Flirt Overview
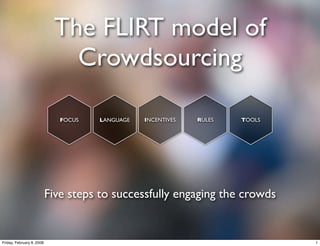
- 1. The FLIRT model of Crowdsourcing FOCUS LANGUAGE INCENTIVES RULES TOOLS Five steps to successfully engaging the crowds Friday, February 8, 2008 1
- 2. Company Perspective Customer Perspective FOCUS WHAT? Strategic WHY? WHAT? LANGUAGE WHY? Tactical INCENTIVES HOW? RULES HOW? Technical TOOLS Friday, February 8, 2008 2
- 3. Creation & IP transfer Creation & Platform Interaction & Legal Sharing Scale of Customers/ Monitoring & Initiation RULES TOOLS Activity Participants Action Business Depth of FOCUS Objectives Activity Extrinsic Area of Organization Social INCENTIVES LANGUAGE Objective Activity Capabilities Objects Extrinsic Organization Social Intrinsic Presence Interaction Subjective Friday, February 8, 2008 3
- 4. Creation & IP transfer Tools of Platform Interaction & Legal Creation Scale of Customers/ Tools for the Initiation RULES TOOLS Activity Participants Company Business Depth of FOCUS Objectives Activity Extrinsic Area of Organization Social INCENTIVES LANGUAGE Objective Activity Capabilities Objects Extrinsic Organization Nature of Intrinsic Presence Interaction Subjective Friday, February 8, 2008 4
- 5. Focus consists of six subelements • Business objectives • Scope of activity • Customer participants • Scale of activity • Organization Capabilities • Depth of activity These non-negotiable determinants These negotiable determinants are are to be taken into account as used to define the planned given when defining activity. crowdsourcing activity on a rough scale. In the long run also these determinants become negotiable. When defining these three elements, they need to be reflected on each of the constraints - as follows... Friday, February 8, 2008 5
- 6. Focus Scope Scale Depth Answers Added cost Business Customer Customer Customer central vs. economies benefits exceed Participants Participants Participants business needs? of scale? added risk? Suitable Manageable Significance of Business Scope of Business Scale of Business Depth of for ‘human’ by the control and Objectives Activity Objectives Activity Objectives Activity systems? people? access sufficient? Respective Support for Organization resources Organization scaling across Organization Organization able to bear and committed Capabilities organizational Capabilities Capabilities manage risk? and capable? borders? Friday, February 8, 2008 6
- 7. Creation & IP transfer Tools of Platform Interaction & Legal Creation Scale of Customers/ Tools for the Initiation RULES TOOLS Activity Participants Company Business Depth of FOCUS Objectives Activity Extrinsic Area of Organization Social INCENTIVES LANGUAGE Objective Activity Capabilities Objects Extrinsic Organization Social Intrinsic Presence Interaction Subjective Friday, February 8, 2008 7
- 8. Language • Social Objects • The “social glue” of the community: why people talk to these people/this company instead of talking to other people/other companies • Not scope as in Focus element but instead the medium via which to sell the scope of the company to the people • In order for the community to thrive, these social objects need to be playable and able to activate people • Social Interaction • The nature of interaction around the social objects, focus on: • Identity • Presence • Relationships • Conversations • Grouping • Reputation • Sharing • Company Presence • Authenticity • Transparency • Human Face / Community Management Friday, February 8, 2008 8
- 9. Creation & IP transfer Tools of Platform Interaction & Legal Creation Scale of Customers/ Tools for the Initiation RULES TOOLS Activity Participants Company Business Depth of FOCUS Objectives Activity Extrinsic Area of Organization Social INCENTIVES LANGUAGE Objective Activity Capabilities Objects Extrinsic Organization Nature of Intrinsic Presence Interaction Subjective Friday, February 8, 2008 9
- 10. Incentives • Intrinsic incentives • Related to the reward from simply undertaking activity, e.g. • Self Efficacy • Learning from doing • Challenge • Satisfying need for creativity • Obligation • Extrinsic subjective incentives • Related to the reward of undertaking activity as part of community / for an organization, e.g. • Peer recognition • Company recognition • Learning from others • Exposure • Reputation • Social Capital • Exclusivity (channels / resources) • Extrinsic objective incentives • Explicit rewards, have direct monetary value, e.g. • Products • Services • Gift cards • Subscriptions • Cash Friday, February 8, 2008 10
- 11. Creation & IP transfer Tools of Platform Creation and Interaction & Legal Sharing Scale of Customers/ Tools for the Initiation RULES TOOLS Activity Participants Company Business Depth of FOCUS Objectives Activity Extrinsic Area of Organization Social INCENTIVES LANGUAGE Objective Activity Capabilities Objects Extrinsic Organization Nature of Intrinsic Presence Interaction Subjective Friday, February 8, 2008 11
- 12. Rules • Initiation • Open or closed? • Screening protocols? • Personal info required? • Creation • Quality constraints • Format constraints • Manufacturing constraints • Arbitrary constraints • Deadlines • Criteria of Approval • Other constraints • Interaction • Seeing others ideas • Building on others ideas • Remixing / mashing up • IP & Legal • IP transfer • Copyright issues • Responsibility releases Friday, February 8, 2008 12
- 13. Creation & IP transfer Creation & Platform Interaction & Legal Sharing Scale of Customers/ Monitoring & Initiation RULES TOOLS Activity Participants Action Business Depth of FOCUS Objectives Activity Extrinsic Area of Organization Social INCENTIVES LANGUAGE Objective Activity Capabilities Objects Extrinsic Organization Nature of Intrinsic Presence Interaction Subjective Friday, February 8, 2008 13
- 14. Tools • Platform • Identity • profile pages and customization tools • proprietary • Presence • 3rd party • presence indicators • hybrid • location indicators • Creation • nearness indicators • web tools • Relationships • social network (binary) • downloadable software / client • social graph (typological) • 3rd party • Conversations • physical tools • IM • Interaction • IRC • Monitoring • Forum • Grouping • Technology / algorithm • groups • Pre-moderation • applications • Post-moderation • Reputation • Customer input • ranking lists • average rating • Action • Sharing • Taking the ideas into the process within the • Within community (tagging, sending, recommending) company • Outside (embeds, links, social bookmarking services other means) Friday, February 8, 2008 14
- 15. CREATORS CRITICS content to scrutinize critique & support co opinions & viewpoints nt increased exposure en t content to share co en tt expert status lle nt o ts ct co in ive po ed ew at eg vi ev gr & al ns ag u a ent io ju te in dg op m aggregated content audience & readership CONNECTORS CROWDS Friday, February 8, 2008 15
- 16. FOCUS LANGUAGE INCENTIVES RULES TOOLS Friday, February 8, 2008 16
