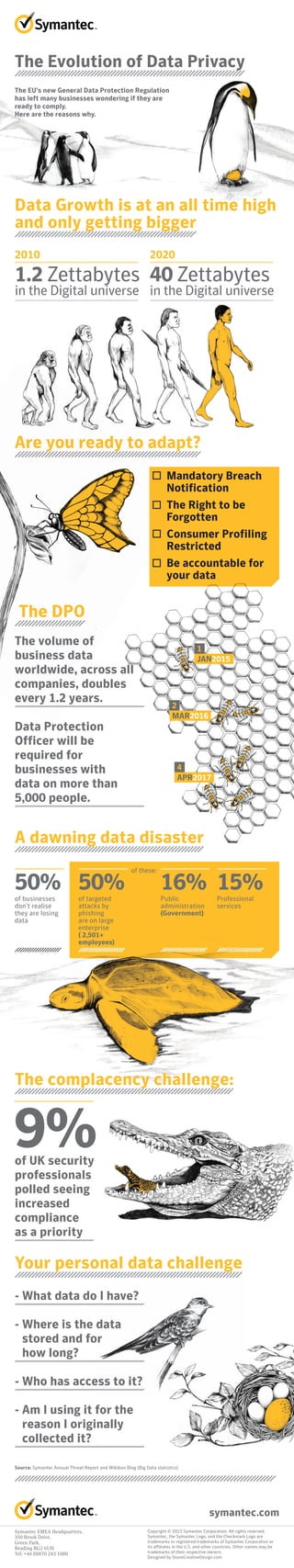
The document discusses the growing issue of data privacy and protection as data volumes continue to rapidly increase. It notes that by 2020 there will be 40 zettabytes of digital data, and many businesses are unprepared to properly handle and protect this data. The EU's new General Data Protection Regulation will require businesses to be more accountable with data and comply with regulations like mandatory breach notification, data subject rights, and restrictions on consumer profiling. Proper compliance will require businesses to know exactly what data they have, where it is stored, who has access, and how it is being used.
Report
Share
Report
Share
Download to read offline
Recommended
Recommended
Sharing the blame: How companies are collaborating on data security breaches

Sharing the blame: How companies are collaborating on data security breachesThe Economist Media Businesses
Critical Update Needed: Cybersecurity Expertise in the Boardroom

Critical Update Needed: Cybersecurity Expertise in the BoardroomStanford GSB Corporate Governance Research Initiative
More Related Content
What's hot
Sharing the blame: How companies are collaborating on data security breaches

Sharing the blame: How companies are collaborating on data security breachesThe Economist Media Businesses
Critical Update Needed: Cybersecurity Expertise in the Boardroom

Critical Update Needed: Cybersecurity Expertise in the BoardroomStanford GSB Corporate Governance Research Initiative
What's hot (19)
Social Media Balancing Security & Authenticity without Controlling the Message

Social Media Balancing Security & Authenticity without Controlling the Message
Information Security - Hiring Trends and Trends for the Future PDF

Information Security - Hiring Trends and Trends for the Future PDF
WSIS10 Action Line C5 Building Confidence and Security in the use of ICT's

WSIS10 Action Line C5 Building Confidence and Security in the use of ICT's
Sharing the blame: How companies are collaborating on data security breaches

Sharing the blame: How companies are collaborating on data security breaches
The Internet Is a Dog-Eat-Dog World, and Your App Is Clad in Milk-Bone Underwear

The Internet Is a Dog-Eat-Dog World, and Your App Is Clad in Milk-Bone Underwear
Chief Audit Execs speak out: Cybersecurity & risk management

Chief Audit Execs speak out: Cybersecurity & risk management
Critical Update Needed: Cybersecurity Expertise in the Boardroom

Critical Update Needed: Cybersecurity Expertise in the Boardroom
Similar to INFOGRAPHIC: The Evolution of Data Privacy
Steve Mills Senior Vice President and Group Executive IBM Software and Systems

Steve Mills Senior Vice President and Group Executive IBM Software and SystemsIBM India Smarter Computing
Similar to INFOGRAPHIC: The Evolution of Data Privacy (20)
CBIZ Cyber Security - What Every Business Needs to Know

CBIZ Cyber Security - What Every Business Needs to Know
2010 6 Things u need 2 know in 2010 Whitepaper Final

2010 6 Things u need 2 know in 2010 Whitepaper Final
http://www.slideshare.net/slideshow/embed_code/28627951

http://www.slideshare.net/slideshow/embed_code/28627951
Webinar - Security 2.0: A new way to deal with today’s security challenges in...

Webinar - Security 2.0: A new way to deal with today’s security challenges in...
11 19-2015 - iasaca membership conference - the state of security

11 19-2015 - iasaca membership conference - the state of security
Steve Mills Senior Vice President and Group Executive IBM Software and Systems

Steve Mills Senior Vice President and Group Executive IBM Software and Systems
Information Security and Data Breach Trends 2014-2015

Information Security and Data Breach Trends 2014-2015
The Evolution of Data Privacy - A Symantec Information Security Perspective o...

The Evolution of Data Privacy - A Symantec Information Security Perspective o...
Cybersecurity Facts & Figures - What Every Business Needs to Know

Cybersecurity Facts & Figures - What Every Business Needs to Know
More from Symantec
More from Symantec (20)
Symantec Enterprise Security Products are now part of Broadcom

Symantec Enterprise Security Products are now part of Broadcom
Symantec Webinar | National Cyber Security Awareness Month: Fostering a Secur...

Symantec Webinar | National Cyber Security Awareness Month: Fostering a Secur...
Symantec Webinar | National Cyber Security Awareness Month: Protect IT

Symantec Webinar | National Cyber Security Awareness Month: Protect IT
Symantec Webinar | National Cyber Security Awareness Month: Secure IT

Symantec Webinar | National Cyber Security Awareness Month: Secure IT
Symantec Webinar | National Cyber Security Awareness Month - Own IT

Symantec Webinar | National Cyber Security Awareness Month - Own IT
Symantec Webinar: Preparing for the California Consumer Privacy Act (CCPA)

Symantec Webinar: Preparing for the California Consumer Privacy Act (CCPA)
Symantec Webinar | How to Detect Targeted Ransomware with MITRE ATT&CK

Symantec Webinar | How to Detect Targeted Ransomware with MITRE ATT&CK
Symantec Webinar | Security Analytics Breached! Next Generation Network Foren...

Symantec Webinar | Security Analytics Breached! Next Generation Network Foren...
Symantec Webinar | Implementing a Zero Trust Framework to Secure Modern Workf...

Symantec Webinar | Implementing a Zero Trust Framework to Secure Modern Workf...
Symantec Webinar | Tips for Successful CASB Projects

Symantec Webinar | Tips for Successful CASB Projects
Symantec Webinar: What Cyber Threats Are Lurking in Your Network?

Symantec Webinar: What Cyber Threats Are Lurking in Your Network?
Symantec Best Practices for Cloud Security: Insights from the Front Lines

Symantec Best Practices for Cloud Security: Insights from the Front Lines
Symantec - The Importance of Building Your Zero Trust Program on a Solid Plat...

Symantec - The Importance of Building Your Zero Trust Program on a Solid Plat...
Symantec Webinar | Redefining Endpoint Security- How to Better Secure the End...

Symantec Webinar | Redefining Endpoint Security- How to Better Secure the End...
Symantec Webinar Using Advanced Detection and MITRE ATT&CK to Cage Fancy Bear

Symantec Webinar Using Advanced Detection and MITRE ATT&CK to Cage Fancy Bear
Recently uploaded
Recently uploaded (20)
Vulnerability_Management_GRC_by Sohang Sengupta.pptx

Vulnerability_Management_GRC_by Sohang Sengupta.pptx
Artificial intelligence in the post-deep learning era

Artificial intelligence in the post-deep learning era
Injustice - Developers Among Us (SciFiDevCon 2024)

Injustice - Developers Among Us (SciFiDevCon 2024)
Integration and Automation in Practice: CI/CD in Mule Integration and Automat...

Integration and Automation in Practice: CI/CD in Mule Integration and Automat...
Azure Monitor & Application Insight to monitor Infrastructure & Application

Azure Monitor & Application Insight to monitor Infrastructure & Application
Hyderabad Call Girls Khairatabad ✨ 7001305949 ✨ Cheap Price Your Budget

Hyderabad Call Girls Khairatabad ✨ 7001305949 ✨ Cheap Price Your Budget
Automating Business Process via MuleSoft Composer | Bangalore MuleSoft Meetup...

Automating Business Process via MuleSoft Composer | Bangalore MuleSoft Meetup...
#StandardsGoals for 2024: What’s new for BISAC - Tech Forum 2024

#StandardsGoals for 2024: What’s new for BISAC - Tech Forum 2024
Neo4j - How KGs are shaping the future of Generative AI at AWS Summit London ...

Neo4j - How KGs are shaping the future of Generative AI at AWS Summit London ...
IAC 2024 - IA Fast Track to Search Focused AI Solutions

IAC 2024 - IA Fast Track to Search Focused AI Solutions
08448380779 Call Girls In Greater Kailash - I Women Seeking Men

08448380779 Call Girls In Greater Kailash - I Women Seeking Men
Presentation on how to chat with PDF using ChatGPT code interpreter

Presentation on how to chat with PDF using ChatGPT code interpreter
INFOGRAPHIC: The Evolution of Data Privacy
- 1. A dawning data disaster The complacency challenge: Your personal data challenge The Evolution of Data Privacy The EU’s new General Data Protection Regulation has left many businesses wondering if they are ready to comply. Here are the reasons why. 2010 1.2 Zettabytes in the Digital universe 2020 40 Zettabytes in the Digital universe 50%of businesses don’t realise they are losing data Data Growth is at an all time high and only getting bigger Are you ready to adapt? Mandatory Breach Notification The Right to be Forgotten Consumer Profiling Restricted Be accountable for your data The volume of business data worldwide, across all companies, doubles every 1.2 years. Data Protection Officer will be required for businesses with data on more than 5,000 people. - What data do I have? - Where is the data stored and for how long? - Who has access to it? - Am I using it for the reason I originally collected it? of UK security professionals polled seeing increased compliance as a priority The DPO 50%of targeted attacks by phishing are on large enterprise ( 2,501+ employees) 16%Public administration (Government) 15%Professional services of these: 9% Source: Symantec Annual Threat Report and Wikibon Blog (Big Data statistics) Symantec EMEA Headquarters, 350 Brook Drive, Green Park, Reading RG2 6UH Tel: +44 (0)870 243 1080 Copyright © 2015 Symantec Corporation. All rights reserved. Symantec, the Symantec Logo, and the Checkmark Logo are trademarks or registered trademarks of Symantec Corporation or its affiliates in the U.S. and other countries. Other names may be trademarks of their respective owners. Designed by StoneCreativeDesign.com symantec.com JAN2015 1 2 4 MAR2016 APR2017
