Windows Firewall.ppt
•Download as PPTX, PDF•
0 likes•614 views
semoga bermanfaat ...
Report
Share
Report
Share
Recommended
The Internet: All about the Internet

a presentation on what is the Internet, how it works, the creation of the internet, history of the internet, and the Uses of the internet. what is it? Discover the internet. find out its history and its uses.
Network Analysis Mini Project 2.pdf

Network traffic analysis is used to monitor network activity and identify anomalies that could indicate security or performance issues. It allows analysis of traffic patterns and protocols to troubleshoot problems, detect malware, and trace attacks. Choosing a network traffic analysis solution requires considering the data sources and network points to monitor, as well as whether full packet capture or flow-based analysis is needed. Network traffic analysis is an important part of network visibility and security.
Introduction to php web programming - sessions and cookies

Introduction to php web programming - sessions and cookiesbaabtra.com - No. 1 supplier of quality freshers
This document discusses cookies and sessions in PHP. Cookies are used to maintain state between HTTP requests and can store a small amount of text data in the user's browser. Sessions serve the same purpose as cookies but store data on the server rather than in the browser. The document demonstrates how to create, access, and destroy both cookies and sessions in PHP code. It also compares the key differences between cookies and sessions, such as cookies persisting after the browser closes while sessions do not. Web browser

This document discusses different web browsers. It defines a web browser as software that acts as an interface between users and web servers to locate and display web pages. The main components of web browsers are the user interface and rendering engine. Some popular browsers mentioned are Google Chrome, Mozilla Firefox, Internet Explorer, Opera, and Safari. Brief histories and release dates are provided for each.
Internet features (2nd topic)

The document provides an overview of key Internet and World Wide Web technologies including:
- The Internet provides global access to communication services and information through tools like email, chat, newsgroups, and file transfer.
- The World Wide Web consists of web pages containing text and images linked through hyperlinks. Collections of linked pages on a common topic form a website.
- Hypertext links allow users to navigate between related pages of information. HTML codes format web pages for display in web browsers which retrieve and present web resources.
- Major technologies include browsers like Firefox and Internet Explorer, HTTP for transferring files between servers and clients, and web servers which process HTTP requests and host websites and web pages.
Web servers – features, installation and configuration

A web server is a computer program and server that allows for hosting of websites and web applications. It accepts requests from browsers and returns HTML documents and other content. Common technologies used on web servers include CGI scripts, SSL security, and ASP to provide dynamic content and server-side processing. Web servers work by accepting connections from browsers, retrieving content from disk, running local programs, and transmitting data back to clients as quickly as possible while supporting threads and processes.
Jsp lifecycle

The document describes the lifecycle of a JSP page, which includes compilation, initialization, execution, and cleanup. During compilation, the JSP engine checks if the page needs to be compiled or recompiled. Initialization involves calling the jspInit() method. Execution handles requests by calling the _jspService() method. Finally, cleanup occurs when the page is removed, calling the jspDestroy() method.
Recommended
The Internet: All about the Internet

a presentation on what is the Internet, how it works, the creation of the internet, history of the internet, and the Uses of the internet. what is it? Discover the internet. find out its history and its uses.
Network Analysis Mini Project 2.pdf

Network traffic analysis is used to monitor network activity and identify anomalies that could indicate security or performance issues. It allows analysis of traffic patterns and protocols to troubleshoot problems, detect malware, and trace attacks. Choosing a network traffic analysis solution requires considering the data sources and network points to monitor, as well as whether full packet capture or flow-based analysis is needed. Network traffic analysis is an important part of network visibility and security.
Introduction to php web programming - sessions and cookies

Introduction to php web programming - sessions and cookiesbaabtra.com - No. 1 supplier of quality freshers
This document discusses cookies and sessions in PHP. Cookies are used to maintain state between HTTP requests and can store a small amount of text data in the user's browser. Sessions serve the same purpose as cookies but store data on the server rather than in the browser. The document demonstrates how to create, access, and destroy both cookies and sessions in PHP code. It also compares the key differences between cookies and sessions, such as cookies persisting after the browser closes while sessions do not. Web browser

This document discusses different web browsers. It defines a web browser as software that acts as an interface between users and web servers to locate and display web pages. The main components of web browsers are the user interface and rendering engine. Some popular browsers mentioned are Google Chrome, Mozilla Firefox, Internet Explorer, Opera, and Safari. Brief histories and release dates are provided for each.
Internet features (2nd topic)

The document provides an overview of key Internet and World Wide Web technologies including:
- The Internet provides global access to communication services and information through tools like email, chat, newsgroups, and file transfer.
- The World Wide Web consists of web pages containing text and images linked through hyperlinks. Collections of linked pages on a common topic form a website.
- Hypertext links allow users to navigate between related pages of information. HTML codes format web pages for display in web browsers which retrieve and present web resources.
- Major technologies include browsers like Firefox and Internet Explorer, HTTP for transferring files between servers and clients, and web servers which process HTTP requests and host websites and web pages.
Web servers – features, installation and configuration

A web server is a computer program and server that allows for hosting of websites and web applications. It accepts requests from browsers and returns HTML documents and other content. Common technologies used on web servers include CGI scripts, SSL security, and ASP to provide dynamic content and server-side processing. Web servers work by accepting connections from browsers, retrieving content from disk, running local programs, and transmitting data back to clients as quickly as possible while supporting threads and processes.
Jsp lifecycle

The document describes the lifecycle of a JSP page, which includes compilation, initialization, execution, and cleanup. During compilation, the JSP engine checks if the page needs to be compiled or recompiled. Initialization involves calling the jspInit() method. Execution handles requests by calling the _jspService() method. Finally, cleanup occurs when the page is removed, calling the jspDestroy() method.
Types of websites 

The document describes 12 different types of websites: educational websites, online social networks, web portals, blogs, content aggregators, business/marketing websites, wikis, advocacy websites, news websites, entertainment websites, informational websites, and personal websites. For each type, 1-3 examples are provided and briefly described. The document was created by 6 authors for a class assignment.
Computer Security and Ethics

This document discusses various common security risks and threats to computers and networks. It covers topics like malware, viruses, spam, spoofing, phishing, botnets, worms, Trojans, backdoors, blended threats, denial of service attacks, and physical threats like hardware theft and vandalism. It also discusses prevention, detection and removal strategies for many of these threats. Passwords, antivirus software, firewalls and regular backups are recommended for protection. The document provides examples of weak versus strong passwords. It cautions that most malware is spread through the internet.
The internet

The document discusses various aspects of the internet including:
- The internet connects millions of websites and servers through an interconnected network.
- It allows people to communicate and share information globally through email, files, videos and more.
- The world wide web was created in 1990 by Tim Berners-Lee and allows webpages to be accessed through browsers and hyperlinks.
- Key components of the internet include URLs, domains, folders, files, protocols, browsers, and web servers.
- There are different categories of websites including news, education, business, entertainment and personal websites.
Computer viruses

Computer viruses have existed since the late 1980s, beginning with the Brain virus created in Pakistan in 1986. Viruses spread primarily through floppy disks in the early years. Over time, viruses increased in sophistication and ability to spread over networks and email. Some notable early viruses include Michelangelo in 1991, which overwrote data on March 6th, and ILOVEYOU in 2000, one of the first major email viruses. Viruses continue to evolve with different transmission methods as technology changes.
Network Security Nmap N Nessus

This document summarizes different types of network scans that can be performed using Nmap, including TCP connect scans, SYN scans, FIN scans, Xmas scans, Null scans, and least traffic scans. It also discusses why vulnerability scanning is important and compares the features of the free Nessus Home Feed versus the paid Professional Feed for vulnerability scanning. The Professional Feed provides more frequent plugin updates, policy compliance checks, unlimited PCI audits, operating system audits, and technical support compared to the free Home Feed.
Maltego Webinar Slides

Please view our webinar to learn the basics of our Maltego integration. https://attendee.gotowebinar.com/recording/2960337559231715841
Malformity Labs has developed a full transform set that allows for data from ThreatConnect™ to be integrated with the capabilities of Maltego.
All ThreatConnect customers can take advantage of the Maltego transform set through the ThreatConnect™ API and a provided transform server. They can use this to:
• Visualize the relationship between incidents, threats, adversaries, and indicators,
• Leverage attributes belonging to indicators and threats to create Maltego Graphs without losing any of the contextual data within ThreatConnect, and
• Pivot from ThreatConnect data and external open source data sources using other transform sets within Maltego.
Web browsers and web servers

Web browsers allow users to access and view webpages. Examples of popular web browsers include Mozilla Firefox, Google Chrome, Internet Explorer, Opera, and Safari. Mobile browsers are optimized for small screens on portable devices and include micro browsers, mini browsers, and mobile browsers. A web server stores web pages and uses HTTP to serve files that make up web pages to users in response to their requests.
ASP.NET 08 - Data Binding And Representation

This document discusses different ways to represent and bind data in ASP.NET applications. It covers data binding controls to data sources, using .NET collections like ArrayList and Dictionary to store data, using generic collections, populating and using DataTable and DataSet objects to store and manipulate tabular data, and integrating data with XML.
Success in decision making data relevance curation

Success in decision making data relevance curationUS Environmental Protection Agency (EPA), Center for Computational Toxicology and Exposure
This presentation was given at the ToxForum 2023 Winter Meeting in the session regarding Life Cycle Impact Assessment: LCIAs are increasingly being utilized within Life Cycle Assessments (LCA) to attempt to quantify impacts to human health, among other impacts, and ultimately compare products or processes. This session will provide the audience with an overview of LCIA, specifically outlining how toxicology data are utilized in LCIA human health impact calculations. Further, our speakers will delve into the nuances related to the interpretation of LCIA human health outputs and how they compare to information obtained via a risk assessment (RA) approach. Toxicology data are key to these newly emerging efforts to characterize total human health impact. Therefore, panelists will be asked to consider new trends in toxicology, data sources, and or approaches that may help to better inform a calculation of human health impact along with appropriate domains of applicability fostering a discussion relevant to regulators, academics and those in application industries. Usage of internet

The document provides an overview of the internet including its history, common uses, and key features. It explains that the internet is a global network connecting billions of electronic devices that allows people to access and share information worldwide. A brief history outlines how it began in the late 1950s and became publicly available in the 1980s before the development of the World Wide Web in 1991 accelerated its expansion. Common uses of the internet described include email, searching for information online, shopping, watching videos and listening to music, and connecting on social media.
UNIX Operating System ppt

The document provides an overview of the UNIX operating system through a seminar presentation. It discusses the history of UNIX from the 1970s to the 2000s, defines what UNIX is, describes common UNIX commands and the file system structure, and covers topics like memory management, interrupts, reasons for using UNIX, and some applications of UNIX like storage consulting and middleware/database administration. The presentation is intended to educate about the key aspects and functionality of the UNIX operating system.
Internet & Email & collaborative Computing & Social Networking by Abeer Ali 👍...

This document discusses internet, email, social networking, and collaborative computing. It begins by defining the internet and how it works by connecting computers globally. It then discusses uses of the internet like accessing information and conducting business. The history and development of the internet and protocols like TCP/IP are described. Email is introduced as a way to send electronic messages over the internet. Social networking allows people to build online communities and interact through sites like Facebook and LinkedIn. Collaborative computing uses technology like messaging and file sharing to enable groups to work together remotely. Benefits include increased productivity, efficiency, and understanding diverse perspectives.
Network monitoring tools

Microsoft Network Monitor is a tool for viewing network packet contents that are being sent and received over a live network or from a captured file. It provides filtering options and can capture traffic to/from its own interface or, in an enhanced version, all network traffic. OpenNMS is an open source network management system that can monitor tens of thousands of devices from a single server or unlimited devices using a cluster. It includes discovery, event management, service assurance, and performance measurement. Capsa is a free network management solution that integrates traffic capture, analysis, fault diagnosis, and performance evaluation to help troubleshoot, secure, and optimize networks.
3 definition of operating systems

The document defines operating systems and describes their basic components and functions. It discusses how operating systems provide an interface between hardware and software, manage system resources, and allow for the execution of user programs. The goals of an operating system are to provide convenience for users and efficient operation of the computer system. An operating system is a type of system software that coordinates hardware and software and controls and allocates resources.
Web Mining

This document provides an overview of web mining and summarizes key concepts. It begins with definitions of data mining and web mining. The document then discusses three categories of web mining: web content mining, web usage mining, and web structure mining. Various matrix expressions used to represent web data are also introduced, including document-keyword co-occurrence matrices, adjacent matrices, and usage matrices. Finally, two common similarity functions - Pearson correlation coefficient and cosine similarity - are outlined.
Joomla

Joomla is a popular open source content management system (CMS) that allows users to manage and organize content on a website without needing technical skills. It uses a simple architecture that separates the user interface from the business logic and data layers. Content is added and managed through a web-based administration panel. Joomla is commonly used for corporate websites, online magazines, e-commerce sites, and other applications. It provides features like user management, content organization, templates, and media management. To use Joomla, a server is needed that meets the minimum requirements of PHP, MySQL, and Apache. New sites can be created by downloading and installing Joomla through a simple process.
3. interface scratch

Dokumen ini memberikan penjelasan tentang interface Scratch yang terdiri dari beberapa bagian utama seperti toolbar, tab block, area script, block costumes, dan block sounds. Area script digunakan untuk mengatur blok-blok perintah yang akan dieksekusi sprite. Terdapat tiga jenis blok perintah yaitu stack block, hats, dan reporters. [/ringkasan]
User management

This document provides information on managing users and groups in Linux. It lists commands for adding, modifying, and deleting users and groups such as useradd, usermod, userdel, and groupadd. It describes how user information is stored in files like /etc/passwd, /etc/shadow, and /etc/group. It also covers setting passwords, restricting login access, giving users root privileges, and managing secondary groups. Potential error scenarios involving permissions and viewing passwords are also addressed.
Politics the Wellstone Way

This document introduces Wellstone Action, a community organizing group that trains people in leadership and organizing skills. It highlights that Wellstone Action has trained over 32,000 people in 45 states since 2004 to win progressive change through hundreds of organizations. The document also outlines Wellstone Action's model for building long-term power through an agenda, growth, and politics, including developing new leaders, community organizing, and electoral politics to determine decision-makers and hold them accountable.
Cookies & Session

Cookies are small pieces of data stored in a user's browser that are sent back to the server with requests. They allow servers to remember stateful information about users, like items in a shopping cart. Sessions use a unique identifier to store server-side data associated with each user, like login details, allowing information to persist across multiple requests. They provide more security than cookies by storing data on the server rather than sending it back and forth with each request. This document explains how cookies and sessions work, when each is appropriate, and how to implement them in PHP.
Mech jointsbuildingdeptpresentation

- Head-of-wall joints are required to be fire-resistant to compartmentalize fires and prevent smoke spread. They must accommodate structural movement while maintaining fire resistance.
- Mechanical joint systems are commonly used and must be tested and listed to required fire resistance standards to ensure proper performance under fire and movement conditions.
- Plans examiners and inspectors must check that listed head-of-wall assemblies are specified and properly installed based on a building's expected deflection rate.
Hitesh cathodic protection

This document is a chapter-by-chapter summary of a document on cathodic protection of pipelines. It discusses the principles of corrosion, forms of corrosion including uniform, galvanic, crevice, pitting and stress corrosion cracking. It explains the mechanisms and prevention methods for different forms of corrosion. The document is intended to provide an overview of corrosion and cathodic protection for pipelines.
More Related Content
What's hot
Types of websites 

The document describes 12 different types of websites: educational websites, online social networks, web portals, blogs, content aggregators, business/marketing websites, wikis, advocacy websites, news websites, entertainment websites, informational websites, and personal websites. For each type, 1-3 examples are provided and briefly described. The document was created by 6 authors for a class assignment.
Computer Security and Ethics

This document discusses various common security risks and threats to computers and networks. It covers topics like malware, viruses, spam, spoofing, phishing, botnets, worms, Trojans, backdoors, blended threats, denial of service attacks, and physical threats like hardware theft and vandalism. It also discusses prevention, detection and removal strategies for many of these threats. Passwords, antivirus software, firewalls and regular backups are recommended for protection. The document provides examples of weak versus strong passwords. It cautions that most malware is spread through the internet.
The internet

The document discusses various aspects of the internet including:
- The internet connects millions of websites and servers through an interconnected network.
- It allows people to communicate and share information globally through email, files, videos and more.
- The world wide web was created in 1990 by Tim Berners-Lee and allows webpages to be accessed through browsers and hyperlinks.
- Key components of the internet include URLs, domains, folders, files, protocols, browsers, and web servers.
- There are different categories of websites including news, education, business, entertainment and personal websites.
Computer viruses

Computer viruses have existed since the late 1980s, beginning with the Brain virus created in Pakistan in 1986. Viruses spread primarily through floppy disks in the early years. Over time, viruses increased in sophistication and ability to spread over networks and email. Some notable early viruses include Michelangelo in 1991, which overwrote data on March 6th, and ILOVEYOU in 2000, one of the first major email viruses. Viruses continue to evolve with different transmission methods as technology changes.
Network Security Nmap N Nessus

This document summarizes different types of network scans that can be performed using Nmap, including TCP connect scans, SYN scans, FIN scans, Xmas scans, Null scans, and least traffic scans. It also discusses why vulnerability scanning is important and compares the features of the free Nessus Home Feed versus the paid Professional Feed for vulnerability scanning. The Professional Feed provides more frequent plugin updates, policy compliance checks, unlimited PCI audits, operating system audits, and technical support compared to the free Home Feed.
Maltego Webinar Slides

Please view our webinar to learn the basics of our Maltego integration. https://attendee.gotowebinar.com/recording/2960337559231715841
Malformity Labs has developed a full transform set that allows for data from ThreatConnect™ to be integrated with the capabilities of Maltego.
All ThreatConnect customers can take advantage of the Maltego transform set through the ThreatConnect™ API and a provided transform server. They can use this to:
• Visualize the relationship between incidents, threats, adversaries, and indicators,
• Leverage attributes belonging to indicators and threats to create Maltego Graphs without losing any of the contextual data within ThreatConnect, and
• Pivot from ThreatConnect data and external open source data sources using other transform sets within Maltego.
Web browsers and web servers

Web browsers allow users to access and view webpages. Examples of popular web browsers include Mozilla Firefox, Google Chrome, Internet Explorer, Opera, and Safari. Mobile browsers are optimized for small screens on portable devices and include micro browsers, mini browsers, and mobile browsers. A web server stores web pages and uses HTTP to serve files that make up web pages to users in response to their requests.
ASP.NET 08 - Data Binding And Representation

This document discusses different ways to represent and bind data in ASP.NET applications. It covers data binding controls to data sources, using .NET collections like ArrayList and Dictionary to store data, using generic collections, populating and using DataTable and DataSet objects to store and manipulate tabular data, and integrating data with XML.
Success in decision making data relevance curation

Success in decision making data relevance curationUS Environmental Protection Agency (EPA), Center for Computational Toxicology and Exposure
This presentation was given at the ToxForum 2023 Winter Meeting in the session regarding Life Cycle Impact Assessment: LCIAs are increasingly being utilized within Life Cycle Assessments (LCA) to attempt to quantify impacts to human health, among other impacts, and ultimately compare products or processes. This session will provide the audience with an overview of LCIA, specifically outlining how toxicology data are utilized in LCIA human health impact calculations. Further, our speakers will delve into the nuances related to the interpretation of LCIA human health outputs and how they compare to information obtained via a risk assessment (RA) approach. Toxicology data are key to these newly emerging efforts to characterize total human health impact. Therefore, panelists will be asked to consider new trends in toxicology, data sources, and or approaches that may help to better inform a calculation of human health impact along with appropriate domains of applicability fostering a discussion relevant to regulators, academics and those in application industries. Usage of internet

The document provides an overview of the internet including its history, common uses, and key features. It explains that the internet is a global network connecting billions of electronic devices that allows people to access and share information worldwide. A brief history outlines how it began in the late 1950s and became publicly available in the 1980s before the development of the World Wide Web in 1991 accelerated its expansion. Common uses of the internet described include email, searching for information online, shopping, watching videos and listening to music, and connecting on social media.
UNIX Operating System ppt

The document provides an overview of the UNIX operating system through a seminar presentation. It discusses the history of UNIX from the 1970s to the 2000s, defines what UNIX is, describes common UNIX commands and the file system structure, and covers topics like memory management, interrupts, reasons for using UNIX, and some applications of UNIX like storage consulting and middleware/database administration. The presentation is intended to educate about the key aspects and functionality of the UNIX operating system.
Internet & Email & collaborative Computing & Social Networking by Abeer Ali 👍...

This document discusses internet, email, social networking, and collaborative computing. It begins by defining the internet and how it works by connecting computers globally. It then discusses uses of the internet like accessing information and conducting business. The history and development of the internet and protocols like TCP/IP are described. Email is introduced as a way to send electronic messages over the internet. Social networking allows people to build online communities and interact through sites like Facebook and LinkedIn. Collaborative computing uses technology like messaging and file sharing to enable groups to work together remotely. Benefits include increased productivity, efficiency, and understanding diverse perspectives.
Network monitoring tools

Microsoft Network Monitor is a tool for viewing network packet contents that are being sent and received over a live network or from a captured file. It provides filtering options and can capture traffic to/from its own interface or, in an enhanced version, all network traffic. OpenNMS is an open source network management system that can monitor tens of thousands of devices from a single server or unlimited devices using a cluster. It includes discovery, event management, service assurance, and performance measurement. Capsa is a free network management solution that integrates traffic capture, analysis, fault diagnosis, and performance evaluation to help troubleshoot, secure, and optimize networks.
3 definition of operating systems

The document defines operating systems and describes their basic components and functions. It discusses how operating systems provide an interface between hardware and software, manage system resources, and allow for the execution of user programs. The goals of an operating system are to provide convenience for users and efficient operation of the computer system. An operating system is a type of system software that coordinates hardware and software and controls and allocates resources.
Web Mining

This document provides an overview of web mining and summarizes key concepts. It begins with definitions of data mining and web mining. The document then discusses three categories of web mining: web content mining, web usage mining, and web structure mining. Various matrix expressions used to represent web data are also introduced, including document-keyword co-occurrence matrices, adjacent matrices, and usage matrices. Finally, two common similarity functions - Pearson correlation coefficient and cosine similarity - are outlined.
Joomla

Joomla is a popular open source content management system (CMS) that allows users to manage and organize content on a website without needing technical skills. It uses a simple architecture that separates the user interface from the business logic and data layers. Content is added and managed through a web-based administration panel. Joomla is commonly used for corporate websites, online magazines, e-commerce sites, and other applications. It provides features like user management, content organization, templates, and media management. To use Joomla, a server is needed that meets the minimum requirements of PHP, MySQL, and Apache. New sites can be created by downloading and installing Joomla through a simple process.
3. interface scratch

Dokumen ini memberikan penjelasan tentang interface Scratch yang terdiri dari beberapa bagian utama seperti toolbar, tab block, area script, block costumes, dan block sounds. Area script digunakan untuk mengatur blok-blok perintah yang akan dieksekusi sprite. Terdapat tiga jenis blok perintah yaitu stack block, hats, dan reporters. [/ringkasan]
User management

This document provides information on managing users and groups in Linux. It lists commands for adding, modifying, and deleting users and groups such as useradd, usermod, userdel, and groupadd. It describes how user information is stored in files like /etc/passwd, /etc/shadow, and /etc/group. It also covers setting passwords, restricting login access, giving users root privileges, and managing secondary groups. Potential error scenarios involving permissions and viewing passwords are also addressed.
Politics the Wellstone Way

This document introduces Wellstone Action, a community organizing group that trains people in leadership and organizing skills. It highlights that Wellstone Action has trained over 32,000 people in 45 states since 2004 to win progressive change through hundreds of organizations. The document also outlines Wellstone Action's model for building long-term power through an agenda, growth, and politics, including developing new leaders, community organizing, and electoral politics to determine decision-makers and hold them accountable.
Cookies & Session

Cookies are small pieces of data stored in a user's browser that are sent back to the server with requests. They allow servers to remember stateful information about users, like items in a shopping cart. Sessions use a unique identifier to store server-side data associated with each user, like login details, allowing information to persist across multiple requests. They provide more security than cookies by storing data on the server rather than sending it back and forth with each request. This document explains how cookies and sessions work, when each is appropriate, and how to implement them in PHP.
What's hot (20)
Success in decision making data relevance curation

Success in decision making data relevance curation
Internet & Email & collaborative Computing & Social Networking by Abeer Ali 👍...

Internet & Email & collaborative Computing & Social Networking by Abeer Ali 👍...
Viewers also liked
Mech jointsbuildingdeptpresentation

- Head-of-wall joints are required to be fire-resistant to compartmentalize fires and prevent smoke spread. They must accommodate structural movement while maintaining fire resistance.
- Mechanical joint systems are commonly used and must be tested and listed to required fire resistance standards to ensure proper performance under fire and movement conditions.
- Plans examiners and inspectors must check that listed head-of-wall assemblies are specified and properly installed based on a building's expected deflection rate.
Hitesh cathodic protection

This document is a chapter-by-chapter summary of a document on cathodic protection of pipelines. It discusses the principles of corrosion, forms of corrosion including uniform, galvanic, crevice, pitting and stress corrosion cracking. It explains the mechanisms and prevention methods for different forms of corrosion. The document is intended to provide an overview of corrosion and cathodic protection for pipelines.
Pertemuan 10 keamanan jaringan dgn firewall

1. Penentuan kebijakan keamanan (security policy) merupakan hal penting dalam mengkonfigurasi firewall.
2. Analisis port-port yang digunakan protokol dan membuka port-port tersebut di firewall sesuai kebutuhan.
3. Pengoptimalan dilakukan dengan menentukan konfigurasi firewall secara tepat.
Fire wall

Name is Noor Azeem, class is PI, section is A, and teacher is Sir. Shehroze Ilyas. The document discusses the benefits of firewalls, which allow wanted traffic but stop unwanted traffic.
Understanding Fire-Rated Assemblies

This presentation explains the code requirements for active and passive building systems used to protect buildings and their occupants and contents from fire.
Partitions and finishes-slideshare

Partitions subdivide interior spaces and can be load-bearing or non-load bearing. Finishes can be thick, property-changing materials like plaster or thin, cosmetic materials like paint. External finishes include dry claddings like timber boarding and wet finishes like lime-based renders. Internal finishes include thick plaster or drywall with joint compound and paint. Proper installation of partitions and selection of appropriate finishes is important for interior construction.
Partitions

Glass partition walls can be constructed of either glass sheets or hollow glass blocks. Glass sheet partitions use a wooden frame with glass sheets fixed into panels divided by vertical and horizontal posts. Hollow glass blocks are translucent units available in different sizes, shapes, and thicknesses that are laid with mortar. Glass partition walls provide architectural effect while being soundproof, fireproof, and heatproof. Steel partition walls can be single or double-skinned and are used to create enclosed work areas in offices and industrial environments.
Partition walls

This document discusses partition walls, which divide interior spaces without carrying structural loads. It defines partition walls and lists their advantages such as dividing spaces, providing privacy, and being lightweight. It describes requirements for good partition walls and various types including brick, hollow block, concrete, glass, wood, strawboard, plaster, metal, and asbestos cement. Movable and portable partition walls are also discussed. Common applications include offices, schools, hotels, and event spaces.
Partition walls

The document discusses different types of partition walls used to divide interior spaces in buildings. It describes timber stud, metal stud, drywall, glass block, and block partitions. Timber stud partitions can be plaster skimmed, dry-lined, or partially glazed. Metal stud partitions are lightweight but strong, consisting of a metal framework covered in plasterboard or fire-resistant sheeting. Glass block partitions are made of translucent glass blocks laid in mortar, sometimes with reinforcement. Block partitions are constructed from masonry blocks.
Partition wall

Partition walls are used to divide interior spaces. They can be load-bearing or non-load bearing. Common types include timber, brick, clay block, concrete, glass, and metal partitions. Timber partitions use a wooden framework, while brick partitions come in plain, reinforced, and nogging styles. Clay block and concrete partitions use hollow blocks or precast panels. Glass partitions employ sheets or hollow blocks for visibility and soundproofing. Metal partitions make use of metal lath and plaster or steel framing. Proper installation of the chosen partition wall type is important for strength and function.
Detailing : Interior Wall Assemblies

The document discusses various types of interior wall assemblies, including:
- Metal stud framing systems for partition walls, suspended ceilings, and shaft walls.
- Different types of gypsum wallboard such as regular, fire-rated, moisture-resistant, soundproofing, and lead-lined varieties.
- Tile backing panels including waterproof cement boards and water-resistant gypsum panels.
- Details such as control joints, sound insulation, vapor barriers and different levels of finishing drywall.
Viewers also liked (13)
Similar to Windows Firewall.ppt
FUNGSI FIREWALL PADA JARINGAN VOIP

Dokumen tersebut membahas tentang fungsi firewall pada jaringan VoIP. Firewall digunakan untuk melindungi jaringan VoIP dari berbagai gangguan seperti interupsi, intersepsi, modifikasi, dan fabrikasi yang dapat terjadi karena faktor ketidaksengajaan atau pihak ketiga. Firewall bekerja dengan menganalisis paket data masuk dan keluar, menyaring berdasarkan kebijakan, dan melaporkan aktivitas jaringan untuk mencegah ganggu
Firewall

Dokumen tersebut membahas tentang firewall dan keamanan komputer. Ia menjelaskan definisi firewall, jenis-jenisnya, fungsi dan teknik yang digunakan firewall, serta langkah-langkah membangun firewall untuk melindungi jaringan dari ancaman di internet.
Cara mendesain sistem keamanan jaringan

Makalah ini membahas desain sistem keamanan jaringan komputer. Pembahasan mencakup tujuan keamanan jaringan seperti ketersediaan, kehandalan dan kerahasiaan data, serta cara pengamanan melalui autentikasi dan enkripsi. Ancaman keamanan jaringan seperti sniffer dan spoofing juga dibahas beserta cara mengamankan jaringan WiFi dan meningkatkan keamanan jaringan secara keseluruhan.
Sim, hapsi ali, nadya natalia 43116110318, forum 10

Sim, hapsi ali, nadya natalia 43116110318, forum 10
AIJ - Materi Firewall.pptx

Firewall merupakan sistem yang dirancang untuk mencegah akses tak diinginkan ke dan dari jaringan internet dengan mengontrol, memfilter, dan memutuskan lalu lintas data berdasarkan aturan. Ada beberapa metode dan teknik yang digunakan firewall seperti packet filtering, stateful inspection, kontrol pengguna, kontrol layanan, dan arah kontrol. Jenis-jenis firewall meliputi packet filtering, NAT, circuit level gateway, virtual, application level gateway, transparent, dan hybrid firewall.
PengamananJaringanKomputer_Kelompok7_1MIB (2).ppt

Dokumen tersebut membahas konsep dasar keamanan jaringan komputer dan berbagai elemen yang membentuk keamanan jaringan seperti ancaman, pengendalian akses, firewall, dan virtual private network."
Korry marintan siahaan, hapzi ali,forum 7 keamanan sistem informasi, ut, 2018

Korry marintan siahaan, hapzi ali,forum 7 keamanan sistem informasi, ut, 2018
aptika.kominfo.go.id-Keamanan Jaringan Internet dan Firewall.pdf

Kemanan Jaringan Internet & Firewall
FIREWALL PADA JARINGAN VOIP.docx

Firewall berfungsi untuk mengontrol lalu lintas jaringan dan melindungi jaringan internal dari akses yang tidak sah. Firewall bekerja dengan memfilter lalu lintas berdasarkan kriteria seperti alamat IP, port, dan protokol untuk menentukan lalu lintas mana yang diizinkan atau diblokir. Firewall memisahkan jaringan internal yang aman dari jaringan eksternal yang kurang aman dan mengontrol komunikasi antara keduanya.
Pengenalan Firewall Dan IPTables Pada Jaringan Komputer

Pengenalan Firewall Dan IPTables Pada Jaringan Komputer
Pengenalan Firewall Dan IPTables Pada Jaringan Komputer
Pengenalan Firewall Dan IPTables Pada Jaringan Komputer
Pengenalan Firewall Dan IPTables Pada Jaringan Komputer
Pengenalan Firewall Dan IPTables Pada Jaringan Komputer
Pengenalan Firewall Dan IPTables Pada Jaringan Komputer
Firewall honeypot it ethic

Firewall digunakan untuk mengontrol lalu lintas jaringan dan menerapkan kebijakan keamanan. Firewall dapat diimplementasikan sebagai perangkat jaringan khusus, perangkat keras, atau software. Ada berbagai jenis firewall seperti filter paket, proxy, dan personal firewall. Honeypot digunakan untuk menangkap penyusup dengan menyajikan target palsu untuk diserang.
Similar to Windows Firewall.ppt (20)
Sim, hapsi ali, nadya natalia 43116110318, forum 10

Sim, hapsi ali, nadya natalia 43116110318, forum 10
Korry marintan siahaan, hapzi ali,forum 7 keamanan sistem informasi, ut, 2018

Korry marintan siahaan, hapzi ali,forum 7 keamanan sistem informasi, ut, 2018
aptika.kominfo.go.id-Keamanan Jaringan Internet dan Firewall.pdf

aptika.kominfo.go.id-Keamanan Jaringan Internet dan Firewall.pdf
10, SIM, Dewi Zulfah, Hapzi Ali, Sistem Informasi Manajemen, Mercu Buana Univ...

10, SIM, Dewi Zulfah, Hapzi Ali, Sistem Informasi Manajemen, Mercu Buana Univ...
Pengenalan Firewall Dan IPTables Pada Jaringan Komputer

Pengenalan Firewall Dan IPTables Pada Jaringan Komputer
Windows Firewall.ppt
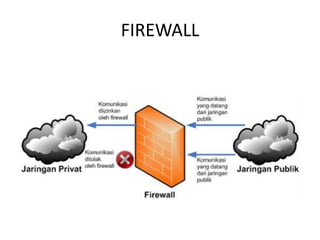
- 1. FIREWALL
- 2. Windows firewall adalah salah satu fitur keamanan yang digunakan oleh Microsoft untuk melindungi Sistem Operasi Windows. Pada dasarnya windows firewall berguna untuk mencegah berbagai macam serangan dari Internet.
- 3. Fungsi Firewall • Mengatur dan mengontrol lalu lintas jaringan • Melakukan autentikasi terhadap akses • Melindungi sumber daya dalam jaringan privat • Mencatat semua kejadian, dan melaporkan kepada administrator
- 4. Cara Kerja Firewall • Menolak dan memblokir paket data yang datang berdasarkan sumber dan tujaun yang tidak diinginkan • Menolak dan menyaring paket data yang berasal dari jaringan intenal ke internet. Contoh nya ketika ada pengguna jaringan internel akan mengakses situs-situs porno
- 5. Lanjutan . . . • Menolak dan menyaring paket data berdasakan konten yang tidak diinginkan seperti situs yang terdeteksi mengandung virus • Melaporkan semua aktivitas jaringan dan kegiatan firewall
- 6. Teknik Firewall 1. Service control (kendali terhadap layanan) 2. Direction Conrol (kendali terhadap arah) 3. User control (kendali terhadap pengguna) 4. Behavior Control (kendali terhadap perlakuan)
- 7. Tipe-tipe Firewall 1. Packet Filtering Router 2. Application-Level Gateway 3. Circuit-level Gateway
- 8. Metode Firewall • Packet Filtering • Stateful Inspeksi
- 9. Cara Mengaktifkan Firewall Windows 8 • Ketikkan "Windows Firewall" Pada Start Screen. Pilih pada tab Setting, klik sekali Ikon Windows Firewall yang tampil.
- 10. • Selanjutnya akan keluar tampilan kotak dialog, lihat pada bagia sebelah kiri, klik "Turn Windows Firewall on or off".
- 11. • Pilih "Turn on Windows Firewall" pada bagian Priavate Network dan Public Network. Klik OK.
- 12. Cara Menonaktifkan Firewall Windows 8 • Anda tinggal pilih "Turn of Windows Firewall (Not Recommended)" kemudian klik OK.
- 13. KESIMPULAN Dengan adanya firewall dalam suatu sistem jaringan komputer diharapkan dapat melindungi informasi-informasi penting dan dapat memanajemen lalu lintas pengaksesan dari dalam maupun dari luar sistem.
- 14. Dengan mengetahui dan menerapkan firewall tentu kita harapkan sebuah jaringan terlindungi dan aman dari penyusup atau craker yang mencoba untuk memanfaatkan celah komputer atau jaringan untuk kepentingan tertentu yang tentu saja dapat merugikan jika penyusup yang datang dari luar behasil mencuri data, mengubah, merusak dan lain sebagainya.
- 15. Guna meningkatkan kinerja seluruh bagian – bagian terkait mencapai kemaksimalan suatu koneksi atau jariangan dari dalam maupun luar yang memberi efek menguntungkan bagi si pengguna ( user ).
Editor's Notes
- Packet Filtering: Pada metode ini paket (potongan kecil data) dianalisa dan dibandingkan denganfilter. filter paket memiliki seperangkat aturan yang datang dengan tindakan menerima dan menolak yang pra-dikonfigurasi atau dapat dikonfigurasi secara manual oleh administrator firewall.. Jika paket berhasil membuatnya melalui filter ini maka itu diperbolehkan untuk mencapai tujuan, kalau tidak akan dibuang. Stateful Inspeksi: Ini adalah metode baru yang tidak menganalisa isi dari paket. Sebaliknya ia membandingkan aspek kunci tertentu setiap paket database sumber terpercaya.. Kedua paket yang masuk dan keluar dibandingkan terhadap database ini dan jika perbandingan menghasilkan pertandingan yang wajar, maka paket yang diizinkan untuk melakukan perjalanan lebih lanjut. Jika tidak, mereka akan dibuang.
