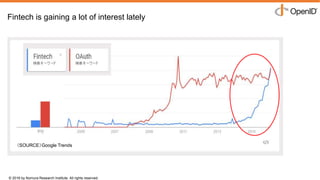
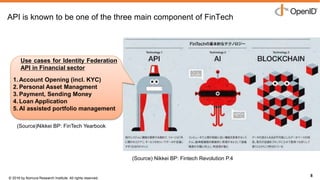
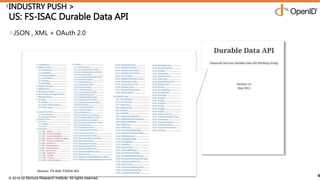
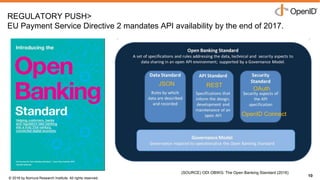
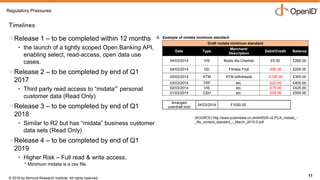
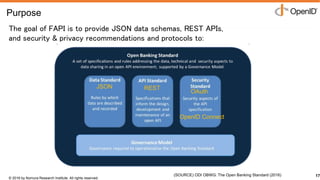
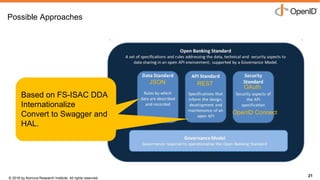
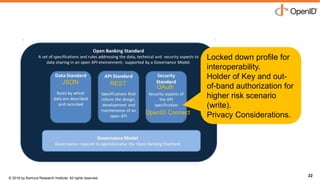
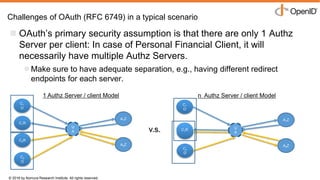
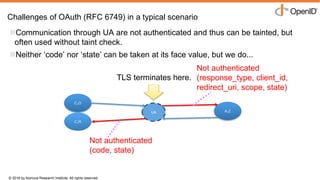
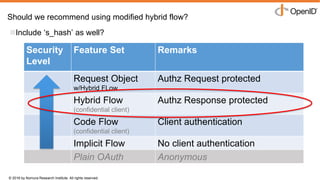
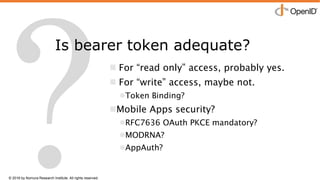
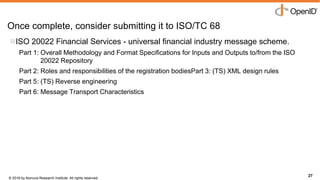
The document discusses the evolution of financial data access through APIs, highlighting the persistence of screen scraping since 2001 and recent regulatory pushes towards open banking solutions. It emphasizes the importance of JSON data schemas and security protocols to facilitate user control over financial data without relying on outdated methods. The document suggests that improved standards will foster innovation in fintech while addressing security concerns associated with OAuth.