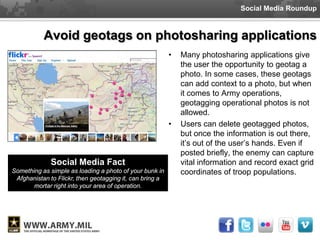
This document discusses the risks of geotagging photos and using location-based social media when one is in the military. It notes that geotagged photos and check-ins on apps like Foursquare can reveal sensitive information like locations of military bases or troop movements. The document provides tips for protecting operational security, such as turning off GPS metadata in photos and location services on phones when one is engaged in military operations. Revealing location data could damage missions and endanger lives.