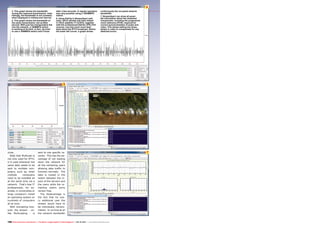
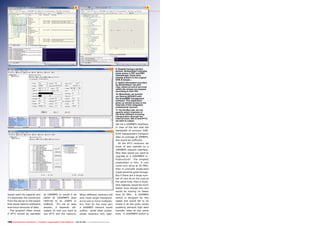
1. The document discusses IPTV (Internet Protocol Television) and key concepts related to implementing an IPTV system such as TCP, UDP, RTP, multicasting, and unicasting.
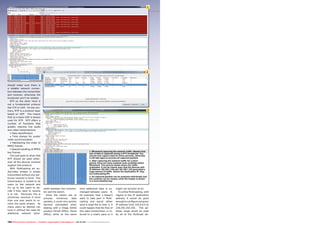
2. TCP ensures correct transmission of data but is not ideal for live video/audio. UDP is better suited for live streams as it does not require acknowledgment of receipt. RTP improves UDP for multimedia transmission.
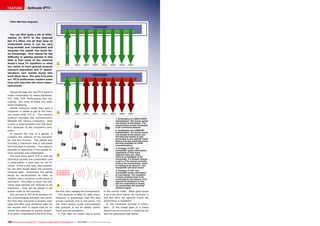
3. Multicasting transmits a single stream to multiple receivers simultaneously without additional bandwidth, while unicasting transmits to a single receiver.