The document discusses the history of formally verifying programming language compiler implementations from the 1960s to the 2000s. It summarizes early work in the 1960s and 1970s proving correctness of compilers for simple arithmetic languages. Later work in the 1980s and 1990s proved correctness for compilers targeting more complex languages and using mechanized theorem proving. Recent work in the 2000s has formally verified compilers for realistic languages to low-level targets using proof assistants like Coq.
![Motivation 1960s Proof 1970s 1980s 1990s 2000s Conclusions
Compiling an arithmetic language
Compile from a simple arithmetic language to machine code for a
simple register machine.
Example taken from [McCart67]](https://image.slidesharecdn.com/litsem-100111105344-phpapp02/85/Formal-Verification-of-Programming-Languages-2-320.jpg)
![Motivation 1960s Proof 1970s 1980s 1990s 2000s Conclusions
Compiling an arithmetic language
Compile from a simple arithmetic language to machine code for a
simple register machine.
Source language
Numeric constants
Variables
Addition
e.g. (x + 3) + (x + (y + 2))
Example taken from [McCart67]](https://image.slidesharecdn.com/litsem-100111105344-phpapp02/85/Formal-Verification-of-Programming-Languages-3-320.jpg)
![Motivation 1960s Proof 1970s 1980s 1990s 2000s Conclusions
Compiling an arithmetic language
Compile from a simple arithmetic language to machine code for a
simple register machine.
Target language
Source language
Load Immediate into ac
Numeric constants LOAD into ac from
Variables address/register
Addition STOre ac value to
address/register
e.g. (x + 3) + (x + (y + 2))
ADD register value to ac
Example taken from [McCart67]](https://image.slidesharecdn.com/litsem-100111105344-phpapp02/85/Formal-Verification-of-Programming-Languages-4-320.jpg)
![Motivation 1960s Proof 1970s 1980s 1990s 2000s Conclusions
Compiling an arithmetic language
Arithmetic expression compiler in Haskell
compile :: I n t → Source → Target
compile t ( Const v ) = [ Li v ]
compile t ( Var x ) = [ Load (Map x ) ]
compile t (Sum e1 e2 ) = c o m p i l e t e1
++ [ Sto ( Reg t ) ]
++ c o m p i l e ( t + 1 ) e2
++ [ Add ( Reg t ) ]
When compiled and executed, is the value in the accumulator the
result of the source arithmetic expression?](https://image.slidesharecdn.com/litsem-100111105344-phpapp02/85/Formal-Verification-of-Programming-Languages-5-320.jpg)
![Motivation 1960s Proof 1970s 1980s 1990s 2000s Conclusions
Compiling an arithmetic language
(x + 3) + (x + (y + 2)) compiled to machine code?
1 LOAD M[x] 8 LOAD M[y]
2 STO R[t + 0] 9 STO R[t + 2]
3 LI 3 10 LI 2
4 ADD R[t + 0] 11 ADD R[t + 2]
5 STO R[t + 0] 12 ADD R[t + 1]
6 LOAD M[x] 13 ADD R[t]
7 STO R[t + 1]
n.b. Where M is a mapping of variable names to memory locations and R is an
indexing of registers.](https://image.slidesharecdn.com/litsem-100111105344-phpapp02/85/Formal-Verification-of-Programming-Languages-6-320.jpg)
![Motivation 1960s Proof 1970s 1980s 1990s 2000s Conclusions
Can you trust your compiler?
Use a compiler to translate from a high-level language to a
low-level
Compilers are programs (generally) written by people
People make mistakes
Can silently turn “a correct program into an incorrect
executable” [Leroy09]
GHC 6.10.x is ≈ 800, 000 lines of code and has had 737 bugs
reported in the bug tracker as of 04/12/2009 [GHC]
Can we formally verify a compiler?](https://image.slidesharecdn.com/litsem-100111105344-phpapp02/85/Formal-Verification-of-Programming-Languages-8-320.jpg)
![Motivation 1960s Proof 1970s 1980s 1990s 2000s Conclusions
McCarthy and Painter, 1967
“Correctness of a compiler for arithmetic expressions”
[McCart67]
Describe, in first-order predicate logic;
Source language semantics
Target language semantics
A compilation process
Reason that the compiler maintains semantic equivalence](https://image.slidesharecdn.com/litsem-100111105344-phpapp02/85/Formal-Verification-of-Programming-Languages-9-320.jpg)
![Motivation 1960s Proof 1970s 1980s 1990s 2000s Conclusions
McCarthy and Painter, 1967
Semantic equivalence in [McCart67]
∀e ∈ Expressions, ∀µ ∈ Variable Mappings •
source(e, µ) ≡ acValue(target(compile(e), construct(µ)))
Very limited, small toy source and target language
Proof performed by hand
Logical framework and proof presented in under ten pages
Shows that proving a compiler correct is possible](https://image.slidesharecdn.com/litsem-100111105344-phpapp02/85/Formal-Verification-of-Programming-Languages-10-320.jpg)
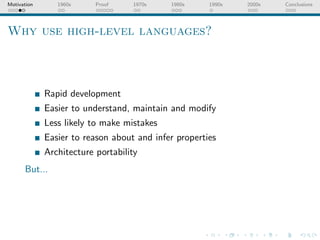
![Motivation 1960s Proof 1970s 1980s 1990s 2000s Conclusions
Proving the [McCart67] compiler
target (compile t x) ( construct s) Ac ≡ source x s
type Abstract = Name → Value
type Concrete = Address → Value
construct s = λ (Map v ) → s v
write k v s = λ k’ → i f k == k ’ t h e n v e l s e s k ’
−− S e m a n t i c s f o r the source language
s o u r c e : : Source → A b s t r a c t → Value
s o u r c e ( Const n ) = n
s o u r c e ( Var v ) s = s v
s o u r c e ( Add x y ) s = source x s + source y s
−− S e m a n t i c s f o r t h e t a r g e t l a n g u a g e
t a r g e t : : Target → Concrete → Concrete
target [ ] s = s
t a r g e t ( i : i s ) s = t a r g e t i s $ case i of
Li n → w r i t e Ac n s
Load r → w r i t e Ac ( s r ) s
Sto r → w r i t e r ( s Ac ) s
Sum r → w r i t e Ac ( s Ac + s r ) s](https://image.slidesharecdn.com/litsem-100111105344-phpapp02/85/Formal-Verification-of-Programming-Languages-11-320.jpg)
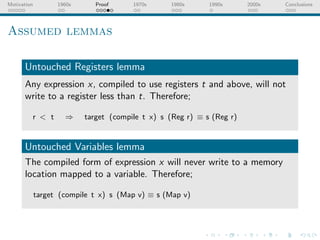
![Motivation 1960s Proof 1970s 1980s 1990s 2000s Conclusions
Proving the [McCart67] compiler
Proof of correctness for constants
{ case where ‘x = Const n’ }
target (compile t (Const n)) ( construct s) Ac
= { inline ‘compile’ }
target [ Li n] ( construct s) Ac
= { inline ‘ target ’ }
write Ac n (construct s) Ac
= { inline ‘ write ’ }
n
= { equivalent to }
source (Const v) s](https://image.slidesharecdn.com/litsem-100111105344-phpapp02/85/Formal-Verification-of-Programming-Languages-12-320.jpg)
![Motivation 1960s Proof 1970s 1980s 1990s 2000s Conclusions
Proving the [McCart67] compiler
Proof of correctness for variables
{ case where ‘x = Var v’ }
target (compile t (Var v)) ( construct s) Ac
= { inline ‘compile’ }
target [Load (Map v)] (construct s) Ac
= { inline ‘ target ’ }
write Ac (construct s (Map v)) (construct s) Ac
= { inline ‘ write ’ }
( construct s) (Map v)
= { inline ‘ construct ’ }
s v
= { equivalent to }
source (Var v) s](https://image.slidesharecdn.com/litsem-100111105344-phpapp02/85/Formal-Verification-of-Programming-Languages-13-320.jpg)
![Motivation 1960s Proof 1970s 1980s 1990s 2000s Conclusions
Proving the [McCart67] compiler
Proof of correctness for addition
{ case where ‘x = Add x y’ }
target (compile t (Add x y)) ( construct s) Ac
= { inline ‘compile’ and ‘ target ’ }
let s1 = target (compile t x) ( construct s)
s2 = write (Reg t) (s1 Ac) s1
s3 = target (compile (t + 1) y) s2
in write Ac (s3 Ac + s3 (Reg t)) s3 Ac
= { State lemmas and inline ‘ write ’ s }
target (compile t x) ( construct s) Ac +
target (compile (t + 1) y) ( construct s) Ac
= { inductive hypothesis − structural induction }
source x s + source y s
= { equivalent to }
source (Add x y) s](https://image.slidesharecdn.com/litsem-100111105344-phpapp02/85/Formal-Verification-of-Programming-Languages-15-320.jpg)
![Motivation 1960s Proof 1970s 1980s 1990s 2000s Conclusions
Milner and Weyhrauch, 1972
“Proving compiler correctness in a mechanised logic”
[Milner72]
Provide an LCF machine-checked proof of the
McCarthy-Painter example
Proceed towards mechanically proving a compiler for a more
complex language to a stack machine
Claim to have “no significant doubt that the remainder of the
proof can be done on machine” [Milner72]](https://image.slidesharecdn.com/litsem-100111105344-phpapp02/85/Formal-Verification-of-Programming-Languages-16-320.jpg)
![Motivation 1960s Proof 1970s 1980s 1990s 2000s Conclusions
Morris, 1973
“Advice on structuring compilers and proving them correct”
[Morris73]
Proves by hand the correctness of a compiler for a source
language that contains assignment, conditionals, loops,
arithmetic, booleans operations and local definitions
“Essence” of the advice presented in [Morris73]
compile
Source language −−→
−− Target language
Target semantics
Source semantics
Source meanings ←−−
−− Target meanings
decode](https://image.slidesharecdn.com/litsem-100111105344-phpapp02/85/Formal-Verification-of-Programming-Languages-17-320.jpg)
![Motivation 1960s Proof 1970s 1980s 1990s 2000s Conclusions
Thatcher, Wagner and Wright, 1980
Advice presented in [Thatch80]
compile
Source language −−→
−− Target language
Target semantics
Source semantics
Source meanings −−→
−− Target meanings
encode
“More on advice on structuring compilers and proving them
correct” [Thatch80]
Provides a different encoding of the target language to
[Morris73]
Claim that mechanised theorem proving tools required further
development](https://image.slidesharecdn.com/litsem-100111105344-phpapp02/85/Formal-Verification-of-Programming-Languages-18-320.jpg)
![Motivation 1960s Proof 1970s 1980s 1990s 2000s Conclusions
Syntax of source language in [Thatch80]
ae ::= integer constant
st ::= continue
| variable
| variable := ae
| - ae
| if be then st else st
| Pr ae
| st ; st
| Su ae
| while be do st
| ae + ae
be ::= boolean constant | ae − ae
| even ae | ae × ae
| ae ≤ ae | if be then ae else ae
| ae ≥ ae | st result ae
| ae = ae | let variable be ae in ae
| ¬ be n.b. Similar to [Milner72] and [Morris73]
| be ∧ be but with more operators and sequential
| be ∨ be composition. Struggling to fit this onto
one slide.](https://image.slidesharecdn.com/litsem-100111105344-phpapp02/85/Formal-Verification-of-Programming-Languages-19-320.jpg)
![Motivation 1960s Proof 1970s 1980s 1990s 2000s Conclusions
The “structuring compilers” series
Discuss constructing algebras to describe language syntax and
meaning
The language abstract syntaxes as initial algebras
Unique homomorphism from syntaxes to meanings, the
semantics
The compiler is the unique homomorphism between source
and target syntaxes
“... reduces to a proof that encode is a homomorphism ...”
[Thatch80]
“No structual induction is required ...” [Thatch80]](https://image.slidesharecdn.com/litsem-100111105344-phpapp02/85/Formal-Verification-of-Programming-Languages-20-320.jpg)
![Motivation 1960s Proof 1970s 1980s 1990s 2000s Conclusions
Meijer, 1994
“More advice on proving a compiler correct: Improve a correct
compiler” [Meijer94]
Given an interpreter for a source language, can we transform
it into a compiler to and residual interpreter for the target
language?
A functional decomposition problem (i.e.
interpreter = emulator ◦ compiler )
Demonstrate this technique for a first-order imperative
language compiling to a three-address code machine
While quite feasible for first-order languages, becomes far
more difficult for higher-order languages](https://image.slidesharecdn.com/litsem-100111105344-phpapp02/85/Formal-Verification-of-Programming-Languages-21-320.jpg)
![Motivation 1960s Proof 1970s 1980s 1990s 2000s Conclusions
Berghofer and Stecker, 2003
“Extracting a formally verified, fully executable compiler from
a proof assistant” [Bergho03]
Proves a compiler for a subset of the Java source language to
Java bytecode
Includes typechecking, abstract syntax tree annotation and
bytecode translation
Isabelle/HOL used to prove properties about an abstract
compiler
Isabelle code extraction to produce an executable compiler](https://image.slidesharecdn.com/litsem-100111105344-phpapp02/85/Formal-Verification-of-Programming-Languages-22-320.jpg)
![Motivation 1960s Proof 1970s 1980s 1990s 2000s Conclusions
Dave, 2003
Papers listed against decade published
Maulik A. Dave’s
bibliography for “Compiler
Verification” [Dave03]
Ninety-nine papers listed
Ninety-one of those listed
were published after 1990
Interestingly neither the
Milner and Weyhrauch paper
nor the Meijer are included](https://image.slidesharecdn.com/litsem-100111105344-phpapp02/85/Formal-Verification-of-Programming-Languages-23-320.jpg)
![Motivation 1960s Proof 1970s 1980s 1990s 2000s Conclusions
Recent work
Leroy’s “A formally verified compiler back-end” [Leroy09]
Proves a compiler for Cminor to PowerPC assembler
Chlipala’s “A verified compiler for an impure functional
language” [Chlipa10]
For a toy (but still quite feature rich) functional source
language to instructions register-based machine
Both use the Coq proof assistant and code extraction
Both decompose the problem into compilation to several
intermediate languages
Both express worries that the proof assistant itself contain
bugs that would invalidate correctness](https://image.slidesharecdn.com/litsem-100111105344-phpapp02/85/Formal-Verification-of-Programming-Languages-24-320.jpg)
![Motivation 1960s Proof 1970s 1980s 1990s 2000s Conclusions
Open questions
What about compilers for larger target languages and more
advanced compilation facilities?
Are our mechanised assistants producing valid proofs?
Are there other ways to decompose the problem?
Are particular language paradigms more amenable to compiler
verification?
Why haven’t the concepts of [Meijer94] been more widely
used?
What other ways are there of decomposing the compiler
verification problem?](https://image.slidesharecdn.com/litsem-100111105344-phpapp02/85/Formal-Verification-of-Programming-Languages-26-320.jpg)