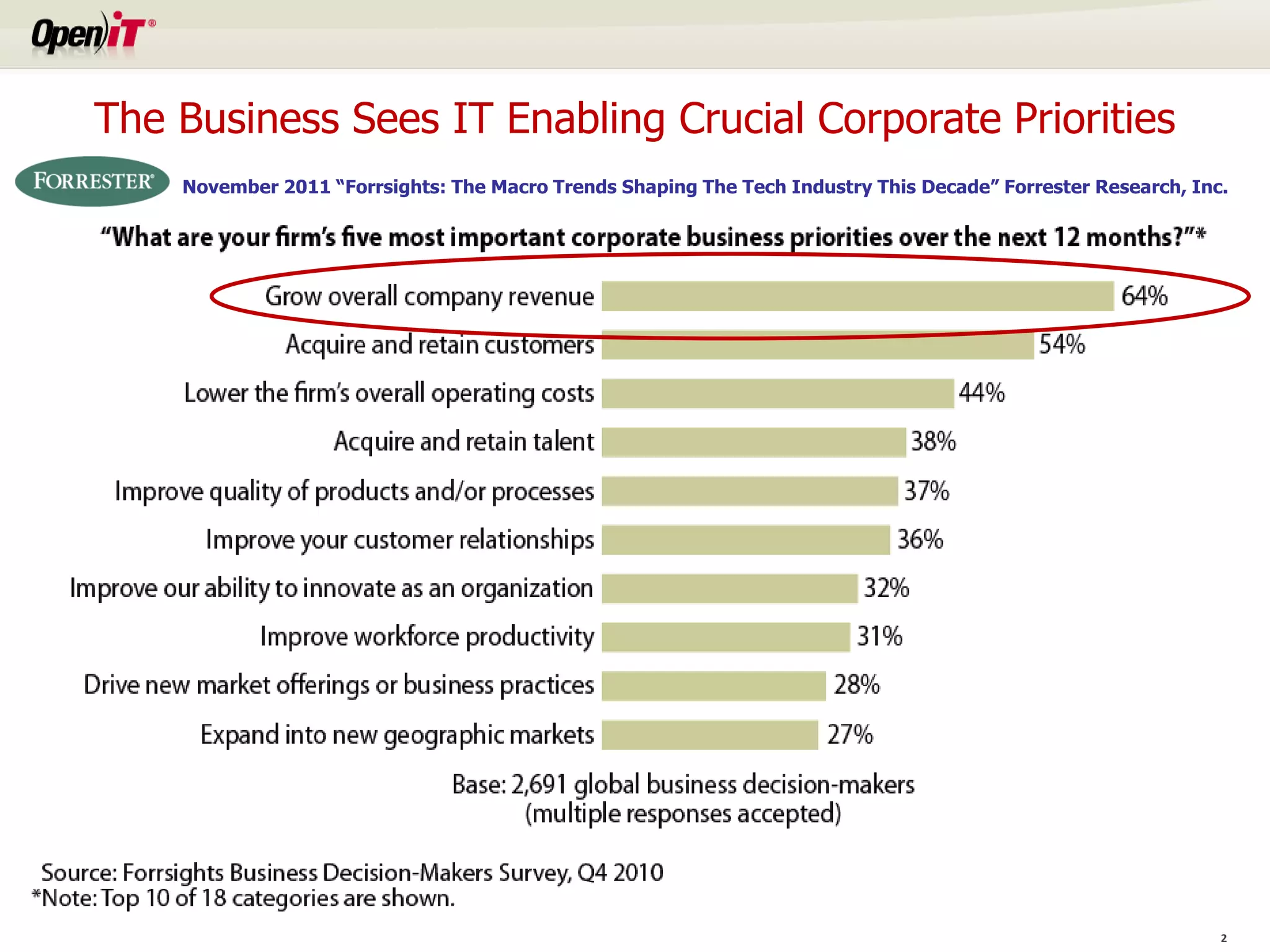
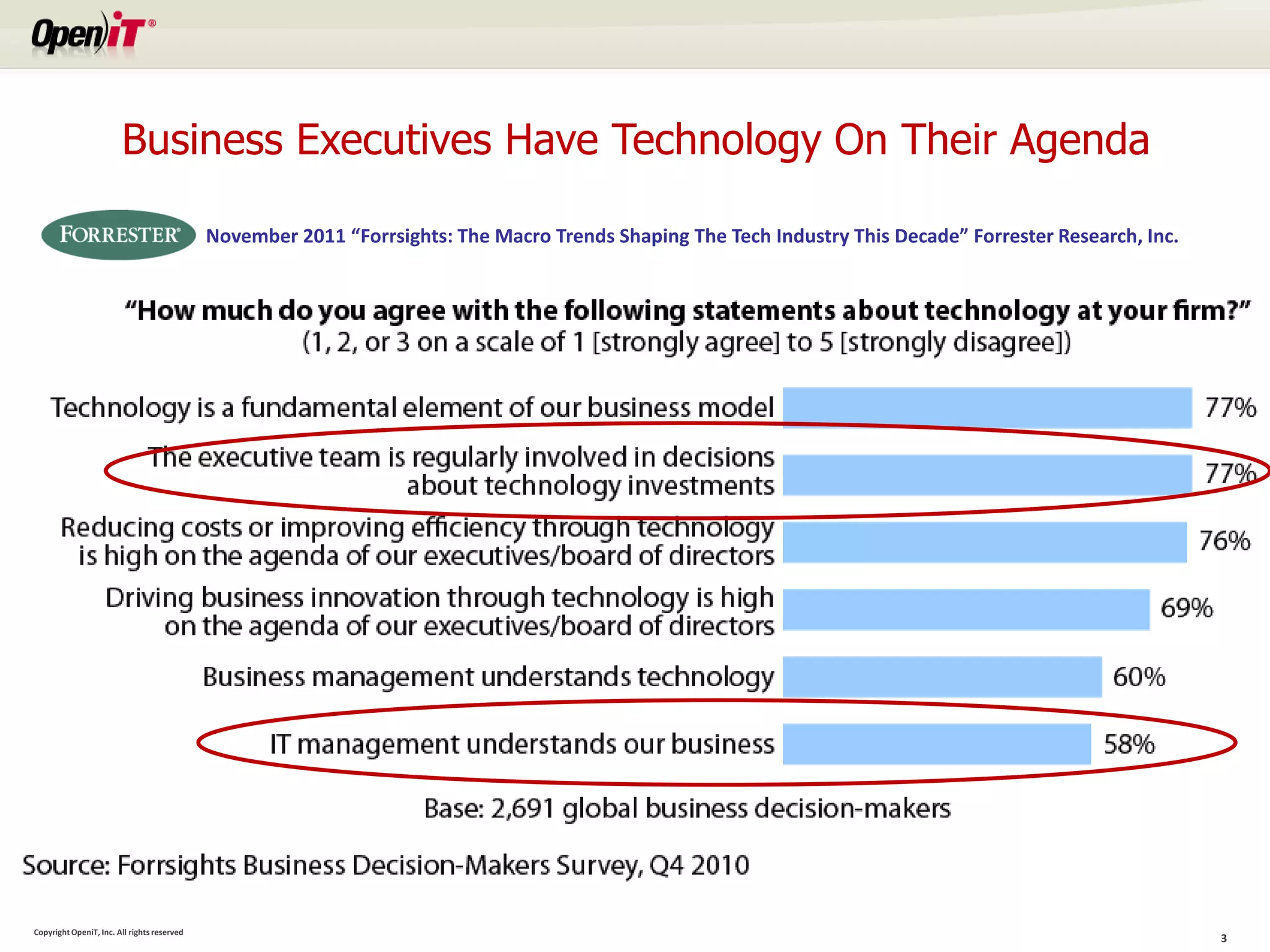
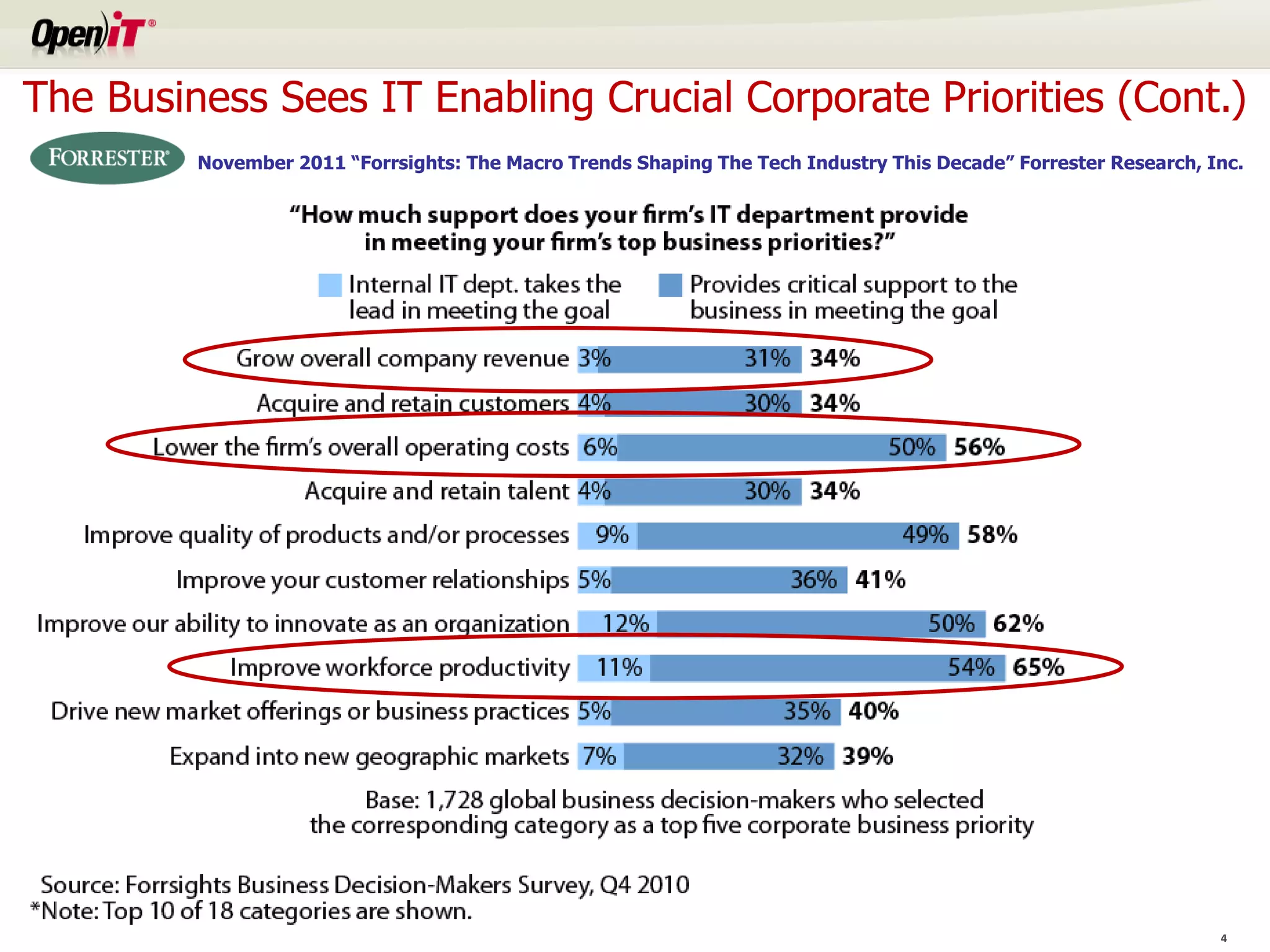
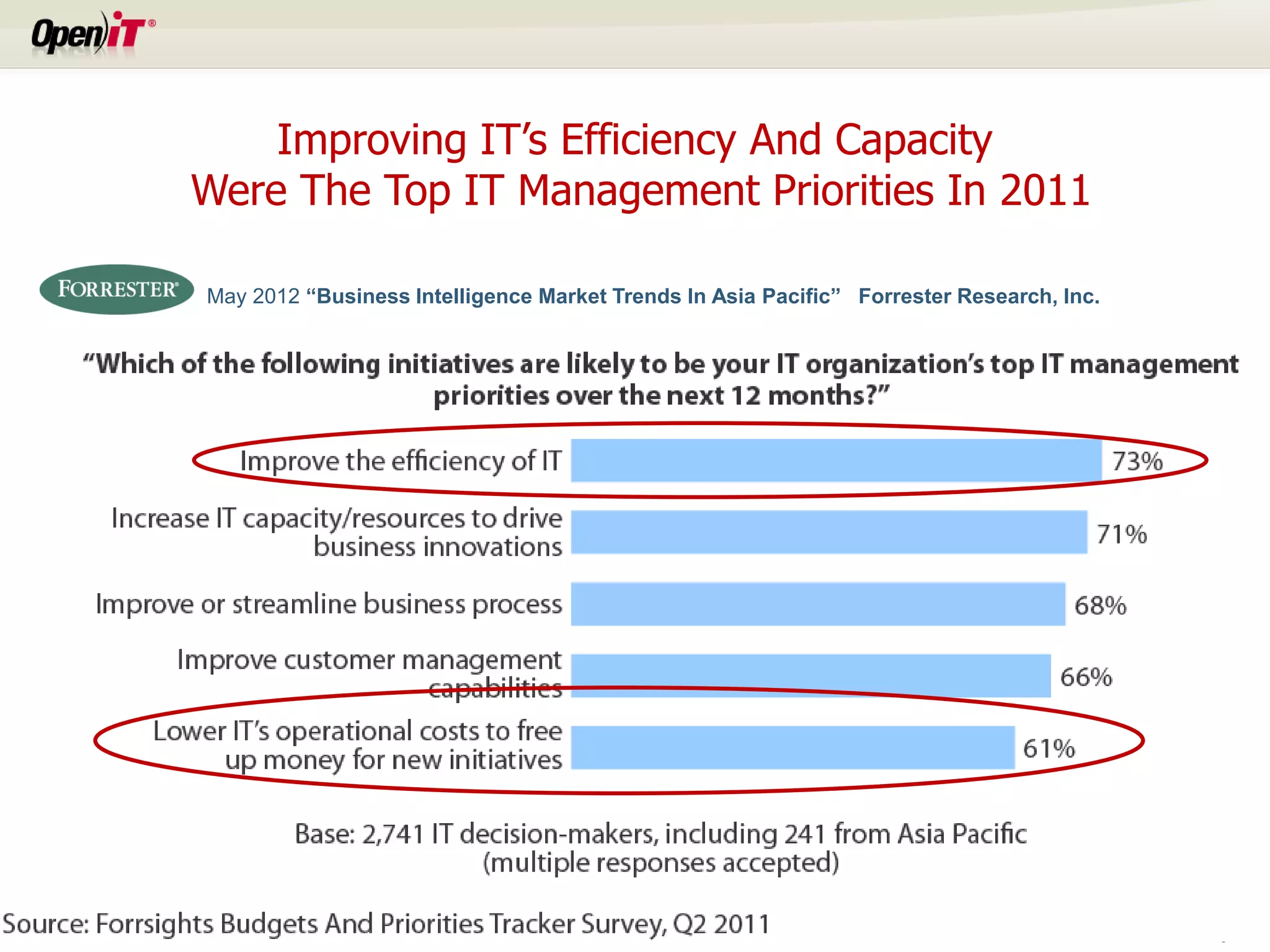
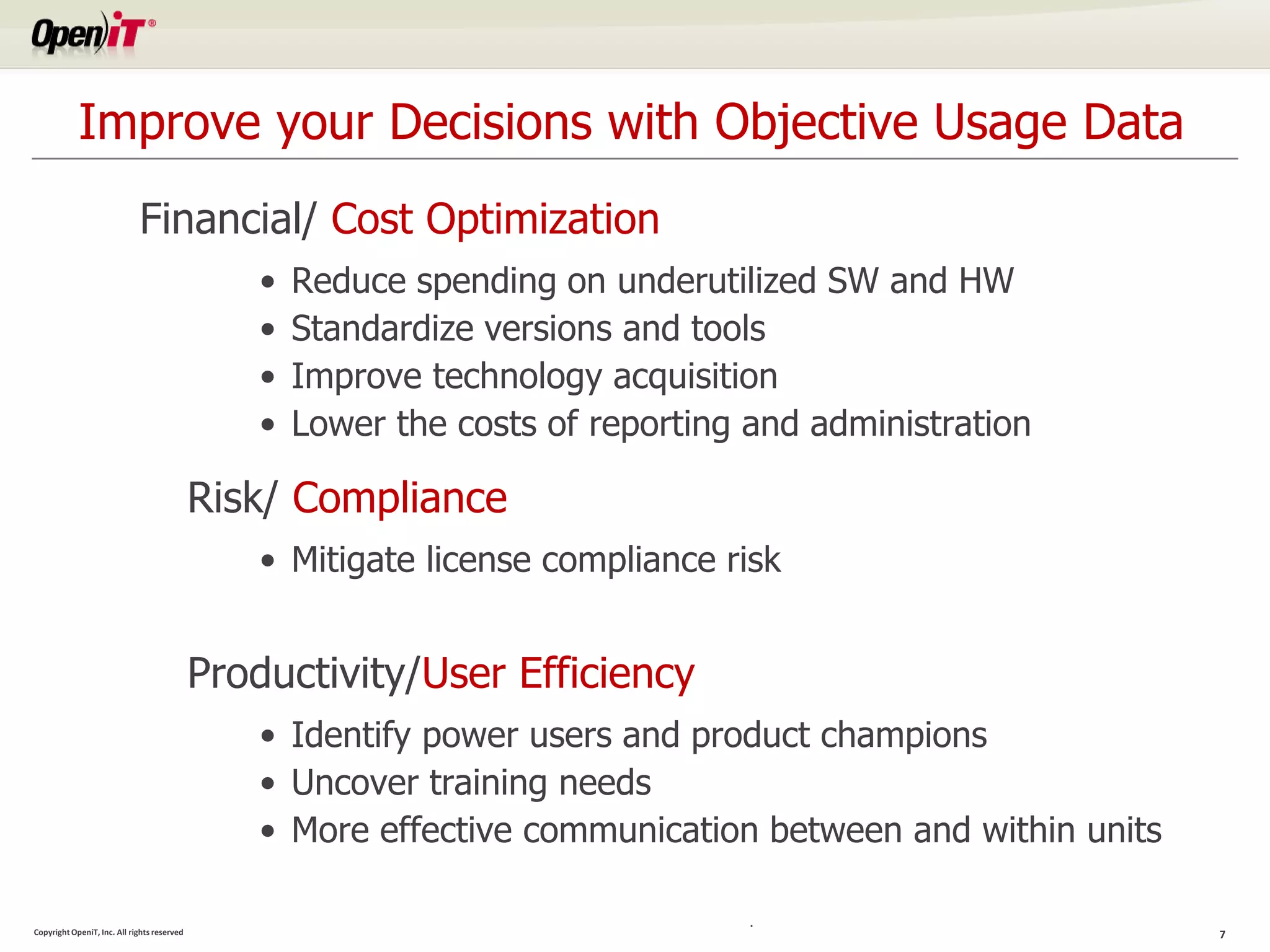
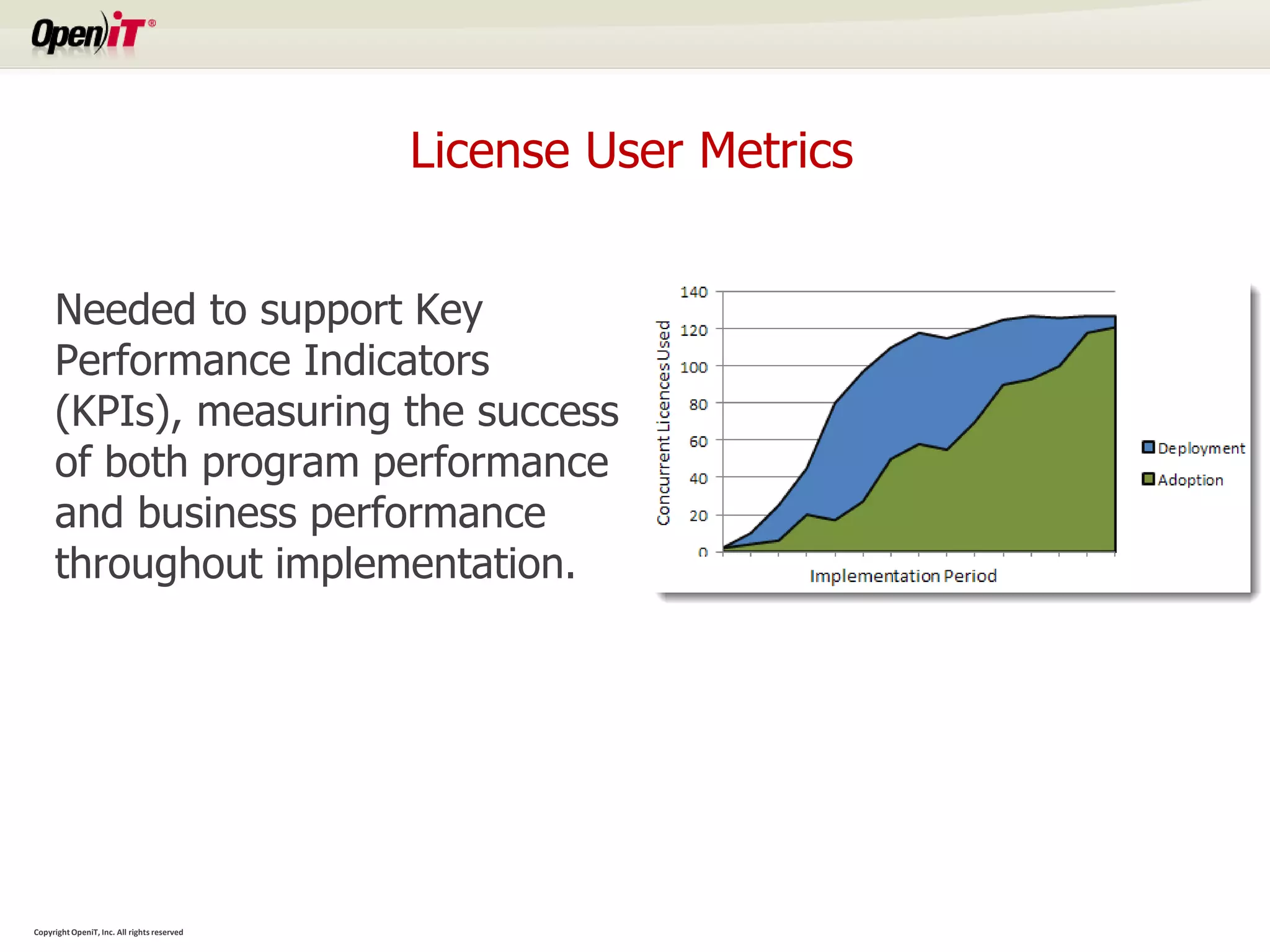
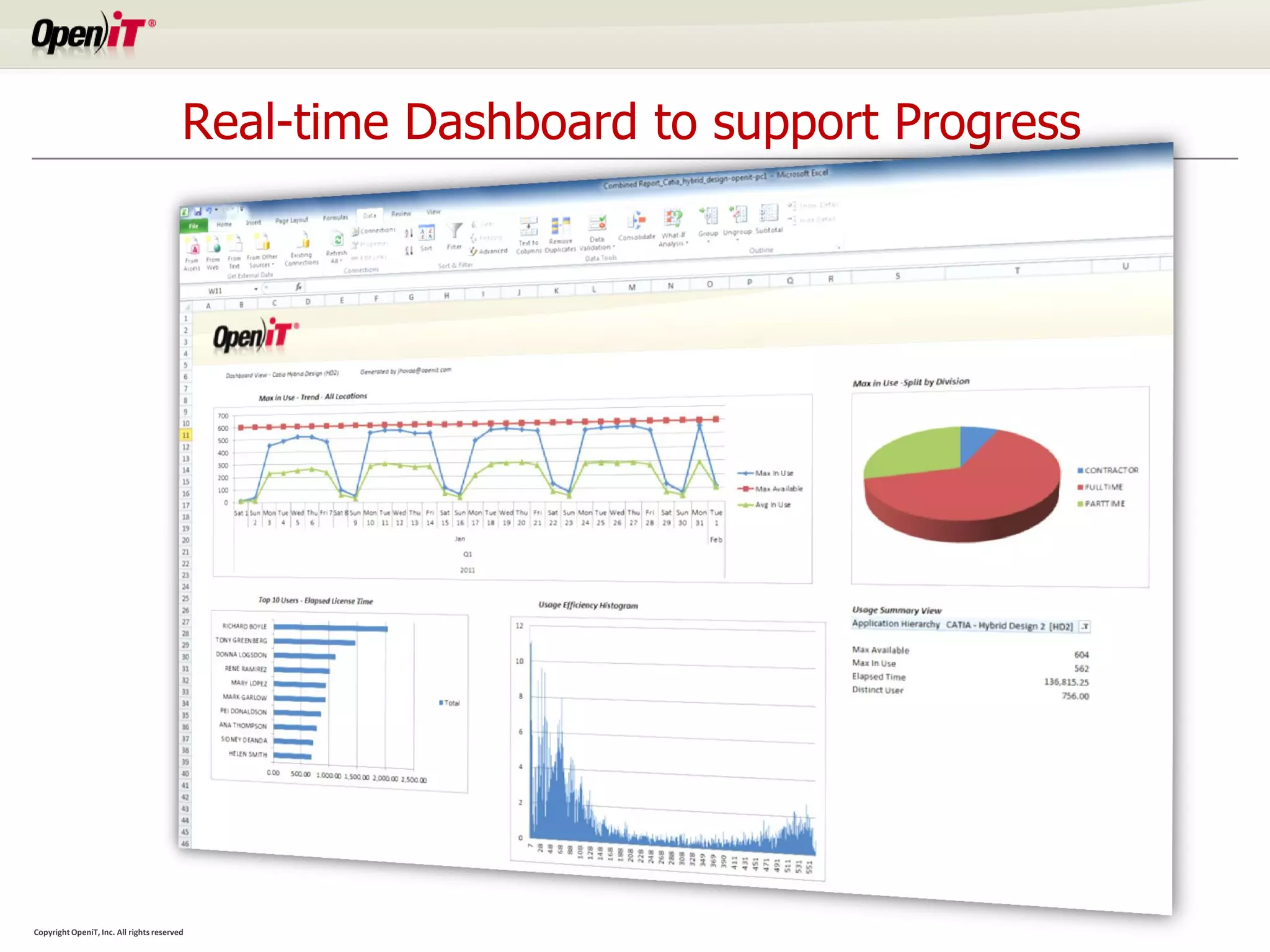
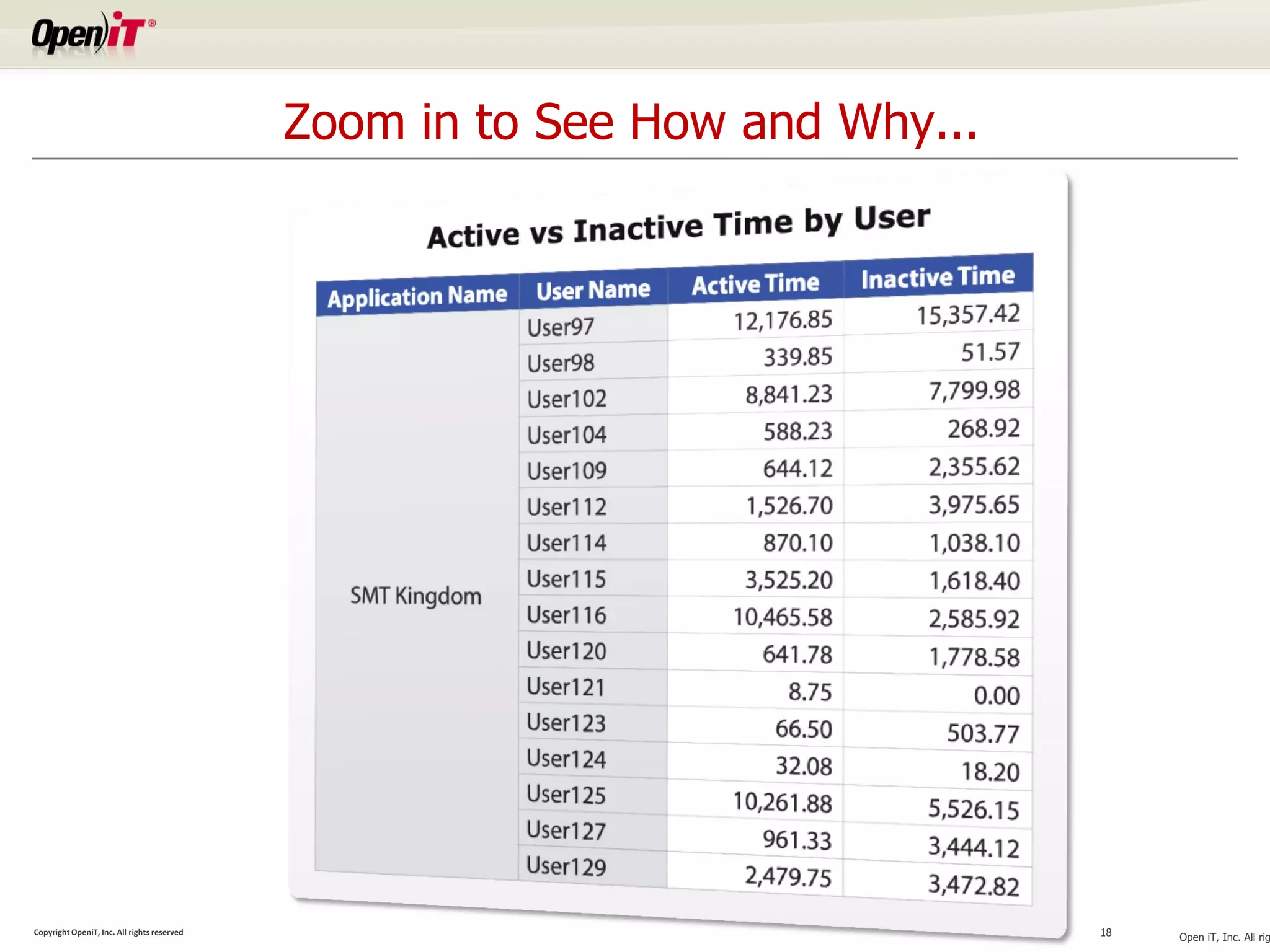
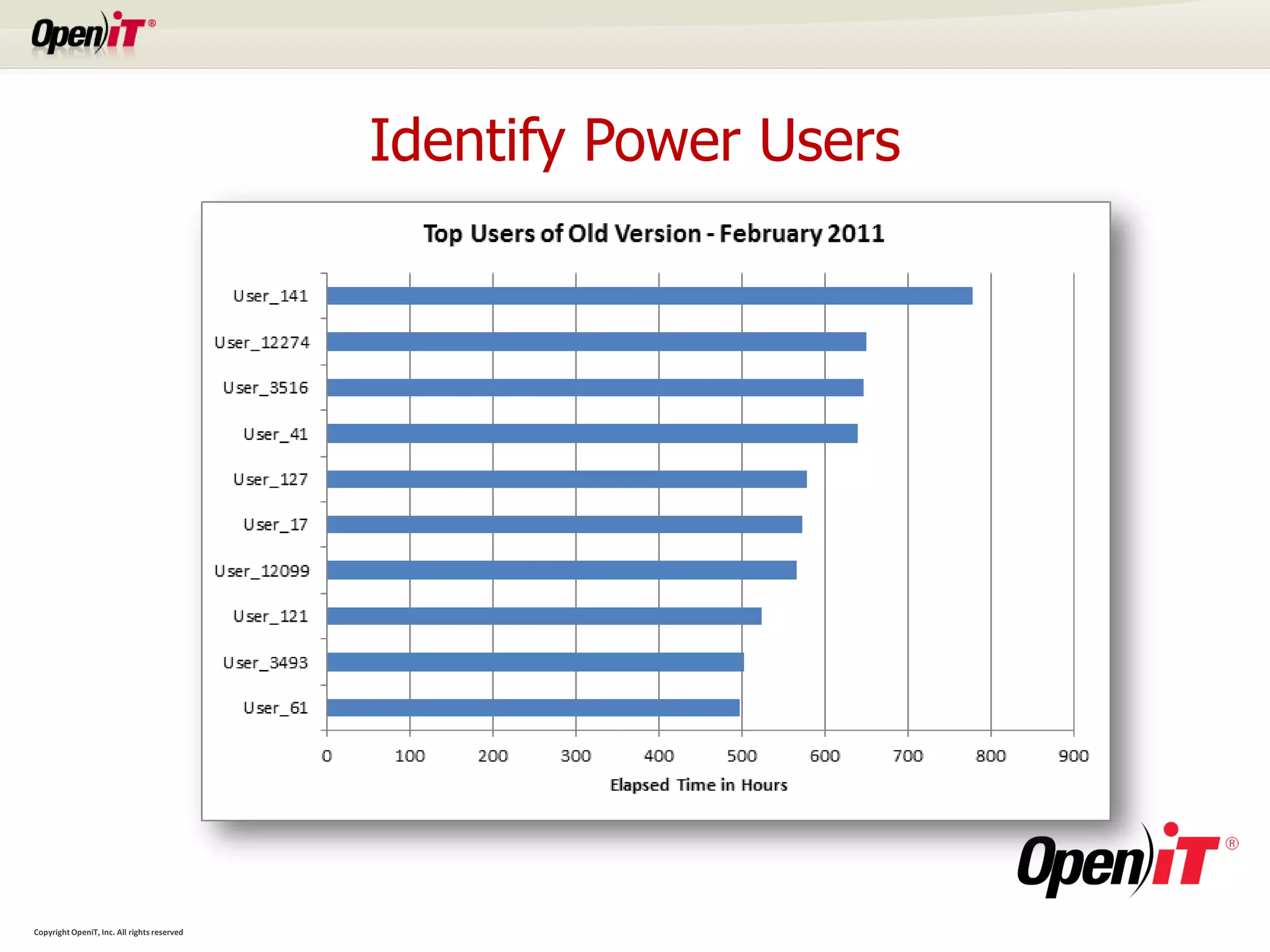
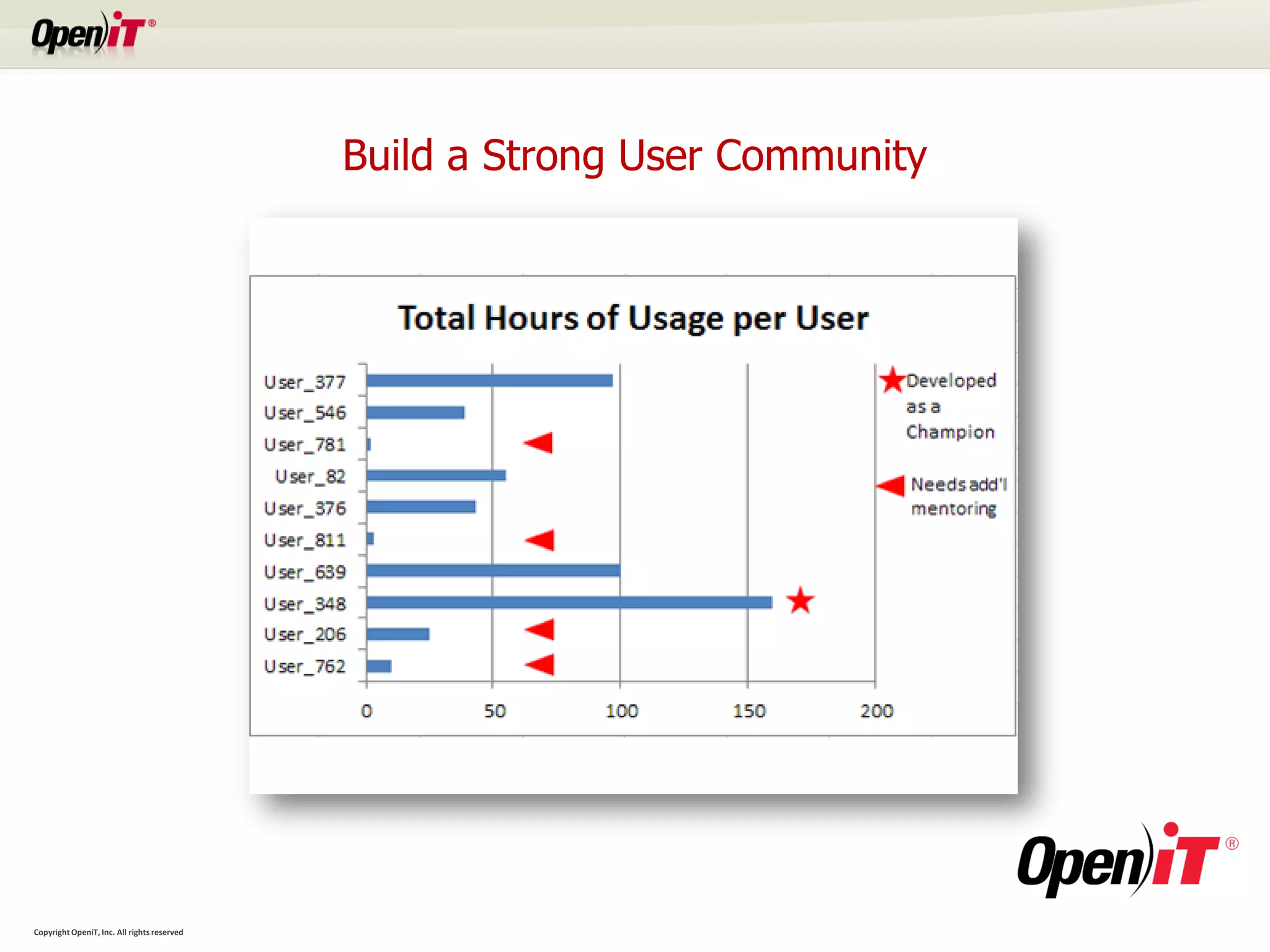
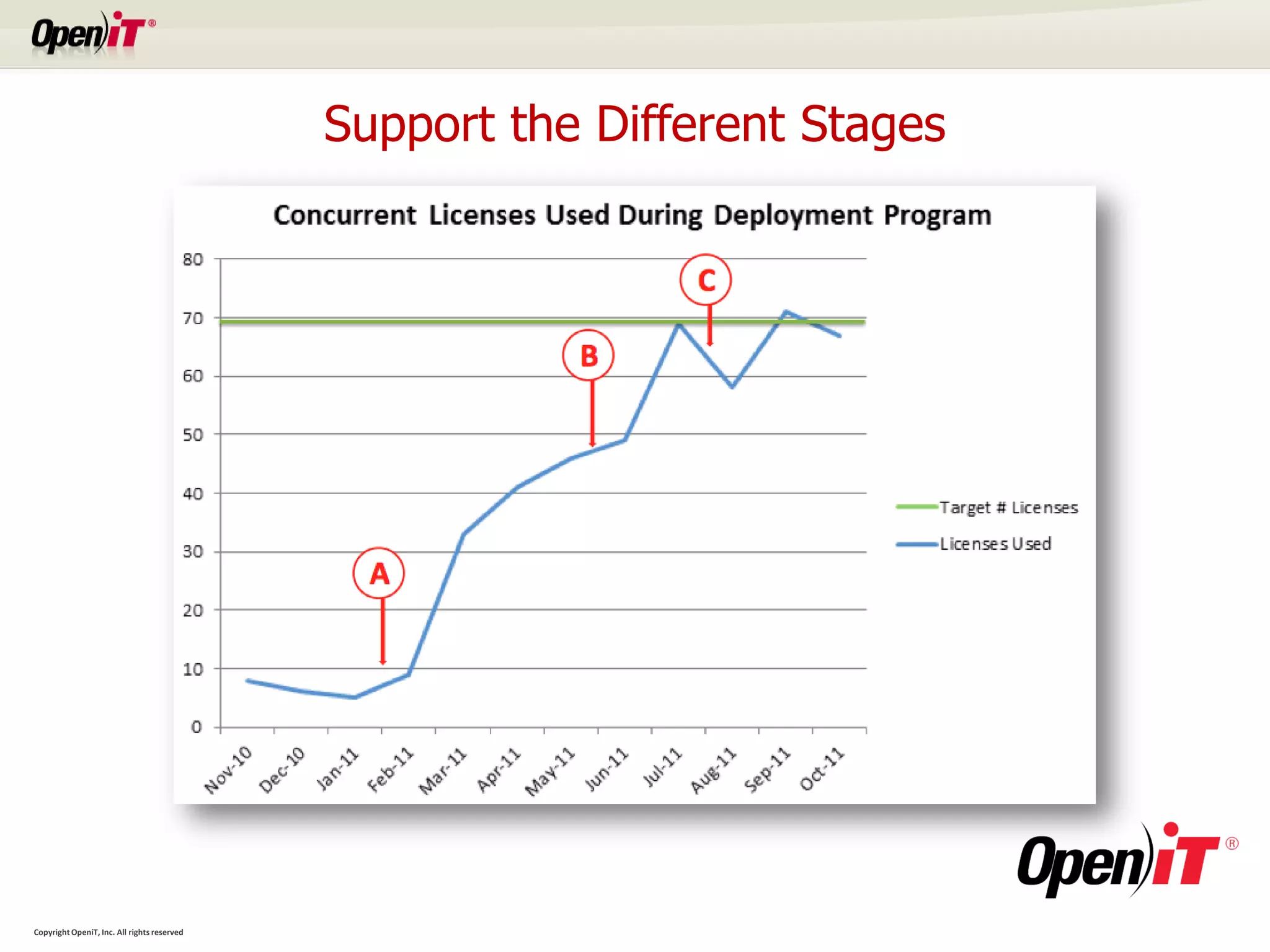
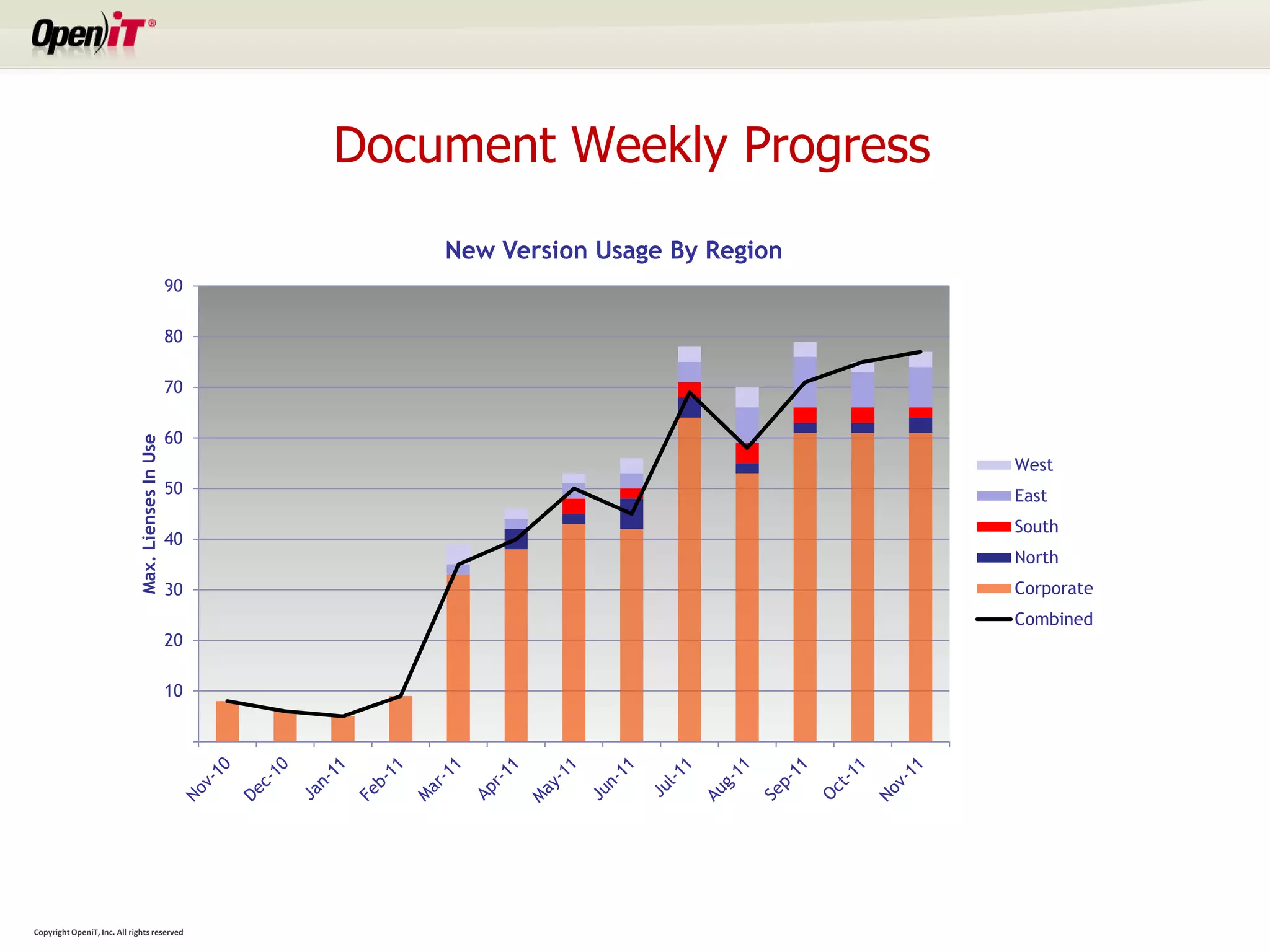
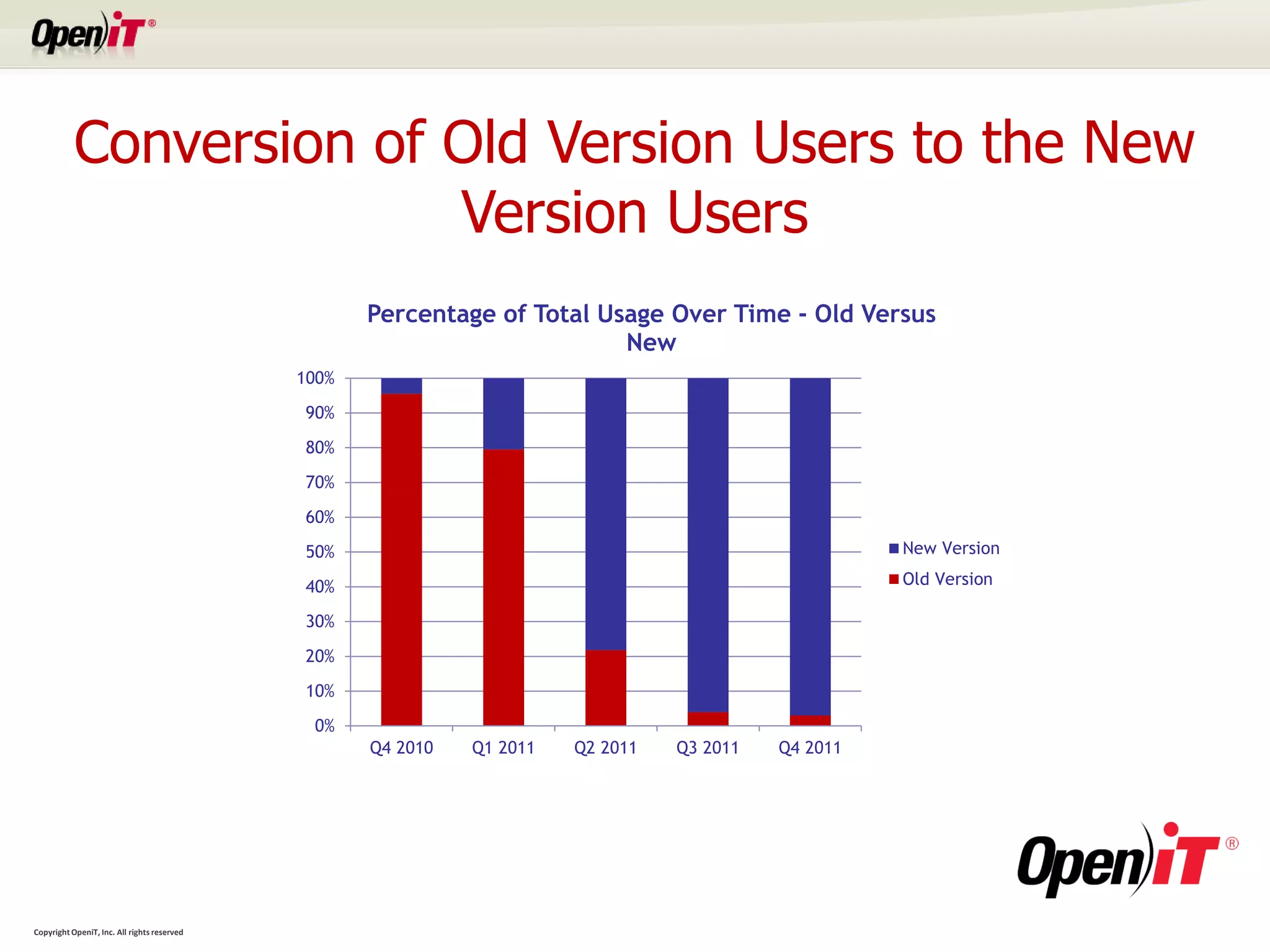
The document discusses how software usage metering can help organizations optimize technology investments and improve user productivity during enterprise software implementations. Key points include identifying underutilized software, standardizing versions, measuring adoption metrics, and reducing productivity losses during the transition to new technologies. Usage data provides insights to support strategic decisions and monitor implementation progress.